The Industrialized Threat: Cloudflare's 2026 Report Reveals 31 Tbps Attacks, Token Theft Killing MFA, and Nation-States Living Inside Your SaaS
Brute force is dead. The era of high-trust exploitation has arrived - and most organizations aren't even looking in the right place.

The modern threat landscape has shifted from brute force to high-trust exploitation. Photo: Pexels
The hacker in the hoodie is a fairy tale. The real threat actor in 2026 looks like your Google Calendar invite, your Dropbox shared folder, your Azure deployment, your new remote developer who passed the Zoom interview with flying colors. Cloudflare just told you exactly how bad it's gotten, and the numbers should make every CISO rethink their entire defensive posture.
On March 31, Cloudflare's elite threat intelligence unit Cloudforce One published its inaugural 2026 Threat Report, a document that reads less like a security advisory and more like a post-mortem on the entire concept of perimeter defense. The report synthesizes trillions of network signals into eight key findings that collectively describe a fundamental evolution: the industrialization of cyber threats. Attackers have abandoned the expensive, flashy zero-day game in favor of something far more dangerous - high-throughput exploitation of the trust relationships that hold modern enterprise infrastructure together.
The headline stats alone demand attention. A record 31.4 terabits-per-second DDoS attack. Ninety-four percent of all login attempts now originating from bots. Sixty-three percent of logins using credentials already compromised elsewhere. Nearly half of all emails failing DMARC authentication. Chinese state actors embedding themselves in American telecom networks. North Korean operatives using deepfakes to land six-figure remote tech jobs. And perhaps most alarmingly: a new attack paradigm where session token theft renders multi-factor authentication completely useless.
This isn't a forecast. This is a field report from the front lines of a war most organizations don't know they're already losing.
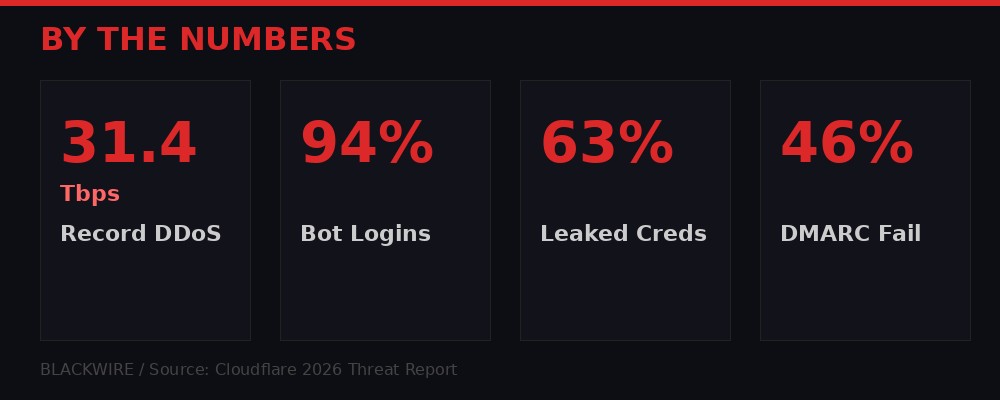
The numbers that define the 2026 threat landscape. Infographic: BLACKWIRE
The Death of the Perimeter: Measure of Effectiveness

Modern adversaries optimize for throughput, not sophistication. Photo: Pexels
Cloudflare introduces a concept that should become standard vocabulary in every security operations center: Measure of Effectiveness, or MOE. This is the cold, rational calculus that modern attackers apply to every potential vector. It's the ratio of effort to operational outcome, and it explains why the most dangerous threats in 2026 look nothing like what security teams were trained to detect.
Consider the economics. A zero-day exploit for a major platform costs anywhere from $500,000 to $2.5 million on underground markets. It's one-use - once discovered, it's patched and burned. A stolen session token, by contrast, costs roughly nothing. It bypasses every authentication layer, grants immediate post-authentication access, and can be harvested at industrial scale by commodity malware that costs $250 per month to license. The MOE calculation isn't even close.
"In 2026, the most dangerous threat actors aren't the ones with the most advanced code; it's the ones who can integrate intelligence and technology into a single, continuous system that achieves their mission in the shortest time possible." - Cloudflare Cloudforce One, 2026 Threat Report
This shift has been building for years, but 2025 marked the inflection point. Cloudforce One's data shows that attackers are systematically abandoning the pursuit of "sophistication" - complex, expensive, one-off exploits - in favor of throughput. Why build a custom command-and-control server when you can hide inside Google Calendar? Why write bespoke malware when you can buy LummaC2 access for the price of a Netflix subscription and harvest session tokens from thousands of machines simultaneously?
The Cloudflare report identifies this as a transition from "brute force entry" to "high-trust exploitation." The implications are profound. Traditional security models assume a boundary between trusted and untrusted traffic. That boundary no longer exists in any meaningful sense. When an attacker's command-and-control traffic is literally a Google Calendar event description, your network monitoring tool cannot distinguish it from a legitimate meeting invite. When a phishing page lives on an azurewebsites.net subdomain, your URL filter gives it a pass because it trusts Microsoft's infrastructure.
The defenders who understand MOE will survive the next three years. The ones who keep investing in perimeter tools designed for a threat model that expired in 2023 will get breached - not because they weren't paying attention, but because they were paying attention to the wrong things entirely.
Eight Horsemen: The Trends Reshaping Cybersecurity

The eight converging threats that define the industrialized threat era. Infographic: BLACKWIRE
The report identifies eight key trends, each driven by MOE optimization. Taken individually, any one of them would be a serious concern. Taken together, they describe a threat ecosystem that has achieved a kind of industrial maturity - standardized, scalable, and ruthlessly efficient.
1. AI-Automated Offensive Operations
Generative AI has collapsed the skill barrier for cyber operations. Cloudflare's researchers observed threat actors using AI for real-time network mapping, automated exploit development, and the creation of deepfake content at scale. The report explicitly warns that "low-skill actors" can now "conduct high-impact operations" using off-the-shelf AI tools. This isn't theoretical - Cloudforce One documented specific campaigns where AI-generated reconnaissance reduced the time from initial access to lateral movement by an order of magnitude.
The defensive implications are asymmetric and troubling. AI-powered reconnaissance can probe thousands of potential entry points simultaneously, while defenders still review alerts sequentially. A single security analyst reviewing a SIEM dashboard cannot match the throughput of an automated system that's generating and testing phishing emails, scanning for exposed services, and crafting social engineering pretexts in parallel.
2. State-Sponsored Pre-Positioning
Chinese threat actors - specifically groups tracked as Salt Typhoon and Linen Typhoon - have moved beyond espionage into something more ominous: pre-positioning for future operations. The Cloudflare report describes these actors as "anchoring their presence" inside North American telecommunications, government, and IT services infrastructure for "long-term geopolitical leverage."
This language should alarm anyone paying attention. Pre-positioning means the attackers aren't stealing data today. They're establishing persistent access that can be activated during a future crisis - a Taiwan Strait confrontation, a trade war escalation, a diplomatic rupture. The FBI's Michael Machtinger described it in blunt terms at CyberTalks in February 2026: the digital equivalent of having "50 Chinese Ministry of State Security spies or contractors sitting inside a major telecom company's building" (CyberScoop, March 2026).
Salt Typhoon has been confirmed inside the networks of major US telecom companies for up to two years, accessing call records, text messages, and even audio from senior officials' phones. As of March 2026, Senator Cantwell's office reported that some carriers still could not confirm they had fully expelled the attackers. Canada has confirmed its top telecom firms were also compromised.
3. SaaS Integration Blast Radius
Modern enterprises don't run on monolithic systems. They run on a mesh of interconnected SaaS platforms, each integrated via API keys, OAuth tokens, and webhook connections. Cloudflare illustrates the danger with a real-world case: the GRUB1 breach of Salesloft, where a single compromised API cascaded into a breach affecting hundreds of separate corporate environments.
The attack surface isn't the application itself. It's the connective tissue - the over-privileged API integrations that enterprise security teams rarely audit and almost never monitor in real time. When a marketing platform has read/write access to your CRM, and your CRM has webhook access to your billing system, and your billing system connects to your identity provider, a single compromised credential can traverse the entire chain faster than any human can respond.
4. Weaponized Cloud Tooling: Living Off the XaaS
This is perhaps the most significant finding in the entire report. Nation-state actors have moved their command-and-control infrastructure inside the cloud platforms that every enterprise trusts and depends on. Cloudflare calls it "living off the XaaS" - a play on the classic "living off the land" technique, but adapted for the SaaS era.
The report documents specific nation-state groups and their methods. Chinese group FrumpyToad uses Google Calendar for encrypted command-and-control communications, reading and writing commands directly into event descriptions. PunyToad (also China) tunnels through legitimate cloud computing platforms to mask origin IPs. Russia's NastyShrew uses paste sites like Teletype.in and Rentry.co as dead-drop resolvers - infected hosts poll these public sites to receive rotating C2 addresses. North Korea's PatheticSlug hosts XenoRAT payloads on Google Drive and Dropbox, using GitHub for covert C2 channels. Iran's CrustyKrill runs credential harvesting operations from Azure Web Apps and ONLYOFFICE.

Four nations, four approaches - all hiding inside platforms you trust. Infographic: BLACKWIRE
The common thread: every one of these operations uses infrastructure that your network security tools are configured to trust. Blocking Google Calendar, Dropbox, GitHub, or Azure would cripple legitimate business operations. The attackers know this, and they've designed their campaigns specifically to exploit that trust gap.
The Token Apocalypse: Why Your MFA Doesn't Matter
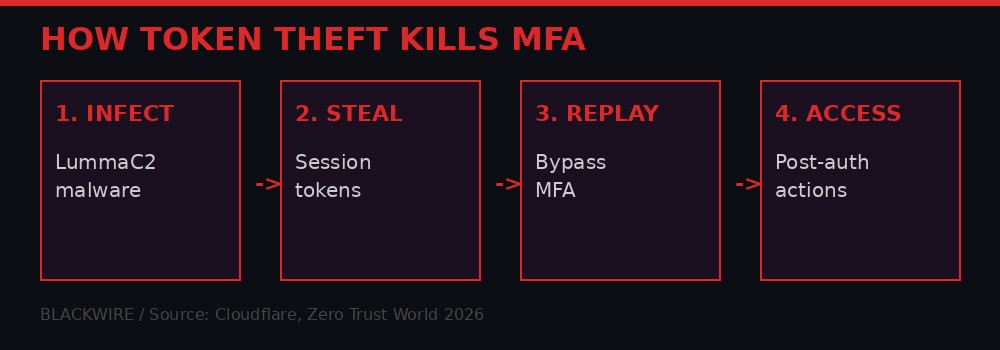
The four-step process that makes multi-factor authentication irrelevant. Infographic: BLACKWIRE
For years, multi-factor authentication was the security industry's answer to credential theft. Enable MFA, the thinking went, and even if a password is compromised, the attacker can't get in without the second factor. That assumption is now demonstrably false.
The Cloudflare report identifies session token theft as the mechanism that "neutralizes multi-factor authentication." Here's how it works: infostealers like LummaC2 and RedLine don't target passwords at all. They target the session tokens - browser cookies - that are issued after a user has already completed MFA. When you log into your corporate email and check the "remember this device" box, your browser stores a session token that proves you've already authenticated. That token is the real key. Steal it, and you walk straight past every authentication layer the organization has deployed.
The economics are devastating. LummaC2 was available for approximately $250 per month before a May 2025 takedown disrupted its operations. In the vacuum that followed, new stealers like Acreed rapidly filled the gap, achieving market dominance by mid-2026 according to threat intelligence firm Webz.io. A single unprotected database discovered in January 2026 contained 149 million stolen login-password pairs, including 48 million Gmail accounts.
Cloudflare's own telemetry provides the damning evidence: 63% of all login attempts they observe involve credentials that have already been compromised elsewhere, and 94% of all login attempts originate from bots. These aren't estimates or projections. These are measured values from one of the largest network infrastructure providers on Earth, observing trillions of requests across its global network.
"Enterprise session hijacking - LummaC2 and RedLine are hooking the browser to rip active auth cookies for IdPs like Entra ID and Okta." - MalwareTips, March 2026
The implications extend beyond individual accounts. When an attacker steals a session token for an Okta or Microsoft Entra ID administrator, they don't just access one application. They access every application federated through that identity provider. In large enterprises, that can mean hundreds of systems, from email to code repositories to financial platforms, all compromised through a single stolen cookie.
The Zero Trust World 2026 conference in March devoted an entire track to this problem. Speakers highlighted that traditional MFA - TOTP codes, SMS verification, even hardware tokens - provides zero protection against token theft because the theft occurs after authentication is complete. The only defenses that work are continuous session validation, device binding, and real-time anomaly detection on session behavior. Most organizations have deployed none of these.
The Ghost Workers: North Korea's Deepfake Job Applicants

What does a North Korean operative look like? Like any other remote developer on a Zoom call. Photo: Pexels
One of the most unsettling findings in the Cloudflare report - and one corroborated by extensive reporting from IBM X-Force, The Register, and OFAC sanctions filings - is the industrialization of North Korea's remote IT worker scheme. This isn't a handful of individuals gaming the system. It's a state-run operation involving an estimated 100,000 operatives generating roughly $500 million per year for the Kim regime.
The operation works like this: North Korean operatives, often educated at elite institutions within the country, use stolen identities and AI-generated deepfakes to apply for remote technology positions at Western companies. They pass video interviews using real-time face-swapping technology. They complete coding assessments with legitimate skill - many of these operatives are genuinely qualified developers. Once hired, they request that company laptops be shipped to "facilitator" addresses in the US, where local collaborators manage the hardware while the actual work is performed from North Korea or China.
The U.S. Treasury Department's Office of Foreign Assets Control (OFAC) sanctioned key members of a DPRK IT worker network in March 2026, describing the scheme under multiple tracking names: Coral Sleet, Jasper Sleet, PurpleDelta, and Wagemole. The Hacker News reported that the network relied on "bogus documentation, stolen identities, and fabricated personas" at scale.
Cloudflare's report identifies this as a MOE-optimized operation: the cost of creating a convincing deepfake identity is negligible compared to the payoff of a six-figure remote salary flowing directly to a sanctioned regime. The operatives typically cycle through multiple jobs, each lasting six to eighteen months, maximizing revenue extraction before moving to the next target.
What makes this particularly difficult to detect is that the workers are actually productive. They write real code, attend real standups, participate in real Slack channels. The espionage and revenue extraction happen in the background - code repositories are exfiltrated, proprietary algorithms are copied, and paychecks are routed through shell companies to Pyongyang. Several documented cases involve the operative attempting to install backdoors or exfiltrate sensitive data once they've established enough trust within the organization.
IBM X-Force and Flare Research published a joint report in March 2026, "Inside the North Korean Infiltrator Threat," detailing the top-level infrastructure used to manage these operations. The scale is staggering - laptop farms across multiple countries, AI-enhanced interview preparation, automated job application systems, and a network of facilitators handling logistics across dozens of US states.
The 31.4 Tbps Wall: DDoS at Industrial Scale

At 31.4 terabits per second, the Aisuru botnet's attack exceeded the bandwidth capacity of most national internet exchanges. Photo: Pexels
In December 2025, the Aisuru botnet launched a distributed denial-of-service attack that peaked at 31.4 terabits per second with a request rate exceeding 200 million per second. To put that in perspective: the total internet backbone capacity of many mid-sized countries doesn't reach 31.4 Tbps. This single attack, targeting a single entity through Cloudflare's network, generated more traffic than the entire national internet infrastructure of most nations on Earth.
Cloudflare describes this as the new "baseline" for hyper-volumetric DDoS. The word "baseline" is doing heavy lifting here. It means that 31.4 Tbps isn't the ceiling - it's the floor from which future attacks will scale upward. The Aisuru botnet achieves this throughput by compromising hundreds of thousands of IoT devices, home routers, and poorly secured servers, each contributing a fraction of the total bandwidth but collectively generating a firehose that can overwhelm any single-provider mitigation system.
The report notes that these attacks are "closing the window for human response." At 31.4 Tbps, automated mitigation must engage within seconds or the target goes dark. Human incident response teams operate on a timescale of minutes to hours. The math doesn't work. Either your DDoS mitigation is fully automated and pre-provisioned, or you are vulnerable. There is no middle ground at this scale.
The Dragos 2026 OT/ICS Cybersecurity Year in Review, released contemporaneously, adds industrial context. Ransomware groups impacting industrial organizations nearly doubled in 2025, with 119 groups tracked across more than 3,300 victims. Many of these attacks begin with DDoS as a distraction or precursor, flooding security teams with noise while the actual intrusion proceeds through compromised credentials or supply chain access.
Dragos also identified three new threat groups - AZURITE, PYROXENE, and SYLVANITE - specifically targeting operational technology environments. SYLVANITE acts as an initial access provider for VOLTZITE, exploiting edge devices and VPN infrastructure to establish footholds in industrial control networks. The convergence of volumetric DDoS, ransomware, and OT-targeted intrusion creates a compound threat that most organizations are structurally unprepared to handle.
The Email Problem: 46% of the Internet Is Unauthenticated

Nearly half of all analyzed emails fail basic authentication checks. Photo: Pexels
DMARC - Domain-based Message Authentication, Reporting, and Conformance - is the email authentication protocol that's supposed to prevent domain spoofing. In theory, it ensures that emails claiming to come from your-company.com actually originate from servers authorized by your-company.com. In practice, Cloudflare found that 46% of analyzed emails fail DMARC verification.
This is not a minor configuration issue. This is a gaping hole in the fabric of trusted communication. Nearly half of all email traffic observed by Cloudflare cannot be verified as legitimate. Phishing-as-a-Service operators have identified this as the highest-MOE vector available: craft a convincing email, send it from an infrastructure that exploits the DMARC gap, and deliver it directly to the target's inbox with the appearance of legitimacy.
The report describes a specific mechanism: "relay blind spots" where mail servers fail to re-verify a sender's identity after the initial relay. In multi-hop email delivery architectures - which describe most enterprise email flows - a message that passes authentication at the first hop may not be re-checked at subsequent hops. Attackers exploit this by injecting spoofed messages at relay points, allowing "high-trust brand impersonations delivered directly to user inboxes."
Cofense, a phishing intelligence firm, published data in March 2026 showing a dramatic increase in attacks abusing Cloudflare Workers and Tunnels services for credential phishing and malware distribution. The irony is sharp: Cloudflare's own infrastructure, designed to protect web applications, is being weaponized to host phishing campaigns that exploit the same trust relationships Cloudflare's report warns about.
The email problem compounds every other threat in the report. Session token theft begins with a phishing email. Deepfake worker recruitment begins with a job application email. DDoS coordination often begins with spear-phishing the target's service providers. Fix the email authentication problem, and you reduce the attack surface for everything else. Leave it broken, and every other defensive investment is undermined at the first hop.
The Citrix Factor: When Your Edge Device Is the Entry Point

Edge devices like Citrix NetScaler are the first target for both state actors and ransomware crews. Photo: Pexels
While Cloudflare's report describes the macro trend, real-world events are providing the micro evidence in real time. On March 30, CISA added CVE-2026-3055 to its Known Exploited Vulnerabilities catalog with a CVSS score of 9.3 and a remediation deadline of April 2, 2026 - giving federal agencies less than 72 hours to patch.
The vulnerability affects Citrix NetScaler ADC and NetScaler Gateway, two products that sit at the very edge of enterprise networks, handling authentication, load balancing, and VPN access. The flaw - a memory overread triggered by manipulated SAML authentication requests - allows attackers to leak sensitive data from device memory, potentially including session tokens, credentials, and configuration data.
Security firm watchTowr confirmed active exploitation in the wild as of March 27, originating from known threat actor IP addresses. The attack is elegant in its simplicity: send a crafted SAMLRequest to the /saml/login endpoint, omit the AssertionConsumerServiceURL field, and the appliance responds with memory contents dumped into the NSC_TASS cookie. A second variant targets the /wsfed/passive endpoint using a malformed query string parameter.
watchTowr researcher Aliz Hammond described the vulnerability in characteristically blunt terms: "If the target Citrix NetScaler is vulnerable, it'll leak memory all over the place and look like a crime scene."
This is the pattern Cloudflare's report describes playing out in real time. Edge devices - VPNs, load balancers, firewalls - are the connective tissue between the internet and the internal network. Attackers don't need to breach the castle walls when the drawbridge mechanism itself is leaking secrets. Citrix has been through this before: CVE-2023-4966 (Citrix Bleed), CVE-2025-5777 (Citrix Bleed 2), CVE-2025-6543, and CVE-2025-7775. The pattern of serial critical vulnerabilities in edge devices isn't a Citrix-specific problem. It's a structural weakness in how enterprises build their perimeters.
Dragos's OT report reinforces this point from the industrial perspective. Their data shows that "most OT incidents do not begin in OT networks. Adversaries consistently gain access through infrastructure that sits between enterprise and operational environments" - VPNs, remote access platforms, identity systems, and internet-facing edge devices. SYLVANITE, one of the newly identified threat groups, specializes in exactly this kind of edge-device exploitation.
The AI Agent Vulnerability: When Your Defense Tool Is the Attack Surface

AI coding agents designed to protect systems may introduce the very vulnerabilities they're meant to prevent. Photo: Pexels
In a move that deserves more attention than it received, Cloudflare's researchers turned their AI tools against themselves. They tasked an AI coding agent with a self-vulnerability analysis - essentially asking the machine to find its own security flaws. The result was CVE-2026-22813, a critical vulnerability (CVSS 9.4) in markdown rendering pipelines that allowed unauthenticated remote code execution.
The vulnerability was discovered in OpenCode, an open-source AI coding agent, and the advisory was published through GitHub's security advisory system. The implications extend far beyond a single tool. As organizations rush to deploy AI coding assistants, automated security scanners, and agentic workflows, each new tool introduces its own attack surface. The AI agent that helps your developers write code may also be rendering untrusted markdown from external sources - and that rendering pipeline, if it contains a flaw like CVE-2026-22813, becomes a direct path to code execution on your systems.
This creates a recursive problem. Organizations deploy AI tools to improve security. Those AI tools have their own vulnerabilities. The vulnerabilities in the AI tools can be exploited to compromise the systems the tools were meant to protect. The Cloudflare report doesn't call this out explicitly as a paradox, but the subtext is clear: the defensive adoption of AI is itself expanding the attack surface in ways that security teams haven't fully mapped.
The broader lesson is about supply chain depth. It's not just your software that needs auditing. It's your AI tools' dependencies, their rendering engines, their plugin ecosystems, their training data pipelines. Every layer of abstraction adds potential vulnerability. The report's recommendation - pivot to "autonomous defense" where automated systems respond at machine speed - is simultaneously the solution and the problem. More automation means more code, more dependencies, more attack surface. The organizations that navigate this paradox successfully will be the ones that treat their defensive tools with the same adversarial scrutiny they apply to their production systems.
The Industrial Blind Spot: 90% of OT Networks Are Flying Dark

Fewer than 10% of OT networks have meaningful monitoring. The rest are operating blind. Photo: Pexels
Dragos estimates that fewer than 10 percent of operational technology networks worldwide have meaningful network monitoring in place. Read that again. Nine out of ten industrial control networks - the systems running power grids, water treatment plants, manufacturing lines, and oil refineries - have no real visibility into what's happening on their networks.
In 30% of Dragos's 2025 incident response cases, investigations began not with a detection alert, but with someone noticing that "something seemed wrong" in operations. Not a SIEM alert. Not an IDS trigger. A human gut feeling. By the time that feeling translates into a security investigation, the attacker has typically been present for days, weeks, or months.
The Dragos report tracked 119 ransomware groups impacting more than 3,300 industrial organizations in 2025 - nearly double the 2024 figure. Many of these attacks were classified as "IT incidents" even when the compromised systems directly supported industrial operations: engineering workstations, SCADA infrastructure, virtualization platforms that underpin OT operations. The classification gap isn't just semantic. It means that the true impact on industrial safety and reliability is systematically underreported.
Three new threat groups - AZURITE, PYROXENE, and SYLVANITE - are specifically targeting the junction between IT and OT environments. AZURITE targets engineering workstations to exfiltrate operational data. PYROXENE compromises IT-to-OT pathways to establish footholds inside industrial environments. SYLVANITE operates at scale as an initial access provider, exploiting edge devices and remote access infrastructure. All three focus on a small set of high-impact assets: engineering workstations, remote access systems, identity infrastructure, and enterprise systems that influence industrial control loops.
The convergence with Cloudflare's findings is exact. The same techniques that compromise enterprise IT - token theft, edge device exploitation, weaponized cloud tooling - provide the entry points into OT environments. The difference is that OT compromise doesn't just mean data loss. It means physical consequences: power outages, water contamination, production shutdowns, and in extreme cases, physical safety hazards for workers and surrounding communities.
What Comes Next: Autonomous Defense or Organized Collapse

The path forward requires automated defense at machine speed - or organizations will be overrun. Photo: Pexels
Cloudflare's prescription is blunt: "autonomous defense." When threats move at machine speed, human-centric defense is no longer viable. The report calls for organizations to "harden the connective tissue of their networks, using real-time visibility and automated response capabilities." The goal isn't to build a better wall. It's to ensure the system can act faster than the attacker, "even when no one is watching."
This is easy to write and extraordinarily difficult to implement. Autonomous defense requires:
- Continuous session validation - not just authentication at login, but ongoing verification that the entity using a session is the entity that created it. Device binding, behavioral analysis, and network fingerprinting, all evaluated in real time.
- Zero-trust architecture that's actually zero-trust - not the marketing version where you buy a product and declare victory, but the operational version where every request is authenticated, authorized, and encrypted regardless of origin.
- Supply chain monitoring at every layer - not just first-party code, but third-party APIs, AI tools, cloud integrations, and the dependencies of dependencies.
- OT network visibility - the 90% gap Dragos identified is a crisis in waiting. Organizations running industrial control systems without network monitoring are not making a risk-based decision. They're making a budget-based decision that will eventually translate into a safety incident.
- Email authentication enforcement - DMARC at enforcement policy (p=reject) for every domain, with SPF and DKIM properly configured across all sending infrastructure. The 46% failure rate is a choice, not a technical limitation.
But the Cloudflare report also contains an implicit warning that it doesn't fully articulate: the arms race has no equilibrium. Every defensive automation creates new attack surface. Every AI-powered defense tool introduces AI-specific vulnerabilities. Every zero-trust architecture relies on identity systems that are themselves targeted by the most sophisticated nation-state actors on Earth.
The Anthropic-Australia AI safety MoU, signed the same day Cloudflare published its report, represents one possible institutional response. Anthropic will share findings on emerging AI model capabilities and risks, participate in joint safety evaluations, and collaborate on research with Australian universities. It's a bilateral arrangement between one AI company and one government. The threat landscape described by Cloudflare is global, simultaneous, and automated. The gap between the pace of institutional response and the pace of threat evolution continues to widen.
Meanwhile, Nvidia's $2 billion investment in Marvell Technology - part of a pattern of investments totaling billions across optical networking and custom chip companies in March alone - signals that the hardware infrastructure underlying AI systems is scaling faster than security frameworks can adapt. More compute, more interconnection, more attack surface. The money flows toward capability. The security challenge flows in the opposite direction, unfunded and understaffed.
The Cloudflare 2026 Threat Report is, ultimately, a document about the end of an era. The era where organizations could buy a firewall, configure an IDS, enable MFA, and consider themselves adequately protected. That era is over. What replaces it is messier, harder, and more expensive: continuous, automated, adversarial defense across every layer of infrastructure, every cloud integration, every employee's browser session, every edge device, every API connection. The organizations that make this transition will survive what's coming. The rest will learn the hard way that in 2026, the attacker doesn't break down your door. They walk in through the front entrance wearing your uniform, using your badge, and sitting down at your desk.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram