BrowserGate: LinkedIn Scans 6,222 Browser Extensions on Every Visit Without Your Consent
Microsoft's professional networking platform runs one of the largest corporate espionage operations in digital history. Hidden JavaScript probes your browser for installed software, maps your religion, politics, disability status, and job search activity - then transmits everything to LinkedIn's servers and a third-party Israeli cybersecurity firm. One billion users. Zero consent.

Every LinkedIn visit triggers a silent scan of your browser. Photo: Unsplash
Every time you open LinkedIn in a Chrome-based browser, something happens that you are never told about. Hidden code buried inside a 2.7-megabyte JavaScript bundle downloads a list of 6,222 browser extensions and attempts to detect every single one installed on your machine. The scan identifies your religious beliefs, your political orientation, whether you have a disability, and whether you are secretly looking for a new job. It then encrypts the results using RSA encryption and transmits them to LinkedIn's servers and to HUMAN Security, an American-Israeli cybersecurity firm formerly known as PerimeterX.
You are never asked. There is no consent dialog. LinkedIn's privacy policy does not mention any of this.
The investigation was published by Fairlinked e.V., a German nonprofit association of commercial LinkedIn users, under the name "BrowserGate." Their researchers reverse-engineered LinkedIn's production JavaScript bundles, identified three distinct surveillance systems operating simultaneously, and documented the entire data pipeline from scan to transmission. On April 2, 2026, the story hit the top of Hacker News with over 1,500 upvotes. The reaction was immediate and visceral: a mix of horror, fury, and grim unsurprise from a tech community that has watched platform companies push privacy boundaries for years - but had never seen anything quite this brazen.
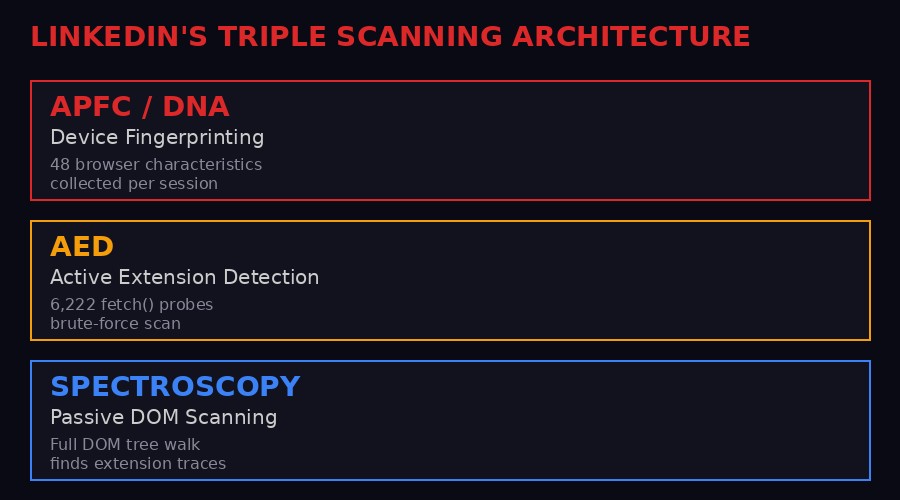
The three scanning systems running simultaneously inside LinkedIn's JavaScript bundle. Infographic: BLACKWIRE
The Machine: How LinkedIn's Triple Scanning System Works

LinkedIn's scanning code lives inside a single Webpack bundle served to every visitor. Photo: Unsplash
The technical architecture of LinkedIn's scanning operation is remarkably sophisticated. It is not a single script running a quick check. It is three independent detection systems working in parallel, each designed to catch what the others might miss. Fairlinked's researchers identified all three systems operating inside a single Webpack-bundled JavaScript file (chunk ID: chunk.905, module 75023) that ships to every LinkedIn visitor's browser.
System 1: APFC/DNA - Device Fingerprinting
The first system, internally labeled "APFC" and "DNA," is a comprehensive device fingerprinting engine. It collects 48 distinct browser characteristics from each visitor. These include standard fingerprinting vectors like screen resolution, installed fonts, WebGL renderer information, and timezone. But the system goes deeper. It feeds into a telemetry pipeline alongside the extension scan results, creating a composite identity profile that can be matched against LinkedIn's user database. Because LinkedIn already knows your real name, employer, and job title from your profile, the fingerprint is not anonymous. It is attributed to a specific person at a specific company.
The fingerprint data is encrypted before transmission using an RSA public key (identified internally as "apfcDfPK"), serialized to JSON, and stored on globalThis.apfcDf. This encrypted payload is then injected as an HTTP header into every subsequent API call you make during your LinkedIn session. Your fingerprint does not get sent once. It accompanies every interaction for the duration of your visit.
System 2: AED - Active Extension Detection
The second system is the core of the scandal. Active Extension Detection (AED) is a brute-force scanner that attempts to load a known internal file from each of 6,222 browser extensions using the Chrome fetch() API.
Chrome extensions can expose internal files to web pages through the web_accessible_resources field in their manifest.json. When an extension is installed and has exposed a resource, a fetch() request to chrome-extension://{id}/{file} will succeed. When the extension is absent, Chrome blocks the request. LinkedIn exploits this to test for each extension on the list.
The researchers found two scanning methods in the code. Method 1 is a parallel batch scan that fires all 6,222 fetch() requests simultaneously using Promise.allSettled(). Every request that resolves as "fulfilled" confirms the extension is installed. Method 2 is a staggered sequential scan with a configurable delay between each probe, designed to reduce visibility in network monitoring tools and lower CPU impact. A configuration parameter called staggerDetectionMs determines which method runs.
The scan can be deferred to requestIdleCallback, which delays execution until the browser is idle. The user sees no performance impact. The scan leaves no visible trace. Someone at LinkedIn has taken the time to identify a specific internal resource - a popup.html, an icon.png, a manifest.json, a sidebar.html - for each of the 6,222 extensions on the list. This is not automated guessing. This is painstaking, systematic cataloging.
// LinkedIn's parallel scan (simplified from production code)
async function scanExtensions() {
const detected = [];
const probes = extensionList.map(({id, file}) =>
fetch(`chrome-extension://${id}/${file}`)
);
(await Promise.allSettled(probes)).forEach((result, i) => {
if (result.status === "fulfilled") {
detected.push(extensionList[i].id);
}
});
return detected;
}
System 3: Spectroscopy - Passive DOM Scanning
The third system, internally called "Spectroscopy," is a passive detection engine that walks the entire DOM tree of the LinkedIn page. Many Chrome extensions inject elements into web pages - modified HTML, added scripts, altered attributes, UI overlays. When they do, the injected content often contains references to the extension's internal URL scheme (chrome-extension://).
The Spectroscopy function starts at the document root and recursively inspects every node. For text nodes, it checks whether the text contains chrome-extension://. For element nodes, it inspects every attribute value. When it finds a match, it extracts the 32-character extension ID from the URL. The results are fired as a SpectroscopyEvent through the same telemetry pipeline.
This dual approach is deliberate. AED catches extensions that are merely installed but do not modify the page. Spectroscopy catches extensions that actively inject content, even if they are not in LinkedIn's hardcoded list. Together, they form a comprehensive net. If you have a Chrome extension, LinkedIn will likely detect it through one system or the other.
The categories of sensitive personal data LinkedIn extracts from extension scanning. Infographic: BLACKWIRE
What LinkedIn Learns About You - and Why It Matters

LinkedIn knows your name, employer, and now what software you run. Photo: Unsplash
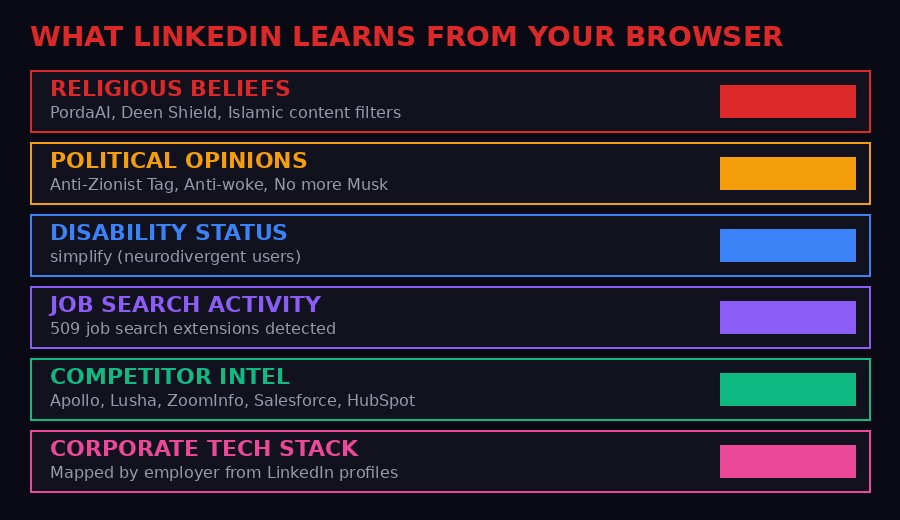
The extension list is not a random collection of browser add-ons. Fairlinked's analysis reveals that LinkedIn specifically scans for extensions that expose the most sensitive categories of personal information under EU law - categories that GDPR Article 9 explicitly classifies as "special category data" requiring explicit consent to process.
Religious Beliefs
LinkedIn scans for PordaAI, a Chrome extension that blurs haram content using real-time AI filtering aligned with Islamic values. It scans for Deen Shield, which blocks haram websites. If you use either of these tools, LinkedIn knows you are likely a practicing Muslim. The platform also scans for other faith-based content filters and religious study tools. This is not inferring religion from behavior. This is detecting the specific tools people install to practice their faith, and mapping that detection to their real name and employer.
Political Opinions
The scan list includes "Anti-Zionist Tag," an extension that tags content related to the Israeli-Palestinian conflict. It includes "Anti-woke," a political filtering tool. It includes "No more Musk," which filters Elon Musk-related content. Each of these is a political statement. The act of installing them reveals a user's political orientation. LinkedIn now has a database mapping political opinions to real identities at real companies. In some countries and contexts, this information could put people at physical risk.
Disability and Neurodivergence
"simplify" is a Chrome extension designed specifically for neurodivergent users. It reduces visual complexity on web pages. If LinkedIn detects it on your browser, LinkedIn knows - or can strongly infer - that you have a cognitive disability or neurodivergent condition. This is health data. Under GDPR, processing health data without explicit consent is not just an infringement. It is prohibited.
Job Search Activity
Here is where the corporate malice becomes impossible to deny. LinkedIn scans for 509 job search extensions. Five hundred and nine. These tools help people search for jobs, organize applications, track interviews, and manage their career transitions. If LinkedIn detects any of them on your browser, LinkedIn knows you are looking for a new job. Your current employer, who may also be on LinkedIn, does not know. But Microsoft does.
Consider the power dynamic. LinkedIn is the platform where your current employer sees your profile, where recruiters find you, where professional reputation lives and dies. And LinkedIn is secretly recording which of its users are planning to leave their jobs. That is not a privacy violation. That is leverage.
Competitor Intelligence and Trade Secret Theft
LinkedIn scans for over 200 products that directly compete with Microsoft's own sales and CRM tools. Apollo. Lusha. ZoomInfo. Salesforce. HubSpot. Pipedrive. Because LinkedIn knows where each user works, detecting these extensions does not just reveal individual preferences. It maps which companies use which competitor products. LinkedIn is extracting the customer lists of thousands of software companies from their users' browsers, without the software companies' knowledge and without the users' consent.
Fairlinked reports that LinkedIn has already weaponized this intelligence. The organization documents cases where LinkedIn sent enforcement threats to users of third-party tools, using data obtained through covert extension scanning to identify its targets. This transforms the scan from passive data collection into an active competitive weapon.
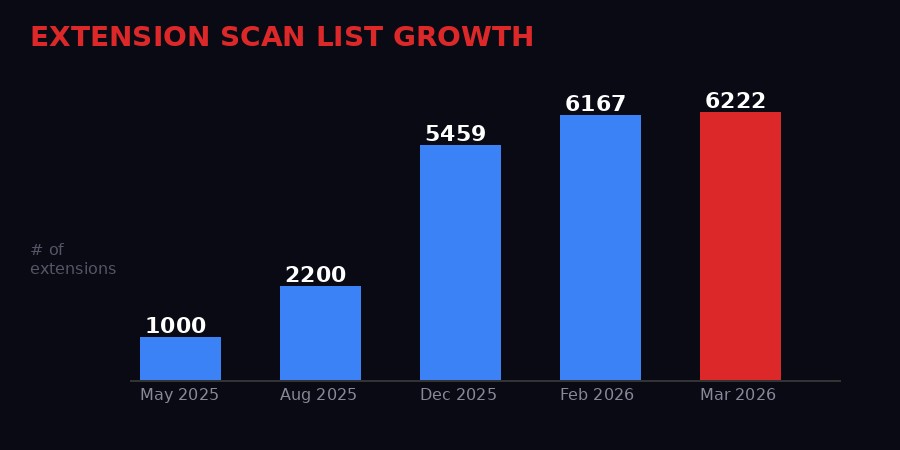
LinkedIn's extension scan list has grown 6x in under a year. Infographic: BLACKWIRE
The Acceleration: From 1,000 to 6,222 in Ten Months

The scan list is growing exponentially. Photo: Unsplash
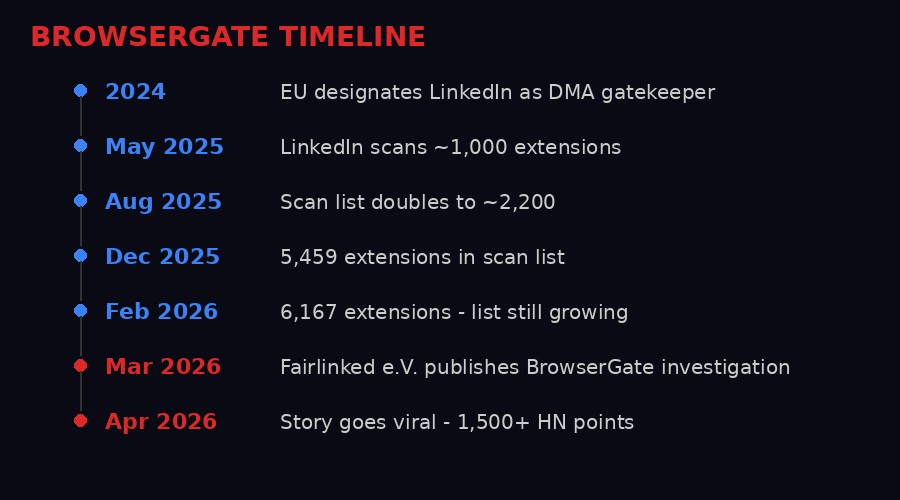
One of the most alarming aspects of the BrowserGate investigation is the pace at which LinkedIn's surveillance operation is expanding. Fairlinked documented the extension list across multiple time periods by analyzing archived versions of LinkedIn's JavaScript bundles. The growth curve tells a story of an operation that is not winding down - it is ramping up at accelerating speed.
In May 2025, LinkedIn's hardcoded extension list contained roughly 1,000 entries. By August 2025, it had doubled to approximately 2,200. By December 2025, the number reached 5,459. By February 2026, it stood at 6,167. When Fairlinked published their investigation in March 2026, the count had reached 6,222. The array alone occupies roughly 409,000 characters of source code inside the JavaScript bundle.
This is not the behavior of a company running a limited security check. This is the behavior of a company that has assigned engineers to systematically catalog the Chrome Web Store, identify web-accessible resources in each extension, and expand its surveillance net month after month. Every new entry in the list represents someone at LinkedIn making a deliberate decision to add another extension to the scan. Someone is maintaining this list. Someone is approving its growth. Someone decided that scanning for an Islamic content filter was a good idea.
The combined user base of the 6,222 scanned extensions is approximately 405 million people. LinkedIn has approximately 1 billion registered users. Even accounting for overlap and inactive accounts, the intersection is enormous. Hundreds of millions of people have been silently scanned. The data has been collected, encrypted, and transmitted. It cannot be unscanned. The damage is already done.
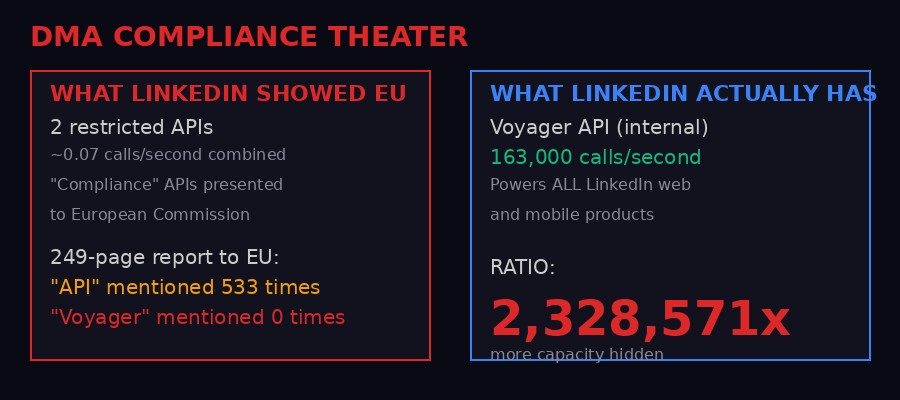
LinkedIn's compliance charade exposed: 0.07 calls/sec shown to EU vs 163,000 calls/sec hidden. Infographic: BLACKWIRE
The EU Charade: Compliance Theater at Industrial Scale

The EU designated LinkedIn as a gatekeeper under the Digital Markets Act. LinkedIn's response was theatrical. Photo: Unsplash
In 2024, the European Union designated LinkedIn as a regulated gatekeeper under the Digital Markets Act (DMA). The DMA exists specifically to prevent dominant platforms from abusing their market position. Under DMA Article 6(10), gatekeepers must provide business users and authorized third parties "free, effective, high-quality, continuous and real-time access" to platform data. In plain language: LinkedIn was legally required to open up to third-party tools.
What LinkedIn did instead is a masterclass in regulatory deception.
Microsoft published two restricted APIs and presented them to the European Commission as compliance. Fairlinked's investigation reveals these APIs handle approximately 0.07 API calls per second combined. Meanwhile, LinkedIn already operates an internal API called Voyager that powers every single LinkedIn web and mobile product. Voyager processes approximately 163,000 calls per second. That is not a rounding error. Voyager handles 2,328,571 times more traffic than the "compliance" APIs LinkedIn presented to EU regulators.
In Microsoft's 249-page compliance report submitted to the European Commission, the word "API" appears 533 times. The word "Voyager" appears zero times. Microsoft did not mention the existence of the API that actually runs LinkedIn. They built a Potemkin village of compliance tools, showed it to Brussels, and continued operating the real system behind closed doors.
But the deception goes further. At the same time LinkedIn was performing compliance theater for EU regulators, it was actively expanding its surveillance of the exact tools the DMA was designed to protect. The extension scan list grew from roughly 461 products in 2024 to over 6,000 by February 2026. The EU told LinkedIn to let third-party tools in. LinkedIn built a surveillance system to find and punish every user of those tools.
Fairlinked documents cases where LinkedIn identified users of third-party LinkedIn tools through extension scanning and then sent them enforcement threats. This is the digital equivalent of a company that is ordered by a court to allow competitors into its market, then installs hidden cameras at every entrance to identify and intimidate anyone who walks in.
The Third-Party Pipeline: HUMAN Security and the Invisible Tracking

Your scan data travels through encrypted channels to LinkedIn's servers and beyond. Photo: Unsplash
The data collected by LinkedIn's scanning operation does not stay within Microsoft's systems. The investigation reveals that LinkedIn loads an invisible tracking element from HUMAN Security, an American-Israeli cybersecurity firm formerly known as PerimeterX. This element is zero pixels wide, hidden off-screen, and sets cookies on your browser without your knowledge.
HUMAN Security specializes in bot detection and fraud prevention. On its face, this relationship might seem benign - a platform using a security vendor to detect automated abuse. But the implementation tells a different story. The invisible tracking element is loaded alongside the extension scanning code. The fingerprinting data - including information about which extensions you have installed - feeds into the same telemetry pipeline. A separate fingerprinting script runs from LinkedIn's own servers. A third script from Google executes silently on every page load.
All of it is encrypted. None of it is disclosed.
The transmission pathway is documented in LinkedIn's code. Detected extension IDs are packaged into AedEvent and SpectroscopyEvent tracking payloads and sent to LinkedIn's li/track endpoint. The transport layer batches up to 29 events per request, retries up to 4 times on failure, and supports LZ-based compression before transmission. The encrypted fingerprint is also sent to two dedicated endpoints: /platform-telemetry/li/apfcDf and /apfc/collect.
The involvement of HUMAN Security raises significant questions about cross-border data transfers. HUMAN Security is headquartered in New York with significant operations in Israel. The extension scan data of EU citizens - including data revealing religious beliefs, political opinions, and health conditions - is being transmitted to servers operated by a company subject to neither EU data protection jurisdiction nor the GDPR's adequacy framework for the US (which remains legally contested after the Schrems II ruling effectively invalidated Privacy Shield in 2020, though its successor, the EU-US Data Privacy Framework, faces ongoing legal challenges).
LinkedIn's privacy policy makes no mention of extension scanning. It makes no mention of data transmission to HUMAN Security in this context. It makes no mention of the fingerprinting system that accompanies every API call for the duration of your session. Under GDPR's transparency requirements (Articles 13 and 14), data controllers must inform subjects about the purposes of processing, the categories of data collected, and any recipients or categories of recipients. LinkedIn has disclosed none of this.
The Legal Exposure: Criminal Territory in Multiple Jurisdictions

The legal consequences stretch across criminal, civil, and regulatory domains. Photo: Unsplash
Fairlinked's legal analysis concludes that LinkedIn's extension scanning is "illegal and potentially a criminal offense in every jurisdiction we have examined." This is not hyperbole. The legal exposure is staggering, crossing multiple regulatory frameworks simultaneously.
GDPR Article 9: Processing Prohibited Data
Under the GDPR, data revealing religious beliefs, political opinions, and health conditions is classified as "special category data." Processing this data is not merely regulated - it is prohibited unless one of a narrow set of exceptions applies. The most common exception is explicit consent. LinkedIn has no consent. It has no disclosure. The extension scanning system is not mentioned anywhere in LinkedIn's public-facing documentation.
The maximum penalty for GDPR violations is 4% of global annual turnover or 20 million euros, whichever is greater. Microsoft's annual revenue for fiscal year 2025 was approximately $245 billion. Four percent of that is $9.8 billion. But the penalties could compound. Each undisclosed processing activity, each category of prohibited data, each jurisdiction where the violation occurred could be treated as a separate infringement. Irish Data Protection Commission (LinkedIn's EU lead supervisor), French CNIL, German state DPAs - all could pursue separate enforcement actions.
Digital Markets Act Non-Compliance
LinkedIn's behavior does not just violate the DMA. It inverts it. The DMA requires gatekeepers to provide access to third-party tools. LinkedIn is using extension scanning to identify and punish users of those tools. DMA fines can reach 10% of global turnover for systematic non-compliance - roughly $24.5 billion in Microsoft's case. For repeat offenses, the European Commission can impose structural remedies, including forced divestitures.
Computer Fraud and Unauthorized Access
In multiple jurisdictions, the act of scanning someone's computer for installed software without authorization may constitute unauthorized access to a computer system. In the UK, the Computer Misuse Act 1990 makes it a criminal offense to access a computer system without authorization. In Germany, Section 202a of the Criminal Code (Ausspaeher von Daten) criminalizes unauthorized access to data. In the US, the Computer Fraud and Abuse Act could apply to the scanning of browser extensions without user consent.
These are not civil penalties. These are criminal statutes. The individuals who designed, approved, and deployed the scanning system could face personal criminal liability in multiple countries.
Trade Secret Misappropriation
By mapping which companies use which competitor products through extension scanning, LinkedIn is extracting trade secrets - customer lists - from thousands of software companies. The EU Trade Secrets Directive (2016/943) and the US Defend Trade Secrets Act provide both civil and, in some jurisdictions, criminal remedies for trade secret theft. Companies like Apollo, Lusha, ZoomInfo, Salesforce, and HubSpot may have grounds for massive damages claims against Microsoft.
Timeline of LinkedIn's extension scanning operation and its exposure. Infographic: BLACKWIRE
The Microsoft Pattern: Azure, Trust, and Institutional Decay

BrowserGate is not an isolated incident. It reflects a pattern across Microsoft's operations. Photo: Unsplash
BrowserGate does not exist in a vacuum. It lands alongside a separate, devastating expose from a former Azure Core engineer that describes systematic technical mismanagement at Microsoft's cloud division. The account, published on Substack under the title "How Microsoft Vaporized a Trillion Dollars," describes an engineering culture where 173 separate agents were deployed to manage Azure nodes despite nobody being able to articulate why they existed, where teams planned to port half of Windows to a tiny ARM SoC that could barely handle the task, and where internal warnings about fundamental architectural problems were systematically ignored.
The former engineer describes joining the Overlake R&D team on his first day and witnessing a planning meeting where senior engineers seriously discussed porting Windows user-mode and kernel components to the Azure Boost accelerator card - a device with 4KB of dual-ported FPGA memory and a power budget the size of a fingernail. The engineer writes that "the stack was hitting its scaling limits on a 400 Watt Xeon at just a few dozen VMs per node" and that the team was "so far from reality" that his day-one problem was convincing an entire organization that they were on a death march.
This matters for BrowserGate because it illuminates the institutional culture that produced the extension scanning operation. Both scandals share the same DNA: a company where growth and control are prioritized over ethics and technical coherence. Where regulatory compliance is treated as a performance to be staged rather than a constraint to be honored. Where the people who raise concerns are ignored or pushed out while the people who build surveillance systems are promoted.
The Azure story also directly implicates the security of the systems that BrowserGate's data flows through. If Azure's node management involves 173 unexplained agents running on fragile, poorly understood infrastructure, what happens to the encrypted extension scan data once it reaches LinkedIn's servers? How secure is the pipeline that transmits the religious beliefs, political opinions, and disability status of a billion people? The same institutional dysfunction that produced Azure's engineering problems is the institutional context in which LinkedIn's surveillance operation was conceived, approved, and deployed.
What Happens Next: The Regulatory Collision

Fairlinked e.V. is preparing class action suits across multiple EU jurisdictions. Photo: Unsplash
Fairlinked e.V. is not just documenting the problem. They are building a legal offensive. The organization has entered a regulatory dialogue with the European Commission about LinkedIn's DMA compliance. They are preparing class action suits in multiple countries and jurisdictions. They have built a Chrome extension that documents LinkedIn's scanning behavior with tamper-proof timestamps, creating an evidence base that grows with each installation. They are accepting co-plaintiff registrations for users who want to participate in legal proceedings.
The regulatory collision is approaching from multiple directions simultaneously.
The Irish Data Protection Commission, LinkedIn's lead EU supervisory authority, will face mounting pressure to investigate. The DPC has been criticized for slow enforcement against Big Tech, but BrowserGate's evidence is unusually concrete. This is not a dispute about algorithm transparency or consent flow design. LinkedIn's production JavaScript code contains the scanning system in plaintext. The extension list is hardcoded. The telemetry endpoints are documented. The evidence is the code itself.
The European Commission's DMA enforcement team will need to reconcile LinkedIn's compliance theater with the reality of a platform that expanded its surveillance of third-party tools while presenting sham APIs to regulators. The Commission has the power to impose fines of up to 10% of global turnover and, in extreme cases, to order structural remedies including forced divestitures. Ordering Microsoft to divest LinkedIn would be an unprecedented step - but the combination of DMA non-compliance and active subversion of the regulation's intent makes it a realistic possibility in the worst case.
National data protection authorities across the EU are likely to receive waves of individual complaints. Fairlinked is building country-specific, pre-filled complaint forms for every EU/EEA data protection authority. The more complaints each DPA receives, the harder BrowserGate is to ignore. GDPR's one-stop-shop mechanism theoretically routes all complaints through the Irish DPC, but national authorities retain the power to act on urgent matters and can refer cases to the European Data Protection Board.
In the US, the Federal Trade Commission may take interest, particularly given the trade secret theft angle and the involvement of HUMAN Security as a third-party data recipient. State-level privacy laws in California (CCPA/CPRA), Colorado, Connecticut, and Virginia could provide additional enforcement vectors. Class action litigation in US courts - where damages for privacy violations can scale quickly with billion-user platforms - is nearly certain.
Microsoft's response so far has been silence. LinkedIn has not commented on the BrowserGate investigation. Microsoft has not addressed the allegations. No public statement has been issued acknowledging or denying the extension scanning system. Given that the scanning code is visible to any developer who opens their browser's developer tools on linkedin.com, denial is not a viable strategy. The question is whether Microsoft will attempt to characterize the scanning as a legitimate security measure (which the breadth and sensitivity of the data collected makes implausible) or quietly remove the code while hoping the story fades (which the scale of regulatory and legal exposure makes unlikely).
What You Can Do Right Now
- Check if your extensions are scanned: Search the full database of 6,222 extensions at browsergate.eu/extensions
- File a GDPR request: Ask LinkedIn specifically for extension detection data, device fingerprinting data, and records transmitted via AedEvent and SpectroscopyEvent tracking systems
- Use Firefox: The scanning system targets Chrome-based browsers. Firefox extensions use a different URL scheme and are not affected by this specific attack
- File a complaint: Contact your national data protection authority. The more complaints the Irish DPC receives, the harder this is to ignore
- Support the legal fight: Fairlinked e.V. is accepting donations at browsergate.eu to fund legal proceedings against Microsoft
The Second-Order Effects Nobody Is Talking About
The immediate story - LinkedIn scans your browser, that is bad - is alarming enough. But the second-order implications are where this gets truly dangerous.
Insurance and employment discrimination. LinkedIn's extension scan data could reveal disability status (neurodivergent extensions), mental health conditions (anxiety and depression management tools), and chronic illness management tools. If this data leaks, is subpoenaed, or is shared with third parties beyond HUMAN Security, it could be used to discriminate in insurance underwriting and employment decisions. LinkedIn already knows where you work. Now it knows whether you are managing a disability. The potential for automated discrimination at scale is unprecedented.
Government surveillance bootstrapping. National security agencies have historically sought to leverage corporate data collection for surveillance purposes. LinkedIn's extension scanning creates a pre-built database mapping political opinions and religious beliefs to real identities. In countries where LinkedIn operates but civil liberties protections are weak - Russia (before the recent Apple cutoff), China, Turkey, the UAE - this data could be weaponized by authoritarian governments to identify dissidents, religious minorities, and political opponents.
Chilling effect on extension development. If users learn that installing a Chrome extension exposes them to corporate surveillance, extension adoption will decline. This damages the entire Chrome Web Store ecosystem and undermines the browser extension model that has been a cornerstone of web innovation since Firefox popularized the concept in the mid-2000s. Developers who build privacy tools, accessibility aids, and productivity extensions will see their user bases shrink not because their products are bad, but because using them has become a surveillance risk.
Precedent for other platforms. If LinkedIn can silently scan your browser for 6,222 extensions without legal consequence, every other website can too. Facebook, Google, Amazon, and every ad-tech company in the world is watching how regulators respond to BrowserGate. A weak or slow enforcement response will be interpreted as tacit permission. The extension scanning technique is not proprietary. Any website with a JavaScript bundle can do it. The only barrier is willingness - and LinkedIn has just demonstrated that willingness exists.
Trust destruction in professional networking. LinkedIn's value proposition depends on users voluntarily sharing professional information. The platform works because people trust it enough to publish their real names, employers, and career histories. BrowserGate fundamentally breaks that trust compact. Users shared their professional data on the understanding that it would be used for networking and job matching. They did not consent to their browsers being searched for evidence of their religion, politics, and disabilities. Once trust is broken at this level, it does not recover. It migrates to competitors.
The Bigger Question
BrowserGate is not really about LinkedIn. It is about the fundamental assumption that underlies every interaction on the modern web: that a website will render content in your browser and nothing more. LinkedIn has shattered that assumption. When you visit linkedin.com, you are not loading a web page. You are submitting to an interrogation. Your browser is being searched. Your extensions are being cataloged. Your religion, politics, and health status are being inferred, encrypted, and transmitted to servers you never agreed to interact with.
The question regulators now face is whether this is the new normal or the line that finally gets enforced. The GDPR was designed for exactly this scenario. The DMA was designed for exactly this scenario. The legal frameworks exist. The evidence is public. The code is readable. There are no ambiguities to hide behind.
Microsoft has 33,000 employees and a $15 billion legal budget. But as Fairlinked puts it: there are one billion LinkedIn users. And now they have the code.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram