Red Hook Down: Chinese Hackers Breach the FBI's Own Wiretap Network
The bureau that surveils America just got surveilled back. DCS-3000 supply-chain compromise declared a 'major incident' under federal law.

The FBI's surveillance infrastructure was compromised through a commercial vendor, not a direct assault. Photo: Pexels
On April 1, 2026, the FBI formally classified a suspected Chinese cyberattack on its internal surveillance management system as a "major incident" under the Federal Information Security Modernization Act. That single bureaucratic designation carries weight that press releases cannot. Under FISMA, a major incident means the breach is "likely to result in demonstrable harm" to United States national security, foreign relations, or civil liberties. The FBI does not throw that label around. According to Cynthia Kaiser, former deputy assistant director of the FBI's cyber division, she cannot recall the bureau making such a determination about a hack on its own systems since at least 2020.
The system that was breached is called DCS-3000, internally known as Red Hook. It is the unclassified network the FBI uses to manage court-authorized wiretaps, pen register data, trap-and-trace surveillance returns, and Foreign Intelligence Surveillance Act warrant metadata. The attackers did not smash through the FBI's front door. They slipped in through a commercial internet service provider that served as a bureau vendor, threading their intrusion through trusted infrastructure that the FBI's own perimeter defenses were designed to trust. This is a textbook supply-chain attack, the kind of operation that Beijing has refined into a near-art form over the past decade.
What follows is the full anatomy of this breach - how it unfolded, what was compromised, who is likely behind it, why it matters for every active FBI investigation in the country, and what it means for the future of American surveillance infrastructure at a moment when that infrastructure is simultaneously being gutted from the inside.
The Discovery: February 17 and the Abnormal Logs

The DCS-3000 system runs on unclassified FBI infrastructure - technically separate from classified intelligence networks. Photo: Pexels
The breach was first detected on February 17, 2026, when FBI analysts identified abnormal log activity on the Digital Collection System Network. DSCNet, as it is formally designated, is the internal infrastructure that processes wiretap and foreign intelligence surveillance requests across the bureau. The specific component compromised was DCS-3000, sometimes called Red Hook - the system responsible for managing pen registers and trap-and-trace surveillance operations. According to Cybernews, the DCS-3000 client was developed at a cost of $10 million as part of a broader $30 million surveillance technology budget in 2024.
Pen registers log every phone number dialed from a monitored line. Trap-and-trace devices record which numbers contact that line. Combined, these tools map the entire communication network of anyone under FBI surveillance. They do not capture the content of calls - that function belongs to a separate system called Digital Storm, which investigators say was not part of the compromised environment. But the distinction between metadata and content, while legally significant, is operationally misleading. Metadata reveals patterns. It shows who talks to whom, when, how often, and for how long. In intelligence analysis, metadata is frequently more valuable than the conversations themselves.
The FBI initially handled the discovery quietly. But by early March, the bureau informed Congress. On March 5, CNN broke the story publicly, and the FBI issued a terse confirmation to TechCrunch: "The FBI identified and addressed suspicious activities on FBI networks, and we have leveraged all technical capabilities to respond." The statement said essentially nothing while technically saying something. Classic bureau communication.
By March 7, the Wall Street Journal reported that U.S. investigators suspected hackers affiliated with the Chinese government were responsible. The White House, NSA, CISA, and Department of Homeland Security all joined the investigation - an interagency mobilization that signals a top-tier national security event, not a routine IT incident.
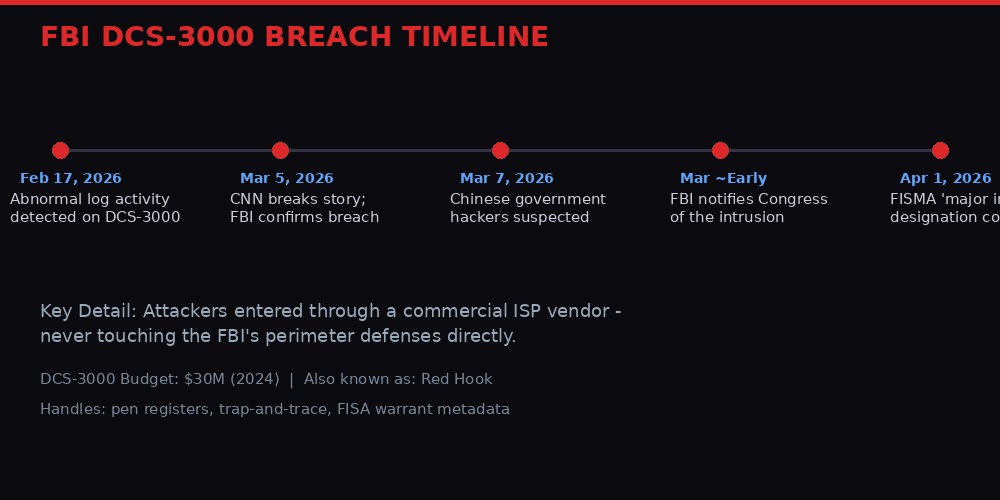
From first detection to FISMA major incident: the 43-day timeline of the DCS-3000 breach.
Inside DCS-3000: What the Hackers Actually Reached

The FBI's surveillance returns - metadata showing exactly who the bureau is watching - were exposed to adversary access. Photo: Pexels
The FBI's congressional notification, reviewed by Politico, described the compromised data with unusual specificity. The affected system is unclassified and contains "law enforcement sensitive information, including returns from legal process, such as pen register and trap and trace surveillance returns, and personally identifiable information pertaining to subjects of FBI investigations."
Break that down. The hackers gained access to:
- Pen register data - every phone number dialed by individuals under FBI surveillance
- Trap-and-trace data - every number that contacted those surveilled individuals
- Personally identifiable information - names, contact details, and other identifying data about people the FBI is actively investigating
- Warrant metadata - information about which court-authorized surveillance orders were in effect
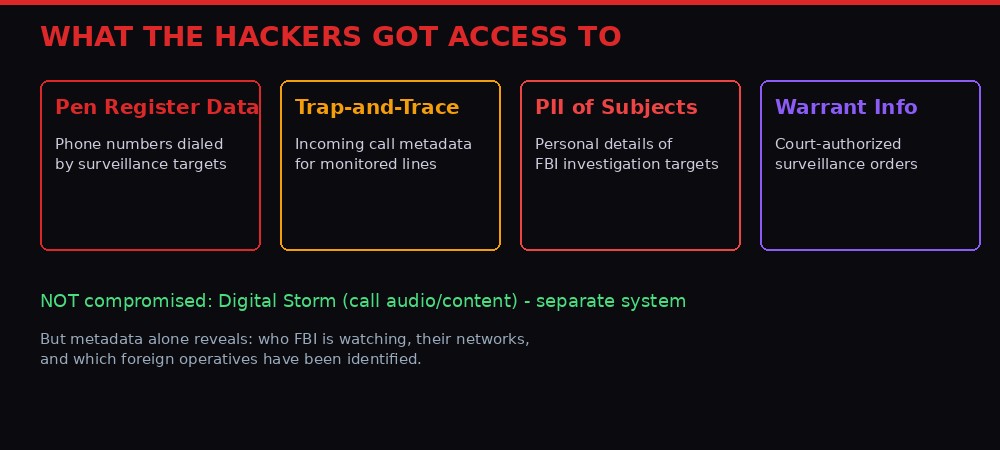
Four categories of sensitive data were within reach of the attackers on the DCS-3000 network.
For a foreign intelligence service, this data is a gold mine. It does not just reveal what the FBI knows. It reveals who the FBI is watching. If Chinese intelligence operatives are operating in the United States - and they certainly are - this data could tell Beijing which of their assets have been identified, which ones are still clean, and which investigations are getting close. It is a counterintelligence map drawn by the FBI itself, now potentially in the hands of its most capable adversary.
As CPO Magazine noted, the breach of metadata alone could allow a foreign intelligence service to identify undercover assets, expose ongoing criminal investigations, and reveal which of their own operatives the FBI has compromised. The operational consequences cascade from there. Investigation subjects could discover they are being monitored and alter behavior. Confidential informants face potential exposure. Criminal defendants may challenge the integrity of evidence gathered through systems that were simultaneously compromised by a foreign adversary.
The Supply Chain Side Door: How Beijing Got In

The attackers exploited a vendor's ISP infrastructure - bypassing the FBI's own perimeter entirely. Photo: Pexels
The attack vector is what makes this breach technically significant and strategically terrifying. According to Aardwolf Security and The Register, the hackers exploited the infrastructure of a commercial internet service provider connected to the FBI's surveillance network. They did not attempt to breach the FBI's perimeter defenses. Instead, they compromised a trusted vendor pathway and rode it straight into the system.
This is the supply-chain attack model that Chinese state-sponsored groups have refined over the past decade. Rather than assaulting a hardened target directly, you identify the softer nodes in its ecosystem - the vendors, contractors, managed service providers, and ISPs that maintain connectivity to the target environment. You compromise one of those, and the target's own trust model becomes your entry ticket. The FBI's perimeter was never bypassed. It was made irrelevant.
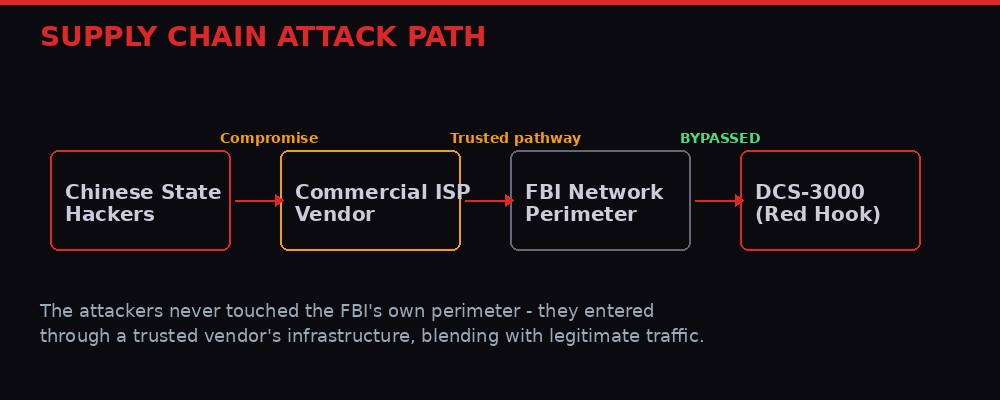
The attackers threaded their intrusion through a trusted vendor, making the FBI's own perimeter defenses irrelevant.
Centraleyes reports that the attackers "relied on careful operational security and infrastructure-level access rather than deploying conventional malware." They blended malicious activity into legitimate network traffic, making detection exponentially harder. When your adversary's traffic looks identical to your vendor's normal operations, your intrusion detection systems are essentially blind.
This pattern should sound familiar to anyone who followed the SolarWinds attack in 2020, when Russian intelligence compromised a software update mechanism to penetrate thousands of organizations including U.S. government agencies. Or the 3CX supply-chain attack in 2023, attributed to North Korea. The lesson has been taught repeatedly, and the U.S. government keeps failing the test: your security perimeter means nothing if your vendors are compromised.
The FBI's congressional notification specifically stated the hackers used "sophisticated techniques" - a phrase that, in the intelligence community, typically signals a well-resourced nation-state actor rather than a criminal group or low-tier threat. The interagency response - pulling in the White House, NSA, CISA, and DHS - reinforces that assessment. This was not some ransomware crew stumbling into federal infrastructure. This was a precision intelligence operation.
Salt Typhoon: The Ghost in America's Wires

Salt Typhoon has become the most prolific Chinese cyber-espionage group targeting American surveillance infrastructure. Photo: Pexels
The FBI has not formally named the threat actor responsible for the DCS-3000 breach. But the methods described in the congressional notification closely resemble those used by Salt Typhoon, the advanced persistent threat group tied to China's Ministry of State Security. Multiple cybersecurity researchers, government officials, and outlets including IBTimes and the Fliegerfaust timeline investigation have drawn the same connection.
Salt Typhoon is not new. But the scale of its operations has crossed a threshold that demands a reckoning with how the United States thinks about cyber defense.
The group first drew widespread public attention in late 2024 when it was revealed to have breached at least nine major U.S. telecommunications providers, including AT&T, Verizon, Lumen Technologies, Charter Communications, and Windstream. That campaign gave the group access to call records covering a substantial portion of the American population. Worse, Salt Typhoon was able to view FBI wiretap data held by those telecoms and steal unencrypted communications from the phone of then-presidential candidate Donald Trump, according to reporting across CNN, Politico, and the Wall Street Journal.
By August 2025, the FBI publicly stated that Salt Typhoon had hacked at least 200 U.S. companies, per TechCrunch. Senator Mark Warner, then chair of the Senate Intelligence Committee, called it "the worst telecom hack in our nation's history." And Democratic lawmakers warned that the telecoms had never fully evicted the group from their networks - that Salt Typhoon likely maintained footholds in systems that were supposedly "remediated."
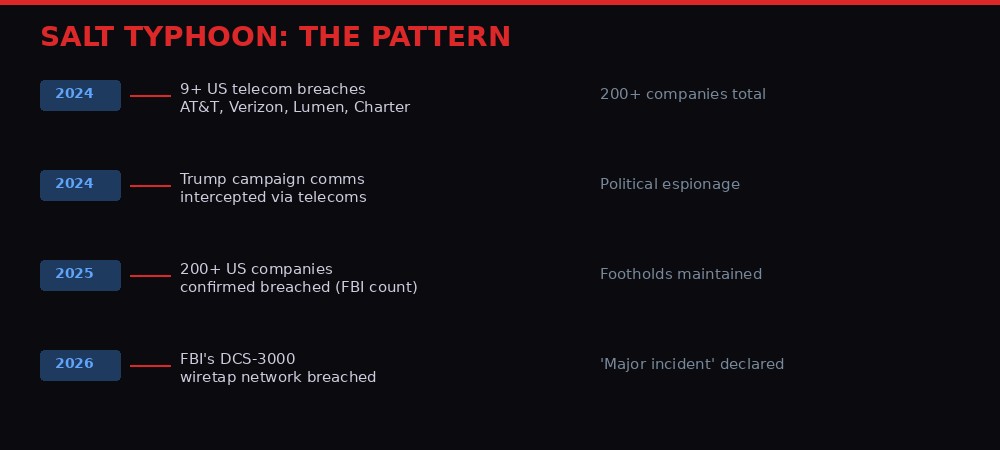
Salt Typhoon's progression: from telecom espionage to breaching the FBI's own wiretap infrastructure.
Now connect the dots. In 2024, Salt Typhoon compromised the telecom layer of American surveillance - the commercial networks through which wiretaps are technically executed. In 2026, suspected Chinese hackers (using Salt Typhoon's signature techniques) compromised the law enforcement layer - the FBI's internal system that manages those same wiretaps. As Fliegerfaust put it: "Together, those two breaches may give Beijing visibility into both the commercial telecom layer and the law enforcement layer of American surveillance."
That is not a coincidence. That is a campaign. Beijing is not hacking random systems for bragging rights. It is systematically mapping and penetrating every node in the American surveillance apparatus, from the private-sector telecoms that carry the data to the federal agency that orders and collects it. If the pattern continues, the classified intelligence layer is next - and maybe it already has been compromised. We would not necessarily know.
The FISMA Threshold: Why "Major Incident" Changes Everything

The FISMA major incident designation obligates the FBI to brief Congress and produce a formal remediation plan. Photo: Pexels
The formal classification of this breach as a "major incident" under FISMA is not performative. It triggers a cascade of legal obligations and political consequences that the FBI cannot quietly manage away.
FISMA requires any federal agency to notify Congress within seven days of determining that a digital intrusion is "likely to result in demonstrable harm" to U.S. national security, foreign relations, public confidence, or civil liberties. According to Kaiser, the former FBI cyber division deputy assistant director, "Thresholds under FISMA are quite high, and only a few agencies declare a major cyber incident every year." The fact that the FBI applied this designation to a hack on its own systems - not a third party's, not a contractor's, but its own internal surveillance infrastructure - is extraordinary.
The immediate consequences are concrete. The FBI must brief relevant congressional oversight committees in detail. It must produce a formal remediation plan and submit to scrutiny from the Office of Management and Budget. The designation also raises the political temperature dramatically. Members of Congress now have a legal hook to demand briefings, documents, and answers that the bureau might otherwise resist providing.
The timing of the formal designation - April 1, roughly six weeks after the initial detection on February 17 - raises its own questions. The bureau detected the breach in mid-February, notified Congress in early March, but did not formally classify it as a major incident until April. What changed? One possibility: the investigation revealed the scope of compromised data was larger than initially understood. Another: the bureau was dragging its feet and congressional pressure forced the classification. Either way, the six-week gap between detection and formal designation deserves scrutiny.
There is another uncomfortable wrinkle. The Politico reporting noted that the FBI breach "does not appear to be connected to a recent Iranian-linked compromise of FBI Director Kash Patel's personal emails." In late March, the Handala Hack Team - an Iran-linked group - published more than 300 emails from Patel's personal inbox spanning 2010 to 2019. That means the FBI was dealing with at least two separate nation-state cyber operations simultaneously targeting its leadership and infrastructure. When you count the 2023 Epstein files breach (disclosed publicly in March 2026 by Reuters), that makes three distinct intrusions touching the FBI in a single month. Three separate adversaries. Three separate failures.
The Budget Knife: Gutting Cyber Defense While Under Attack

Federal cyber agencies face simultaneous budget cuts and personnel losses while confronting state-sponsored intrusions. Photo: Pexels
This breach does not exist in a vacuum. It arrives at a moment when the FBI's cyber capabilities are under unprecedented strain - not from adversaries, but from Washington itself.
The Trump administration's proposed 2026 budget includes an approximately $500 million cut to the FBI. Critics argue this has already weakened the bureau's cyber defense posture. Cybernews reporting noted that "many of the FBI's top cyber leaders have reportedly left, retired, or been fired," draining institutional knowledge that is not easily replaced. When your most experienced counterintelligence cyber analysts walk out the door, they take with them the pattern recognition and institutional memory that helps detect anomalies like abnormal log activity on DCS-3000.
The FBI is not alone. CISA, the Cybersecurity and Infrastructure Security Agency that would normally be a key partner in responding to exactly this kind of breach, is projected to lose a third of its workforce under the 2026 budget, according to State of Surveillance reporting. The agency's budget has been cut from $3.0 billion and 4,021 positions in FY2025 to significantly less, per SOCRadar analysis. Meanwhile, the FBI, NSA, and CISA all withdrew from RSA 2026, the largest cybersecurity conference in the world - a federal boycott that left the private sector scrambling to fill the void.
Sally Vincent, Senior Threat Research Engineer at Exabeam, summarized the situation to Cybernews: "The breach comes at a time when federal cybersecurity capabilities are under increasing strain." That is the diplomatic version. The undiplomatic version is that the United States is dismantling its own cyber defense apparatus while simultaneously being attacked by the most sophisticated state-sponsored hacking operations in the world.
There is a bitter irony here. The FISMA framework that triggered the major incident designation was designed to ensure federal agencies maintain adequate cybersecurity. The agencies are now being starved of the resources needed to comply with that same framework. You cannot have a functioning cybersecurity posture when your budget is being slashed, your experts are being fired, and your adversaries are being funded by a nation-state with functionally unlimited resources dedicated to cyber operations.
The FISA 702 Collision: Surveillance Power Meets Surveillance Failure

The FBI breach lands directly in the middle of the politically charged FISA Section 702 reauthorization debate. Photo: Pexels
The DCS-3000 breach lands in the middle of one of the most politically charged surveillance debates in Washington: the reauthorization of FISA Section 702. This provision, which allows the U.S. government to conduct warrantless surveillance on foreigners located abroad (but inevitably sweeps up American communications in the process), was last reauthorized in April 2024 for just two years. It is now due for renewal, and Congress is deeply divided.
Section 702 is the legal framework under which much of the surveillance managed through systems like DCS-3000 is authorized. The FBI has been one of the most aggressive institutional defenders of the program, arguing it is essential for national security. But here is the problem: the bureau is simultaneously arguing that it needs broad surveillance powers while demonstrating that it cannot secure the infrastructure those powers depend on.
The Electronic Frontier Foundation has argued that Section 702 "should not be reauthorized without any additional safeguards or oversight." The Brennan Center for Justice has published detailed analysis of how Section 702 has been used for warrantless access to Americans' communications. Three reform bills are currently before Congress: SAFE, PLEWSA, and GSRA.
The DCS-3000 breach hands ammunition to both sides. Critics of warrantless surveillance can point to the breach and ask: why should we expand the government's power to collect data when it cannot even protect the data it already has? Defenders can counter that the breach proves the sophistication of Chinese cyber operations and argues for more, not less, intelligence collection authority.
But here is the deeper issue neither side wants to confront. The Salt Typhoon campaign - from the 2024 telecom breaches to the 2026 FBI breach - fundamentally undermines the architecture on which FISA surveillance depends. The system assumes that surveillance data, once collected, remains in the hands of U.S. law enforcement and intelligence agencies. That assumption is now demonstrably false. Chinese hackers have penetrated both the collection infrastructure (the telecoms) and the management infrastructure (the FBI's own systems). The question is no longer whether Section 702 should exist. The question is whether the surveillance apparatus it authorizes can be trusted to function at all.
Volt Typhoon: The Other Chinese Threat Nobody Talks About Enough

While Salt Typhoon targets intelligence systems, Volt Typhoon has burrowed into American critical infrastructure. Photo: Pexels
The DCS-3000 breach is occurring against the backdrop of a second, parallel Chinese cyber campaign that receives less attention but may pose an even greater threat. Volt Typhoon, a separate Chinese state-sponsored group, has burrowed deep inside U.S. critical infrastructure - including ports, water treatment facilities, and energy substations.
Where Salt Typhoon is about espionage - stealing information - Volt Typhoon is about pre-positioning. U.S. intelligence officials have warned that Volt Typhoon's operations appear designed to establish persistent access to infrastructure that could be disrupted or destroyed during a military conflict, particularly over Taiwan. These are not systems being hacked for their data. They are being hacked so that China can flip a switch during a crisis and turn off the lights, the water, or the port operations in targeted American cities.
Politico's reporting on the DCS-3000 breach referenced both groups: "One Chinese hacking group dubbed Volt Typhoon has burrowed deep inside critical infrastructure across the United States - including ports, water facilities and energy substations - while a second group labeled Salt Typhoon has breached some of the most sensitive surveillance systems the country has."
Consider the combined picture. Beijing now has demonstrated access to the commercial telecommunications layer (Salt Typhoon, 2024), the law enforcement surveillance layer (suspected Salt Typhoon, 2026), and the physical critical infrastructure layer (Volt Typhoon, ongoing). These are not separate problems. They are different facets of a single strategic reality: China is preparing a digital battlefield that spans American communications, intelligence, and infrastructure. If Taiwan becomes a flashpoint, Beijing will not just contest control of the Taiwan Strait. It will contest America's ability to function domestically.
The FCC has taken some action, banning Chinese-manufactured routers over security risks in March 2026, per the Foundation for Defense of Democracies. But as that same analysis noted, Salt Typhoon's previous operations "predominantly targeted known vulnerabilities in Western-produced devices rather than relying on new points of entry into critical systems." Banning Chinese routers addresses one vector while the adversary pivots to others. It is playing whack-a-mole against an opponent who has already mapped the entire arcade.
What Happens Next: The Investigation, the Politics, and the Reckoning

The FBI must now produce a remediation plan while simultaneously fighting to retain the cyber staff needed to execute it. Photo: Pexels
Several critical questions remain unanswered. The FBI has not confirmed whether any data was successfully exfiltrated from the compromised network. There is a meaningful difference between an adversary gaining access to a system and an adversary successfully extracting its contents. But the FISMA major incident designation - which requires "demonstrable harm" to national security - strongly suggests the bureau concluded that the damage went beyond mere unauthorized access.
Formal attribution is still pending. The FBI has not officially named Salt Typhoon or any specific Chinese group. But the convergence of evidence - the supply-chain attack vector, the targeting of surveillance infrastructure, the sophistication of techniques, the pattern matching with previous Salt Typhoon operations - points overwhelmingly in one direction. When formal attribution does come, it will trigger diplomatic consequences. Under the Obama-era 2015 agreement, the United States and China agreed not to conduct cyber-enabled theft of intellectual property. That agreement has been effectively dead for years, but formal attribution of espionage against the FBI's own surveillance systems would represent a new escalation, one that demands a policy response beyond the usual sanctions and indictments.
Congress has several potential levers. The FISA Section 702 reauthorization debate provides an immediate vehicle for attaching cybersecurity requirements to surveillance authority renewal. Senator Cantwell has already been pushing telecoms for vulnerability documentation related to Salt Typhoon since the 2024 breaches. The major incident designation gives congressional committees the legal standing to demand detailed briefings on the FBI's cybersecurity posture, its vendor management practices, and the specific remediation steps being taken.
But the most significant variable may be the simplest: money. You cannot mount an adequate cyber defense on a shrinking budget with a depleted workforce. The DCS-3000 breach is what happens when a $30 million system is defended by an agency losing $500 million and its top cyber talent simultaneously. Every fired analyst, every unfilled position, every canceled training program is a gap in the wall. Beijing does not need to find zero-day vulnerabilities when you are handing them structural ones.
Key Takeaways
- The FBI classified a Chinese hack of its DCS-3000 wiretap system as a "major incident" under FISMA - the most serious cybersecurity designation available, triggered by "demonstrable harm" to national security.
- The breach entered through a commercial ISP vendor, not the FBI's own perimeter - a supply-chain attack that made the bureau's defenses irrelevant.
- Compromised data includes pen register returns, trap-and-trace metadata, and PII of investigation subjects - revealing not what the FBI knows, but who it is watching.
- Salt Typhoon is the primary suspect, extending a campaign that previously hit 200+ telecom companies and intercepted Trump campaign communications.
- Combined with Volt Typhoon's infrastructure operations, China now has demonstrated access to America's telecom, surveillance, and critical infrastructure layers.
- The breach arrives during FBI budget cuts (~$500M), mass staff departures, and the FISA 702 reauthorization debate - creating a perfect storm of reduced capacity meeting escalating threat.
The FBI has been hacked before. Every large organization has. But there is a difference between a data breach and a counterintelligence catastrophe. When an adversary gains access to the system that manages who you are surveilling and how, they have not just stolen data. They have compromised the integrity of your intelligence apparatus. Every active investigation that touched DCS-3000 during the compromise window is now tainted by the possibility that the target knew they were being watched. Every confidential informant whose identity was stored in the system faces a risk that cannot be undone.
Red Hook is down. The question is whether anyone in Washington has the budget, the personnel, or the political will to bring it back up in a way that can withstand the next assault. Based on the current trajectory - more cuts, fewer experts, deeper adversary penetration - the honest answer is: probably not.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram