Cryptopocalypse 2029: Google Just Moved Up the Day the Internet Breaks
Google announced Wednesday that Q Day - the moment a quantum computer becomes powerful enough to crack the encryption protecting virtually everything online - could arrive as early as 2029. That's not a research estimate. It's an operational deadline, and it means the entire internet has roughly three years to rewrite its security stack from the ground up.

For thirty years, the cryptography community ran a dark joke: Q Day was always "ten to twenty years away." It was the nuclear option nobody wanted to think about too hard. RSA encryption - the foundation of HTTPS, banking, email, government communications, and national security infrastructure - has a known Achilles heel. Mathematician Peter Shor proved in 1994 that a quantum computer of sufficient power could factor large integers exponentially faster than any classical machine, making RSA solvable in hours instead of millennia.
The catch was that "sufficient power" kept retreating like a mirage. A 2012 estimate said you'd need a billion physical qubits. A 2019 paper from Google's own Craig Gidney revised that down to 20 million. Last June, Gidney published again - and the number dropped below one million. Now Google is saying 2029. No joke.
The announcement on Wednesday came via a Google blog post authored by Heather Adkins, Google's VP of security engineering, and Sophie Schmieg, a senior cryptography engineer. Simultaneously, Google published a separate technical post detailing how Android 17 - currently in beta - will be the first major mobile operating system to begin hardening itself against quantum attack. The two posts together constitute something the security world had been waiting for: a corporate giant treating Q Day not as a thought experiment but as a hard calendar date.
Why 2029 Is a Shock - And Why It Probably Isn't Wrong

To understand why Google's 2029 deadline rattled even hardened cryptography researchers, you need to understand how rapidly the qubit threshold has collapsed.
Every estimate for Q Day hinges on one key number: how many physical qubits does it take to run Shor's algorithm against a 2048-bit RSA key? The answer has been revised downward with brutal regularity, each revision driven by improvements in error correction, qubit architecture, and algorithmic efficiency.
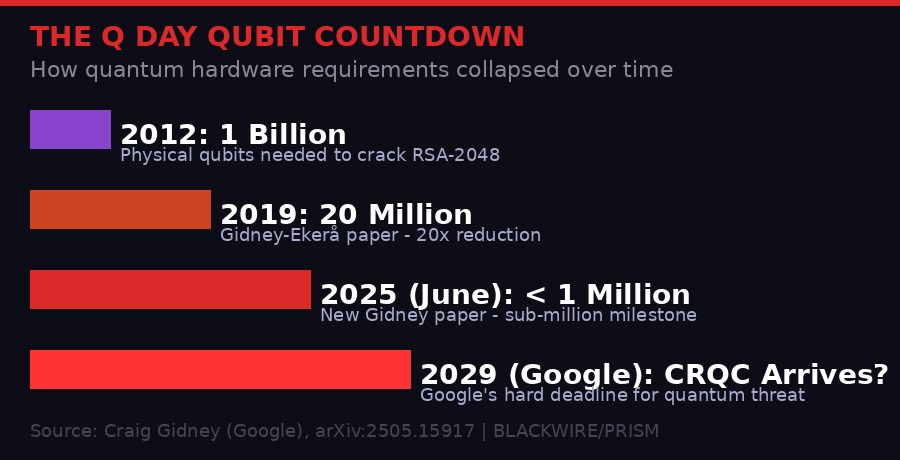
In 2025, Gidney published "How to factor 2048-bit RSA integers with less than a million noisy qubits" - a paper that reduced the required qubit count by another 20x versus his own 2019 estimate. The approach combined three separate algorithmic improvements: approximate residue arithmetic from a 2024 French research team, a technique called "yoked surface codes" for storing idle qubits more efficiently, and "magic state cultivation" for reducing costly Toffoli gate operations.
The result: a 2048-bit RSA key could theoretically be cracked in under a week on a quantum computer with fewer than one million noisy qubits - meaning qubits that make errors, not the hypothetical perfect qubits of textbook quantum computing.
Current quantum computers don't have one million qubits yet. But Google's Willow chip, announced in late 2024, demonstrated exponentially improving error correction as qubits scaled up - the first time a quantum system showed that fundamental characteristic. IBM's roadmap pushes past 100,000 qubits by 2033. Startups like PsiQuantum and IonQ are pursuing different hardware architectures. The race to the million-qubit threshold is no longer theoretical.
"That is certainly a significant acceleration and tightening of the public transition timelines we've seen to date, and is accelerated over even what we've seen the US government ask for. The 2029 timeline is an aggressive speedup but raises the question of what's motivating them."
- Brian LaMacchia, cryptography engineer, formerly oversaw Microsoft's post-quantum transition 2015-2022
LaMacchia's question - what's motivating Google - is the interesting one. Google didn't disclose the internal reasoning in either post. A company spokeswoman declined to answer questions. What's clear is that internal threat modeling at one of the world's most sophisticated security organizations has been updated, and the result was urgent enough to announce publicly and bluntly.
The "Store Now, Decrypt Later" Attack Already Happening Today

The 2029 deadline matters for future threats. But there's a threat happening right now that doesn't require waiting for quantum hardware: store now, decrypt later.
The premise is straightforward. Encrypted data intercepted today is unreadable today. But if a nation-state actor captures and stores that encrypted traffic - classified government communications, diplomatic cables, financial transactions, personal medical records, source code - they can hold it indefinitely. When Q Day arrives, they run Shor's algorithm against the stored RSA keys and decrypt years of accumulated secrets retroactively.
This attack has been a known theoretical risk for over a decade. The intelligence community's working assumption is that sophisticated adversaries have been running harvest-and-store operations for years. The NSA has publicly acknowledged the threat. The question isn't whether stored data is being collected - it's whether the encryption protecting that data will remain safe long enough to matter.
For short-lived secrets - today's stock trades, tonight's restaurant order - Q Day arriving in five years is irrelevant. For long-lived secrets - nuclear submarine communications, intelligence source identities, proprietary pharmaceutical research, 30-year government contracts - data being encrypted today could be decrypted by an adversary in 2029 or 2030. The window is shorter than anyone comfortable thought a year ago.
"The threat to encryption is relevant today with store-now-decrypt-later attacks, while digital signatures are a future threat that require the transition to PQC prior to a Cryptographically Relevant Quantum Computer (CRQC). That's why we've adjusted our threat model to prioritize PQC migration for authentication services."
- Google Security Blog, March 25, 2026
Google's statement distinguishes between two categories of quantum threat. Encryption - scrambling data so only the holder of the private key can read it - faces the store-now-decrypt-later risk today. Digital signatures - the mechanism that proves software came from its legitimate publisher, that a website certificate is authentic, that an Android app wasn't tampered with - face a different risk profile. Signatures only need to be verified at the moment of use. But if a quantum computer can forge signatures, the entire software supply chain collapses. Every signed binary, every TLS certificate, every code commit becomes potentially untrustworthy.
Android 17 and the First Wave of Quantum Hardening
Google's parallel announcement covers the technical details of Android 17's post-quantum hardening. For the first time, the company publicly laid out its PQC roadmap for the most widely deployed operating system on earth - a platform running on roughly 3.6 billion active devices.
The centerpiece is ML-DSA (formally NIST FIPS 204), an implementation of the CRYSTALS-Dilithium lattice-based digital signature algorithm. Lattice-based cryptography relies on the mathematical hardness of certain problems involving high-dimensional lattice structures - problems that quantum computers gain no significant advantage solving over classical machines, as far as current research shows.
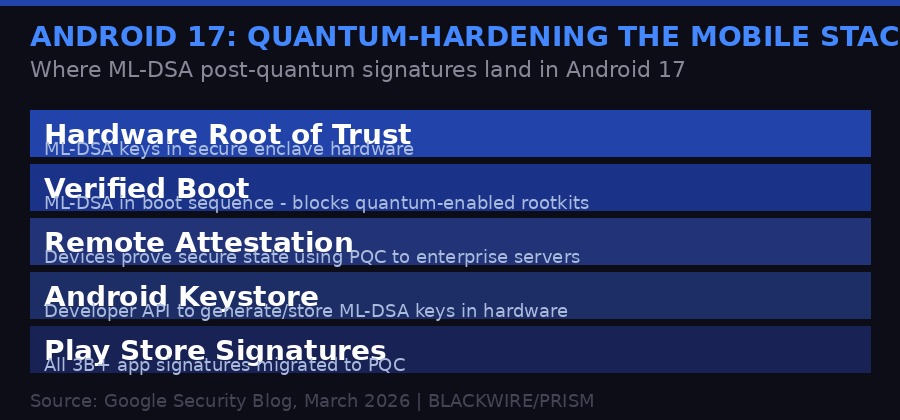
Android 17 integrates ML-DSA in five distinct layers of the security stack:
Hardware Root of Trust: ML-DSA keys are being embedded into Android's hardware security module - the secure enclave that stores cryptographic material in tamper-resistant hardware. This is the deepest level of the Android security stack. Keys stored here cannot be extracted even by a compromised operating system.
Verified Boot: Every Android device checks during startup that the OS hasn't been tampered with by verifying cryptographic signatures on each boot stage. Android 17 adds ML-DSA to this verification chain. A quantum-capable attacker who could forge RSA signatures could potentially deploy undetectable rootkits at boot time; ML-DSA closes that avenue.
Remote Attestation: Enterprise environments use remote attestation to verify that employee devices are running authorized, secure software before granting network access. These attestations rely on digital signatures - signatures that are now being migrated to PQC.
Android Keystore: The developer-facing API for generating and storing cryptographic keys. From Android 17, developers can generate ML-DSA key pairs that live in hardware. This is significant: it means app developers can begin signing application data, authenticating users, and verifying communications using quantum-resistant keys today, building against the 2029 horizon.
Play Store and App Signatures: Google is migrating the signatures on every app in the Play Store - currently numbering in the millions, installed on billions of devices - to PQC. This is a massive engineering undertaking. Developer signing workflows will need to be updated. Build pipelines will need to generate ML-DSA signatures alongside or instead of existing RSA/EC ones. The migration will put significant workload on the Android developer ecosystem.
The announcement is the first time Google has publicly committed Android to a PQC timeline, and it suggests internal discussions about 2029 have been going on for some time before the public disclosure.
What Needs to Change - And How Much Work That Actually Is

To appreciate the scale of what Google's 2029 deadline demands, consider what actually runs on RSA and elliptic curve cryptography today.
TLS - the protocol securing every HTTPS connection - uses RSA or elliptic curve keys for its initial handshake. Every time a browser connects to a bank, an email provider, a government portal, or a shopping site, those first few milliseconds involve RSA or EC operations. The TLS standard supports newer PQC algorithms, but adoption has been piecemeal. Google Chrome, Apple's WebKit, and Mozilla Firefox have begun adding support. Cloudflare announced PQC-hybrid TLS in 2023. But the long tail of web servers, load balancers, VPNs, and embedded systems running old TLS implementations is enormous.
SSH - the protocol sysadmins use to access servers remotely - is RSA-dependent in most deployments. OpenSSH added experimental PQC support in 2023. But the installed base of servers, network devices, and embedded systems running older SSH versions stretches across millions of machines, many of which receive infrequent updates.
PKI - the public key infrastructure issuing TLS certificates that make the web's identity system function - is entirely RSA and EC-based. Certificate authorities must begin issuing PQC or hybrid PQC certificates. Web browsers must validate them. The CA/Browser Forum, which governs certificate policies, has been working on this transition but has not set binding deadlines.
Code signing pipelines - the processes that sign operating system updates, application installers, firmware updates, and driver packages - need to be migrated. A quantum computer that can forge code signing keys could theoretically distribute malware disguised as legitimate software updates, signed with valid-looking quantum-forged keys.
Hardware security modules - the specialized chips inside servers, payment terminals, HSMs, and smart cards that store private keys - often have firmware that is difficult or impossible to update in the field. Many HSM manufacturers are releasing new hardware supporting PQC, but the installed base in financial services, healthcare, and government infrastructure runs for years or decades.
The Long Tail Problem
The crypto libraries that almost every developer depends on - OpenSSL, BoringSSL, LibreSSL, NSS - have begun adding PQC support, but software inheriting these libraries needs to be compiled against new versions and redeployed. Industrial control systems, medical devices, and infrastructure equipment running embedded software may have no clear upgrade path. The 2029 deadline applies to every device running RSA, not just the ones with active engineering teams.
The second-order problem is hybrid implementations. The transition period - roughly now through 2029+ - means systems need to support both classical and post-quantum algorithms simultaneously. A TLS connection between a PQC-capable browser and a non-PQC server must still work using classical crypto. A signed Android app must still be verifiable on old Android versions running RSA-based verification. This hybrid complexity multiplies the surface area of potential implementation bugs.
The NIST Standards Race and Who Else Is Preparing
Google's 2029 deadline doesn't exist in a vacuum. The broader PQC migration has been building momentum for years, driven by a parallel effort at NIST - the US National Institute of Standards and Technology - to standardize post-quantum algorithms that the world can actually trust and implement.
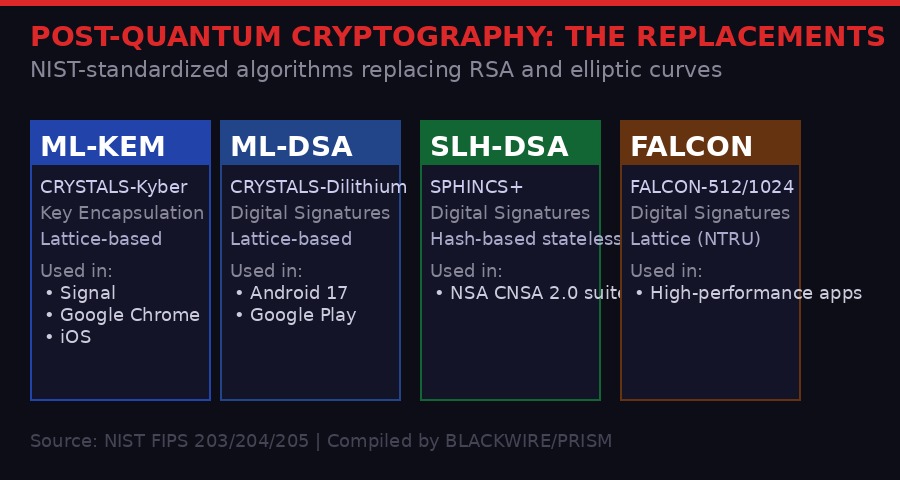
After a seven-year evaluation process that began in 2017, NIST finalized its first four PQC standards in August 2024. The standards cover two fundamental cryptographic operations:
Key encapsulation (replacing RSA key exchange): ML-KEM (FIPS 203), based on the CRYSTALS-Kyber algorithm. Already deployed in Google Chrome, Apple's iMessage, Cloudflare's network, and Signal messenger. The Signal app added ML-KEM-768 in 2024 in a hybrid scheme that runs alongside the existing X3DH protocol, meaning both a classical and a quantum-resistant algorithm must be broken to compromise a conversation.
Digital signatures (replacing RSA and ECDSA signing): Three standards address this. ML-DSA (FIPS 204, based on CRYSTALS-Dilithium) is the primary choice for most applications, offering a good balance of security, key size, and signature size. SLH-DSA (FIPS 205, based on SPHINCS+) is a stateless hash-based scheme that doesn't rely on lattice mathematics at all - useful for applications where the lattice assumptions are not yet considered proven. FALCON (FIPS 206) uses a different lattice structure (NTRU lattices) and produces smaller signatures than ML-DSA, making it attractive for performance-constrained environments.
On the government side, the NSA published its CNSA 2.0 (Commercial National Security Algorithm Suite 2.0) requirements in 2022. The suite mandates PQC algorithms for all national security systems and sets two deadline categories:
- Priority applications (software signing, web browsers, cloud services) must transition by 2030
- All national security systems (NSS) must transition by 2031
- Some specialized hardware like network equipment has a 2033 deadline
The Biden administration issued a National Security Memorandum in 2022 directing federal agencies to begin PQC inventorying. The Trump administration has maintained continuity on this directive - quantum cryptography has unusually strong bipartisan support because it's framed as national security infrastructure rather than tech policy.
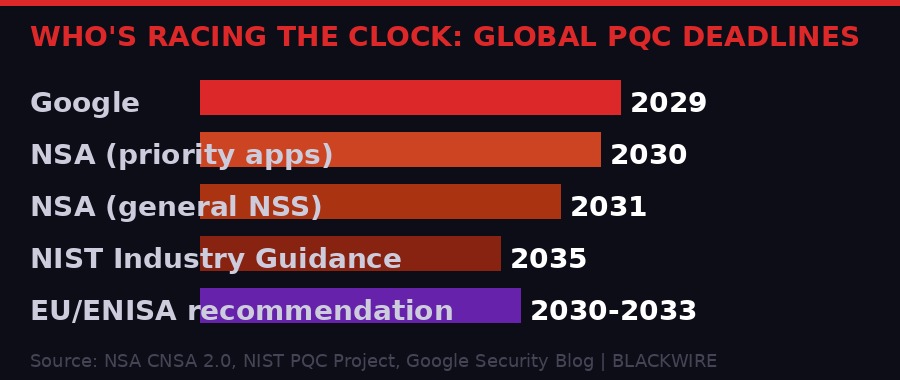
Beyond the US, the EU's ENISA (European Union Agency for Cybersecurity) has been pushing member states toward PQC adoption since 2022. Germany's BSI published PQC migration guidance in 2023. The UK's NCSC released similar guidance. China's cryptography regulator has developed its own parallel post-quantum standards, raising the prospect of algorithm fragmentation along geopolitical lines - where quantum-safe communications might not be interoperable between Western and Chinese systems.
The Second-Order Threat: When Nation-States Get There First

The geopolitical dimension of Q Day is where the threat model gets genuinely alarming.
A cryptographically relevant quantum computer - CRQC in the jargon - is not a device that will be publicly announced when it arrives. The first organization to achieve one faces an overwhelming strategic incentive to keep it secret. Every day of secrecy translates to continued ability to decrypt intercepted adversary communications, forge authentication tokens, compromise infrastructure, and access systems that believe their encryption is intact.
This creates an asymmetric intelligence windfall unlike anything in the history of espionage. Historical codebreaking - Bletchley Park, Venona, the NSA's Cold War capabilities - required years of analytical work against specific targets. A CRQC, once operational, could retroactively decrypt years of stored traffic near-automatically. The KGB's successor services, China's MSS, Iran's MOIS - all have been running bulk interception operations for years. Any organization that has been storing encrypted traffic against a future quantum capability could suddenly read it all.
The store-now-decrypt-later attack means the intelligence value of a CRQC isn't just about what can be decrypted going forward. It's about the accumulated archives. Consider: diplomatic cables from the 2016 election cycle, encrypted proprietary research from pharmaceutical companies developing vaccines, classified military procurement communications, banking transaction details from major institutions. All of it potentially sitting in foreign intelligence archives, waiting.
Even without a CRQC, the 2029 deadline introduces a new form of strategic calculation. Nations with advanced quantum programs - the US, China, Russia, Israel, the EU bloc collectively - are racing to achieve Q Day first and simultaneously racing to transition their own systems off RSA before an adversary achieves it. The asymmetry between these two objectives is uncomfortable: migrating to PQC is slow and expensive, while achieving a CRQC is fast and secrets-rich.
Google's decision to announce a 2029 deadline publicly can be read as a responsible disclosure of sorts - warning the industry that the window is closing, while also subtly signaling that Google's own systems will be hardened and thus less useful as targets. The announcement is both practical engineering guidance and competitive positioning.
The TeamPCP Wildcard: Quantum Meets Supply Chain

The quantum cryptography story landed on the same week as an unrelated but thematically resonant cybersecurity event: the TeamPCP hacking group's ongoing supply-chain rampage through the open-source security ecosystem.
TeamPCP - a financially motivated hacking collective first identified in December 2025 - spent this past week compromising virtually all versions of the Trivy container vulnerability scanner after gaining access to the GitHub account of Aqua Security, Trivy's creator. From there, the group published malicious Trivy updates to Docker Hub, compromised a second Aqua Security GitHub account, and defaced and published 44 internal repositories including source code for Tracee, internal Trivy forks, CI/CD pipelines, and team knowledge bases.
Over the weekend, researchers from security firm Aikido observed TeamPCP deploying a new worm - dubbed CanisterWorm - that spread through npm packages. A developer with a compromised npm token who installed an infected package would have their own publishable packages laced with malware and re-released within 60 seconds. Aikido observed the worm targeting 28 packages in under a minute.
The novel wrinkle: CanisterWorm used a command-and-control mechanism built on Internet Computer Protocol smart contracts - blockchain-based canisters that the attackers believed would be impossible to take down. Infected machines checked in with the canister every 50 minutes for updated server URLs. (The canister was ultimately taken down Sunday night, though researchers noted it "wasn't as reliable as they expected.")
A later version of CanisterWorm added a data wiper targeting machines in Iran - checking for Iranian timezone settings or locale configuration, then deploying a component the attackers named Kamikaze. The logic was blunt: Kubernetes clusters in Iran got a DaemonSet that wiped every node. Non-Kubernetes machines in Iran got rm -rf / --no-preserve-root. Machines outside Iran got the backdoor installed instead.
The connection to the quantum cryptography story is structural. TeamPCP is attacking the exact infrastructure that code signing and software supply chain security depends on: npm repositories, Docker Hub images, GitHub accounts, CI/CD pipelines. These are precisely the systems that need to migrate to PQC signing first - because a compromised software distribution channel is a vector for delivering malware disguised as legitimate, signed software. If signing keys can eventually be forged by quantum computers, the supply chain attacks of today become trivially scalable.
The TeamPCP campaign serves as a preview of a post-Q-Day world where attackers don't need to compromise a CI/CD pipeline or steal a signing key - they can generate convincing signatures mathematically. The defense against that future requires the PQC migration Google is now demanding happens by 2029.
Timeline: The Road to Q Day
Q Day: The Abbreviated History
What Organizations Must Do Before the Clock Runs Out

If 2029 is real, the practical question is: what do organizations need to do, and how much time do they actually have?
The first step, and the one most organizations haven't started, is cryptographic inventory. Before you can migrate away from vulnerable algorithms, you need to know where they are. RSA and EC keys are embedded in certificates, hardware security modules, VPN configurations, code signing pipelines, SSH server configurations, internal APIs, mobile app builds, IoT firmware, payment terminals, and legacy enterprise software. Most large organizations have no complete accounting of their cryptographic posture.
Google's announcement will accelerate demand for cryptographic discovery tools - software that scans networks and codebases to identify RSA and EC usage. Several vendors, including Crypto Quantique, PQShield, and SandboxAQ (a Google spinout), have been building commercial products in this space. The 2029 deadline announcement is likely to substantially accelerate enterprise procurement conversations.
Once inventoried, the migration itself proceeds in priority order. Long-lived secrets - data encrypted today that will still be sensitive in 2030 - are the highest priority because of the store-now-decrypt-later risk. This means government communications, financial records, intellectual property, and personal health data should be encrypted with PQC or hybrid PQC schemes first.
Software signing and authentication infrastructure comes next, because these systems need to be hardened before Q Day arrives, not after. A quantum computer that can forge code signatures represents an immediate capability for deploying undetectable malware at scale the moment the threshold is crossed.
For developers specifically, the Android 17 announcement carries a concrete call to action. Applications generating and storing cryptographic keys should begin testing ML-DSA integration. Developers building authentication systems should evaluate ML-KEM for key exchange. The PQC APIs in Android 17's Keystore will give developers the tools; using them is a choice each development team will need to make before the deadline.
The financial services sector faces particular urgency. Payment card infrastructure, interbank settlement systems, and regulated financial communications run on long-lived certificates and HSMs with multi-year refresh cycles. The PCI Security Standards Council has been engaged with PQC but has not yet updated the PCI DSS standard to require it. That update, when it comes, will create compliance deadlines that may actually be tighter than Google's 2029 technical threshold.
For most organizations, the honest reality is that 2029 is uncomfortably close. Enterprise software deployments take years. Hardware refresh cycles run 5-7 years in critical infrastructure. Regulatory approval timelines for financial and medical device software run 18 months to several years. The organizations that needed to begin planning yesterday are the ones that haven't started yet.
Google's announcement does one thing above all else: it removes the excuse of uncertainty. The joke about Q Day always being ten to twenty years away is no longer available. One of the most technically sophisticated security organizations in the world has looked at the current state of quantum hardware, applied its threat modeling, and set a date. Whether 2029 is precisely correct is less important than what it signals: the window is real, it is closing, and the migration is mandatory.
The Cryptopocalypse has a calendar entry now. The question is whether the internet's security infrastructure can be rebuilt before that appointment arrives.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram