$285 Million Gone in Minutes: Inside the Drift Protocol Exploit That Gutted Solana's Biggest Perps Exchange

The Drift attacker moved fast - vault balances collapsed in under 60 minutes. Photo: Pexels
At approximately 1:30 PM Eastern on April 1, 2026, blockchain monitors flagged something deeply wrong on Solana's largest perpetual futures exchange. Within an hour, $285 million had vanished from Drift Protocol's vaults, routed through Jupiter swaps, bridged to Ethereum, and converted into 38,820 ETH. The attacker's wallet - HkGz4K - now sits as one of the most tracked addresses in crypto history. This is not an April Fools joke. Those were Drift's own words.
The First Alarm: How the Attack Unfolded

On-chain detectives spotted the anomaly before Drift's own team did. Photo: Pexels
The first public alarm came from the Solana ecosystem's unofficial watchtowers. Lookonchain, the blockchain analytics account with 1.4 million followers on X, flagged suspicious outflows from Drift Protocol's vault addresses around 1:30 PM ET on April 1. Seconds later, PeckShield, the security firm that has tracked billions in DeFi losses over the past three years, posted its own alert tagging Drift directly.
What they saw was stark. Massive chunks of capital - JLP tokens, USDC, wrapped SOL, wrapped Bitcoin - were moving out of Drift's vault contracts in rapid-fire transactions. The destination was a single Solana wallet: HkGz4KmoZ7Zmk7HN6ndJ31UJ1qZ2qgwQxgVqQwovpZES. Blockchain explorers immediately flagged it as potentially attacker-controlled.
Mert Mumtaz, CEO of Helius - the Solana developer platform used by hundreds of projects - was among the first high-profile figures to sound the alarm. "Not 100% fully certain yet, but it seems Drift might be getting exploited," he posted on X. "Monitor your positions." That post went viral within minutes, triggering a cascade of panic across Solana Twitter.
The Drift team's initial response came roughly 30 minutes after the first on-chain anomaly was detected. "We are observing unusual activity on the protocol," they wrote on X. "We are currently investigating. Please do not deposit funds into the protocol while we investigate. This is not an April Fools joke. Proceed with caution until further notice."
That last line carried weight. April 1 is the single worst day of the year for a crypto exploit to surface. Every response, every warning, every urgent post gets second-guessed by a community conditioned to expect pranks. But the on-chain data was irrefutable. The money was moving in real time, visible to anyone with a Solscan tab open.
By 2:30 PM ET, the picture had sharpened dramatically. Drift updated its status to confirm what on-chain sleuths already knew: "Drift Protocol is experiencing an active attack. Deposits and withdrawals have been suspended. We are coordinating with multiple security firms, bridges, and exchanges to contain the incident."
Anatomy of the Drain: $309 Million to $24 Million
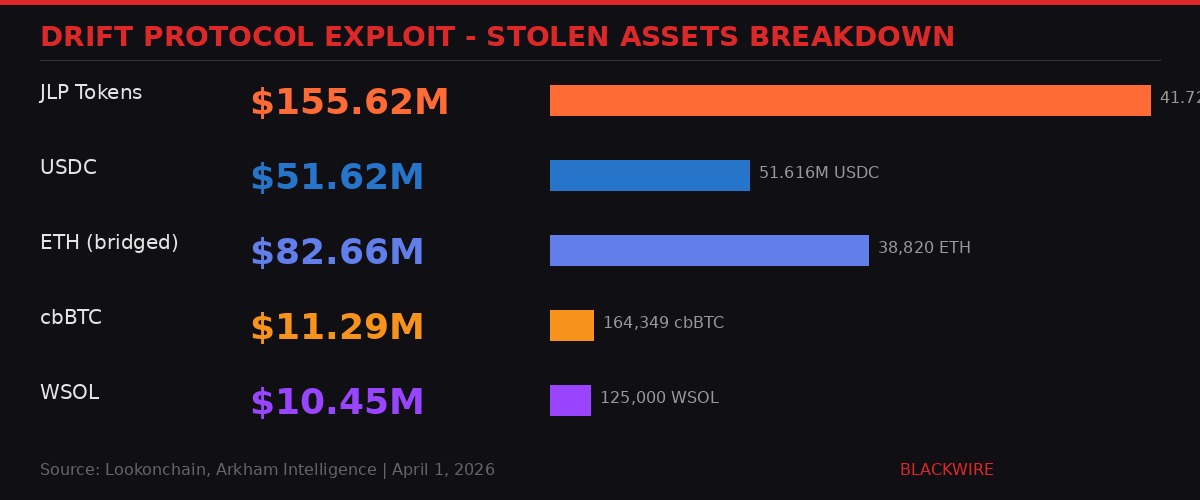
Breakdown of assets stolen from Drift Protocol vaults. Infographic: BLACKWIRE
The attack was surgical. On-chain data compiled by Lookonchain and confirmed by Arkham Intelligence shows the attacker executed approximately 11 distinct transactions in rapid succession. Each one targeted a different asset class within Drift's multi-collateral vault system.
The biggest single extraction: 41.72 million Jupiter Liquidity Pool (JLP) tokens, valued at approximately $155.62 million at the time of the theft. JLP tokens represent shares in Jupiter's liquidity pools - the backbone of Solana's DeFi routing layer. Taking $155 million of JLP in a single sweep is not just a theft; it is a structural blow to the Solana DeFi ecosystem's deepest liquidity pool.
The second-largest tranche was stablecoins. The attacker moved 51.616 million USDC directly out of Drift vaults. Reports indicate that Circle, the USDC issuer, was alerted to the breach and asked to freeze the relevant addresses. As of the last update from Drift's team at 18:54 UTC, no public confirmation of a USDC freeze had been issued.
Beyond the two headline figures, the attacker also extracted 125,000 WSOL (wrapped Solana, worth approximately $10.45 million), 164,349 cbBTC (Coinbase wrapped Bitcoin, valued at roughly $11.29 million), and various other tokens including wrapped Ethereum and even Fartcoin - the memecoin that somehow keeps appearing in serious DeFi exploits.
Within minutes of the first transactions hitting the chain, Drift's total vault balance collapsed from approximately $309 million to roughly $24 million. That is a 92% drawdown. For users with open perpetual futures positions collateralized by Drift's vaults, the implications are catastrophic. Their margin is functionally gone. Liquidation cascades became a near-certainty for leveraged positions that relied on vault-backed collateral.
The speed matters here. This was not a slow bleed over hours or days, like the Euler Finance exploit of March 2023 where the attacker drained $197 million across multiple transactions over several hours. The Drift drain happened in what blockchain data suggests was a window of less than 60 minutes from first suspicious outflow to vault depletion. That compression of time gave the Drift team almost no window to respond, pause contracts, or coordinate a freeze.
The Laundering Pipeline: Jupiter, Bridges, and 38,820 ETH

The attacker used Solana's Jupiter aggregator and cross-chain bridges to move funds at speed. Photo: Pexels
What happened next reveals an attacker with a clear exit strategy, prepared well in advance of the exploit itself. Rather than sitting on the stolen assets in a single wallet - which would make freezing trivial - the attacker immediately began converting and dispersing the funds across multiple chains and venues.
Step one: Jupiter aggregator. The stolen assets were routed through Jupiter, Solana's dominant DEX aggregator that handles over 60% of all on-chain swap volume on the network. Jupiter's routing engine - which splits trades across multiple liquidity sources to minimize slippage - was used to convert JLP, WSOL, cbBTC, and other tokens into USDC and SOL at scale. The irony is painful: Jupiter's infrastructure, built to give DeFi users the best possible prices, was weaponized by the attacker for maximum extraction efficiency.
Step two: Cross-chain bridging. Once consolidated into portable assets (primarily USDC and SOL), the attacker began bridging funds from Solana to Ethereum. The exact bridge or bridges used have not been publicly confirmed as of this writing, but the destination Ethereum address - 0xFcC47866Bd2BD3066696662dbd1C89c882105643 - shows a clear pattern of incoming transfers followed by immediate purchases of ETH.
Step three: ETH accumulation. By 17:49 UTC on April 1, the attacker had acquired 19,913 ETH, worth approximately $42.6 million at the time. But they were not done. Tracking by Cryip and Lookonchain showed continued buying. By 18:17 UTC - roughly 30 minutes later - the attacker's ETH holdings had ballooned to 38,820 ETH, approximately $82.66 million worth. The ETH buying continued after that timestamp.
Why ETH? Because Ethereum is the most liquid, most widely traded asset after Bitcoin. ETH can be mixed through Tornado Cash forks, deposited into DeFi lending protocols, used as collateral for loans, or simply held. Unlike USDC, which Circle can freeze at the smart contract level, ETH is permissionless. No entity can unilaterally freeze an ETH balance. The attacker knows this.
Step four: Diversified exits. On-chain researchers also flagged that portions of the stolen SOL were deposited directly into Binance, the world's largest centralized exchange by volume. Additional SOL was also reportedly deposited into HyperLiquid, the perpetual futures DEX on Arbitrum, where it was swapped for ETH. This multi-venue approach - centralized exchanges, DEX aggregators, cross-chain bridges - is a textbook laundering playbook, designed to fragment the trail across as many jurisdictions and protocols as possible.
The Attack Vector: What We Know and What We Don't

Timeline of events during the Drift exploit on April 1, 2026. Infographic: BLACKWIRE
Here is what makes the Drift exploit genuinely alarming for the broader DeFi ecosystem: nobody knows how it happened.
As of publication, neither Drift Protocol's team nor any of the security firms working on the investigation have confirmed the exploit vector. That is unusual. In most DeFi hacks, the vulnerability becomes apparent within hours - either from on-chain analysis of the malicious transactions or from security researchers reverse-engineering the contract calls. In the case of Drift, we are now past the 12-hour mark with no confirmed root cause.
The three leading theories, per Bitcoin.com, CryptoTimes, and independent researchers:
Theory 1: Smart Contract Vulnerability
Drift Protocol runs on a virtual automated market maker (vAMM) architecture with multi-asset collateral support. The protocol's smart contracts manage vault deposits, perpetual futures settlement, cross-margining calculations, and liquidation logic. Any vulnerability in these contracts - a reentrancy bug, an integer overflow, an access control flaw - could potentially allow an attacker to drain funds. Drift's contracts have been audited multiple times, but audits are not guarantees. Euler Finance had been audited before its $197 million exploit. Wormhole had been audited before its $325 million hack.
Theory 2: Compromised Private Keys
The Futunn analysis referenced earlier draws a direct parallel to Bybit's $1.4 billion hack in February 2025, which was attributed to North Korea's Lazarus Group compromising Safe{Wallet}'s frontend to inject malicious transaction signing. If Drift's vault admin keys or multisig signers were compromised - through phishing, social engineering, malware, or supply chain attack - the attacker could have authorized the transfers without exploiting the contracts themselves. This is the "Occam's Razor" theory: the simplest explanation is that someone got the keys.
Theory 3: Oracle Manipulation
Drift uses external price oracles (including Pyth Network, Solana's primary oracle provider) to determine asset prices for its perpetual futures market. If an attacker could manipulate the oracle prices fed into Drift's contracts - even briefly - they could potentially create artificial price discrepancies, drain collateral through favorable liquidations, or trick the vault logic into releasing more funds than it should. Oracle attacks have been a recurring theme in DeFi exploits, including the Mango Markets hack of October 2022, where Avraham Eisenberg manipulated oracle prices to extract $114 million.
The absence of a confirmed vector is itself a risk signal. It means other Solana DeFi protocols that share similar architecture - or the same oracle infrastructure, or the same multisig tooling - cannot yet assess whether they are vulnerable to the same attack. Until Drift or a security firm publishes a postmortem, the entire Solana DeFi stack operates under a cloud of uncertainty.
Market Fallout: DRIFT Token, Solana Ecosystem, and Fear Index at 8

The DRIFT token had already lost 98% from its all-time high before the exploit struck. Photo: Pexels
The DRIFT governance token was already on life support before the exploit. Trading at approximately $0.072, the token had declined roughly 98% from its all-time high - a death spiral familiar to anyone who has watched DeFi governance tokens in a bear market. The exploit pushed it over the cliff.
Within hours of the first alerts, DRIFT dropped from $0.072 to $0.055, a decline of approximately 24%. CoinMarketCap data shows trading volume surged 198% to $22.15 million - but almost all of it was sell pressure. The market cap collapsed to $31.27 million. For a protocol that just had $309 million in its vaults, a $31 million token valuation tells you exactly how much confidence remains: none.
The broader context makes this worse. The crypto Fear and Greed Index sat at 8 on April 1, 2026 - classified as "Extreme Fear." That is one of the lowest readings in the index's history, on par with the depths of the 2022 bear market. The Drift exploit landed on top of an already-shattered market.
Bitcoin had just posted its worst Q1 performance since 2018, dragged down by the ongoing Iran-Hormuz conflict, massive ETF outflows, and growing fears that the Federal Reserve would reverse course and raise interest rates. Ethereum, Solana, and every major altcoin were deep in the red before the hack even happened. The Drift exploit was gasoline on a fire that was already consuming the market.
For Solana specifically, the timing is devastating. EthCC 2026 in Cannes - Ethereum's marquee institutional conference - just wrapped with over $24 billion in announced institutional commitments to Ethereum-based products. Solana was already fighting the narrative that institutions prefer Ethereum. A $285 million exploit on Solana's largest perps exchange does not help that fight.
The Phantom wallet team issued an immediate advisory, warning users attempting to connect to Drift that the protocol was under investigation and requiring explicit risk acknowledgment before proceeding. That warning screen - a stark departure from Phantom's usually seamless UX - underscored the severity of the situation.
Where This Ranks: The DeFi Hack Hall of Shame
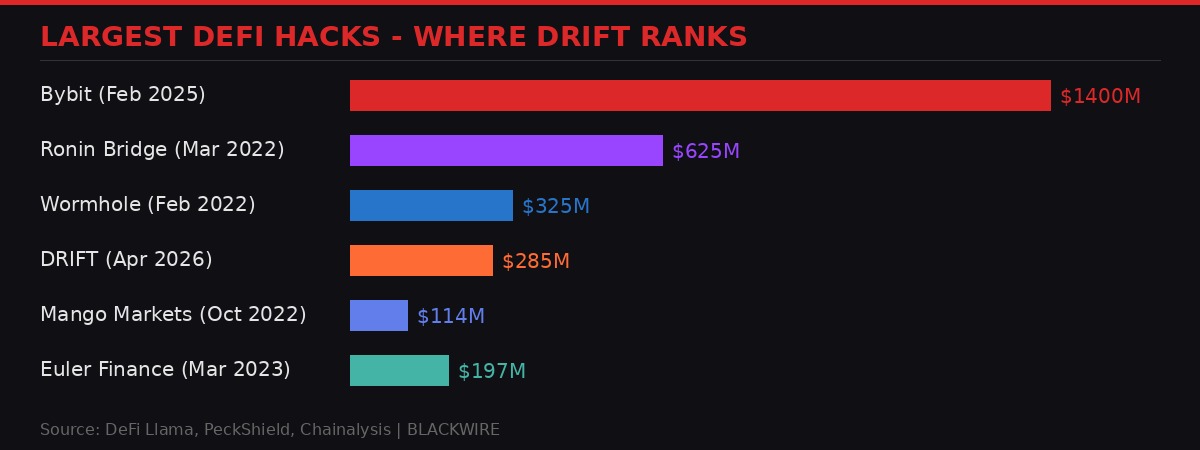
Drift now ranks among the largest DeFi exploits in history. Infographic: BLACKWIRE
The Drift Protocol exploit now ranks as the second-largest Solana ecosystem breach in history, behind only the Wormhole bridge hack of February 2022, which cost $325 million. In the all-time DeFi hack rankings, it sits in the top five:
1. Bybit - $1.4 billion (February 2025)
North Korea's Lazarus Group compromised the Safe{Wallet} frontend used by Bybit's cold wallet infrastructure. The attackers injected malicious JavaScript that modified transaction payloads during the signing process, redirecting 401,347 ETH to attacker-controlled addresses. The largest crypto hack in history by any measure.
2. Ronin Bridge - $625 million (March 2022)
Lazarus Group again. Five of nine validator private keys for the Ronin bridge (connecting Axie Infinity's sidechain to Ethereum) were compromised through a combination of social engineering and a legacy access control flaw. The attackers forged fake withdrawals over two transactions. The hack went undetected for six days.
3. Wormhole - $325 million (February 2022)
A smart contract vulnerability in Wormhole's Solana-side bridge contract allowed the attacker to mint 120,000 wrapped ETH on Solana without depositing corresponding ETH on Ethereum. The bug was in the signature verification logic, allowing the attacker to bypass the guardian validation.
4. Drift Protocol - $285 million (April 2026)
Attack vector unknown. Approximately 980,000 SOL and $51 million in USDC drained from vaults, converted through Jupiter and bridged to Ethereum for 38,820+ ETH. Investigation ongoing.
5. Euler Finance - $197 million (March 2023)
A flash loan exploit targeting a vulnerability in Euler's donation mechanism. The attacker used a series of deposits, borrows, and donations to manipulate the protocol's accounting, extracting DAI, WBTC, stETH, and USDC. In a twist, the attacker returned all funds two weeks later.
The pattern is damning. In every case above except Euler, the stolen funds were never fully recovered. The Ronin hack eventually saw $30 million frozen, but the Lazarus Group still holds the vast majority. Wormhole's $325 million was made whole by Jump Crypto, which injected its own capital - not because the attacker returned anything. Bybit's $1.4 billion remains largely with Lazarus Group.
The question for Drift users: is there any realistic path to recovery? Without knowing the exploit vector, without confirmed freezing of the USDC component, and with the attacker actively converting everything into permissionless ETH, the odds are grim. If this turns out to be a Lazarus-style state-sponsored attack, the probability of meaningful recovery drops to near zero.
What Drift Users Should Do Right Now

Security researchers advise immediate revocation of all Drift-related wallet approvals. Photo: Pexels
If you have ever interacted with Drift Protocol - deposited collateral, opened a perpetual futures position, provided liquidity, or even connected your wallet for a test trade - you need to take action immediately. The attack vector is unknown, which means the scope of the vulnerability is unknown. It is possible (though not confirmed) that wallet approvals granted to Drift's contracts could be leveraged for additional theft.
Step 1: Revoke all Drift approvals. Phantom wallet users can do this directly through the wallet's connected apps interface. For other Solana wallets, use a tool like Solana's Token Revoke (revoke.cash) to check and revoke any outstanding approvals tied to Drift's contract addresses. This is precautionary - there is no evidence that wallet approvals were the attack vector - but it costs nothing and eliminates a potential risk.
Step 2: Do not interact with Drift. Do not deposit. Do not withdraw. Do not attempt to close positions. The protocol's smart contracts may be compromised, and any interaction could expose your wallet to additional risk. Wait for the team to confirm the situation is fully resolved and the contracts are safe before reconnecting.
Step 3: Ignore unsolicited refund offers. Within hours of any major hack, phishing campaigns launch that impersonate the hacked protocol and offer "refunds" or "compensation claims." These are scams. Drift Protocol will only communicate through its official X account (@DriftProtocol) and its official website. Any DMs, emails, or links claiming to offer refunds are malicious.
Step 4: Track the money. If you had funds in Drift and want to follow the investigation, monitor the attacker's wallets on Arkham Intelligence (Solana wallet) and Etherscan (Ethereum wallet). On-chain tracking accounts like Lookonchain and ZachXBT will likely publish detailed fund-flow analyses in the coming days.
Step 5: Document everything. Screenshot your Drift transaction history, your deposit records, your open positions. If there is eventually a claims process, insurance filing, or legal action, you will need proof of your losses. Do this now while the data is still accessible on block explorers.
The Bigger Picture: DeFi's Unresolved Security Crisis

$52M in March alone. $285M in a single day in April. The pace of DeFi exploits is accelerating. Photo: Pexels
Drift is not an isolated event. It is the latest - and largest - data point in a trend that shows no sign of slowing. PeckShield's March 2026 report tallied $52 million in DeFi hack losses across the month, with exploits hitting protocols on BSC, Ethereum, and Solana alike. The LML staking protocol on Binance Smart Chain lost $950,000 just hours before Drift was hit, with its token crashing 99.66%. DBXen staking lost $150,000 to a meta-transaction bug in March. Venus Protocol lost $3.7 million to an oracle manipulation attack.
These are not isolated mistakes by careless developers. They represent a systemic failure in how DeFi protocols approach security. The industry's standard approach - pre-launch audits by firms like Trail of Bits, Certik, or Halborn, followed by bug bounty programs - is demonstrably insufficient. Audits check code at a point in time. Protocols evolve. Dependencies update. Oracles change. Admin keys rotate (or do not rotate, which is worse). The attack surface is not static, but the security model treats it as if it is.
Drift Protocol had been audited. Drift Protocol had a bug bounty program. Drift Protocol was backed by Polychain Capital, one of the most respected crypto venture firms in the industry, which led a $23.5 million Series A in January 2024. None of that prevented a $285 million drain.
The uncomfortable truth: DeFi security is an arms race that the defenders are losing. Attackers have several structural advantages. They need to find one vulnerability; defenders need to prevent all of them. Attackers can test their exploits on forked chains with no consequences; defenders cannot. Attackers operate across jurisdictions with effective impunity; defenders are bound by regulations and corporate structures. And increasingly, sophisticated state actors - North Korea's Lazarus Group chief among them - are dedicating nation-state resources to crypto theft.
The Bybit hack was a watershed moment. When Lazarus stole $1.4 billion from a top-five centralized exchange, it proved that even the most security-conscious organizations in crypto were not safe. Drift's hack, if it turns out to be a private key compromise rather than a smart contract bug, would reinforce the same lesson for DeFi: the weakest link is almost never the code. It is the humans and the infrastructure around the code.
Formal verification - mathematical proof that smart contracts behave as intended - remains the gold standard for contract security, but adoption is glacially slow. Runtime monitoring tools that can detect and pause suspicious transactions before they drain a protocol are still in their infancy. Insurance protocols like Nexus Mutual cover only a fraction of DeFi's total value locked. And users, ultimately, bear the brunt of every failure.
What Happens Next

The investigation is still active. Security firms, bridges, and exchanges are coordinating. Photo: Pexels
The next 72 hours will determine the trajectory of this story. Several key questions remain open:
Will Circle freeze the USDC? The $51.6 million in USDC is the most recoverable component of the stolen funds, because Circle has the technical ability to blacklist addresses holding USDC. If Circle acts fast enough - and the attacker has not already converted all USDC to ETH or other permissionless assets - a significant chunk could be frozen. But speed is everything. Every hour that passes gives the attacker more time to swap, bridge, and scatter.
Will Drift publish a postmortem? The team has said it is coordinating with security firms. A detailed technical analysis of the exploit vector is critical - not just for Drift users, but for every other DeFi protocol that shares similar architecture, oracle dependencies, or multisig tooling. If this was a contract bug, other protocols need to know exactly which code pattern was vulnerable. If it was a key compromise, the industry needs to understand how the keys were obtained.
Is there a realistic path to fund recovery? The Euler Finance precedent offers a sliver of hope: in March 2023, the Euler attacker returned all $197 million after two weeks of negotiation. But that was an individual acting alone who eventually decided the heat was not worth it. If the Drift attacker is a state-sponsored group or a professional criminal operation, voluntary return is unlikely. Law enforcement involvement - FBI, Interpol, or local authorities - may be necessary, but crypto investigations move slowly and international coordination even slower.
What happens to Drift's users? Anyone with open perpetual futures positions on Drift is effectively trapped. The protocol is frozen. Their collateral may be gone. If the protocol eventually restarts, the question of how to handle the gap between what the vaults held before the hack and what they hold now will define whether Drift survives or dies. Some protocols have used treasury reserves, insurance funds, or tokenized IOUs to bridge post-hack shortfalls. Drift's ability to do the same depends on factors that are not yet public.
One thing is certain: the $285 million is moving. As of the last confirmed on-chain tracking at 18:54 UTC on April 1, the attacker was still actively converting assets to ETH. The clock is ticking. Every block that passes makes recovery harder.
This is developing. BLACKWIRE will update this article as new information emerges from the investigation.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram