The Surveillance State Can't Keep Its Own Secrets

Someone posted the door codes to a US Border Patrol facility on Quizlet. A public flashcard platform. The kind of site middle schoolers use to study vocab tests.
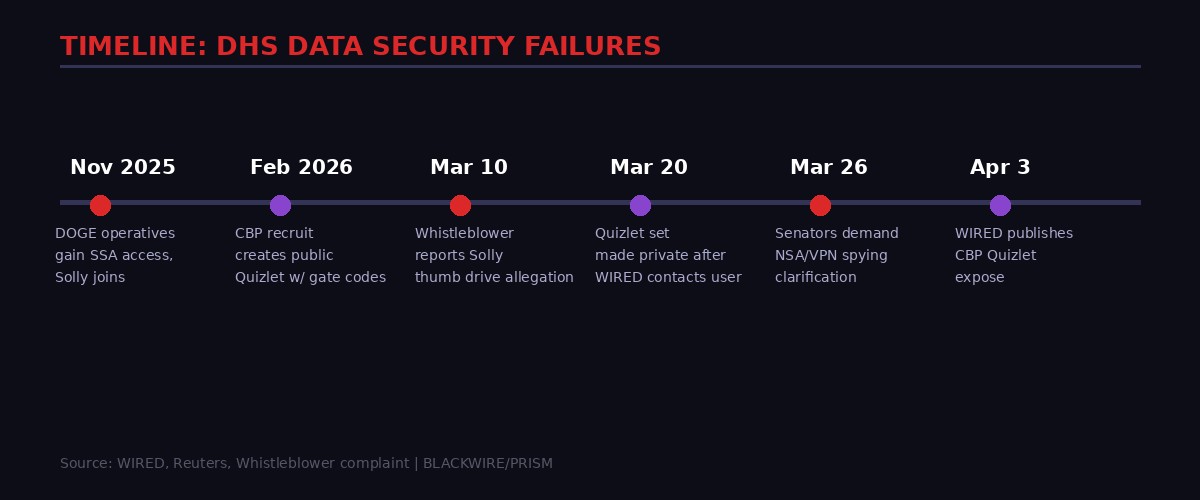
Not metaphorically. Literally. A flashcard set titled "USBP Review" - discovered by WIRED through basic Google keyword searches - contained what appear to be specific four-digit combinations for facility entrances, gate codes, and checkpoint doors at Customs and Border Protection locations around Kingsville, Texas. It sat publicly accessible for weeks before being made private, about thirty minutes after WIRED contacted a phone number potentially linked to the creator. (WIRED, April 3, 2026)
This is not an isolated incident. It is a pattern. And the pattern is getting harder to ignore.
At the same moment DHS is deploying AI-powered surveillance networks across American cities, ICE is operating facial recognition at scale, and Congress is debating whether VPN use gives the NSA license to spy on American citizens - the agencies building that surveillance machine are leaking their own operational secrets through basic operational security failures so mundane they beggar belief.
The question is not whether classified information ended up on Quizlet. The question is: what does it mean for the credibility of the surveillance state when the surveillors cannot practice what they preach?

The Quizlet Problem: When Study Tools Become Security Threats
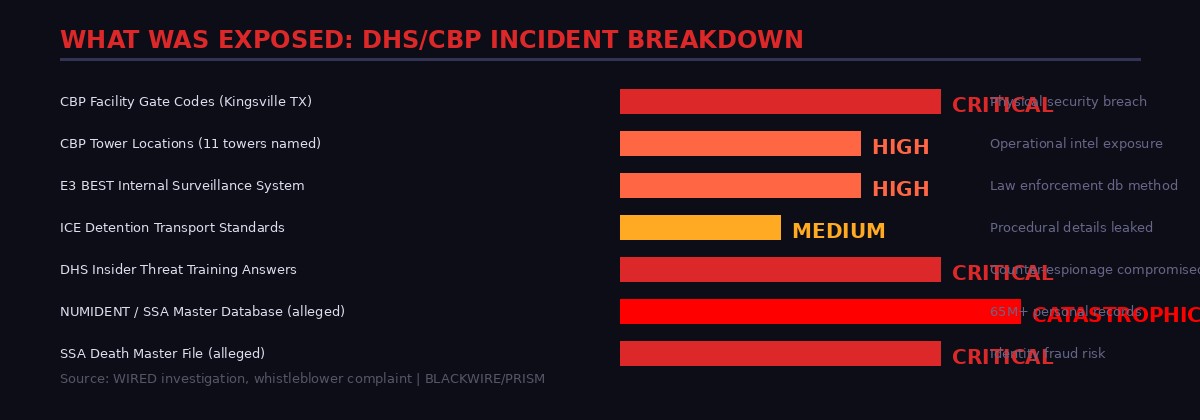
The scope of what ended up in the Kingsville Quizlet set is genuinely alarming once you catalog it systematically. This was not one rogue data point. It was a comprehensive operational briefing, converted into flashcard format, left publicly accessible on one of the world's most-indexed educational platforms.
The set documented: specific four-digit codes for facility entrance doors, codes for multiple named checkpoint gates (which WIRED declined to publish), the 1,932-square-mile area of responsibility for the Kingsville sector, the names and locations of 11 CBP "towers" in the region, the agency's internal grid and zone organizational system (including a note that one grid "does not exist" due to highway layout), and the internal "E3 BEST" surveillance system used to query suspects simultaneously across multiple law enforcement databases.
"This incident is being reviewed by CBP's Office of Professional Responsibility," a CBP spokesperson told WIRED. "We will not be getting ahead of this review. A review should not be taken as an indication of wrongdoing."
That statement requires translation. What CBP is saying is: we do not yet know if this was an active agent, a contractor, or a civilian. What they are not saying is whether those gate codes have been changed. Whether the towers have been repositioned. Whether the E3 BEST system has been audited for unauthorized access since the exposure.
The set went private on March 20th, less than thirty minutes after WIRED made contact. It had been live for weeks. Anyone with a Google search could have found it. WIRED's investigation found this was not the only set. Multiple apparent DHS recruits had created public Quizlet flashcards covering ICE detention transport standards, DHS insider threat training questions (complete with answer keys), CBP body camera policies, and immigration law procedures - all discoverable through basic keyword searches with no account required.
"We take reports of sensitive or inappropriate content seriously and act promptly when content is found to violate our policies. We encourage anyone who encounters concerning material to report it directly from the flashcard set, class, or profile page." - Quizlet spokesperson statement to WIRED
That is the wrong answer. Quizlet is not the problem here. The problem is that CBP and DHS apparently have no system to monitor whether their agents are posting operational data to publicly accessible platforms. No content policy training that stuck. No automated detection. Nothing. WIRED found the exposure through basic Google searches. CBP's own security apparatus did not.
The Thumb Drive: DOGE's Most Explosive Allegation
The CBP Quizlet incident would be alarming on its own. But it arrived alongside a potentially far more serious allegation involving the Department of Government Efficiency's access to the Social Security Administration.
John Solly, a software engineer who served as one of approximately 12 DOGE operatives embedded at SSA, is named in a whistleblower complaint filed with SSA's Office of the Inspector General. The complaint, first reported by the Washington Post and subsequently confirmed with additional details by WIRED, alleges that Solly told coworkers he had stored copies of two of the most sensitive databases in the federal government on a thumb drive. (WIRED, March 12, 2026)
The databases in question: NUMIDENT, SSA's master file containing every Social Security number application filed in the United States - full names, birth dates, race, and more personally identifiable information for tens of millions of Americans - and the Death Master File, an SSA database of deceased persons' Social Security records maintained specifically to prevent identity fraud.
The whistleblower further alleges that Solly sought help "sanitizing" the data before sharing it with his new employer. Solly left SSA and subsequently became Chief Technology Officer of the health IT division at Leidos, a major government contractor that holds an estimated $1.5 billion in SSA contracts signed in 2023. The complaint alleges he believed he would receive a presidential pardon if his actions were found to be illegal.
Solly's legal counsel denied the allegations forcefully. Leidos conducted an internal investigation that included "advanced digital forensics" and said it found no evidence Solly had ever plugged a thumb drive or external storage device into his company-issued laptop. SSA itself dismissed the complaint. Multiple named parties - SSA, Solly, and Leidos - have all denied the allegations.
The investigation continues. But the allegation alone reveals something important about the DOGE model of government access: when you give a private individual with private-sector employment prospects root-level access to the most sensitive government databases in the country, the theoretical attack surface for data exfiltration becomes enormous. Whether or not this specific complaint has merit, the architecture of access that made it possible remains in place.

Firing the Watchdogs: DHS Removes Its Own Privacy Officers
A functioning security apparatus requires internal accountability. When agents leak operational data, there should be mechanisms to catch and correct it. When political appointees attempt to misuse government records, career professionals with oversight responsibilities should be able to object.
DHS has been systematically dismantling those mechanisms.
According to WIRED's reporting, Department of Homeland Security leadership removed top privacy officers who objected to what they described as "illegal" orders - specifically, orders to mislabel government records in ways that would block their release under Freedom of Information Act requests. The privacy officers flagged the practice. They were ousted.
This is not a footnote. This is the operating system of institutional failure. When the people whose job it is to object to improper data handling are removed for objecting to improper data handling, every subsequent failure becomes more likely.
The Quizlet incident happens in an environment where oversight is weakened. The DOGE thumb drive allegation happens in an environment where normal controls around data access have been suspended in the name of efficiency. These events are connected not by conspiracy but by atmosphere - a culture that has systematically prioritized expansion of access over security of that access.
"An attacker who already holds operator.pairing scope - the lowest meaningful permission in a deployment - can silently approve device pairing requests that ask for full administrative access. Once that approval goes through, the attacking device holds full administrative control. No secondary exploit is needed. No user interaction is required." - Blink security researchers, describing a structural access-control failure in AI agent systems (CVE-2026-33579) that mirrors DHS's own internal access failures
The parallel is instructive. Whether we are talking about a Border Patrol recruit putting gate codes on Quizlet, or a DOGE operative allegedly walking out with SSA records, or an AI agent tool that let anyone with minimal permissions silently escalate to admin control - the failure mode is identical. Insufficient verification at the point of access. No monitoring of what happens after access is granted. Accountability mechanisms either absent or actively dismantled.
The VPN Trap: When Your Privacy Tool Flags You as a Target
The surveillance security failure is not only internal. There is a parallel problem in how NSA and related agencies have structured the legal basis for mass surveillance - and it is creating an absurd situation where following government advice on digital security might void your constitutional rights.
Six Democratic senators sent a letter on March 26th to Director of National Intelligence Tulsi Gabbard demanding clarification on a specific question: Does using a VPN cause Americans to lose their Fourth Amendment protections against warrantless government surveillance? (WIRED, March 26, 2026)
The concern is not hypothetical. Under Section 702 of the Foreign Intelligence Surveillance Act - the program authorizing the NSA to collect communications of foreign targets, which also sweeps in vast quantities of American communications - and under Executive Order 12333, the NSA operates under a default presumption: if the location of a communications source is unknown, that source is presumed to be non-American.
VPNs work by routing user traffic through servers that may be located anywhere in the world. Those servers carry traffic from thousands of simultaneous users. To an intelligence agency conducting bulk collection, an American connected to a VPN server in Amsterdam is indistinguishable from a Dutch citizen. The American's communications may then be collected under authorities that require no warrant and no specific suspicion.
The irony is sharp. The NSA, FBI, and Federal Trade Commission have all officially recommended that Americans use VPNs to protect their privacy. If those lawmakers' concern is correct, following that advice may be precisely what strips Americans of the privacy protections they are trying to maintain.
Section 702 was facing expiration in April. The battle over its renewal became one of the sharpest debates in Congress, with a bipartisan coalition pushing to require warrants for FBI access to collected American communications and to ban federal purchase of commercial data on US residents.
The outcome of that fight will determine whether the legal framework for mass surveillance gets reformed or extended in its current form. But the VPN question exposes something deeper: the rules governing who counts as a surveillance target were written before commercial VPN adoption became widespread. The law has not kept up with the technology. That gap, like the gaps in CBP's opsec training, is something that exploits write themselves.

The Recruitment Surge and the Security Gap
Context matters for the CBP Quizlet exposure. The Department of Homeland Security is in the middle of one of the most aggressive law enforcement hiring campaigns in its history.
CBP is offering up to $60,000 in recruitment and retention incentives for new agents. ICE is offering $50,000 signing bonuses plus up to $60,000 in student loan repayment. Both agencies are processing thousands of new hires simultaneously, running accelerated training programs, and pushing people into operational roles faster than traditional onboarding timelines allowed. (GAO report on CBP hiring surge)
In that environment, the Quizlet incident is almost overdetermined. New recruits, unfamiliar with opsec culture, studying for training exams using the tools they have always used for studying. The tools happen to be public by default. The flashcards happen to contain operational security codes. Nobody flagged it until a journalist found it through Google.
This is what institutional security culture actually looks like when stripped to its skeleton: individual agents making individual decisions about how to study for their tests, with no ambient culture of information security, no technical controls preventing operational data from entering public platforms, and no monitoring system to catch it when it happens.
The rapid hiring surge has a second consequence beyond the opsec risk. The whistleblower complaint that named Solly noted that he allegedly told coworkers he expected a presidential pardon if caught. That expectation - that political protection would insulate technical violations of law - reflects an environment where accountability structures are perceived as inoperative. You do not say that in an organization with a functioning internal accountability culture. You say it when you believe the rules have been suspended.

Pattern Recognition: What the Failures Have in Common
Step back from the individual incidents and the structure becomes clear. The CBP Quizlet exposure, the DOGE thumb drive allegation, the firing of DHS privacy officers, the VPN surveillance paradox - these are not separate stories. They are facets of a single problem.
The problem is this: the United States government is simultaneously expanding its surveillance capabilities at historic speed and degrading its capacity to apply those capabilities safely, legally, or with meaningful accountability.
The expansion side is well-documented. ICE is using real-time facial recognition in American cities. CBP is deploying AI-powered analytics to monitor border crossings. DOGE operatives gained access to financial, benefits, and identity databases that career civil servants typically require years of vetting to touch. The NSA's collection authorities were being debated for renewal in their current form. The infrastructure for mass surveillance is growing fast.
The degradation side is the story that is easier to miss. DHS fired its privacy officers. The accountability function at CBP is being invoked to investigate a Quizlet incident rather than proactively prevent the next one. The legal framework governing who counts as a surveillance target has not been updated to account for VPN adoption. DOGE's model of rapid access by politically-connected private individuals created a scenario where, whatever the facts of the Solly case, the theoretical risk of data exfiltration was built into the architecture from day one.
"An attacker with the lowest permission level can gain full administrative access. The authentication gate that is supposed to slow this down does not exist." - Blink security researchers, April 2026, on CVE-2026-33579 - a structural failure that mirrors DHS's own access control environment
Security researchers have a term for this: the attack surface has expanded faster than the defense perimeter. When you add capabilities faster than you add controls, you do not get a more secure system. You get a more powerful system that is easier to exploit. The failures are not bugs in the expansion. They are features of it.

The Second-Order Effects: Who Benefits From These Failures?
The most important question is not who leaked what. It is who can use what was leaked, and what the downstream consequences look like.
The CBP gate codes in the Quizlet set are the most immediately actionable piece of exposed data. If those codes have not been changed - and CBP has not publicly stated that they have been - then any actor who downloaded that Quizlet set before March 20th has physical access parameters for a US border facility. That is not a theoretical vulnerability. It is a current operational risk. The Kingsville sector processes significant cross-border traffic. Checkpoint penetration has been a documented objective of organized crime networks operating along the Texas border for decades.
The E3 BEST system documentation is more subtle but potentially more durable as a risk. Knowing the internal structure of the system CBP uses to query suspects across multiple law enforcement databases - how events are created, how referrals are processed, what triggers arrest - is the kind of information that could help a sophisticated actor understand how to evade or manipulate that system. It is operational intelligence about the surveillance apparatus itself.
The NUMIDENT and Death Master File allegations, if true, represent a categorically different order of magnitude. NUMIDENT contains personally identifiable information for tens of millions of Americans. The Death Master File contains records of deceased persons maintained specifically to prevent their identities from being used for fraud. A complete export of either database, in the hands of a private sector actor with no public accountability, would represent an unprecedented breach of federal data stewardship. The allegations are denied by all named parties. But the allegation itself reflects the risk architecture of the DOGE model.
The VPN spying question carries its own second-order effect that is easy to underestimate. If millions of Americans who use VPNs are being treated as foreign intelligence targets under existing surveillance authorities, their communications - including with lawyers, journalists, political organizers, religious communities, and medical providers - may have been collected under programs with far less oversight than domestic surveillance requires. The senators asking Gabbard to clarify the issue are not asking an abstract legal question. They are asking whether a significant slice of American civil society has been placed under surveillance without anyone saying so explicitly.

The Reform Window: What Would Actually Fix This
None of these problems are without solutions. The solutions just require prioritizing security over speed - something the current operating environment has consistently deprioritized.
For the CBP Quizlet problem: automated monitoring of public platforms for operational keywords is technically trivial. Security training that explicitly addresses study tool opsec is not complicated to implement. Regular audits of whether gate codes, internal system names, and grid designations match what is circulating on publicly accessible platforms would catch most of what WIRED found through basic Google searches. None of this requires new technology. It requires organizational will.
For the DOGE access model: the core problem is that private individuals with private-sector employment prospects were given root-level access to government databases with essentially no separation of duties between access and accountability. Normal federal data access involves compartmentalization, audit trails, and multi-person authorization for export. Restoring those controls does not require reversing any policy on government efficiency. It requires applying to DOGE operatives the same controls applied to career civil servants.
For the VPN surveillance paradox: the statutory fix is relatively straightforward. Update the presumption of foreignness in NSA targeting procedures to account for commercial VPN use. Or require the intelligence community to publicly disclose the extent to which VPN-routed American traffic has been collected under foreign surveillance authorities. Senator Wyden has been trying to force this disclosure for months. The resistance comes not from technical difficulty but from the intelligence community's institutional preference for opacity.
For the broader accountability gap: DHS needs privacy officers who can object to illegal orders without losing their jobs for doing so. That is not a complicated policy. It is a minimal condition for functioning institutional governance. The fact that it currently does not exist in practice is the most alarming detail in this entire set of incidents.

The Credibility Problem
There is a deeper issue underneath all of this that no technical fix addresses directly: the credibility of the institutions doing the surveilling.
Surveillance, as a legitimate function of democratic governance, rests on a specific bargain. Citizens accept reduced privacy in certain domains, for certain purposes, under certain oversight conditions, because they trust that the institutions exercising surveillance power are competent, accountable, and operating within legal boundaries. The bargain is inherently faith-based - most people cannot independently verify what the NSA collects or how CBP uses its databases. They rely on institutional trustworthiness as a proxy.
Every incident in this pattern erodes that proxy. When CBP cannot prevent new recruits from posting facility codes on flashcard websites, it signals something about the overall competence of CBP's security culture. When a DOGE operative is alleged to have walked out with SSA master files and the response is to note that all parties denied wrongdoing, it signals something about the robustness of DOGE's accountability structure. When DHS fires the people who object to mislabeling records, it signals something about whether the accountability mechanisms are real or performative.
The surveillance apparatus does not just need to be secure. It needs to be trustworthy. Trustworthiness is not established by press releases denying allegations. It is established by demonstrably functioning security culture, intact accountability mechanisms, and institutions that treat internal failures as problems to fix rather than reputational threats to manage.
Right now, the evidence suggests the opposite dynamic is operating. The failures are being managed for optics. The accountability mechanisms are being dismantled. The oversight capacity is being fired. And the capabilities are being expanded regardless.
That combination - more power, less accountability, demonstrated incompetence at basic security - is not the profile of an institution that deserves the trust the surveillance bargain requires. The gate codes on Quizlet are not just an embarrassment. They are a signal.

What Comes Next
The Section 702 renewal battle will play out over the coming weeks, and its outcome will set the legal baseline for mass surveillance for years. The Solly whistleblower complaint is being reviewed by SSA's Inspector General, a process with no public timeline. CBP's Office of Professional Responsibility is reviewing the Quizlet incident with similarly no stated timeline for resolution or public report.
What is likely to happen, based on the pattern so far: the individual incidents will be processed quietly, the institutional changes needed to prevent recurrence will not be implemented, and the capabilities expansion will continue uninterrupted.
WIRED's investigation into the Quizlet exposure took basic Google keyword searches. It took under an hour. The finding - that CBP facility codes were publicly accessible on one of the most indexed platforms on the internet - was not the result of sophisticated research. It was the result of minimal effort applied to a public platform that DHS apparently was not watching.
If WIRED found it, anyone with an interest in it found it first.
The surveillance state wants to know everything about you. It has not yet demonstrated that it can keep basic secrets about itself. That asymmetry is not a minor operational issue. It is the structural condition of the current moment - and the implications reach considerably further than one Quizlet set in Kingsville, Texas.
Sources: WIRED (Sammy Sussman, April 3, 2026); WIRED (Vittoria Elliott / Makena Kelly, March 12, 2026); WIRED (Dell Cameron, March 26, 2026); CBP spokesperson statement to WIRED; Quizlet spokesperson statement to WIRED; Seth Waxman (Solly legal counsel) via WIRED; Leidos spokesperson Todd Blecher via WIRED; SSA spokesperson via WIRED; GAO CBP hiring surge report; Blink security researchers (CVE-2026-33579); Senators Wyden, Warren, Markey, Padilla, Jayapal, Jacobs letter to DNI Gabbard.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram