The European Commission does not have a cybersecurity problem. It has a pattern - a repeating sequence of breach, confirmation, and containment that keeps restarting every few weeks. The latest episode, disclosed on March 27, is the most serious yet: attackers accessed the Commission's Amazon Web Services cloud environment, walked out with over 350 gigabytes of data, and then told a cybersecurity publication they have no intention of negotiating. They plan to release everything publicly.
The implications are significant. The European Commission is the EU's top executive body. It drafts legislation affecting 450 million people, negotiates trade deals worth trillions, manages competition enforcement against the world's largest corporations, and coordinates foreign policy across 27 member states. Whatever was sitting in those AWS accounts reflects at least some portion of that work. And it is now in the hands of an unknown threat actor with public-leak intentions.
The Commission issued a careful statement through spokesperson Thomas Regnier, telling TechCrunch that it had "discovered a cyber-attack, which affected part of our cloud infrastructure" and that it had taken "immediate steps" to contain the attack. The internal systems, the Commission said, "were not affected." That framing deserves scrutiny. The breach targeted cloud-hosted infrastructure, specifically the Commission's web presence on the Europa.eu platform, which is not separate from the institution's digital operations. It is the front door.

The attack targeted the Commission's Amazon Web Services cloud account, which hosted the Europa.eu web platform and multiple databases. Photo: Pexels
How the Breach Happened
The threat actor contacted BleepingComputer before the Commission disclosed anything publicly, providing screenshots as proof of access. Those screenshots showed access to Commission employee information and to an email server used by Commission staff. The attacker claimed to have extracted more than 350 gigabytes of data, including multiple internal databases. The method used to gain initial access was not disclosed.
Amazon Web Services issued a statement clarifying its own position: "AWS did not experience a security event, and our services operated as designed." That is a standard and technically accurate response. Cloud providers secure the infrastructure layer. The customer secures the data and the access credentials. The breach appears to have originated from compromised Commission credentials, not from any flaw in AWS itself - making this a case of identity-layer compromise rather than platform vulnerability.
The distinction matters for how the incident gets classified and remediated. If the credentials were stolen, that points to phishing, credential theft through prior malware infection, or leaked API keys. If the access came through an unprotected service or misconfigured bucket, that is a different class of failure requiring different fixes. The Commission has not yet disclosed which vector was used, and its investigation is "ongoing."
"We have taken immediate steps and contained the attack. Risk mitigation measures were also implemented. The investigation is ongoing but we can already confirm that the Commission's internal systems were not affected by the cyber-attack." - European Commission spokesperson Thomas Regnier, March 27, 2026 (via TechCrunch)
Critically, the attacker told BleepingComputer they will not attempt extortion. They are not holding the data for ransom. They intend to release it. That removes the possibility of a quiet resolution through negotiation, and it removes the Commission's ability to manage the disclosure timeline. When the leak happens - and given the attacker's stated intent, it should be treated as a "when" not an "if" - the contents of those 350 gigabytes will become public knowledge. The Commission has no mechanism to stop that.

The threat actor provided BleepingComputer with screenshots as proof of access before the Commission had publicly disclosed anything. Photo: Pexels
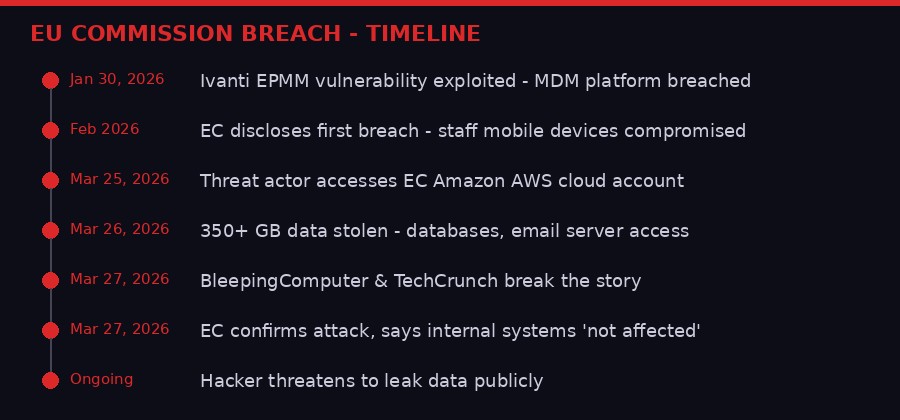
Timeline of the European Commission's breach cascade from January to March 2026. Graphic: BLACKWIRE/PRISM
This Is the Third Breach in Three Months
The March AWS attack is not an isolated event. It is the third significant security failure affecting EU institutions in less than 90 days - and the second to hit the European Commission directly.
On January 30, the Commission discovered that the mobile device management platform used to administer staff devices had been hacked. The attack exploited a code-injection vulnerability in Ivanti Endpoint Manager Mobile software, a flaw that also affected other European institutions simultaneously. The Dutch Data Protection Authority confirmed it was hit by the same vulnerability. Finland's Valtori, a government agency under the Ministry of Finance, was also compromised through the same Ivanti flaw.
The Commission disclosed that first breach in February. At the time, the focus was on mobile device data - staff information tied to devices under management. The January compromise appears distinct from the March AWS breach, suggesting these are separate threat actors operating independently, or potentially the same group that retained residual access from the earlier intrusion.
Just a week before the AWS breach broke publicly, the EU Council sanctioned three Chinese and Iranian companies for orchestrating cyberattacks targeting the critical infrastructure of EU member states. The timing is worth noting. The EU was publicly naming and sanctioning state-linked cyber actors while simultaneously sustaining a breach of its own executive body's cloud environment.
EU Institutions Breached - 2025/2026
- European Commission MDM platform (Jan 2026) - Ivanti EPMM code-injection flaw
- Dutch Data Protection Authority (Jan 2026) - Same Ivanti vulnerability
- Finnish Valtori Agency (Jan 2026) - Ivanti EPMM compromise
- European Commission AWS account (Mar 2026) - 350GB+ exfiltrated
- Attacker intends public data leak - no extortion demanded

The European Commission, headquartered in Brussels, is the EU's top executive body - responsible for legislation, trade, and foreign policy for 450 million people. Photo: Pexels
What 350GB of EU Data Actually Means
Raw storage numbers can obscure what they represent. 350 gigabytes is not a massive haul by the standards of large corporate breaches, but its value is almost entirely determined by what types of data were stored in those accounts.
The attacker's own evidence points to access to Commission employee information and an email server used by staff. If email archives are included, the implications extend well beyond what the Commission's brief statement suggests. Institutional email typically contains internal deliberations, draft positions on legislation, negotiating strategies, communications with member state governments, and correspondence with regulated entities including major technology and pharmaceutical companies currently under Commission investigation.
The Commission is, right now, running enforcement proceedings against Apple, Google, Meta, Microsoft, and numerous other corporations under the Digital Markets Act and Digital Services Act. Any internal communications about those proceedings, about evidence standards, about settlement positions, or about which targets are next in line, would be extraordinarily sensitive. If that material is in the leaked databases, its exposure could compromise active regulatory cases and benefit the targets of those investigations.
The EU's web presence infrastructure also contains operational data: configuration details, system architecture, potentially API keys or service credentials used by Europa.eu's backend systems. A competent attacker - and one who voluntarily disclosed their access before the Commission knew they had it almost certainly qualifies - would have already used that time to map the broader infrastructure and identify lateral movement opportunities.
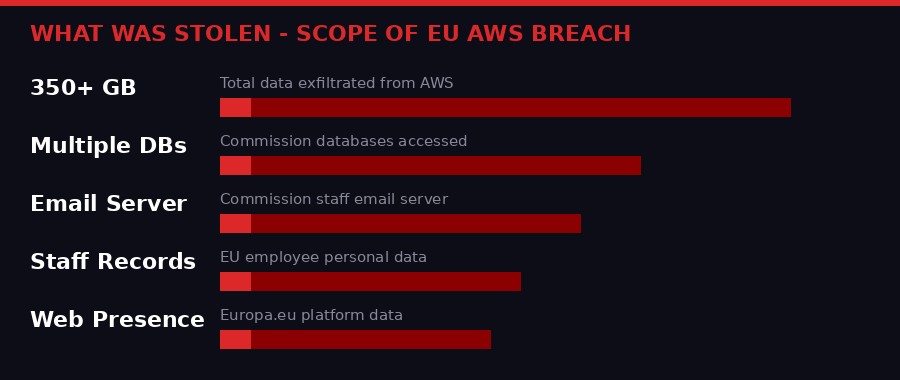
What the attacker claims to have extracted from the European Commission's AWS environment. Graphic: BLACKWIRE/PRISM
The Attacker's Unusual Posture
Most breaches of this scale follow a predictable sequence: compromise, exfiltration, extortion demand, negotiation or public disclosure. The threat actor in the Commission breach departed from that script at step three.
By explicitly telling BleepingComputer that they would not attempt extortion and planned to release the data publicly, the attacker signaled something important: their motivation is not financial. Public exposure, reputational damage to the EU, or ideological opposition to European institutions could all factor into that calculus. So could a desire for the operational security benefits that come from never running a negotiation channel that can be traced.
The decision to contact a cybersecurity publication before the Commission had disclosed anything is also instructive. The attacker controlled the disclosure timeline. The Commission confirmed the breach only after BleepingComputer's story was already filed - not because Commission investigators detected the intrusion first and chose to go public, but because the attacker forced their hand. That sequence reveals a significant gap in the Commission's threat detection capability.
The attacker provided screenshots as proof. Those screenshots have been reviewed by BleepingComputer's editorial team and were deemed credible. Screenshots alone can be fabricated, but the Commission's own confirmation of the attack removes any meaningful doubt about whether the breach occurred. The open question is whether the full 350-gigabyte figure is accurate, and what specific data categories it encompasses.

The threat actor reached out to a cybersecurity publication before the Commission had publicly disclosed the incident, controlling the narrative from the start. Photo: Pexels
The EU's Cybersecurity Legislation Problem
The timing of the breach lands at an awkward moment for European cybersecurity governance. In January 2026 - the same week the first Commission breach was discovered - the European Commission published a proposal for new cybersecurity legislation aimed at strengthening defenses against state-backed actors and criminal groups targeting European critical infrastructure.
The Commission regulates cybersecurity for the rest of Europe's institutional and corporate landscape. The NIS2 Directive, which came into effect across member states in 2024, imposed strict incident reporting and security requirements on operators of essential services throughout the EU. Critical entities - energy companies, water utilities, financial institutions, transport operators - face mandatory security audits, incident reporting within 24 hours, and penalties of up to 10 million euros or 2 percent of global turnover for compliance failures.
The Commission is technically exempt from many of these requirements because it operates under different legal frameworks as an EU institution rather than a member state entity. That exemption now looks like a structural oversight. The institution that writes and enforces cybersecurity rules for 450 million people has been breached twice in three months and appears to be operating without the kind of real-time threat detection that would let it identify a cloud account compromise before the attacker contacts the press.
"These recent security breaches come on the heels of the Commission's January 20 proposal for new cybersecurity legislation to strengthen defenses against state-backed actors and cybercrime groups targeting Europe's critical infrastructure." - BleepingComputer, reporting on the European Commission AWS breach, March 27, 2026
The EU Council's decision to sanction Chinese and Iranian entities for cyberattacks just days before the Commission's own breach became public adds another layer of tension. Sanctioning adversary states while failing to detect an active intrusion into your own cloud infrastructure creates a credibility problem that diplomatic language cannot easily paper over.
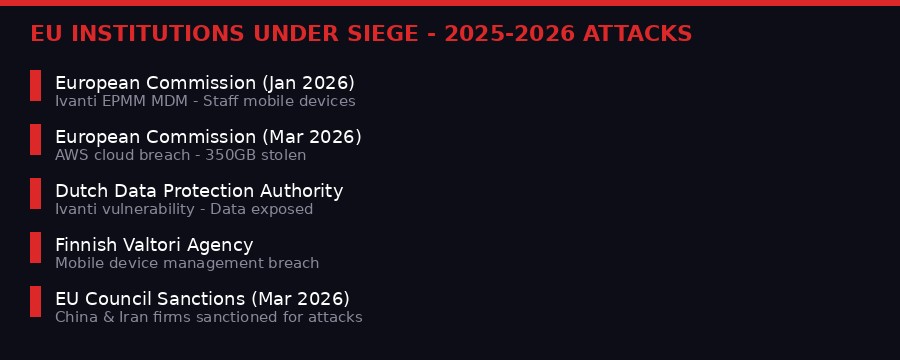
EU institutions have sustained multiple security breaches in rapid succession since late 2025. Graphic: BLACKWIRE/PRISM
Cloud Security and the Shared Responsibility Gap
Amazon's statement - "AWS did not experience a security event, and our services operated as designed" - is both accurate and a textbook example of the shared responsibility model that governs all major cloud platforms. Under that model, AWS secures the physical infrastructure, the hypervisor, the network, and the global backbone. The customer is responsible for everything above that line: access credentials, identity and access management configuration, encryption key management, data classification, and monitoring for suspicious activity.
Government institutions globally have struggled with cloud security under the shared responsibility model. The model is well-documented and well-understood in principle, but its implementation requires organizational maturity that many public sector bodies have not yet developed. Traditional IT security teams were trained to monitor perimeter defenses - firewalls, intrusion detection systems on network boundaries, physical access controls. Cloud security requires a different approach: monitoring API calls, auditing identity and access management policies, setting alerts on anomalous data transfer volumes, and implementing zero-trust architectures that assume any session could be compromised.
A transfer of 350 gigabytes of data from a cloud account to an external destination should trigger automatic alerts in any cloud security posture management tool worth running. The fact that the Commission appears to have learned about this breach from the attacker, not from its own detection systems, suggests those tools either were not deployed adequately or their alerts were not acted upon in time.
AWS provides a suite of security tools for exactly this kind of detection: CloudTrail for API call logging, GuardDuty for threat detection, Security Hub for consolidated security findings, and Macie for identifying sensitive data stored in S3 buckets. Whether the Commission was using these tools, and whether their alerting thresholds were configured appropriately, will likely form a central question in the post-incident review.

Under the cloud shared responsibility model, AWS secures infrastructure while the customer must secure credentials, identity management, and data monitoring. The Commission appears to have failed on the customer side. Photo: Pexels
What Happens When the Data Drops
The attacker's stated plan to release the data publicly sets up a disclosure event that will be qualitatively different from the initial breach. The breach confirmation, while damaging, allows the Commission to frame the narrative with language about "containment" and "risk mitigation." The leak eliminates that framing entirely.
When 350 gigabytes of Commission data becomes downloadable, journalists, researchers, privacy advocates, competing governments, corporate legal teams, and adversarial intelligence services will all be reading through it simultaneously. Any internal documents that touch on active regulatory proceedings, personnel decisions, diplomatic communications, or legislative strategy will be pulled out and published within hours.
For the Commission's active regulatory cases, this creates specific legal risks. Defense lawyers representing companies under investigation by the Commission will immediately examine whether any leaked documents constitute privileged internal deliberations that should not have been accessible to third parties - and whether their clients can use that exposure to challenge the validity of ongoing proceedings. The Commission's lawyers will argue that the breach does not invalidate the legal proceedings. Defendants' lawyers will argue the opposite. European courts will have to sort it out.
The personal data dimension triggers EU law directly. The General Data Protection Regulation, which the Commission itself helped design and which it enforces across Europe, requires controllers to notify relevant supervisory authorities within 72 hours of becoming aware of a personal data breach. The Commission is the data controller for its own employee data. Its DPA notification obligations are not optional. The European Data Protection Supervisor, which oversees EU institutions rather than member state data protection authorities, will be examining whether the Commission met its own 72-hour notification window.

The Commission may face scrutiny under GDPR rules it wrote and enforces, as the breach likely involved personal data of EU employees. Photo: Pexels
The Second-Order Effects No One Is Talking About
The immediate coverage of the Commission breach has focused on the breach itself - what was taken, who did it, what the Commission said. The second-order effects are more significant.
First, the credibility of EU cybersecurity governance. The Commission is simultaneously the entity that writes cybersecurity rules for Europe, enforces them against private sector actors, proposes new legislation to strengthen defenses, and appears unable to detect a 350-gigabyte data exfiltration from its own cloud account. That contradiction will not be lost on member state governments, corporate legal teams, or the Commission's regulatory targets. Every tech company currently under Commission investigation now knows the Commission's digital security posture in more detail than it did last week.
Second, the intelligence value of what was taken. The Commission manages relationships with all 27 EU member state governments, with NATO allies, with trading partners globally, and with major technology companies it regulates. Its internal communications reflect those relationships in ways that raw data does not. A sophisticated intelligence service analyzing the leaked material would not just be reading what the Commission knows - they would be mapping who talks to whom, which positions have internal disagreement, where there is flexibility in the EU's negotiating stances, and which regulatory proceedings are likely to settle versus go to adjudication.
Third, the timing relative to the EU's geopolitical position. Europe is managing the aftermath of the Iran war, US-EU trade tensions, pressure on its defense spending commitments, and a series of major technology regulation cases. The Commission's ability to manage all of those simultaneously depends on secure internal communications. A leak of internal deliberations on any one of those fronts would constrain the Commission's negotiating room in real and immediate ways.
Fourth, the pattern itself. Three breaches in three months across EU institutional infrastructure suggests a systematic targeting campaign, not opportunistic attacks. Whether that campaign is state-directed, financially motivated, or ideologically driven, the pattern means more breaches are likely. The Commission's current response - contain, investigate, issue careful statements - is reactive. A proactive posture would involve treating the current situation as an active campaign and hardening the remaining attack surface before the next incident.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on TelegramThe Road Ahead
The Commission's investigation is ongoing. The European Data Protection Supervisor is expected to open a formal inquiry into the GDPR compliance aspects of the breach. Member state governments are watching to see how the Commission handles disclosure if and when the attacker makes good on the public leak threat.
The Commission published its new cybersecurity legislation proposal in January precisely because it recognized that European institutions were under systematic attack. That legislation now needs to reckon with the reality that the institution proposing it could not prevent two major breaches in the time it took the proposal to be drafted and circulated.
The practical short-term steps are clear: rotate all AWS credentials, audit IAM policies for every service account, enable comprehensive CloudTrail logging if not already active, deploy GuardDuty across all accounts, and conduct a full review of what data was stored in cloud-hosted infrastructure versus air-gapped systems. None of that recovers the 350 gigabytes already gone.
The attacker has the data. They have stated their intention. The Commission is now waiting for a disclosure event it cannot prevent, cannot time, and cannot control the narrative around. For an institution built on regulatory authority and institutional credibility, that is not a comfortable position.
The question the Commission should be answering right now is not just "how did this happen" but "what else do they have access to that we don't know about yet." Given the pattern of the past three months, the cautious assumption is that the answer is more than the current investigation has found.
Key Facts - EU Commission AWS Breach
- Data stolen: 350+ gigabytes including multiple databases
- Platform breached: Amazon Web Services cloud account
- Attacker intends public release - no extortion demanded
- Commission confirmed breach March 27 - after attacker contacted press
- Second Commission breach in 60 days; third EU institution breach overall
- Attacker provided screenshots as proof of access
- Internal systems "not affected" per Commission - cloud infrastructure was
- GDPR notification obligations to European Data Protection Supervisor triggered
- AWS confirmed no failure on their side - shared responsibility model applies
Sources: BleepingComputer (March 27, 2026), TechCrunch/Zack Whittaker (March 27, 2026), European Commission official statement via presscorner, Amazon Web Services spokesperson statement, BleepingComputer reporting on prior Ivanti EPMM incidents (February 2026), EU Council sanctions announcement (March 2026).
