America's Router Ban: The FCC Just Locked China Out of Your Home Network
The device that connects your home to the internet just became a geopolitical battleground. On March 23, 2026, the Federal Communications Commission published an order banning the import and authorization of all new consumer-grade routers manufactured in foreign countries - a sweeping move that effectively targets China, which controls roughly 60 percent of the global consumer router market according to Reuters.
The FCC's order states that "consumer-grade routers produced in foreign countries pose unacceptable risks" to U.S. national security. It follows a formal determination by both the Departments of Defense and Homeland Security that foreign-made home network hardware represents a critical vulnerability in American digital infrastructure.
This is not a Huawei-style ban on a single company. It is a categorical exclusion of an entire class of hardware from an entire category of foreign manufacturing. Nothing like it has ever been done to consumer electronics at this scale. The second-order effects - for router prices, for the companies that make them, for U.S. manufacturing capacity that doesn't yet exist - will take years to fully materialize.

What the FCC Order Actually Does
The order, published late Monday March 23, updates what the FCC calls its "Covered List" - the agency's running registry of communications technology deemed to threaten national security. Adding all foreign-made consumer routers to this list means the FCC will no longer authorize new models for use in the United States.
Authorization matters here. Every piece of radio-frequency equipment sold in the US - including routers, which use WiFi radio frequencies - must receive FCC equipment authorization before it can be legally imported or sold. By removing that pathway for foreign-made consumer routers, the FCC has effectively closed the door on the next generation of home network hardware coming from overseas factories.
Critically, the ban does not require anyone to throw away the router they currently own. Existing devices in homes and businesses are unaffected - there is no recall, no enforcement against current equipment. What changes is the pipeline for new products. Routers in warehouses and already in the retail channel occupy a legal gray area the order did not address.
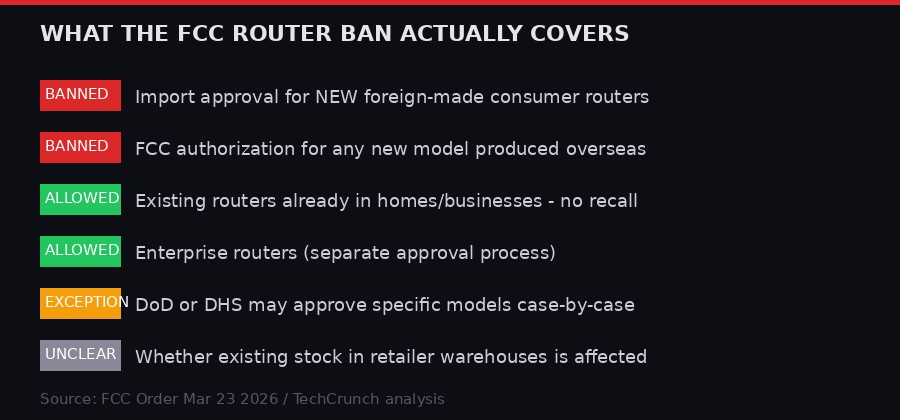
The exceptions written into the order are narrow. The Department of Defense or Department of Homeland Security may grant case-by-case approvals for specific models if they determine a particular device meets security requirements. This safety valve suggests the intent is not to create an absolute embargo but to create a security review bottleneck that foreign manufacturers - particularly Chinese ones - would struggle to pass.
FCC Chairman Brendan Carr said the agency would "continue to do our part in making sure that U.S. cyberspace, critical infrastructure, and supply chains are safe and secure," per prepared remarks reported by TechCrunch.
"China's hackers are positioning on American infrastructure in preparation to wreak havoc and cause real-world harm to American citizens and communities, if or when China decides the time has come to strike." - Christopher Wray, former FBI Director, testifying before Congress
The Typhoon Hackers: Why This Ban Exists
To understand why the U.S. government moved against home routers specifically, you need to understand the family of Chinese state-backed hacking operations that have spent the past several years turning those devices into weapons.
U.S. intelligence agencies have publicly identified at least four distinct Chinese hacking groups - collectively called the Typhoon family - each assigned a different strategic mission inside American networks. Together they represent what officials have called an "epoch-defining threat."

Volt Typhoon is the most alarming. Microsoft first identified the group in May 2023, finding it had been burrowing into U.S. critical infrastructure - water systems, energy grids, transportation networks, military logistics - since at least mid-2021. The group's purpose is not espionage in the traditional sense. The intelligence community believes Volt Typhoon is pre-positioning for destructive attacks intended to paralyze U.S. military mobilization in the event of a conflict over Taiwan. By January 2025, more than 100 confirmed Volt Typhoon intrusions had been discovered across the US and its territories. A large concentration targeted Guam - the Pacific island that houses critical forward military assets.
Volt Typhoon achieved much of its reach by compromising routers. The group hijacked end-of-life home and small office routers to build an anonymizing relay network, routing its malicious traffic through devices in American homes and businesses to disguise its Chinese origin. The FBI disrupted this botnet via court-sanctioned operation in January 2024, but the underlying vulnerability - poorly secured home routers that can be conscripted into hostile infrastructure - remains.
Flax Typhoon ran a variant of the same playbook on an even larger scale. Operating under the cover of a Beijing-based cybersecurity company, Flax Typhoon built a botnet of at least 126,000 hijacked internet-connected devices in the United States alone, plus thousands more internationally. The FBI seized this botnet in September 2024. But the point stands: home routers, running outdated firmware, with default passwords, are effectively free real estate for nation-state hackers building operational infrastructure.
Salt Typhoon took a different angle. Rather than compromising home devices, Salt Typhoon went after the routers that sit at the edge of major telecommunications networks - specifically Cisco gear. Over the course of what researchers describe as one of the broadest hacking campaigns in recent history, Salt Typhoon compromised AT&T, Verizon, T-Mobile, Lumen (formerly CenturyLink), Viasat, Charter Communications, and Consolidated Communications in the United States, according to reporting by TechCrunch. It also hacked the National Guard networks of at least one US state, gaining lateral access to networks across every state and several territories.
Silk Typhoon - previously known as Hafnium - has been active since at least 2021 targeting financial systems, including a campaign against the US Treasury in December 2024. Where the other Typhoon groups focus on telecommunications and critical infrastructure, Silk Typhoon appears more interested in financial intelligence and government data.

Salt Typhoon's Global Reach - and Why Routers Are the Entry Point
Salt Typhoon's victim list stretches across six continents. Confirmed or attributed hacks span at least 200 organizations globally, according to FBI officials cited by TechCrunch. The geographic breadth is staggering.
In North America: Canada confirmed its top telecommunications firms were compromised, with hacked Cisco routers at the network edge serving as the access point. In South America: Trend Micro observed Salt Typhoon activity in Brazil. Across Asia: compromised networks in Taiwan, the Philippines, Myanmar, Bangladesh, Indonesia, Malaysia, Thailand, and Japan. In Africa: at least one South African telecommunications provider targeted. In Europe: the British government confirmed "a cluster of activity" from Salt Typhoon across UK networks. Australia and New Zealand both issued formal warnings and confirmations of compromise across their telecom, government, transport, and military sectors.

The consistent theme across nearly every confirmed Salt Typhoon intrusion: Cisco routers at the network edge, running unpatched firmware or exploited via known vulnerabilities, served as the entry point. The group's focus on the lawful intercept systems that telecoms are legally required to install - the backdoors built in specifically for law enforcement wiretaps - gave China access not just to bulk call records but to the surveillance infrastructure of American intelligence agencies themselves.
The FBI responded by publicly urging Americans to switch to end-to-end encrypted messaging apps in December 2024, an unusual and blunt admission that the telecom layer could not be trusted. This was not a fringe security advisory. It was the federal government acknowledging that a foreign adversary had compromised the communications backbone.
"Salt Typhoon is behind one of the broadest hacking campaigns in recent years, targeting some of the world's largest phone and internet companies and stealing tens of millions of phone records about senior government officials." - TechCrunch analysis, March 9, 2026
The Contradiction at the Heart of the FCC's Move
The FCC order lands with an inherent tension that its critics have already started pulling at. The agency provided no evidence that US-made consumer routers are more secure than foreign ones. And there is a glaring biographical problem with the announcement's architect.
FCC Chairman Brendan Carr - who is now claiming credit for this national security crackdown - was one of two FCC commissioners who voted in November 2025 to scrap cybersecurity rules requiring telecom operators to secure their lawful intercept systems from unauthorized intrusions. In other words: the same official who removed the rules that would have forced telecoms to lock down the very access points Salt Typhoon exploited is now banning the hardware category that Volt and Flax Typhoon abused.
This is not a coherent security posture. It is piecemeal hardware nationalism wrapped in security language.
The order also does not address the fact that Salt Typhoon's most devastating intrusions targeted American-brand Cisco routers - enterprise and carrier-grade devices that are categorically not covered by this ban. The consumer router ban would have done nothing to stop the AT&T, Verizon, or T-Mobile breaches. The threat the ban is designed to address - Volt and Flax Typhoon's exploitation of home routers as relay infrastructure - is a firmware and configuration security problem as much as a manufacturing origin problem.
A Chinese-designed router running properly updated firmware and a strong password is arguably more secure than a US-designed router sitting on a shelf for five years without a single security patch. The FCC did not engage with this distinction.

Market Disruption: What Happens to Router Prices
The market implications are significant. Reuters reported that China commands roughly 60 percent of the global consumer router market. The major brands that dominate American retail - TP-Link, which commands the single largest US market share by unit volume, Tenda, Netgear's ODM supply chain, and much of the hardware inside devices sold under brands like Asus and Linksys - either manufacture in China or rely heavily on Chinese contract manufacturers.
TP-Link specifically has been under US government scrutiny since late 2024, when the Commerce Department opened an investigation into the company following reports that its routers were used in cyberattacks on American organizations. The investigation was still ongoing as of early 2026. The FCC's blanket ban on foreign-made consumer routers effectively accelerates whatever outcome the Commerce probe might have reached for TP-Link - and extends it to every competitor.
The question that the order does not answer is: who fills the gap? The US domestic router manufacturing industry is essentially non-existent at consumer scale. Companies like Cisco and Juniper make enterprise and carrier-grade networking gear in the United States, but the high-volume, low-margin home router market has been dominated by Asian manufacturers for decades. Building a domestically sourced supply chain for consumer routers would take years and cost billions.
In the interim, the most likely outcome is a price increase for American consumers. If the exception pathway through DoD and DHS remains workable, some foreign manufacturers will pursue it, creating a two-tier market: DoD/DHS-approved foreign devices at premium prices alongside whatever domestic alternatives emerge. More likely, the short-term result is market tightening, with existing inventory repriced upward and new product launches delayed or killed for the US market.

The Deeper Problem: Firmware, Not Just Flags
Security researchers have been making the case for years that the most dangerous element of the home router threat is not where the device was manufactured - it is what the device is running. And in this regard, the FCC ban is attacking a shadow while the substance of the problem remains unaddressed.
The Volt Typhoon botnet relied on end-of-life routers. "End-of-life" is a manufacturer's designation for a device that will no longer receive security updates. Tens of millions of these devices remain active in American homes and businesses, running firmware that has not been patched in years, exposing vulnerabilities that are publicly catalogued in NIST's National Vulnerability Database. A hacker does not need to install a backdoor at the factory. They just need to find a device running a three-year-old firmware version with a known authentication bypass, which takes approximately 30 seconds with readily available scanning tools.
The FCC order does nothing about this installed base. The 60 million-plus foreign-made routers already deployed in the United States continue operating under the same risk conditions they operated under before March 23. The ban stops new Chinese routers from entering the country but does nothing to address the existing attack surface.
A more targeted and technically coherent approach would have combined the ban with mandatory security certification requirements - something like the UK's Product Security and Telecommunications Infrastructure Act, which requires manufacturers to publish minimum supported periods for security updates, ban default passwords, and report vulnerabilities. The US does not yet have an equivalent at the consumer device level. The FCC's order is blunter: stop the imports, figure out the rest later.

Geopolitical Context: Routers in the Taiwan Equation
To fully understand why the US government moved on this issue now, in March 2026, you need to pull back and look at the strategic context. The Typhoon hacking operations are not primarily motivated by financial gain or espionage in the Cold War sense. They are pre-war infrastructure operations. The goal, as stated by multiple senior US intelligence officials, is to position China to deliver crippling cyberattacks on American critical infrastructure in the opening hours of any military confrontation over Taiwan - specifically targeting the military's ability to mobilize and project force to the Pacific.
A router in a home in Iowa sounds like it has nothing to do with Taiwan. But chain the logic: Volt Typhoon converts home routers into relay nodes. Those relay nodes anonymize traffic. Anonymized traffic is used to access operational planning networks, defense contractor systems, and critical infrastructure controls. The compromised networks include systems on Guam - the forward staging area for any Pacific military operation. Interrupt the US military's logistics and communications in the first 72 hours of a conflict, and the calculus of intervention changes dramatically.
The router ban is, viewed through this lens, less a cybersecurity policy and more a geopolitical signal. It is the United States government formally acknowledging that it views Chinese hardware in American homes as a latent threat asset in a potential war scenario - and taking the first legislative step to remove it from the equation for future deployments.
"Volt Typhoon represents a new breed of China-backed hacking groups; no longer just aimed at stealing sensitive U.S. secrets, but rather preparing to disrupt the U.S. military's ability to mobilize." - John Hultquist, Chief Analyst, Mandiant
The ban comes as the US is already engaged in military operations in the broader Middle East and as tensions around Taiwan remain elevated. The timing suggests this is not coincidental. The FCC published its order on March 23, 2026 - the same week the US military is managing multiple active theaters. Reducing avenues for foreign adversaries to preposition inside US networks during a period of heightened military activity is consistent with a broader hardening posture.
What Comes Next: The American Router Industry Problem
The FCC has created a demand mandate without creating a supply solution. American companies capable of manufacturing consumer routers at scale do not currently exist in meaningful numbers. Cisco's consumer brand, Linksys, was sold to Belkin years ago. Belkin itself sources hardware from Asian manufacturers. The supply chain problem is not a political problem that trade policy can quickly solve - it is a decade-long industrial development challenge.
The most plausible short-term scenarios are: first, existing inventory gets repriced and stretched; second, Taiwanese manufacturers - who have a complicated but distinct relationship with the US government compared to mainland Chinese firms - apply for the DoD/DHS exception pathway and potentially capture significant market share; third, US firms like Qualcomm or Intel, which supply the chip platforms inside routers, partner with North American or European manufacturing operations to bring products to market under domestic authorization.
Taiwan Semiconductor Manufacturing Company, which fabricates the majority of the world's advanced router chips, is already in the process of expanding US manufacturing capacity under the CHIPS Act framework. But chip fabrication in Arizona does not automatically translate to router assembly in the United States. The vertical integration required to produce a domestic router from US-designed silicon to final device is a multi-year and multi-billion dollar project.
The router ban also raises a practical enforcement question. The FCC authorizes devices but does not conduct customs enforcement at the border - that falls to Customs and Border Protection and the Department of Commerce. The interagency coordination required to actually stop foreign routers at US ports of entry is a different operational challenge from publishing an order that prohibits their authorization. History with Huawei equipment shows that enforcement of such restrictions can be incomplete for years.

The Bigger Picture: Hardware as National Security Terrain
The FCC's router ban sits within a broader and accelerating reconfiguration of how the United States government thinks about technology hardware. The Huawei ban in 2019 was the opening move - barring a single company from critical telecom infrastructure. The CHIPS Act of 2022 was the construction response - trying to rebuild domestic semiconductor fabrication. The TikTok legislation was a software and data sovereignty assertion. The router ban is the consumer hardware front of the same campaign.
Each of these moves shares a common underlying logic: the physical and digital layers of American infrastructure have been penetrated by Chinese equipment and software during a period of economic integration that is now being unwound under security pressures. The unwinding is messy, expensive, and slow - but it is real and it is accelerating.
The router ban has specific teeth that some prior actions lacked. Unlike executive orders that created carve-outs for existing contracts or grandfather clauses that stretched for years, the FCC's Covered List mechanism operates through authorization denial - if you cannot get FCC authorization, you cannot legally sell the product in the US market. There is no grandfather clause for new products. The cut is clean.
The question is whether it is a meaningful cut or a largely symbolic one. With 60 million or more Chinese-made routers already deployed in American homes, the operational threat landscape does not change on March 24, 2026. It changes slowly, over years, as that installed base is replaced - by what, nobody has fully articulated. The FCC has defined the problem clearly. The solution remains an industrial and policy project that has not yet begun in earnest.
Bottom line: The FCC's foreign router ban is the most aggressive hardware security action in US consumer electronics history. It correctly identifies the threat and takes a decisive step. But it cannot fix the 60 million-device installed base already in American homes, does not address the firmware and credential security failures that made those devices exploitable, and has no credible domestic manufacturing industry waiting to fill the gap. Banning the import is step one. Building the alternative is the decade-long project nobody has quite committed to yet.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram