
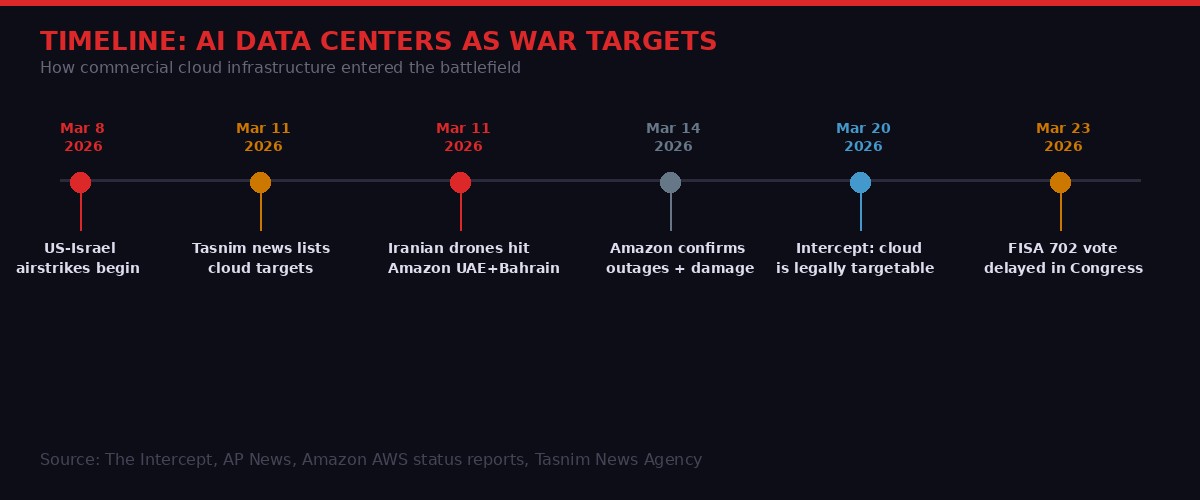
Somewhere in the UAE and Bahrain, Iranian kamikaze drones hit Amazon. Not a military base. Not a weapons depot. A server farm. Three days after the United States and Israel began their joint bombardment of Iran in early March 2026, the Islamic Revolutionary Guard Corps launched drone strikes against Amazon-owned data centers running cloud services across the Middle East.
The strikes caused structural damage, disrupted power delivery, triggered fire suppression systems that added water damage on top, and knocked out services across the region. According to The Intercept, Amazon confirmed the impacts and outages - but said little about the military significance of what was housed in those buildings.
Iran said plenty. According to Iranian state television, the strikes were not about disrupting grocery deliveries or social media. The stated motive was to highlight "the role of these centers in supporting the enemy's military and intelligence activities." And on March 11th, the quasi-official Tasnim News Agency published a list of dozens of regional facilities - Amazon, Microsoft, Google, and others - classified as "Enemy Technology Infrastructure" suitable for targeting.
This is not merely a war story. It is the moment the abstract concept of "the cloud" collided with the physical reality of warfare. And if legal scholars are right, Tehran may have a point.
The Argument Iran Is Making
International humanitarian law - the body of rules governing what is and is not legal in armed conflict - operates on a basic principle: civilian infrastructure is protected, military infrastructure is not. Everything turns on which category a given object falls into at the moment it is struck.
The problem with data centers is that the same building, the same racks of servers, the same fiber cables can simultaneously support a teenager's Netflix stream and an Air Force targeting algorithm. The distinction that matters in law - effective contribution to military action - is almost impossible to assess from the outside.
"The legality turns on whether the specific facility, at the specific moment, is genuinely serving the military operations of a party to the conflict in a way that offers a concrete and definite advantage to the attacker." - León Castellanos-Jankiewicz, Asser Institute for International and European Law, The Hague
This is not a theoretical problem. Amazon Web Services holds billions of dollars in Pentagon contracts. Amazon's GovCloud regions provide cloud computing for classified government workloads. The Joint Warfighter Cloud Capability - a multi-vendor contract the Pentagon awarded to Amazon, Microsoft, Google, and Oracle - explicitly provides the US military with "greater lethality" in the words of the Pentagon's own documentation.
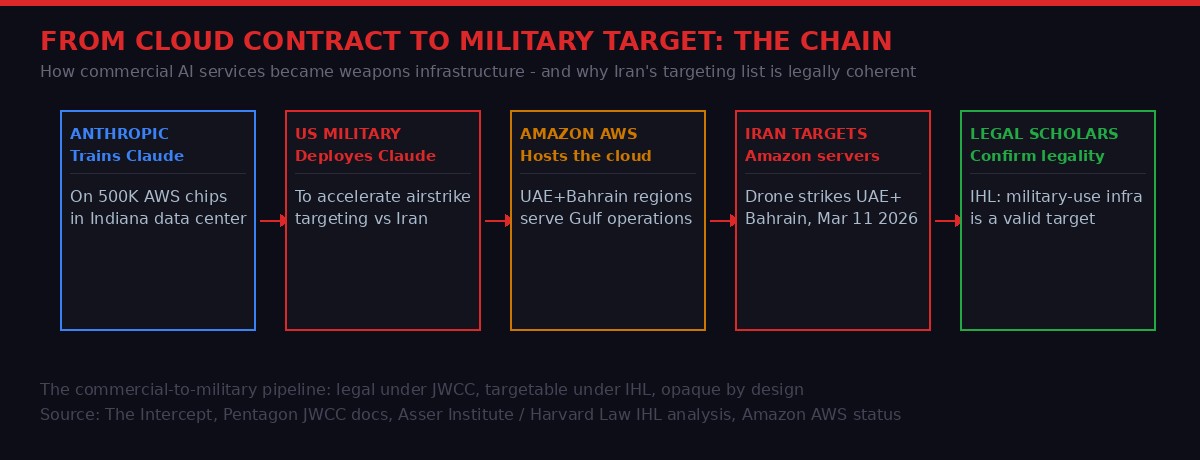
And then there is the AI angle. Anthropic's Claude large language model was reportedly used to accelerate American airstrikes against Iranian targets. Claude was trained in part using 500,000 chips housed in an $11 billion Amazon data center in Indiana. If Claude is now a weapons system - if it is being used to identify targets, process battlefield signals, or generate strike recommendations - what does that make the facility that houses its chips?
"If the facility is currently used in the training of the LLM that is used in the conduct of military operations - for example, by fine-tuning object classification or user-interaction features - then this could render it targetable." - Ioannis Kalpouzos, international law scholar and visiting professor, Harvard Law
The question is no longer hypothetical. It has been answered with drone strikes.

The Pentagon's Cloud Dependency
To understand why data centers are now targets, you have to understand how thoroughly the US military has outsourced its digital infrastructure to commercial cloud providers over the past decade.
The shift began in earnest with the controversial JEDI contract - Joint Enterprise Defense Infrastructure - a $10 billion deal that Microsoft eventually won after Amazon protested. But JEDI was just the beginning. By 2024, the Pentagon had transitioned to the Joint Warfighter Cloud Capability, a broader multi-vendor arrangement that brings Amazon, Microsoft, Google, and Oracle into what defense officials describe as deeply integrated military computing.
Each of the four JWCC providers maintains dedicated, Pentagon-exclusive cloud regions. Microsoft's US DoD Central and US DoD East regions are "reserved for exclusive Department of Defense use," according to Microsoft documentation, with data centers in Des Moines, Iowa, and Northern Virginia. Amazon offers similar dedicated regions, though their physical locations are classified. Oracle operates Pentagon-specific facilities in Chicago, Phoenix, and Virginia.
But here is where the dual-use problem compounds: these same companies also provide general-purpose cloud services to civilian customers worldwide. The same AWS region that hosts a startup's database might be physically co-located with infrastructure supporting classified DoD workloads. Companies are deliberately vague about where the lines are drawn - for obvious reasons.
Google's arrangement is particularly complex. The tech giant sells the Pentagon both its general-purpose public cloud for lower-sensitivity work and specialized air-gapped networks for classified operations. The company also sells modular mini-data centers designed for deployment near battlefields or military bases. Even work involving Top Secret military data "can operate within Google's trusted, secure, and managed data centers" - meaning the same buildings that run Gmail could theoretically host Air Force classified operations.
When Iran's Tasnim News Agency listed "Enemy Technology Infrastructure," it was not guessing. It was reading the same Pentagon press releases and contract announcements available to anyone. The list included Microsoft Azure facilities, Google Cloud nodes, and others alongside Amazon. The message was: we know which buildings run your war.
Dual Use, Dual Risk: The Legal Minefield
International humanitarian law was designed for a world where weapons factories looked like weapons factories. Bomb-making facilities had chimneys and fences and guards. Power stations that supplied military bases were distinguishable from power stations serving hospitals. The categories were not always clean, but there was at least a plausible geography to the battlefield.
Cloud computing collapsed that geography. A single physical data center in Abu Dhabi might run workloads for: a regional airline, a government health portal, Amazon Prime video streaming, a US intelligence contractor, and a US Central Command battlefield analytics tool. All running simultaneously, on the same hardware, in the same building.
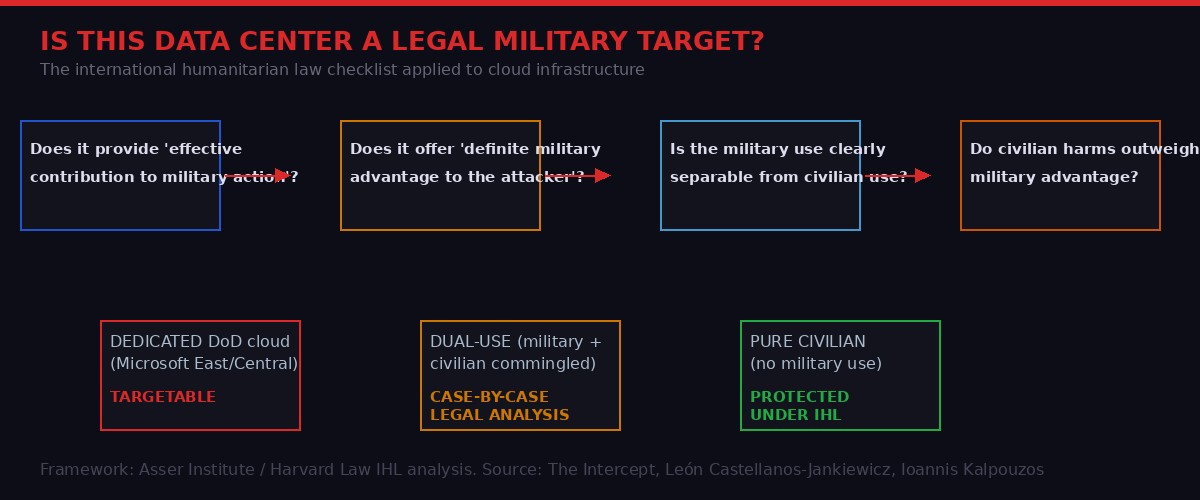
"The picture becomes more legally complex when a data center functions as a 'dual-use' object - simultaneously hosting military data or capabilities alongside civilian services. Once a facility is found to make an effective contribution to military action, the entire physical object can, under the dominant legal view, qualify as a military objective." - León Castellanos-Jankiewicz, Asser Institute
The dominant legal view Castellanos-Jankiewicz is referring to comes from Additional Protocol I to the Geneva Conventions - the core document governing attacks on civilian objects. Under Article 52, objects are military objectives if by "their nature, location, purpose or use make an effective contribution to military action and whose total or partial destruction, capture or neutralization, in the circumstances ruling at the time, offers a definite military advantage."
Notice what that framework requires: effective contribution at the time of attack. Not historical association. Not future potential. The legal question is what those servers are doing when the drone hits.
This creates a surveillance and intelligence problem that no drone operator can actually solve. The physical opacity of cloud infrastructure is total. From the outside - and often from the inside - there is no way to know which racks of servers are processing what workloads at any given moment. Kubernetes clusters spin up and down. Workloads migrate across availability zones. A server running military AI in the morning might be running civilian analytics in the afternoon.
Castellanos-Jankiewicz put it plainly: "The practical challenge is that cloud infrastructure is often technically opaque, even to providers themselves. The services a given data center supports may not be readily ascertainable from the outside or even inside, which complicates the attacker's legal obligations considerably."
Iran resolved this ambiguity by deciding the question in its own favor. If Amazon provides cloud services to the US military, Amazon's infrastructure in the theater of war is fair game. Whether that is legally correct under any particular treaty framework is a question for scholars - and future war crimes tribunals.
The AI Acceleration That Made This Inevitable
The drone strikes on Amazon's data centers did not happen because Iran randomly decided to attack commercial infrastructure. They happened because the US military's adoption of AI - specifically large language models for targeting, intelligence analysis, and battlefield decision support - created a logical chain that transformed commercial servers into weapons.
AI training and inference require massive compute infrastructure. The large-scale AI systems being used by the US military are built on the same AWS, Azure, and Google Cloud hardware that runs commercial workloads. Anthropic's Claude being used to accelerate airstrikes is not a distant hypothetical - it is being reported as current operational reality.
Consider what this means: Anthropic trained Claude on 500,000 specialized chips housed in an Amazon data center in Indiana. The Pentagon then uses Claude to help identify and prioritize airstrike targets against Iran. Under IHL, the Indiana facility is potentially a military target - not because it looks like a weapons factory, but because of what it processed months ago.
Ioannis Kalpouzos at Harvard Law was careful to note that targetability under IHL depends on current use, not past contribution. But the line is blurrier than that: if a facility is still being used to fine-tune the same AI systems that are being used in active operations - improving object classification, updating user-interaction features, scaling inference capacity - then the legal case for targeting strengthens with each training run.
Defense Secretary Pete Hegseth has been aggressively pushing AI tools into military operations across the board. The more AI the US military uses in combat, and the more that AI runs on commercial cloud infrastructure, the more commercial infrastructure becomes militarily relevant. The logical endpoint of that process is a world where every major AWS region is a potential wartime target.
The Intercept's analysis draws a striking comparison to Cold War ICBM silo placement. Nuclear launch capabilities were clustered in the sparsely populated Upper Midwest deliberately - forming what strategists called a "nuclear sponge" to draw Soviet strikes away from population centers. The analogy to data centers is uncomfortable but apt: as AI infrastructure becomes military infrastructure, its physical location becomes a strategic question with life-and-death consequences for nearby communities.
Project Nimbus, AWS Bahrain, and Why the Middle East Was First
The Iranian drones did not hit data centers in Virginia or Oregon. They hit facilities in the UAE and Bahrain - Amazon's Middle East regions. This was not accidental geography.
Amazon's Middle East cloud operations serve a mix of commercial customers and government clients across the Gulf. But Amazon and Google are both party to Project Nimbus - a $1.2 billion joint cloud contract with the Israeli government that provides services across Israeli government agencies, including the Ministry of Defense and state-owned weapons companies.
Project Nimbus has been enormously controversial. Google employees staged walkouts and were fired for protesting the company's role. Researchers have documented the contract providing cloud services for Israeli military operations in Gaza. Google executives admitted internally they could not always track how their cloud services were being deployed by Israeli military users.
From Iran's perspective, Amazon and Google infrastructure in the Gulf is not neutral commercial technology. It is infrastructure serving the combined military operations of the US, Israel, and allied Gulf states. The strikes on UAE and Bahrain facilities were a message: proximity to the conflict zone does not protect you if your servers serve the enemy.
The second-order effect is significant. Cloud providers have been aggressively expanding into Gulf markets - AWS Bahrain launched in 2019, UAE in 2022. These regions were supposed to serve the booming Gulf commercial market: financial services, government digitization, regional tech startups. They are now in the blast radius of a military conflict they have no control over.
For enterprise customers in the region, the question is no longer just about service reliability or data sovereignty. It is about whether their cloud provider's military contracts make their data center a target. That is a completely new risk category that no business continuity plan was designed to address.
FISA, Surveillance, and the Domestic Parallel
While Iranian drones were striking cloud infrastructure in the Gulf, a parallel debate about the relationship between tech companies and state surveillance was playing out in Washington. It offers a window into how the same dynamics that made Amazon a military target also threaten civil liberties at home.
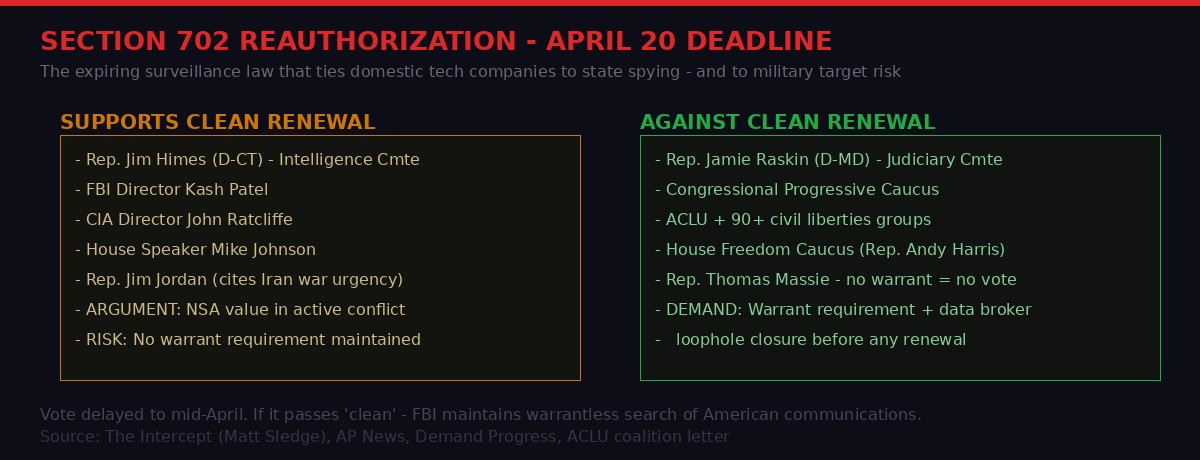
House Speaker Mike Johnson delayed a vote this week on reauthorizing Section 702 of the Foreign Intelligence Surveillance Act - the law that allows intelligence agencies to collect foreign communications, and permits the FBI to search that collected data for information on American citizens and residents without a warrant.
The connection to the data center war is direct. Section 702 is why tech companies provide intelligence agencies with user data - and why that cooperation makes their infrastructure a target from adversaries who assume the companies are extensions of the surveillance state. Amazon, Google, and Microsoft do not just run Pentagon war clouds. They also respond to FISA orders, hand over user communications, and in some cases build dedicated government interfaces for intelligence collection.
Critics of a "clean" renewal of Section 702 - including Rep. Jamie Raskin and a coalition of more than 90 civil liberties organizations - have highlighted what they call the "data broker loophole": the ability of intelligence agencies to purchase location data, search histories, and transaction records from commercial data brokers, circumventing civil liberties protections entirely. FBI Director Kash Patel testified this week that the agency was gleaning "valuable intelligence" from such purchases.
"The safeguards put in place in 2024 have been badly eroded by the Trump Administration. The 'clean' extension favored by President Trump and Stephen Miller leaves the Trump Administration in charge of policing its own abuses of this authority - and what could go wrong with that?" - Rep. Jamie Raskin (D-MD), letter to House Democrats, March 20, 2026
The FISA debate connects to the data center strikes in a way that most coverage misses. Every time the US government requires tech companies to build backdoors, share data, or provide military-adjacent services, it narrows the gap between "commercial cloud" and "military infrastructure" - in the eyes of adversaries, under international law, and in the minds of foreign governments who might decide these servers are legitimate targets.
Section 702 is set to expire April 20th. If it is renewed without a warrant requirement, American intelligence agencies maintain the ability to search Americans' private communications without judicial oversight. If it expires or is amended, there is a brief window for reforms that privacy advocates have sought for a decade. The Iran war and the data center strikes have added a new dimension: every expansion of US government surveillance powers is simultaneously an argument that American commercial cloud infrastructure is military infrastructure subject to attack.

What Happens Next: The New Topology of War
The Iranian strikes on Amazon data centers were the opening shot in what may become a new theater of conflict. Not a cyber theater - not remote, not bloodless, not deniable. A physical theater where commercial buildings full of servers get hit with drones because of what runs on them.
The implications branch in several directions:
For Cloud Providers
Amazon, Microsoft, Google, and Oracle now face a conflict between their commercial and government businesses that cannot be resolved by internal policies. Their government contracts made them military actors. Their civilian customers are collateral exposure. No amount of "we take security seriously" language in terms-of-service addresses the reality that their buildings are on Iranian targeting lists.
Expect pressure on cloud providers to physically segregate military and civilian infrastructure - dedicated regions, separate buildings, geographic separation from civilian data centers. This will be expensive. It will be operationally complex. And it may be mandatory. The alternative - maintaining dual-use infrastructure that enemy states are actively targeting - creates liability exposure and reputational risk that boardrooms will eventually find unacceptable.
For the Tech Industry Broadly
Every company that provides services to the US military - AI firms, analytics companies, satellite operators, even telecommunications providers - now needs to think about what their military contracts mean for their civilian infrastructure. Anthropic's relationship with the US government makes its training data centers a potential target in future conflicts. Palantir's analytics platforms running on commercial clouds create similar exposure.
The defense tech investment boom of recent years - billions flowing into AI companies with military contracts - looks different when the physical infrastructure housing that AI becomes a wartime target. Investors did not price "drone strikes on our data center" into their models.
For the Legal Framework
International humanitarian law urgently needs updated guidance on dual-use cloud infrastructure. Current treaty frameworks were not designed for a world where the same server farm runs Instagram and Air Force targeting algorithms. The ICRC and relevant UN bodies will eventually produce guidance, but the Iran strikes have already forced the issue into the real world faster than any theoretical framework anticipated.
The key question - whether commingling military and civilian workloads on the same physical infrastructure creates collective liability for the entire facility - will be litigated in future conflicts, in scholarly journals, and potentially in international courts. Iran has already answered it in the affirmative, with drones.
For Civilian Users
The most unsettling implication is for ordinary users whose data is stored in cloud infrastructure near conflict zones. AWS Bahrain users who lost access to their data during the March strikes were not military targets. They were collateral damage of the military-civilian infrastructure merger that commercial cloud providers have been building for years.
In the Cold War, Americans were warned about proximity to nuclear silos. The new version of that warning may need to be about proximity to data centers. The "nuclear sponge" that absorbed Soviet warheads in the Upper Midwest has a digital equivalent - a nationwide network of server farms that, because they serve the Pentagon, could be legitimate targets for any adversary with sufficiently long-range weapons.
No one told Amazon's customers in Bahrain that their invoices and databases might be hosting data that put them physically near a military target. The cloud industry has been selling seamless, borderless, always-available infrastructure. The Iran conflict has exposed the lie. Infrastructure has borders. Servers have addresses. And some of those addresses are now on targeting lists.

The Question That Cannot Be Avoided
There is a question buried in all of this that no one in the tech industry wants to answer directly: did the companies whose servers were struck do anything wrong?
Amazon, Google, and Microsoft chose to pursue Pentagon contracts. They chose to build cloud infrastructure in Gulf countries that are party to the US-Israel military alliance. They chose to integrate their commercial platforms with military and intelligence agency requirements. They did this openly, reporting the contracts to investors, touting government work as a stable revenue stream.
From a pure business perspective, these were rational decisions. Government cloud contracts are lucrative, long-term, and relatively stable. AWS, Azure, and Google Cloud have all built significant government-focused businesses that their shareholders value highly.
From a strategic perspective, those decisions came with consequences that are now becoming visible. By accepting military contracts and intelligence cooperation requirements, these companies signed onto a bargain: government revenue in exchange for a particular legal and strategic status. That status has now been tested with Iranian drones, and the test confirmed what IHL scholars have argued for years - commercial cloud infrastructure is not neutral when it serves the war machine.
The tech industry cannot simultaneously argue that it provides essential civilian infrastructure deserving of legal protection and that it provides essential military capabilities deserving of defense contracts. Those two positions are now in direct tension. The Iran strikes did not create that tension - they just made it impossible to ignore.
The cloud went to war in March 2026. The industry will spend the next decade dealing with what that means.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on TelegramPrimary sources: The Intercept (Sam Biddle, "Data Centers Are Military Targets Now," March 20 2026); AP News (Nevada ALPR surveillance investigation); The Intercept (Matt Sledge, "Democrats Might Save Mike Johnson's Push to Give Trump Domestic Spying Power," March 23 2026); The Verge (Musk Terafab announcement, March 22 2026); Amazon AWS status reports; León Castellanos-Jankiewicz / Asser Institute; Ioannis Kalpouzos / Harvard Law; Tasnim News Agency (Iran); Pentagon JWCC documentation.