Fedware: Inside the Government Apps That Spy Harder Than the Apps They Banned
The White House app ships with a sanctioned Chinese company's tracking SDK. The FBI app serves you ads while reading your phone identity. FEMA demands 28 permissions to show you weather alerts. Welcome to the era of federal spyware hiding in plain sight on the Google Play Store.
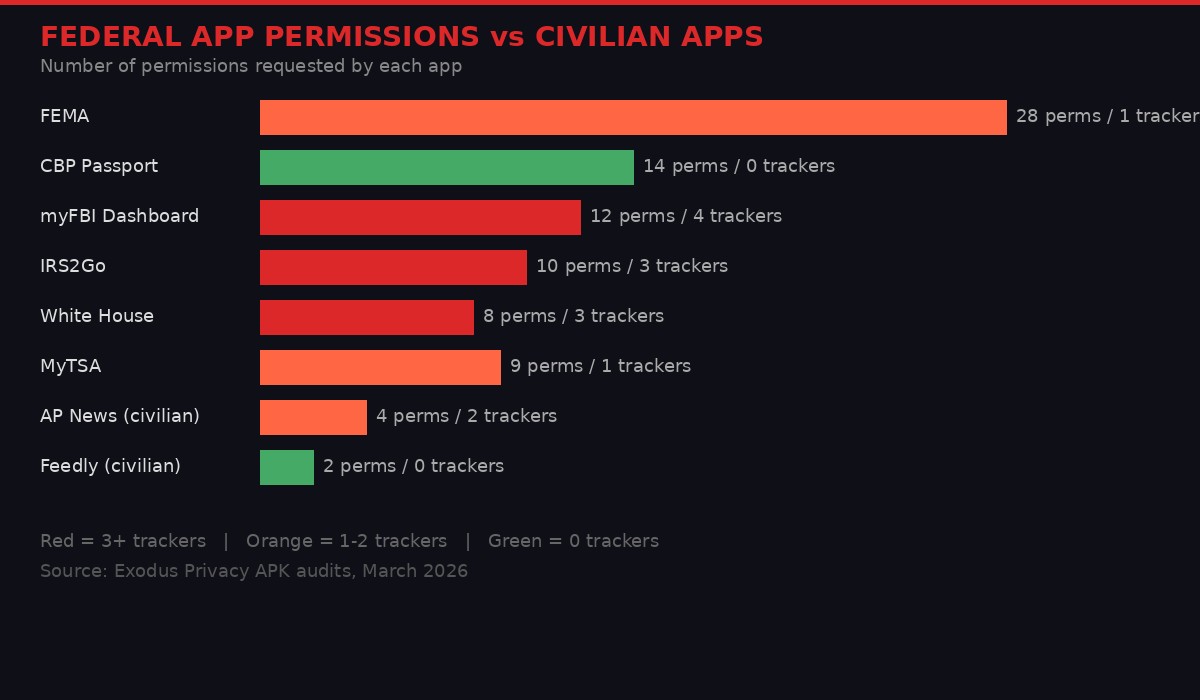
Federal government apps request dramatically more permissions than civilian apps delivering similar content. Source: Exodus Privacy audits.
The United States government spent the last five years telling Americans that Chinese technology companies are an existential threat to their privacy. TikTok was banned. Huawei was blacklisted from American telecom networks in 2019 under executive order. ZTE was sanctioned. Congressional hearings were held. Intelligence briefings were leaked to reporters who dutifully produced stories about the invisible hand of Beijing reaching through your smartphone screen.
Then, on March 27, 2026, the Trump White House released its own app - and shipped it with Huawei Mobile Services Core embedded in the code.
This is not a metaphor. This is not an inference drawn from suspicious network traffic. This is a verifiable fact, confirmed by Exodus Privacy, the nonprofit organization that audits Android application packages for embedded trackers and permission requests. The official app of the sitting President of the United States contains tracking infrastructure built by the very Chinese company that same president's administration sanctioned as a national security threat.
And the White House app is, somehow, one of the milder offenders. A systematic audit of 13 federal government apps reveals an ecosystem of surveillance tools masquerading as public information services - requesting permissions that would trigger congressional hearings if a Chinese app dared ask for them.
Security researcher Sam Bent coined a term for this: Fedware. The word deserves to stick.
The White House App: Version 47.0.1

The White House released an app promising "unparalleled access." It delivered unparalleled surveillance instead. Photo: Unsplash
Let's start with the version number, because it tells you everything about the mindset behind this project. The White House app is labeled version 47.0.1 - Trump being the 47th president. This is not software engineering. This is branding. And the substance matches the aesthetic: all show, no accountability.
The app markets itself as a gateway to press releases, livestreams, and policy updates from the Trump administration. This is content that any RSS feed delivers with a single permission: network access. Your browser does it with zero additional permissions. The White House's own website does it. There is no functional reason for this content to require a dedicated app.
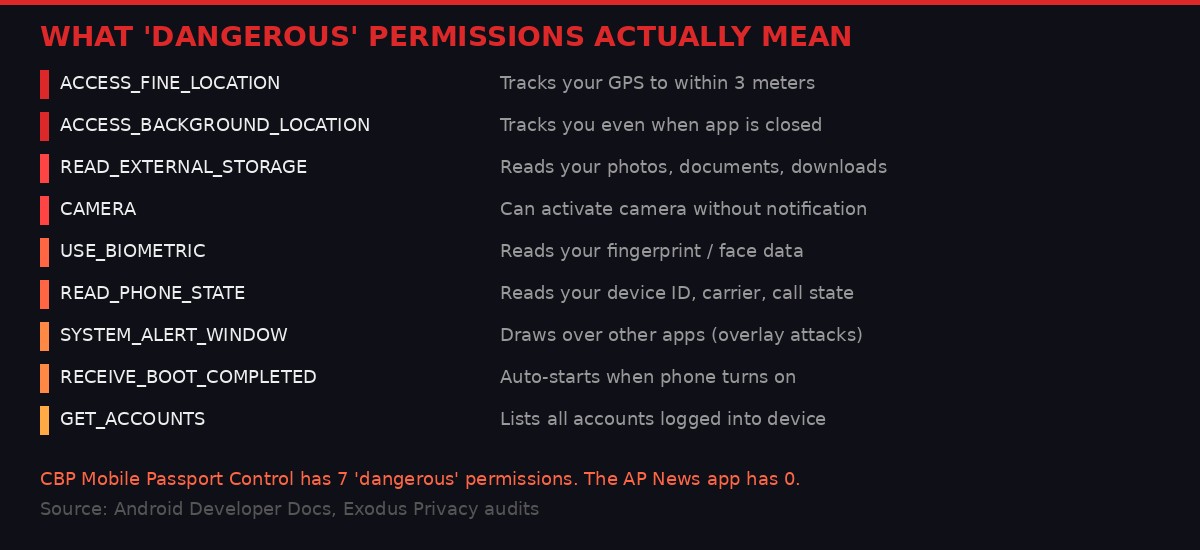
But the app requests: precise GPS location tracking, biometric fingerprint access, external storage modification, the ability to auto-start when your phone boots, permission to draw overlay windows on top of other apps, Wi-Fi connection scanning, and badge notification reading. According to IBTimes reporting, security analysts described these permissions as granting "full control over your device."
Exodus Privacy's audit found three embedded trackers in the APK. One is OneSignal, a push notification and analytics platform that the company itself describes as enabling location tracking via its SDK (opt-in at the OS level, they claim, though the app's permission requests suggest otherwise). The second is a standard analytics library. The third is Huawei Mobile Services Core.
There is no universe in which the inclusion of a Huawei SDK in the official White House app is defensible. The U.S. government placed Huawei Technologies on the Entity List in May 2019, restricting American companies from selling technology to Huawei without a license. The Federal Communications Commission designated Huawei as a national security threat in June 2020. The Secure Equipment Act of 2021 prohibits the FCC from reviewing or issuing new equipment authorizations for Huawei. Multiple intelligence agency directors have publicly testified that Huawei hardware and software could be used as vectors for Chinese espionage.
And then the White House put Huawei's code in its own app. The hypocrisy is not subtle. It is structural.
The app also features a "Text the President" button that auto-fills the message field with "Greatest President Ever!" before collecting your name and phone number. There is no app-specific privacy policy - just a generic whitehouse.gov privacy statement that makes no reference to the app's tracking capabilities, biometric access, or Huawei integration.
Key finding: The White House app (v47.0.1) contains 3 embedded trackers including Huawei Mobile Services Core - the same Chinese company the U.S. government sanctioned as a national security threat. The app requests precise GPS, biometric access, storage modification, and auto-boot permissions to deliver content available via any web browser.
The Full Fedware Lineup: 13 Apps, Zero Accountability
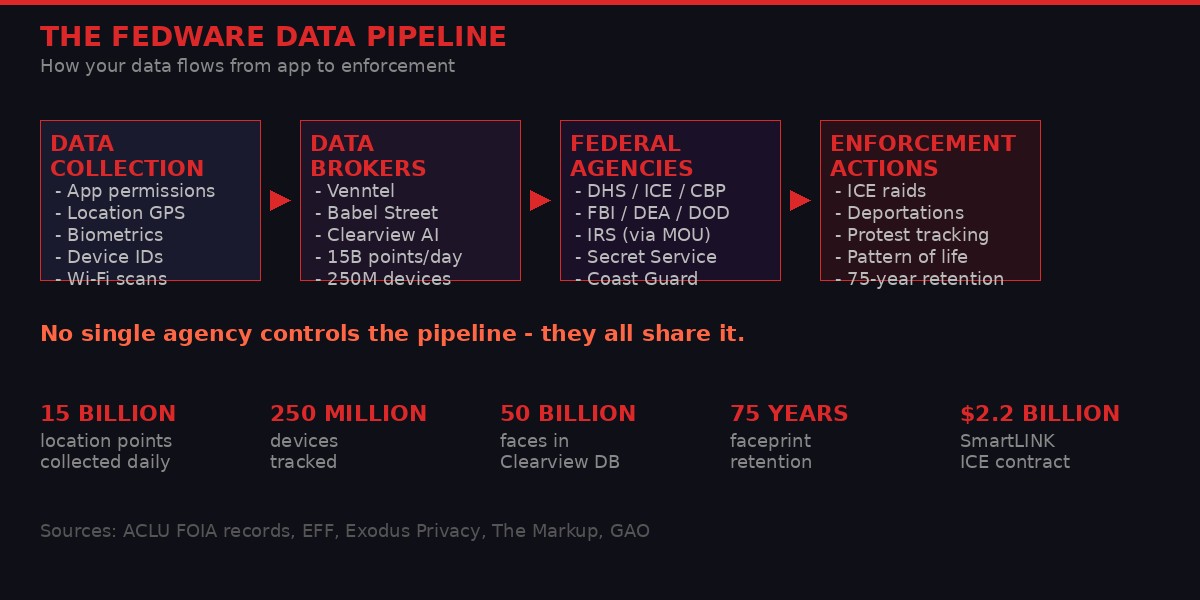
How data flows from federal apps through brokers to enforcement actions. No single agency controls the pipeline - they all share it.
Bent didn't stop at the White House app. Using Exodus Privacy's auditing tools, he systematically analyzed every federal agency app available on Google Play. The results form a pattern that looks less like institutional negligence and more like deliberate infrastructure design.
myFBI Dashboard - 12 permissions, 4 trackers
The FBI's official app requests storage modification, Wi-Fi network scanning, account discovery (meaning it can enumerate every account logged into your device), phone state reading (which exposes your device's unique IMEI identifier), and auto-start at boot. The app contains four trackers, one of which is Google AdMob - a mobile advertising SDK.
Read that again. The Federal Bureau of Investigation's official app ships with ad-serving infrastructure while simultaneously reading your phone identity. The FBI's news app - whose purpose is to publish press releases and wanted posters - contains more embedded trackers than most weather apps. There is no legitimate reason for a law enforcement agency's public communications tool to serve advertisements. The presence of AdMob in an FBI app is either staggering incompetence or a data collection vector disguised as monetization. Neither explanation is comforting.
FEMA - 28 permissions, 1 tracker
The Federal Emergency Management Agency's app requests 28 permissions including both precise and approximate location tracking. Twenty-eight permissions for an application whose primary function is displaying weather alerts and shelter locations. The AP News app delivers equivalent disaster coverage with a fraction of these permissions. Your phone's built-in weather app does it with fewer still.
FEMA's tracker count has actually decreased over time - from 4 in older versions to 1 in the current v3.0.14. This suggests someone at FEMA realized the optics were bad and cleaned up the most visible trackers while leaving the permission architecture intact. The permissions are where the real data extraction happens. Trackers are just the visible tip.
IRS2Go - 10 permissions, 3 trackers
The IRS mobile app contains three trackers and requests 10 permissions. That alone would be unremarkable by Fedware standards. What elevates IRS2Go into a case study is the audit trail - or lack thereof.
According to a Treasury Inspector General for Tax Administration (TIGTA) audit, the IRS released this app to the public before the required Privacy Impact Assessment (PIA) was signed. This violated OMB Circular A-130, the federal government's own policy governing information resources management. The app shares device IDs, app activity data, and crash logs with third parties. TIGTA also found that the IRS never confirmed that filing status and refund amounts were properly masked and encrypted in the app interface. The agency responsible for collecting the most sensitive financial information of every American taxpayer shipped a mobile app without verifying that your tax refund amount wasn't visible to third-party analytics companies.
MyTSA - 9 permissions, 1 tracker
The Transportation Security Administration's app comes in lighter at 9 permissions and 1 tracker, but still requests both precise and approximate location. To TSA's credit, their own Privacy Impact Assessment states the app stores location data locally and claims it never transmits GPS coordinates to TSA servers. This is the only federal app in Bent's audit that has a PIA specifically addressing its mobile tracking capabilities. The bar is in hell, and TSA barely cleared it.
CBP Mobile Passport Control - 14 permissions, 7 classified "dangerous"
This is where Fedware graduates from concerning to alarming. Customs and Border Protection's passport app requests 14 permissions, 7 of which Android classifies as "dangerous": background location tracking (it follows you when the app is closed), camera access, biometric authentication, and full external storage read/write capabilities.
But the permissions are just the front door. The entire CBP app ecosystem - CBP One, CBP Home, Mobile Passport Control - feeds data into a network that retains your faceprints for up to 75 years and shares that biometric data across DHS, ICE, and the FBI. Your face, submitted through a passport app, becomes a permanent entry in a surveillance database that outlives you.
Android classifies certain permissions as "dangerous" because they access sensitive user data. CBP Mobile Passport Control has 7 of them.
(incl. Huawei)
Mobile Fortify: The Face Scanner in Every Agent's Pocket

ICE agents now carry handheld facial recognition in the field - drawing from 50 billion scraped images. Photo: Unsplash
The consumer-facing apps are the soft end of the Fedware ecosystem. Behind them sits a tool built explicitly for enforcement: Mobile Fortify, a facial recognition app that ICE agents carry in the field during street encounters.
Mobile Fortify draws from hundreds of millions of images across DHS, FBI, and State Department databases, according to Biometric Update reporting on internal DHS documents. In September 2025, ICE Homeland Security Investigations signed a $9.2 million contract with Clearview AI, the company that scraped over 50 billion facial images from the public internet without consent. This gave ICE field agents access to what is essentially the world's largest non-consensual facial recognition database.
DHS's own internal documents acknowledge that Mobile Fortify can be used to amass biographical information of "individuals regardless of citizenship or immigration status." CBP confirmed it will "retain all photographs" - including those of U.S. citizens - for 15 years. The Electronic Frontier Foundation found that ICE does not allow people to opt out of being scanned.
"ICE does not allow people to opt-out of being scanned, and ICE agents apparently have the discretion to use a facial recognition match as a definitive determination of a person's immigration status even in the face of contrary evidence. Using face identification as a definitive determination of immigration status is immensely disturbing." - Coalition letter from EFF, EPIC, and Asian Americans Advancing Justice
There is at least one documented case of a U.S.-born citizen being told he could be deported based solely on a biometric match, contradicting his actual citizenship documentation. Mobile Fortify treats a probabilistic algorithm match as more authoritative than government-issued identity documents. This is not a bug in the system. The system was designed to operate this way.
In March 2026, NPR reported on how ICE agents were using Mobile Fortify during confrontational street encounters - scanning faces without consent, without warrants, and without informing the people being scanned that their biometric data was being entered into a permanent federal database. A coalition of organizations including the EFF, the Project on Government Oversight, and EPIC demanded DHS shut down Mobile Fortify, release its privacy analyses, and clarify its facial recognition policies. DHS has not complied with any of these demands.
ICE also concluded it did not need to conduct a new Privacy Impact Assessment for Mobile Fortify - the standard practice required for government technologies that collect people's data. The agency that deploys handheld facial recognition during street encounters decided, on its own, that no privacy review was necessary.
SmartLINK: The $2.2 Billion Ankle Bracelet in Your Pocket

SmartLINK went from 6,000 users in 2019 to over 230,000 by 2022. It collects location, faceprints, voice prints, and pregnancy data. Photo: Unsplash
If Mobile Fortify is the government's surveillance camera, SmartLINK is its ankle bracelet - except it's installed as an app on your personal phone, and its terms of service make it clear that nothing you do on that phone is private anymore.
SmartLINK is ICE's electronic monitoring application, as documented by The Markup. It was built by BI Incorporated, a subsidiary of the GEO Group - a private prison company that profits directly from the volume of people under ICE monitoring. The contract is worth $2.2 billion. The financial incentive structure is transparent: the more people on SmartLINK, the more money GEO Group makes.
The app collects geolocation data, facial images, voice prints, medical information including pregnancy data, and phone numbers of your contacts. ICE's contract gives the agency "unlimited rights to use, dispose of, or disclose" all data collected through SmartLINK. The app's former terms of service explicitly allowed sharing "virtually any information collected through the application, even beyond the scope of the monitoring plan."
Think about what "beyond the scope of the monitoring plan" means. The monitoring plan is ostensibly about ensuring compliance with immigration check-ins. "Beyond the scope" means the data can be used for anything - shared with other agencies, fed into pattern-of-life analysis, sold to contractors, or used in prosecutions that have nothing to do with immigration status.
SmartLINK's user base grew from 6,000 in 2019 to over 230,000 by 2022 - a 38x increase in three years. In 2019, ICE used GPS data harvested from SmartLINK monitors to coordinate one of the largest immigration raids in U.S. history, arresting approximately 700 people across six cities in Mississippi. The people being monitored were, in effect, providing ICE with the precise coordinates needed for their own arrest.
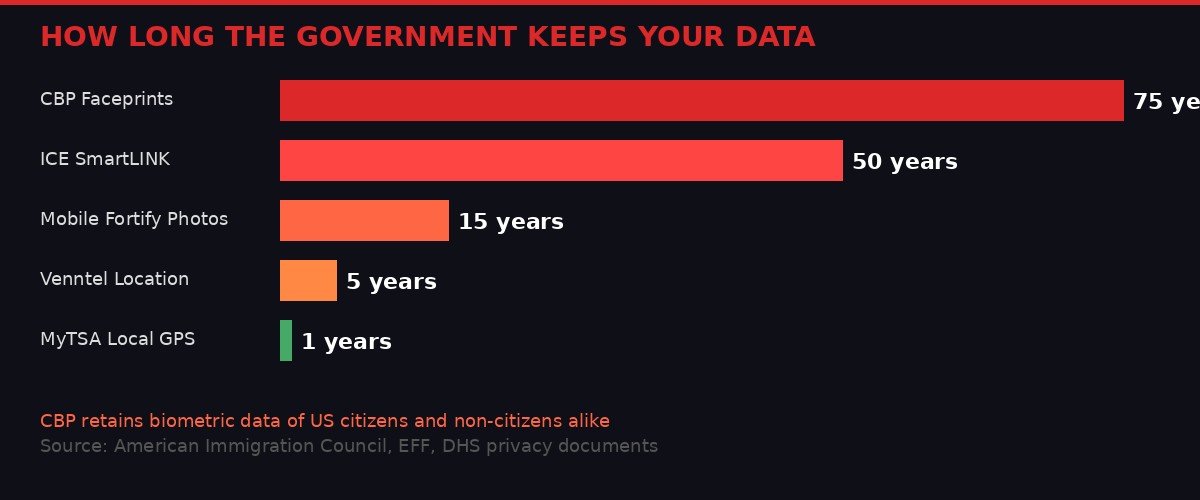
Federal agencies retain biometric and location data for periods ranging from 1 year to 75 years. CBP faceprint retention outlives most humans.
The Data Broker Pipeline: 15 Billion Location Points Per Day

Companies like Venntel collect 15 billion location data points daily from 250 million devices - and sell that data to federal agencies without warrants. Photo: Unsplash
Federal apps are just one intake valve in a much larger data pipeline. Even if you never install a single government app, the federal government is almost certainly buying your location data through commercial brokers.
Companies like Venntel and Babel Street operate as intermediaries between the commercial data economy and federal law enforcement. According to ACLU FOIA records obtained through a lawsuit filed in December 2020, Venntel collects more than 15 billion location data points from over 250 million mobile devices every single day. These data points are extracted through SDKs embedded in over 80,000 commercial apps - weather services, navigation tools, coupon apps, games, and prayer apps.
DHS, FBI, DOD, and the DEA purchase this data without warrants, exploiting a loophole around the Supreme Court's 2018 Carpenter v. United States ruling. In Carpenter, the Court held that the government needs a warrant to access a person's cellphone location history from cellular service providers. The government's workaround was simple: don't get it from the carrier. Buy it from a data broker instead. The constitutional protection applies to the carrier. It doesn't apply to a company that scraped the same data through an SDK buried in a flashlight app.
Venntel's own marketing materials, obtained through the ACLU's FOIA case, describe their product as enabling agencies to "identify devices observed at places of interest," "identify repeat visitors, frequented locations, pinpoint known associates, and discover pattern of life." These are intelligence capabilities being marketed to domestic law enforcement agencies for use against the domestic population.
The Defense Department purchased location data from Muslim prayer apps to monitor religious communities, as documented by the EFF. Police departments used similar commercially purchased data to track racial justice protesters in 2020. The data broker pipeline doesn't distinguish between a suspected terrorist, an undocumented immigrant, and a citizen exercising their First Amendment right to protest. They're all just coordinates on a map.
In scattered internal emails obtained through the FOIA lawsuit, some DHS employees raised concerns. Internal briefing documents acknowledged that "legal, policy, and privacy reviews have not always kept pace with the new and evolving technologies." A senior director of privacy compliance flagged that the DHS Office of Science & Technology appeared to have purchased access to Venntel before a required Privacy Threshold Assessment was approved. All projects involving Venntel data were temporarily halted because of unresolved privacy and legal questions.
Then the projects resumed. The purchases continued. The pipeline kept flowing.
The Carpenter Loophole: In 2018, the Supreme Court ruled the government needs a warrant for cell location data from carriers. The government's response: buy the same data from commercial brokers instead. No warrant needed. 15 billion data points per day, $0 judicial oversight.
The IRS-ICE Pipeline: When Your Tax Return Becomes a Deportation Tool
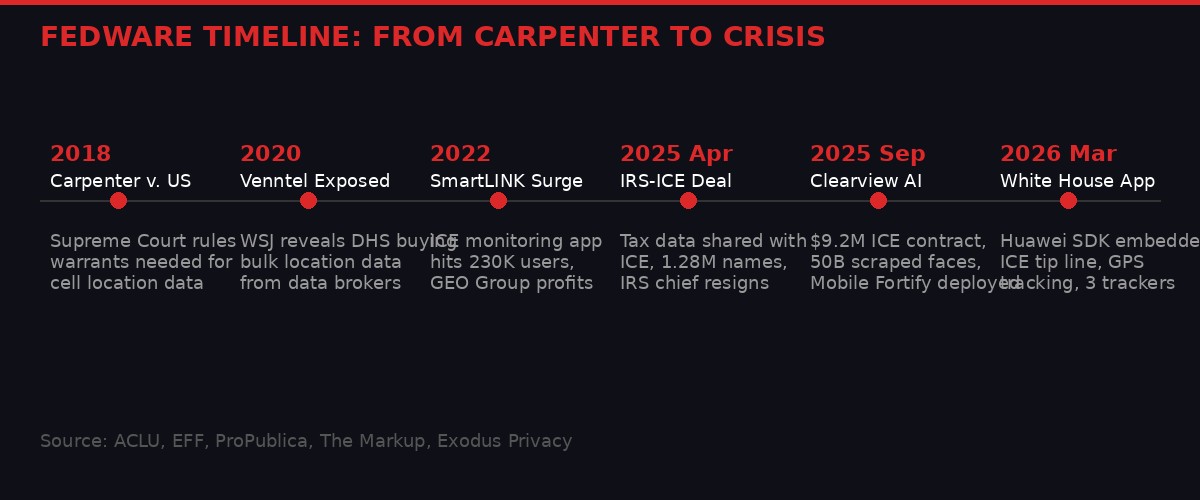
A timeline of federal surveillance expansion: from the Supreme Court's Carpenter ruling in 2018 to the White House app's Huawei trackers in 2026.
In April 2025, the IRS and ICE signed a Memorandum of Understanding that transformed the U.S. tax system into an immigration enforcement tool. Under the agreement, as reported by ProPublica, ICE could receive names, addresses, and tax data for individuals with removal orders. ICE submitted 1.28 million names for data matching.
The IRS then erroneously shared the data of thousands of people who should never have been included - taxpayers who did not have removal orders, whose records were swept up in the bulk data transfer. The acting IRS Commissioner, Melanie Krause, resigned in protest. The agency's chief privacy officer also quit.
This matters because it reveals how Fedware's data pipeline actually operates. The apps collect biometric data, location data, and device identifiers. Commercial brokers provide bulk location intelligence. And now the tax system - the one government database that touches virtually every adult in the United States - becomes another input feed. Each data source is individually justifiable through narrow bureaucratic reasoning. Together, they form a comprehensive surveillance infrastructure that no single law authorized and no single agency controls.
A federal judge blocked further IRS-ICE data sharing in November 2025, ruling it likely violates IRS confidentiality protections under Section 6103 of the Internal Revenue Code. But by the time the injunction was issued, the IRS was already building an automated system to give ICE bulk access to home addresses with minimal human oversight. Court orders are speed bumps. The infrastructure always finds another route.
The pattern is consistent: agency builds capability first, ignores required privacy reviews, gets caught, faces a temporary legal restraint, and then builds a workaround. Mobile Fortify deployed without a Privacy Impact Assessment. IRS2Go launched before its PIA was signed. Venntel purchases continued after internal privacy flags were raised. The legal and regulatory frameworks exist. They are simply not enforced because the agencies enforcing them are the same agencies violating them.
The Oversight Illusion

Nearly 60% of GAO privacy recommendations from 2010-2023 remain unimplemented. Congress has been told twice to pass privacy legislation. It hasn't.
In 2023, the Government Accountability Office reported that nearly 60% of 236 privacy and security recommendations it had issued since 2010 remained unimplemented. Congress was told in 2013 to pass comprehensive internet privacy legislation. It didn't. Congress was told again in 2019. It didn't. It's 2026 now, and there is still no federal privacy law governing how government agencies collect, share, and retain data from mobile applications.
The absence of legislation is not an oversight. It is a choice. The surveillance apparatus serves the people who run it, and the people who run it write the laws. Oversight is theater: the GAO issues a report, Congress holds a hearing, everyone performs concern for the cameras, and then the contracts get renewed and the data keeps flowing.
Consider the structural incentives. The GEO Group profits from SmartLINK's expansion - more monitored individuals means more revenue. Clearview AI's business model depends on law enforcement contracts. Venntel and Babel Street exist solely to sell location intelligence to government buyers. These companies lobby Congress. They attend government technology conferences. They hire former DHS and ICE officials as executives and board members. The revolving door between surveillance contractors and the agencies they serve is not a secret - it's a business model.
Meanwhile, the only independent audit infrastructure for mobile app surveillance - Exodus Privacy - is a French nonprofit running on donations. The primary FOIA litigation forcing disclosure of bulk location data purchases is being conducted by the ACLU with charitable funding. The EFF's campaigns against Mobile Fortify are donor-supported. The people trying to hold the surveillance state accountable are funded by tax-deductible donations. The surveillance state is funded by the federal budget.
This asymmetry is not accidental. It is the system functioning as designed.
The Technical Reality: Why Apps Exist When Websites Would Suffice

Every federal app in this investigation could be replaced by a web page. The app exists because a website can't read your fingerprint. Photo: Unsplash
Every single piece of content delivered by these 13 federal apps could be served through a standard web page. Press releases, weather alerts, tax refund status, TSA wait times, passport information - all of it is available through federal websites that require zero special permissions to access.
The app exists for one reason: a web page cannot read your fingerprint, track your GPS in the background, inventory the other accounts on your device, or auto-start when your phone boots up. A web page cannot enumerate your Wi-Fi connections, access your camera without an explicit prompt, or draw overlay windows on top of your banking app. The app format is the surveillance vector. The content is the bait.
This is a design pattern that the commercial surveillance industry perfected over the past decade, and the government has adopted wholesale. Facebook, Google, and Amazon demonstrated that wrapping information in a native app creates data extraction opportunities that browser-based delivery cannot match. The federal government watched, learned, and deployed the same architecture - with the added advantage that government apps can claim "national security" as justification for permission requests that would trigger antitrust investigations if a tech company made them.
The Android permission model - for all its flaws - at least requires apps to declare their permission requests. This is how Exodus Privacy can audit them. But declaration is not justification. The White House app declares that it needs precise GPS location. It does not explain why an app delivering press releases needs to know your physical coordinates to within three meters. The FBI app declares that it needs to read your phone state. It does not explain why a news feed about wanted persons requires access to your device's unique hardware identifier.
Apple's iOS enforces stricter permission controls and app review processes, but the fundamental problem is architectural: native apps are surveillance-superior to web pages, and the government has chosen the surveillance-superior delivery mechanism for content that doesn't require it. The decision to build an app instead of using a website is itself the tell.
What This Means and What Comes Next

The Fedware pipeline connects app permissions, data brokers, facial recognition, tax records, and monitoring apps into a unified surveillance infrastructure. Photo: Unsplash
Fedware is not a conspiracy theory. It's a documentation exercise. Every fact in this article is sourced from Exodus Privacy audits, ACLU FOIA records, EFF investigations, GAO reports, TIGTA audits, ProPublica reporting, The Markup's analysis, and the federal government's own published privacy impact assessments (or conspicuous lack thereof). The data is public. The pattern is clear. The infrastructure is real.
The government publishes content available through standard web protocols, wraps it in applications demanding access to biometrics, location, storage, and device identity, embeds advertising and tracking SDKs from companies including one it sanctioned as a national security threat, and feeds all of this into a pipeline that connects to bulk location data purchases, facial recognition databases containing 50 billion scraped images, tax records, and electronic monitoring systems operated by private prison companies under billion-dollar contracts.
The legal frameworks that should prevent this - the Fourth Amendment, the Carpenter precedent, OMB Circular A-130, Section 6103 of the IRC - are either being circumvented through commercial data brokers, ignored through failure to complete required privacy assessments, or blocked by court orders that the government treats as temporary inconveniences while building automated workarounds.
What comes next is predictable because it has already started. The Android Developer Verification program Google announced on March 30, 2026, will add identity requirements for developers publishing apps on the Play Store. This will make it harder for independent security researchers to publish anonymously - the same researchers who discovered the Fedware ecosystem. The government's response to being caught is never to stop surveilling. It's to make catching harder.
The practical advice is simple: don't install federal government apps. Use their websites. Use RSS feeds. Use a browser. Every piece of information these apps deliver is available without granting a single additional permission to your device. The app adds nothing except data extraction. If you've already installed one, check its permissions in your phone settings and revoke everything non-essential. Better yet, uninstall it entirely.
The version number of the White House app is 47.0.1. The irony isn't in the number. It's in the decimal point - the .0.1 that marks this as a first release, a foundation, a beginning. What comes in version 47.1.0, or 47.2.0, or whatever version ships after the next election cycle, will be built on the permission architecture established right now. Fedware is not a finished product. It's a platform - and it just launched.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram