Cryptopocalypse by 2029: Google's Q-Day Warning and the Race to Save the Internet
Google just moved its internal deadline for quantum-safe cryptography to 2029 - three years away. RSA is dying. Elliptic-curve encryption is dying. The migration window is closing, and most of the world has barely started.
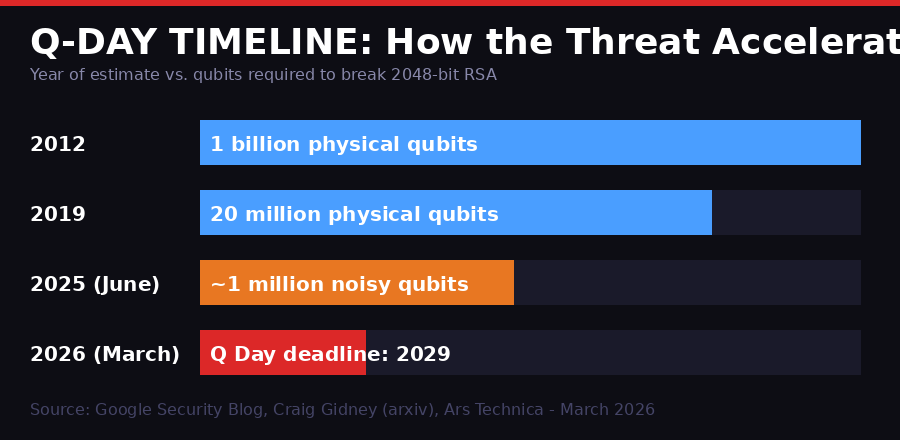
The acceleration of Q-Day estimates from 2012 to 2026. What once seemed a century away is now a 2029 problem. (BLACKWIRE/PRISM infographic)
On Wednesday, Google published something the cryptography world had been dreading - a firm deadline. The company said it was giving itself until 2029 to complete its internal migration to post-quantum cryptography. It also told the rest of the world it should do the same thing.
That date is not a horizon. It is an alarm clock. Three years is barely enough time for a large organization to catalog what it uses, let alone replace it. Banks, governments, hospitals, militaries, and telecom providers have been warned for years. Most of them are nowhere near ready.
Q Day - the point at which a cryptographically relevant quantum computer (CRQC) can break the encryption protecting essentially all of modern digital infrastructure - has been a running joke in security circles for three decades. It was always 10 to 20 years away. Google just stopped laughing.
What Google Actually Said

The quantum threat to public-key cryptography has accelerated faster than most industry forecasts predicted. (JuSun/Getty Images via Ars Technica)
The announcement came in two parts. First, a post on the Google blog signed by Heather Adkins, the company's VP of security engineering, and Sophie Schmieg, a senior cryptography engineer. Second, a detailed technical writeup on what Google is doing to Android specifically.
"As a pioneer in both quantum and PQC, it's our responsibility to lead by example and share an ambitious timeline. By doing this, we hope to provide the clarity and urgency needed to accelerate digital transitions not only for Google, but also across the industry." - Heather Adkins and Sophie Schmieg, Google Security Blog, March 2026
The announcement focused on two distinct threat categories that Google says require different urgency levels.
The first is encryption. Quantum computers can break the key exchange protocols that protect data in transit - TLS, for instance. The threat here is already active, in a form known as "store now, decrypt later." Adversaries - primarily nation-states - are believed to be intercepting and archiving encrypted communications today, with the intention of decrypting them once a CRQC exists. Every secure communication from today is potentially compromised retroactively when Q Day arrives.
The second is digital signatures - the mechanism that verifies software authenticity, device identity, and authentication credentials. This is the "future threat" Google prioritized in its updated threat model. When a quantum computer can forge signatures, the entire chain of trust that holds together software updates, app stores, banking systems, and identity verification collapses. Google said it has specifically adjusted its threat model to prioritize signature migration first, because the impact of signature failure is more immediate and harder to recover from.
Why 2029 - And What Changed

Google's Willow processor demonstrated below-threshold quantum error correction for the first time in December 2024 - a milestone that changed the calculus on how quickly a CRQC might arrive. (BLACKWIRE/PRISM infographic)
The 2029 date surprised even people who work in post-quantum cryptography full-time. Brian LaMacchia, who oversaw Microsoft's PQC transition from 2015 to 2022, called it "a significant acceleration" when Ars Technica reached him for comment.
"That is certainly a significant acceleration/tightening of the public transition timelines we've seen to date, and is accelerated over even what we've seen the US government ask for. The 2029 timeline is an aggressive speedup but raises the question of what's motivating them." - Brian LaMacchia, Farcaster Consulting Group
Google didn't explain its reasoning publicly. Its spokeswoman didn't respond to questions from Ars Technica. But reading between the lines of its own research publications gives a clear picture of why the internal clock moved up so sharply.
In June 2025, Google's Craig Gidney - the same researcher behind the 2019 estimate - published a paper on arXiv titled "How to factor 2048-bit RSA integers with less than a million noisy qubits." That paper showed that a quantum computer with approximately one million physical qubits - qubits prone to errors from environmental noise - could crack 2048-bit RSA in under a week. This was a dramatic reduction from the 20 million qubits Gidney himself had estimated in 2019.
Before that, in December 2024, Google's Willow quantum processor - a 105-qubit chip - demonstrated something the field had been working toward for decades: quantum error correction operating below the surface code threshold. Published in Nature, the result showed that Willow could suppress logical error rates exponentially as qubit count increased, with a distance-7 surface code preserving quantum information for more than twice as long as its best individual physical qubit.
That combination - a sharp reduction in the qubit count needed to break RSA, plus a chip that actually demonstrated the error correction properties required to build a CRQC - appears to be what forced Google's hand. The math closed the gap faster than anyone's public models had projected.
The Encryption That Will Break
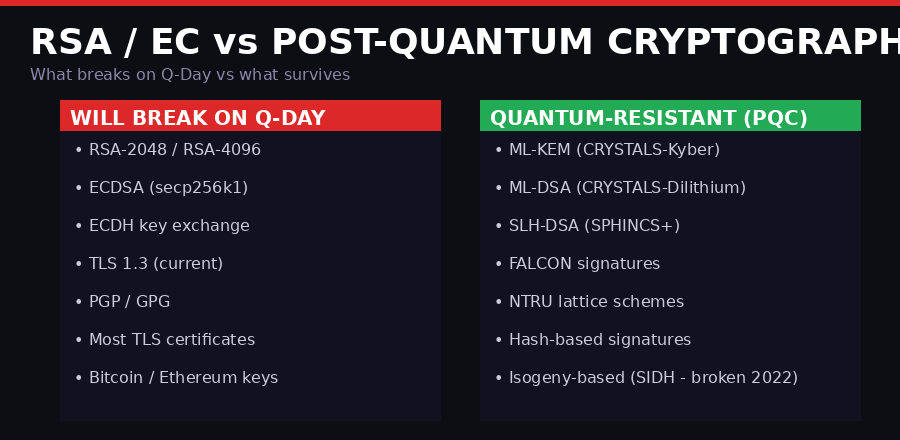
What breaks on Q-Day versus what survives. Almost everything currently used on the internet falls in the left column. (BLACKWIRE/PRISM infographic)
The scope of what breaks on Q-Day is difficult to overstate. Public-key cryptography is not one system - it is the foundational layer underneath virtually every system that moves sensitive data anywhere.
RSA (Rivest-Shamir-Adleman) is used for key exchange and signatures in TLS, PGP, SSH, certificate authorities, and dozens of protocols that hold the web together. RSA-2048, considered strong by current standards, will be broken. RSA-4096 buys time - maybe a day or two more for a well-resourced quantum attacker. It is not a solution.
Elliptic-curve cryptography (ECC) is what replaced RSA as the preferred public-key system for performance reasons. ECDSA is used to sign Bitcoin transactions. ECDH is used for key agreement in Signal, WhatsApp, iMessage, and TLS 1.3. The secp256k1 curve used by Bitcoin and Ethereum has no quantum resistance whatsoever. When a CRQC arrives, every wallet with a visible public key - meaning any address that has ever sent a transaction - can have its private key derived. Estimates suggest roughly four million Bitcoin addresses are potentially vulnerable.
TLS 1.3, which protects the overwhelming majority of HTTPS traffic, relies on elliptic-curve Diffie-Hellman key exchange. It will break. The TLS handshake that protects your bank login, your healthcare records, your corporate VPN - all of it assumes the discrete logarithm problem is hard. Quantum computers dissolve that assumption.
The threat to digital signatures is arguably more dangerous in the near term. When a CRQC can forge signatures, a malicious actor could sign malicious software with a trusted certificate, compromise app store verification, impersonate government servers, or break the certificate authority system entirely. The "identity layer" of the internet - the infrastructure that lets your browser know it is actually talking to your bank and not a fake - fails at the signature level.
Store Now, Decrypt Later - The War Already Underway
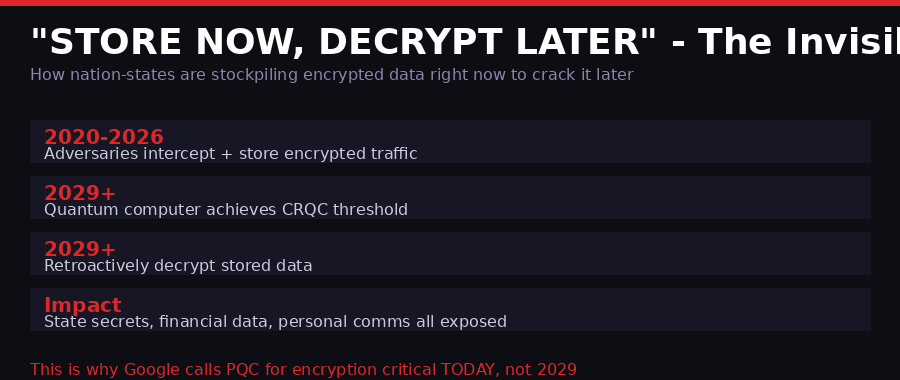
Nation-states are believed to be actively harvesting encrypted communications today for retroactive decryption once quantum computers reach CRQC capability. (BLACKWIRE/PRISM infographic)
The most underreported aspect of this threat is that it is not a future problem. It is a current problem with a delayed payload.
The "store now, decrypt later" (SNDL) strategy is exactly what it sounds like. Intelligence agencies, and likely some criminal organizations with state-level resources, are intercepting and archiving encrypted internet traffic right now. The data is useless to them today. When a CRQC comes online, they decrypt the archive. Every secret ever transmitted over RSA or elliptic-curve encryption - diplomatic cables, corporate mergers, medical records, private communications - becomes readable.
The window of exposure is not 2029. It is 2026. The data being collected and archived this year will be exposed by a quantum computer three years from now.
"Quantum computers will pose a significant threat to current cryptographic standards, and specifically to encryption and digital signatures. The threat to encryption is relevant today with store-now-decrypt-later attacks." - Google Security Blog, March 25, 2026
This is precisely why Google's threat model update prioritizes PQC for authentication services now - not just as a future defensive measure, but as an immediate response to an attack that is probably already in progress.
The NSA's classified signals intelligence budget almost certainly includes large-scale SNDL collection programs. China's National Cryptographic Administration and Russia's FSB/FAPSI are believed to run equivalent operations. The U.S. has been aware of this possibility since the early 2000s; the fact that the intelligence community has consistently been ahead of academia on PQC timelines suggests the threat assessment behind closed doors has always been more alarming than what gets published.
What Google Is Actually Doing - Android 17 and Beyond
Google did not just issue a warning. It announced a concrete, phased program. The Android component is the most immediately visible piece.
Starting with the beta release, Android 17 will support ML-DSA - Module Lattice-based Digital Signature Algorithm, standardized by NIST as FIPS 204. ML-DSA will be added to Android's hardware root of trust, the secure element that anchors the boot chain and application signing.
ML-DSA is based on CRYSTALS-Dilithium, a lattice-based signature scheme whose security rests on the hardness of finding short vectors in lattices - a problem quantum computers provide no known speedup for. It produces larger signatures than ECDSA (roughly 2.4 KB for a Dilithium3 signature vs. 64 bytes for secp256k1), but this is considered an acceptable tradeoff.
The specifics of what Google is building into Android 17:
Android 17 Post-Quantum Cryptography Implementation
- ML-DSA hardware root of trust: Quantum-resistant keys baked into secure hardware, not just software
- Verified boot library: ML-DSA integrated into the secure boot sequence against manipulation attacks
- Android Keystore: ML-DSA key generation and storage in secure hardware for third-party apps
- Remote attestation migration: Devices proving their state to remote servers using PQC
- Play Store signature migration: Every app in the Play Store will eventually carry a PQC-signed certificate
- Developer impact: App signing pipelines will require updates to support ML-DSA keys
The Play Store migration is notable because it will cascade requirements onto every Android developer. At some point, Google will require apps to carry PQC signatures as a condition of distribution. The timeline for that mandate hasn't been announced, but the infrastructure groundwork is what Android 17 is laying.
Beyond Android, Google has been methodically migrating its own infrastructure. Chrome added experimental support for ML-KEM (the key exchange algorithm, formerly CRYSTALS-Kyber) in 2024. Google Cloud offers PQC key wrapping. Internal communications migrated to hybrid PQC in phases over the past two years. The 2029 deadline is the hard cutover point - the date by which Google says everything must be running on post-quantum algorithms.
Who Else Is Moving - And Who Isn't
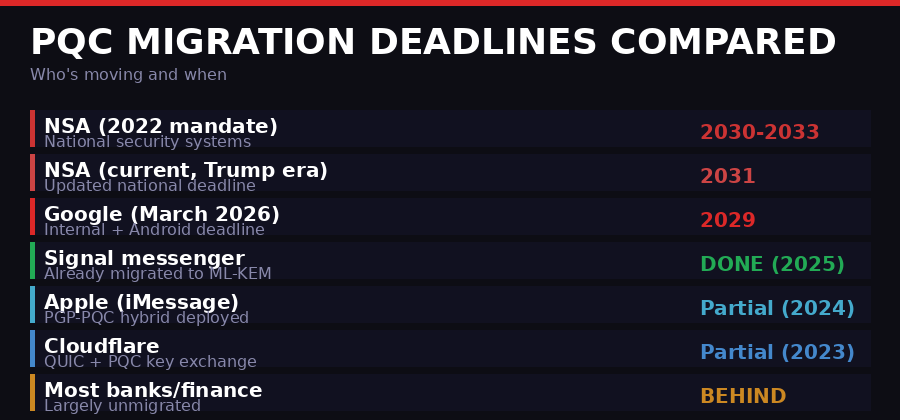
Migration timelines vary wildly. Google's 2029 deadline is more aggressive than even current NSA mandates. Most financial institutions haven't started. (BLACKWIRE/PRISM infographic)
Google is not alone. It is, however, ahead of the curve in terms of public commitment to a hard timeline.
Signal completed the most comprehensive PQC migration of any major consumer communications platform, deploying ML-KEM-768 (CRYSTALS-Kyber) in 2025 as a hybrid with its existing X3DH elliptic-curve key exchange. A Signal message today uses both protocols in parallel - if one is broken, the other maintains confidentiality. Ars Technica called it "an amazing engineering achievement" at the time of deployment.
Apple deployed PQ3 in iMessage in 2024, integrating Kyber-based key encapsulation in a hybrid scheme with its existing protocol. Apple assigned PQ3 its highest security classification for any messaging protocol it had deployed. However, iMessage's PQC covers key establishment, not signatures - and Apple hasn't announced a timeline for full PQC signature migration across iOS and macOS.
Cloudflare has been running PQC experiments in QUIC connections since 2023 and has added ML-KEM support to its TLS termination infrastructure. It publishes a public dashboard of PQC-capable connection percentages.
The NSA, under its Commercial National Security Algorithm Suite 2.0 (CNSA 2.0) mandate, has set 2030 for national security systems and 2033 for a broader set of applications. The current NSA deadline under the Trump administration has been revised to 2031. Google's 2029 target is now more aggressive than current federal mandates.
The sectors that are not moving fast enough are the critical ones: banking and finance, healthcare, energy infrastructure, and telecommunications. These sectors have enormous existing deployments of PKI-based systems with long replacement cycles. Updating a hospital's internal certificate infrastructure requires touching every device, every application, every authentication system. Replacing legacy banking mainframe cryptography is a multi-year, multi-billion-dollar project even without a looming deadline.
A 2025 NIST survey of enterprise organizations found that the majority had completed only the first phase of PQC preparation - inventorying their cryptographic assets. Far fewer had begun actual migration. The gap between "we know what we have" and "we have replaced it" is where most organizations currently sit, and three years is unlikely to be enough time for the laggards.
The Qubit Math - Why the Numbers Keep Shrinking
Understanding why Google moved the deadline requires understanding how the qubit requirement estimates have moved over time - and why they keep going down.
In 2012, the consensus estimate was that breaking 2048-bit RSA would require roughly one billion physical qubits. That was a number so large it seemed safely distant - building a billion-qubit machine would take decades at any plausible rate of progress.
In 2019, Craig Gidney and Martin Eker published a revised estimate: 20 million qubits. Still a very large machine, but noticeably closer. The improvement came from better algorithms for quantum arithmetic and more efficient error correction schemes.
In June 2025, Gidney published again. The new estimate: approximately one million noisy physical qubits, completing the factorization in under a week. The reduction came from algorithmic improvements - specifically, a more efficient modular exponentiation circuit and better use of magic state distillation for T-gate synthesis.
The trajectory here is not linear. Each revision reflects both better quantum algorithms and better understanding of how to use available hardware. There is no guarantee the next revision won't drop the requirement further.
At the same time, the hardware side has been closing in. Google's Willow chip demonstrated below-threshold quantum error correction in December 2024 - the first unambiguous demonstration that as you add more physical qubits to a surface code, the logical error rate actually improves exponentially, as theory predicts. Previously, the empirical data had been messier. Willow produced clean results. The coherence time for Willow's qubits is 68 microseconds, with gate fidelity exceeding 99.9%.
Current state of the art: around 1,000 high-fidelity qubits in leading research systems. Required for RSA attack: ~1 million. The distance to cover sounds large, but qubit counts in superconducting platforms have been doubling roughly every two to three years. Microsoft's topological qubits, ion trap systems from IonQ and Quantinuum, and photonic platforms from PsiQuantum are pursuing alternative architectures that may scale more efficiently than superconducting qubits.
Whether Q Day arrives in 2029 or 2032 or 2034, the migration work takes the same amount of time. Starting later just means failing later.
The NIST Standards - What PQC Actually Looks Like
NIST finalized its first set of post-quantum cryptography standards in August 2024, after an eight-year standardization process that began in 2016 and attracted global cryptanalysis attempts. Three algorithms were standardized:
NIST Post-Quantum Standards (Finalized 2024)
- ML-KEM (FIPS 203) - Key encapsulation mechanism based on Module-Lattice. Replacement for ECDH key exchange. Three variants: ML-KEM-512, ML-KEM-768, ML-KEM-1024. Signal uses ML-KEM-768.
- ML-DSA (FIPS 204) - Digital signatures based on Module-Lattice (formerly CRYSTALS-Dilithium). Replacement for ECDSA. Three parameter sets. This is what Android 17 is deploying.
- SLH-DSA (FIPS 205) - Hash-based stateless signatures (formerly SPHINCS+). More conservative security basis - relies only on hash function security rather than lattice hardness assumptions. Slower but extremely well-understood.
A fourth algorithm, FALCON, is under consideration for standardization as an alternative ML-DSA signature scheme. FALCON produces smaller signatures (690 bytes vs 2,420 bytes for Dilithium3) but is harder to implement correctly and has had side-channel vulnerabilities identified in naive implementations.
It is worth noting that one of the NIST candidates, SIKE (Supersingular Isogeny Key Encapsulation), was completely broken in 2022 by a classical attack that ran in about an hour on a standard laptop. This is why NIST ran an extended evaluation period - lattice-based schemes have survived intense scrutiny for years, but the process is not infallible. The current NIST standards are considered conservative, but the field is not finished.
The practical challenge with PQC migration is not just cryptographic - it is infrastructural. ML-DSA signatures are 2,420 bytes. An RSA-2048 signature is 256 bytes. ECDSA (secp256k1) is 64 bytes. Every protocol that currently transmits signatures will need to handle larger payloads. TLS handshakes grow. Certificate chains grow. Code signing packages grow. For bandwidth-constrained environments - embedded systems, IoT devices, satellite links - the overhead is significant.
Second-Order Effects: Blockchain, Finance, and the Security Industrial Complex
The implications of a quantum-capable adversary extend well beyond broken TLS connections. Several second-order effects deserve attention that they rarely receive in mainstream coverage.
Cryptocurrency: Bitcoin's secp256k1 curve is not quantum-resistant. Approximately 4 million BTC (roughly 20% of circulating supply) is held in addresses whose public keys are exposed on-chain - primarily because they have been used to send transactions, making the public key visible. A CRQC could derive the private keys for all of those addresses. The Bitcoin development community has discussed quantum resistance proposals (including Lamport signatures, hash-based schemes, and lattice-based alternatives) but the upgrade would require a hard fork and has no consensus timeline. The Ethereum community has similar exposure and has published EIPs addressing it, without finalized migration plans.
Certificate Authorities: The entire PKI web of trust - the system that lets browsers validate websites via chains of signed certificates - depends on RSA and ECC. A CRQC-enabled attack on a root CA private key would allow forging certificates for any domain in the world. Mass migration of root CA infrastructure to PQC algorithms requires browser vendors, OS vendors, CA operators, and website operators to coordinate. The last major PKI migration (extending RSA-1024 to RSA-2048) took about a decade and left substantial legacy exposure. PQC migration is a larger change.
The security vendor market: Hardware Security Modules (HSMs) - the physical devices that store private keys in secure enclaves - will need firmware and hardware updates to support PQC algorithms. Companies like Thales, nCipher (now part of Entrust), and AWS CloudHSM have begun offering PQC-capable HSMs, but the installed base of legacy devices is enormous. Enterprises that use HSMs for key storage - banks, government agencies, healthcare systems - face hardware replacement cycles on top of software migration work.
Long-lived secrets: Some secrets need to remain confidential for decades. Nuclear facility operational data. Intelligence source identities. Long-term financial arrangements. State negotiating positions. These are precisely the categories most at risk from SNDL attacks - because they were sensitive when collected and will remain sensitive when decrypted years later. For this category, the window to protect data retroactively closed when the data was first transmitted over RSA or elliptic-curve channels. The damage from SNDL is partially irreversible.
What Happens If the Industry Doesn't Move
Google has been unusually direct about the consequences. Its blog post essentially says: if you are running RSA or ECC when a CRQC comes online, everything you have ever protected with those algorithms is compromised simultaneously.
The scenario is not a slow leak. It is a cliff. One day RSA is secure; the next day every RSA-protected secret in history is readable by whoever has the quantum hardware. Given that state-level actors are the most likely to have early access to a CRQC, the initial beneficiaries of that cliff are intelligence agencies - the same ones already running SNDL collection programs.
The second wave is criminal. Once CRQC capability diffuses beyond state actors - either through espionage, commercial development, or academic replication - criminal organizations will have access to the same decryption capability. Bank account credentials protected by TLS. Stored passwords from breaches. Medical records. Corporate intellectual property.
Google's 2029 deadline is aggressive not because it believes Q Day definitely arrives in 2029. It is aggressive because completing the migration before the threat arrives requires starting now. The people who wait for Q Day to be confirmed before beginning their migration will be too late. The migration work itself takes years.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on TelegramThe Timeline - From Shor to 2029
Peter Shor publishes Shor's algorithm, showing that a quantum computer can factor integers in polynomial time - directly breaking RSA. Also shows discrete log (ECDH, ECDSA) can be broken. Cryptographers are put on notice.
Best estimate: breaking 2048-bit RSA requires ~1 billion physical qubits. Q Day seems safely a century away.
NIST opens its Post-Quantum Cryptography standardization process, accepting 69 candidate algorithms. The PQC migration formally begins as a field.
Craig Gidney and Martin Eker revise the RSA-break estimate down to 20 million qubits. The threat doubles in perceived proximity overnight.
NSA publishes CNSA 2.0, mandating PQC for national security systems by 2030-2033. SIKE, a finalist NIST candidate, is broken by a classical attack in under an hour.
NIST finalizes three post-quantum standards: ML-KEM (FIPS 203), ML-DSA (FIPS 204), SLH-DSA (FIPS 205). The algorithms the world must migrate to are now settled.
Google's Willow chip (105 qubits) demonstrates below-threshold quantum error correction. Published in Nature. The hardware trajectory shifts. Error-corrected qubits are now real, not theoretical.
Craig Gidney publishes revised RSA-break estimate: ~1 million noisy qubits sufficient. Approximately a 20x reduction from the 2019 estimate. The Gidney paper directly cites Willow-class hardware as motivation for revisiting assumptions.
Google sets internal deadline of 2029 for full PQC migration. Announces Android 17 will include ML-DSA in the hardware root of trust. Tells the rest of the industry to follow suit. The public alarm clock goes off.
What to Watch Next
Google's announcement is likely to trigger a cascade of similar disclosures. When a major technology company with Google's internal threat intelligence sets a hard deadline, it changes the political calculus for CISOs at banks, hospitals, and government agencies who have been deferring the migration conversation.
Several near-term developments are worth watching closely:
Android 17 beta timeline. Google typically releases its first developer previews in February and the public beta around May-June. The ML-DSA integration will be technically verifiable once the beta ships. Whether the implementation is actually resistant to side-channel attacks - a genuine weakness in many early PQC deployments - will be scrutinized by the research community immediately.
NSA deadline movement. If Google is moving to 2029 based on threat intelligence, the NSA may follow with an accelerated CNSA 2.0 mandate. The current 2031 date has always been treated as conservative. A revision to 2029 or earlier would send an unmistakable signal to federal contractors and critical infrastructure operators.
Banking sector response. Financial regulators - OCC, FDIC, Fed - have been watching PQC migration requirements accumulate without firm mandates. A Google-level public declaration of 2029 as a credible threat horizon may accelerate regulatory action. Banking CISOs who have been using regulatory ambiguity as cover for delayed migration will have less cover after this week.
Cryptocurrency emergency planning. The Bitcoin and Ethereum developer communities have known this was coming. The question is whether a credible 2029 threat estimate finally forces the hard fork conversations that have been repeatedly deferred. Any quantum-resistant migration for Bitcoin requires enormous community coordination and years of implementation work. If that process doesn't start now, it doesn't finish before Q Day.
Google's 2029 deadline will probably not be exactly right. Q Day might arrive in 2028. It might arrive in 2034. But the direction of travel on the qubit estimates is unambiguous - every major revision has been downward. The people who wait for certainty before beginning migration are making a bet with other people's secrets.
The migration window is closing. The alarm just went off.
Sources: Google Security Blog (March 25, 2026), Ars Technica, Craig Gidney/Google Research arXiv:2505.15917, Google Willow paper in Nature (December 2024), NIST Post-Quantum Cryptography Standards (FIPS 203/204/205), NSA CNSA 2.0, Brian LaMacchia/Farcaster Consulting Group via Ars Technica.