Privacy's Worst Week: DarkSword, Meta's Encryption Retreat, and the VPN Trap
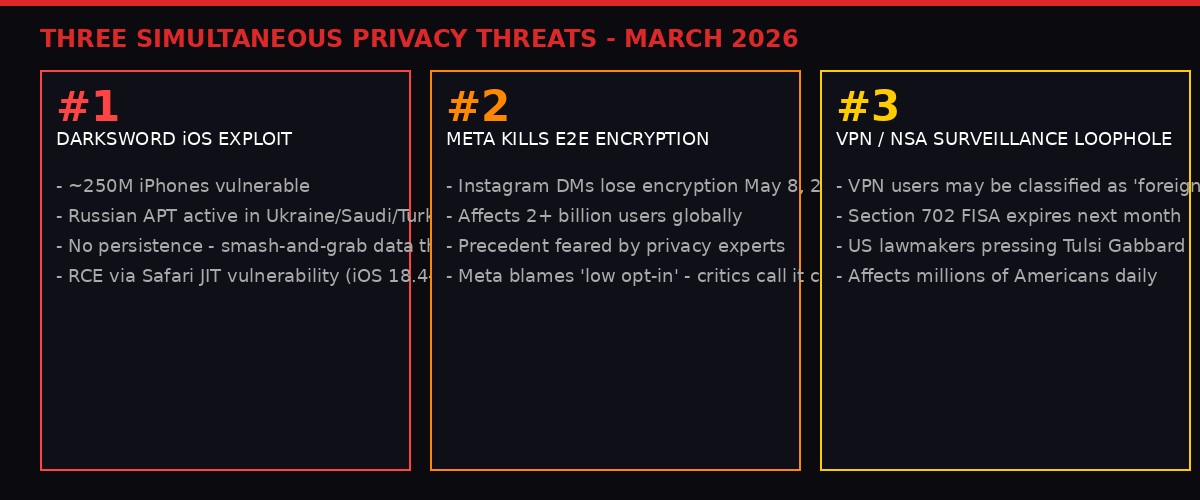
Three separate events in a single week have exposed how thin the membrane protecting digital privacy actually is. A new iOS exploit found in the wild can silently empty your phone in minutes. Meta just announced it is removing encryption from Instagram's messages, affecting two billion users. And US lawmakers have revealed that using a VPN - the very tool most people turn to for privacy - may legally flag you as a foreigner subject to warrantless NSA surveillance. These stories are usually covered separately. They shouldn't be. Together they form a pattern.

DarkSword: The iPhone Exploit That Nobody Bothered to Hide

On March 18, 2026, researchers at Google's Threat Intelligence group, the mobile security firm iVerify, and cybersecurity company Lookout jointly published findings on a sophisticated iPhone-hacking technique they named DarkSword. The name was not invented by the researchers - it came directly from the exploit code itself. Deep inside the implant's JavaScript, a variable that extracts Wi-Fi passwords from compromised devices carries the comment: const TAG = "DarkSword-WIFI-DUMP".
That detail matters. Sophisticated exploit kits are not normally left lying around with their variable names intact and their purpose described in plain English comments. Professional hacking tools - the kind sold by firms like NSO Group, Paragon Solutions, or Intellexa - are typically obfuscated, stripped of identifying labels, and deployed against carefully chosen targets. DarkSword was different. The researchers who found it describe an operation conducted with a startling degree of carelessness: the full exploit kit, complete with stage-by-stage commentary explaining how each component works, was sitting on an Estonian server accessible to anyone with the right targeting IP.
"Anyone who manually grabbed all the different parts of the exploit could put them onto their own web server and start infecting phones. It's as simple as that. It's all nicely documented, also. It's really too easy." - Matthias Frielingsdorf, iVerify co-founder and researcher
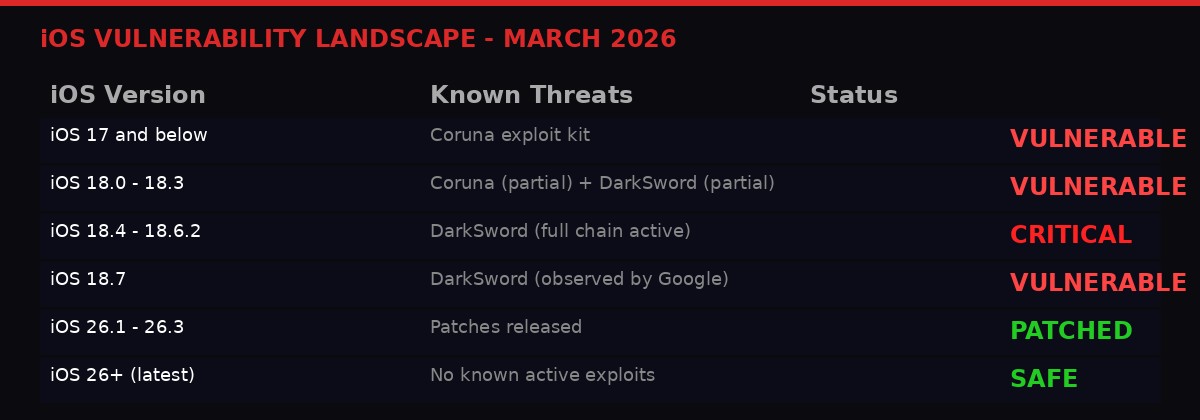
The DarkSword exploit targets devices running iOS 18.4 through iOS 18.6.2 - Apple's previous major operating system, which as of last month still accounted for roughly a quarter of all iPhones in use, according to Apple's own developer statistics cited by WIRED. That is not a marginal population. A quarter of the world's 1.4 billion active iPhones translates to somewhere in the range of 250 to 350 million vulnerable devices.
How the Attack Works
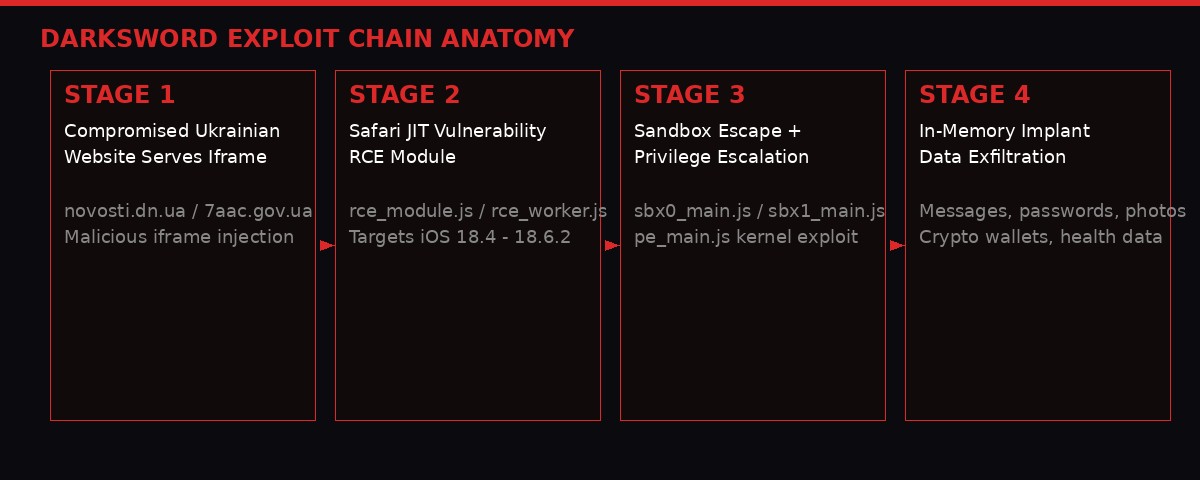
DarkSword operates through what security researchers call a "watering hole" attack. Rather than targeting specific devices through phishing or direct intrusion, the attackers compromised two Ukrainian websites - a news outlet at novosti.dn.ua and a government agency at 7aac.gov.ua - and embedded a malicious iframe that silently loads exploit code whenever someone visits the page on a vulnerable iPhone.
The technical chain is elegant and comprehensive. The rce_loader.js file initiates an attack beginning with a remote code execution module that exploits a JavaScript JIT (just-in-time compilation) vulnerability in Safari's WebKit engine. Once initial execution is achieved, two sandbox escape modules break out of Safari's restricted environment to reach the media playback daemon - a system process with broader access to device resources. From there, a kernel privilege escalation script gains root-level access. Finally, multiple in-memory implants deploy across several processes to begin harvesting data.
The term "in-memory implant" is significant for two reasons. First, it means the attack is "fileless" - it never writes a traditional executable to storage, which makes it far harder to detect with conventional mobile security software. Second, it means the attack does not survive a reboot. Once the phone restarts, DarkSword is gone. But by then it has already done its work.
The data DarkSword collects in its brief window of access is comprehensive: passwords stored on the device, photos, message logs from iMessage, WhatsApp, and Telegram, browser history, calendar and notes data, Apple Health records, and - notably for a tool used by Russian intelligence - cryptocurrency wallet credentials. That last item suggests the operators may be supplementing their espionage work with for-profit financial theft, or that the tool is being licensed to multiple actors with different objectives.
Who Made It and Who Is Using It
Google's Threat Intelligence team identified the exploit's use by what it describes as a Russian state-sponsored espionage group - the same actors previously linked to a separate iOS hacking toolkit called Coruna, revealed by researchers just two weeks before DarkSword. That timeline is notable: two separate zero-day-level iPhone exploit chains disclosed within fourteen days, both connected to the same Russian intelligence operation.
Beyond the Russian campaign targeting Ukrainian news site visitors, Google reports DarkSword has been observed in operations targeting entities in Saudi Arabia, Turkey, and Malaysia. In the Turkish and Malaysian operations, Google identified that customers of PARS Defense - a Turkish surveillance technology company - appear to have used DarkSword. This proliferation to multiple distinct threat actors is the most concerning aspect of the disclosure. What began as a Russian intelligence tool has spread to commercial surveillance firms operating in multiple countries.
The researchers who analyzed DarkSword are confident the Russian hackers who deployed it did not build it. The English-language comments throughout the code suggest it was created by a different team and delivered to its users as a finished product - almost certainly through a commercial "broker" who sells hacking capabilities to governments and intelligence agencies. Who built it is not yet publicly known.
What It Means in Practice
Apple's response to the disclosure was measured but direct: the vulnerabilities have been patched in iOS 26.1 and newer, and emergency patches were released for older devices that cannot run iOS 26. The fix is available. The problem is adoption. Getting a quarter of the world's iPhone users to update is not a technical challenge - it is a human behavior challenge, and human behavior moves slowly.
For users who cannot or will not update, or who are running devices no longer supported by Apple's latest OS, the risk remains. iVerify and Lookout both confirm their security applications can detect a DarkSword infection as currently documented - but "as currently documented" is doing a lot of work in that sentence. Any modifications to the kit that alter its observable signatures would blind those detections.
The more durable lesson from DarkSword is not about this specific exploit. It is about what it represents: a professional-grade iPhone zero-day, built by unknown parties, distributed to Russian state intelligence, spread to at least two commercial surveillance vendors, and left exposed on a public server where anyone could copy it. Exploit tools are not staying in their intended hands.
Meta Kills Instagram Encryption: A Broken Decade of Promises

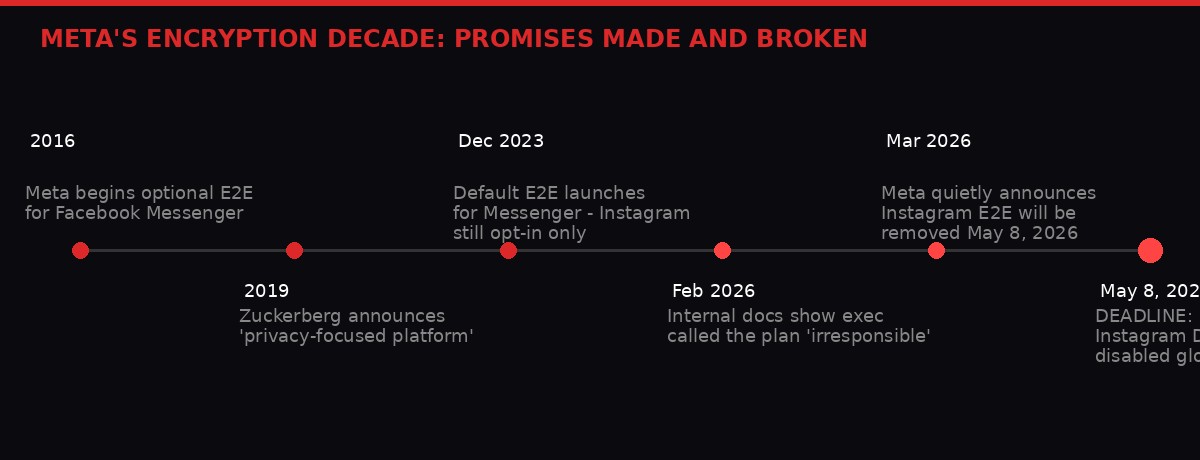
In late March 2026, Meta quietly announced that it would be removing end-to-end encryption from Instagram Direct Messages, effective May 8. The announcement drew immediate outrage from privacy researchers and cryptography experts - not just because of what is being removed, but because of the reasoning given for removing it.
Meta's explanation: very few Instagram users were opting in to the encryption feature, so the company decided to eliminate it. "Very few people were opting in to end-to-end encrypted messaging in DMs, so we're removing this option from Instagram in the coming months," a Meta spokesperson told WIRED and other outlets.
The statement struck researchers as deeply cynical. End-to-end encryption for Instagram DMs was never the default - it was an opt-in feature buried behind multiple menu layers. It was, in effect, designed to be hard to find. Meta then used the low adoption rate of the hidden feature as justification for removing it entirely. Critics noted this is a logical structure that could justify eliminating any privacy protection: make it inconvenient, watch it fail, then cite the failure as evidence nobody wants it.
"Meta's deployment of encryption was a public commitment, and they were weathering a lot of pressure from various governments to do it. Public commitments to support privacy features are literally the only thing that we the public have. If they're worthless, then why should we assume we'll continue to have end-to-end encryption in Messenger and WhatsApp?" - Matt Green, Johns Hopkins University cryptographer
A Decade of Commitments, Now Discarded
The history here matters. In 2016, Meta began testing optional end-to-end encryption for Facebook Messenger. In April 2019, Mark Zuckerberg published a lengthy philosophical treatise announcing his vision for Meta as a "privacy-focused platform" - a fundamental reinvention, he said, of how the company operated. End-to-end encryption across all messaging services was central to that pledge.
It took another four years to make good on part of that promise. In December 2023, Meta announced that Messenger had default end-to-end encryption enabled - a genuine technical achievement, covering a billion-plus users simultaneously. Instagram DMs were supposed to follow. Instead, the company implemented Instagram encryption as an opt-in feature with no default status, then used that opt-in's low uptake as a retroactive justification to remove it.
Documents released as part of a separate lawsuit about Meta's protection of young users revealed the internal reality behind the encryption saga. Reuters reported in February 2026 that Meta's head of content policy, Monika Bickert, wrote internally in March 2019 - precisely as Zuckerberg was announcing the privacy-first pivot - that "we are about to do a bad thing as a company. This is so irresponsible." The public messaging and the private reality were moving in opposite directions.
Why This Sets a Dangerous Precedent
Privacy advocates' concern is not only about Instagram users losing a feature that few were using anyway. It is about what Meta's retreat signals to the rest of the industry, and to governments worldwide that have been pressing tech companies to weaken or eliminate encryption for years.
Few companies have the user scale and financial stability to withstand government pressure demanding access to encrypted communications. Law enforcement agencies in the UK, EU, Australia, and the US have each at various points proposed legal requirements that would force messaging platforms to provide government access to encrypted messages - sometimes called "lawful access" mechanisms or "client-side scanning." Apple and Meta, by virtue of their size and legal resources, were among the handful of companies capable of pushing back.
Meta's retreat gives other companies permission to follow. And it gives governments a template: the company that spent years defending default encryption just voluntarily removed it. The argument that end-to-end encryption is a fundamental consumer right that must be defended at all costs becomes harder to make when one of the industry's most visible proponents quietly deletes the feature and blames user apathy.
"Designed the feature so nobody could find it, killed it for not being easy enough to find and, therefore, unpopular. It's deeply cynical." - Davi Ottenheimer, security executive and creator of pqprobe
The announcement came the same week that Moxie Marlinspike - Signal's creator and perhaps the most credentialed encryption advocate alive - announced his new privacy-focused AI platform, Confer, would be integrated into Meta AI. The juxtaposition is jarring: Meta is simultaneously partnering with the person who encrypted WhatsApp for a billion users to protect AI conversations, while eliminating encryption from Instagram DMs for two billion others.
Marlinspike framed his collaboration with Meta AI in explicitly cautionary terms: "Right now, none of that data is private. It is shared with AI companies, their employees, hackers, subpoenas, and governments. As is always the case with unencrypted data, it will inevitably end up in the wrong hands." He wrote that specifically about AI chat. The exact same logic applies to Instagram DMs. Meta is apparently listening to only half of the argument.
The VPN Trap: Your Privacy Tool Might Flag You for NSA Surveillance

On March 26, 2026, six Democratic lawmakers sent a letter to Director of National Intelligence Tulsi Gabbard asking a pointed question: does using a VPN expose Americans to warrantless NSA surveillance?
The concern is structural and rooted in how surveillance law currently operates. Under Section 702 of the Foreign Intelligence Surveillance Act - a controversial warrantless surveillance program set to expire next month - US intelligence agencies can intercept communications targeting non-US persons abroad without a warrant. Americans are supposed to be protected. But the protection is built on a location assumption.
When your internet traffic passes through a VPN server, especially one located in another country, you look to a network observer like you are in that country. The NSA's own targeting procedures, declassified and cited in the lawmakers' letter, establish a default presumption: if a person's location is unknown, they are presumed to be a non-US person. A VPN, by design, obscures your true location.
The practical implication: millions of Americans using VPNs - to watch overseas sports broadcasts, access content blocked in their region, protect their data on public Wi-Fi, or exercise what they understand to be basic privacy - may be inadvertently waiving their Fourth Amendment protections against warrantless surveillance. The FBI, the NSA, and the FTC have all at various points recommended VPN use as a privacy best practice. The surveillance agencies have, in effect, been recommending a tool that may subject users to their own collection programs.
The letter warns that the same foreignness presumption applies under Executive Order 12333 - a Reagan-era directive that permits bulk collection of foreigners' communications with even fewer constraints than Section 702, operating under guidelines approved by the US attorney general alone - meaning Americans on foreign VPN servers could be exposed to "bulk, indiscriminate surveillance of foreigners' communications."
Section 702 and the Coming Battle in Congress
The timing of this letter is not coincidental. Section 702 is set to expire next month, and Congress is engaged in a fierce debate over whether to renew it, and under what conditions. The program authorizes not just targeted foreign surveillance but sweeps in vast quantities of Americans' communications as collateral collection - and allows the FBI to search those communications without a warrant.
Senator Ron Wyden, one of the six signatories, is a member of the Senate Intelligence Committee with access to classified details about how these programs actually operate. He has a documented history of using carefully worded public statements to raise alarms about surveillance he cannot discuss openly. His specific focus on VPNs and the foreignness presumption suggests he has reason to believe this is not just a theoretical legal concern.
The letter also raises a second authority: Executive Order 12333, a Reagan-era directive that governs bulk collection of foreigners' communications with fewer constraints than any statute. Unlike FISA Section 702, which requires court approval and congressional oversight, EO 12333 surveillance operates under guidelines the Attorney General approves alone. VPN traffic routed through overseas servers could fall under this even broader authority.
Gabbard had not publicly responded to the letter as of this reporting. Her office did not immediately provide comment to outlets covering the story.
Three Stories, One Pattern: The Erosion is Structural

In a single week, here is what happened: a nation-state-grade iPhone exploit kit was found loose on the public internet, ready for anyone to download and deploy against a quarter billion vulnerable phones. The world's largest social media company, under pressure from governments and facing internal skepticism about its own encryption commitments, removed end-to-end encryption from two billion users' private messages. And lawmakers revealed that one of the most widely recommended consumer privacy tools - the VPN - may actually expose Americans to the warrantless surveillance regime it was supposed to circumvent.
Each story is significant in isolation. Together they reveal something more systemic: the privacy infrastructure that most people assume protects their digital lives is eroding on multiple fronts simultaneously, and the erosion is not random. It is the product of specific choices - by governments demanding access, by corporations managing regulatory and political pressure, and by the sprawling commercial market for surveillance tools that supplies whichever actor is willing to pay.
The second-order effect that most coverage misses is the interaction between these trends. DarkSword becomes more valuable as a tool in a world where users have abandoned encrypted apps, or where their "secure" app conversations are being stored in plaintext by the platform. Meta's removal of Instagram encryption creates a larger pool of unprotected communications for tools like DarkSword to exfiltrate. The VPN loophole means that users who turn to privacy tools for protection may be accelerating their exposure.
The Chilling Effect on Dissent
The most significant second-order effect is political, not technical. When activists, journalists, human rights defenders, and political dissidents - in any country, including the United States - cannot trust that their communications are private, they change their behavior. They communicate less. They share less information with each other. They take fewer risks.
That behavioral shift is the actual goal of mass surveillance, whether conducted by authoritarian governments or democratic ones. The NSA does not need to read every VPN user's messages to achieve a chilling effect on dissent. It just needs people to believe that using a VPN might get them classified as a foreign target. Meta does not need to actively surveil Instagram DMs to change how people communicate. It just needs to eliminate the expectation of privacy. DarkSword does not need to compromise every phone in Ukraine to suppress independent journalism. It just needs journalists to wonder whether their phone is safe.
These effects are not incidental. They are outcomes, and in some cases they are features rather than bugs.
What Protective Options Actually Remain

The picture is not entirely bleak, but it requires active engagement rather than passive assumption of safety.
On the iOS exploit front, the fix is straightforward: update to the latest iOS version. DarkSword specifically targets iOS 18.4 through 18.6.2 - all of which have been patched. iOS 26.1 and newer are protected against both DarkSword and the earlier Coruna kit. Apple also released emergency security patches for older devices unable to run iOS 26. There is no reason not to update, and the risk of not doing so is now concretely documented rather than theoretical.
For users facing elevated risk - journalists, activists, dissidents, lawyers handling sensitive matters - Apple's Lockdown Mode remains a recommended hardening measure. As BLACKWIRE reported earlier this week, Apple has maintained a remarkable record: no successful mercenary spyware attack against a Lockdown Mode-enabled device since the feature launched in 2022. Lockdown Mode does restrict certain device functionality, but for high-risk individuals, that tradeoff is unambiguously worth making.
On the messaging encryption front, the answer that privacy researchers have consistently given is consistent: use Signal. WhatsApp remains end-to-end encrypted by default for all conversations. Telegram offers end-to-end encryption only in its "Secret Chats" mode - regular Telegram conversations are not encrypted at the server. Instagram DMs will lose encryption on May 8. For anything sensitive, Signal is the current gold standard.
Moxie Marlinspike's Confer project, which aims to bring end-to-end encryption to AI chat conversations, represents a meaningful but early-stage effort to extend privacy protections into the emerging world of AI assistants. The collaboration with Meta AI is promising but has not yet specified its technical implementation. Users who discuss sensitive matters with AI assistants should assume, for now, that those conversations are accessible to the AI company, its employees, and potentially governments with legal process.
The VPN Question Has No Clean Answer
The VPN situation is the most difficult to navigate cleanly, because the threat is legal and structural rather than technical. A VPN can still protect your data from your internet service provider, from network-level attackers on public Wi-Fi, and from various forms of commercial tracking. Those protections remain real. What is newly uncertain is whether VPN use triggers a surveillance authority loophole that exposes you to the exact agency whose collection you were trying to avoid.
Until Gabbard's office clarifies the legal position, or until Section 702 reauthorization debate produces more transparency about targeting procedures, the safest advice is: use a VPN for the protections it demonstrably provides, but do not use it as your sole defense if you are genuinely concerned about US government surveillance. End-to-end encrypted applications operating on top of a VPN provide layered protection that is significantly harder to crack than either alone.
The Bigger Picture: Privacy in a Wartime Economy of Surveillance

The timing of this week's privacy revelations is not entirely disconnected from the broader geopolitical context. The US-Israel war with Iran, which entered its second month in late March 2026, has created an environment in which surveillance authorities face reduced scrutiny, governments have strong arguments for expanded intelligence collection, and technology companies face intense pressure not to provide cover for adversaries' communications.
DarkSword was deployed by Russian intelligence primarily against Ukrainians - a wartime intelligence operation that security researchers happened to discover because the attackers left their tools lying around. The Iranian Handala hacker group breaching FBI Director Kash Patel's personal Gmail account, revealed just one day before this article's publication, is another data point in the same pattern: state-linked actors attacking adversary institutions through the digital infrastructure connecting them.
In this environment, legal surveillance authorities expand, technology companies come under pressure to be "cooperative," and the line between wartime intelligence operations and peacetime mass surveillance blurs predictably. Section 702's impending expiration is being debated against a backdrop where the intelligence community can credibly point to active adversary cyberoperations as justification for maintaining broad collection authorities.
But the surveillance infrastructure built in wartime does not disappear when the conflict ends. The tools and legal frameworks developed to target Iranian hackers and Russian spies will remain available to use against journalists, activists, political opponents, and ordinary citizens once the emergency justification fades. This is not speculation - it is the documented history of every surveillance expansion in the past century.
What makes the current moment different is the density of the surveillance infrastructure. State-level exploit kits have proliferated to commercial vendors who sell to any government willing to pay. Platforms that spent a decade building end-to-end encryption are quietly rolling it back under pressure. Legal frameworks designed for foreign intelligence collection are being scrutinized for their application to domestic users. All three of these trends are happening in the same week, with no coordinating actor driving them - which suggests the erosion is structural rather than episodic.
Timeline: The Week Privacy Lost Ground
Google, iVerify, and Lookout jointly disclose DarkSword iOS exploit kit. Active since at least December 2025 based on server timestamps. Affects iOS 18.4 through 18.6.2 - roughly 250 million devices.
Signal creator Moxie Marlinspike announces Confer encryption technology will be integrated into Meta AI. WhatsApp head Will Cathcart endorses the collaboration.
WIRED publishes full analysis of Meta's decision to remove end-to-end encryption from Instagram DMs, effective May 8. Johns Hopkins cryptographer Matt Green: "Nothing about this is honest."
Six Democratic senators and representatives send letter to DNI Tulsi Gabbard asking whether VPN use strips Americans of constitutional protections against warrantless surveillance under Section 702 and EO 12333.
Iranian hacker group Handala announces breach of FBI Director Kash Patel's personal Gmail account. Department of Justice confirms Patel's email was compromised. Emails appear authentic but date to 2010-2019.
Meta deadline: Instagram Direct Message end-to-end encryption will be removed for all users.
The bottom line: Update your iPhone now. Move sensitive conversations to Signal. Do not assume any tool provides complete protection - layered defenses are the only realistic approach. And watch the Section 702 reauthorization debate closely. What gets decided in the next four weeks will shape the legal architecture of American surveillance for years.
WIRED: "Hundreds of Millions of iPhones Can Be Hacked With a New Tool Found in the Wild" (Andy Greenberg, Mar 18, 2026)
iVerify blog: "Inside DarkSword: A New iOS Exploit Kit Delivered Via Compromised Legitimate Websites" (Frielingsdorf and Krzywicki, Mar 18, 2026)
WIRED: "The Danger Behind Meta Killing End-to-End Encryption for Instagram DMs" (Lily Hay Newman, Mar 20, 2026)
WIRED: "Signal's Creator Is Helping Encrypt Meta AI" (Newman and Burgess, Mar 19, 2026)
WIRED: "Using a VPN May Subject You to NSA Spying" (Dell Cameron, Mar 26, 2026)
AP News: "He suddenly couldn't speak in space. NASA astronaut says his medical scare remains a mystery" (Mar 28, 2026)
Reuters: confirmation of Kash Patel Gmail breach (Mar 27, 2026)
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram