Google Found Bitcoin's Kill Switch Inside Taproot - 500K Qubits, 9 Minutes, One-Third of All BTC Exposed
Google's Quantum AI team dropped a whitepaper Monday showing Bitcoin's cryptography can be broken with far fewer quantum resources than anyone assumed. Worse: the 2021 Taproot upgrade - designed to improve privacy - accidentally expanded the attack surface. 6.9 million BTC are sitting exposed. The clock isn't ticking in decades anymore. It's ticking in years.

Quantum processors are advancing faster than Bitcoin's defense mechanisms can adapt. Photo: Unsplash
There's a number that should keep every Bitcoin holder awake tonight: 500,000.
That's how many physical qubits Google's Quantum AI team now estimates it would take to crack the elliptic curve cryptography protecting Bitcoin wallets. Not the "millions" that researchers have been casually throwing around for years. Not the comfortable far-future timeline that lets everyone sleep easy. Half a million. And Google has been openly targeting commercially useful quantum systems by 2029.
The research, published Monday in a new whitepaper alongside a blog post on Google's research portal, doesn't just move up the quantum threat timeline. It identifies a specific, overlooked vulnerability that Bitcoin's own community engineered into the protocol: Taproot.
The 2021 upgrade was supposed to be a win - better privacy, more efficient transactions, cleaner smart contract execution. Instead, Google's researchers argue, it stripped away a layer of cryptographic protection that had been quietly shielding wallets from quantum attacks. Public keys, which older address formats kept hidden until funds were spent, are now visible on the blockchain by default under Taproot.
That visibility is the kill switch. And 6.9 million BTC - roughly one-third of the entire supply, worth approximately $459 billion at current prices - are already sitting in wallets where public keys have been exposed.
The gap between current quantum capability and a viable Bitcoin attack is shrinking faster than anyone modeled.
The Whitepaper That Rewrote the Timeline

Google's quantum team has been systematically mapping cryptocurrency vulnerabilities since 2024. Photo: Unsplash
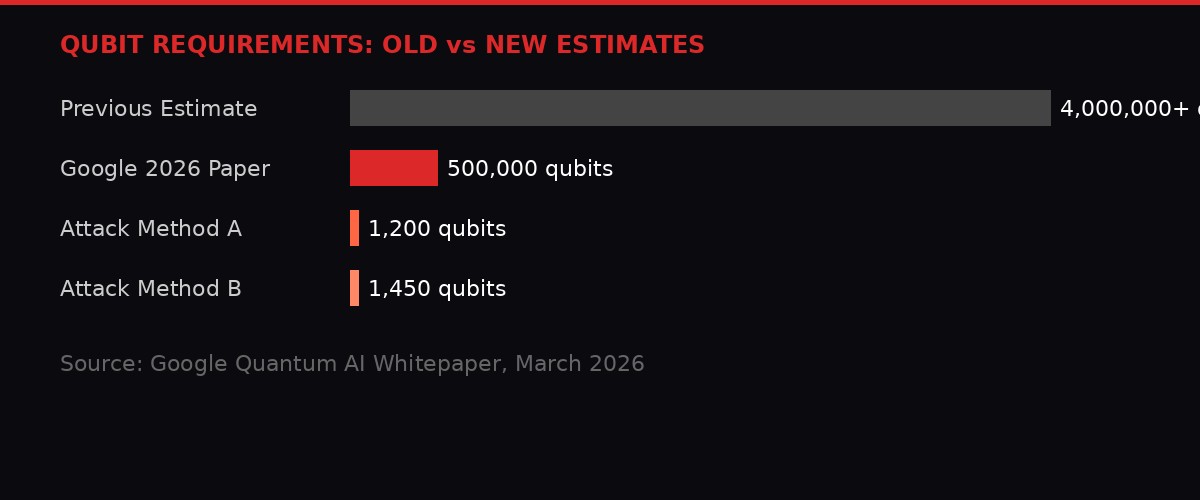
Google Quantum AI's paper presents two distinct attack methods against Bitcoin's Elliptic Curve Digital Signature Algorithm (ECDSA), the cryptographic scheme that secures every transaction on the network. Both methods require between 1,200 and 1,450 high-quality logical qubits - a fraction of the physical qubit count but still a breakthrough reduction from prior estimates.
The distinction between logical and physical qubits matters enormously here. Logical qubits are error-corrected, reliable quantum bits. Physical qubits are the raw hardware units, which are noisy and error-prone. You need many physical qubits to create each logical qubit. Google's estimate of fewer than 500,000 physical qubits to mount a viable attack accounts for this overhead - and it's still dramatically lower than the 4 million+ figure that was standard wisdom as recently as 2024.
To put this in context: Google's current Willow chip operates with around 105 physical qubits. IBM's Condor processor hit 1,121 qubits in late 2023. The roadmap for both companies targets 100,000+ physical qubits by 2029-2030. At the current pace of scaling, 500,000 qubits could arrive by the early 2030s - not the 2040s or 2050s that the crypto community had been pricing in.
KEY NUMBERS FROM THE GOOGLE WHITEPAPER
500,000 - Physical qubits needed to break Bitcoin's ECDSA (new estimate)
4,000,000+ - Physical qubits previously estimated (pre-2026 consensus)
1,200-1,450 - Logical qubits required for two attack methods
6.9 million - BTC with exposed public keys (33% of supply)
9 minutes - Time to complete key derivation once a transaction is broadcast
41% - Probability of beating Bitcoin's 10-minute block confirmation
2029 - Google's target year for commercially useful quantum systems
The previous consensus, built on a series of academic papers from 2019-2023, assumed that attacking ECDSA would require at minimum 2,500 logical qubits and millions of physical ones. Google's team achieved the lower bound through algorithmic optimization - not hardware breakthroughs. They found more efficient ways to decompose the mathematical problem, reducing the circuit depth and qubit overhead simultaneously.
This is the part that should genuinely alarm people. The hardware hasn't changed. The math got better. And math improvements compound - every new optimization applies retroactively to every quantum chip that will ever be built.
The 9-Minute Heist: How a Quantum Attack Actually Works
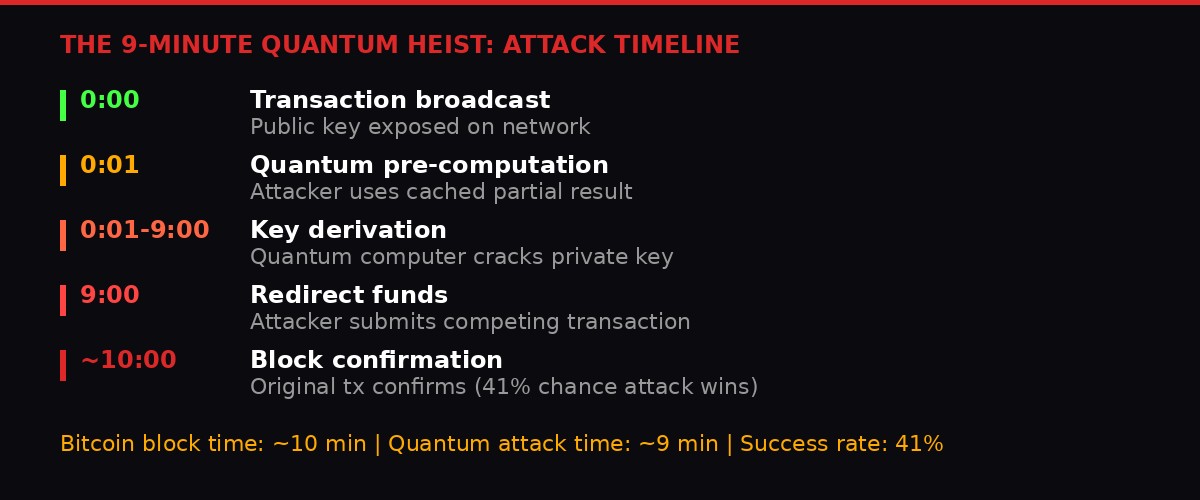
The attack window is terrifyingly narrow - and precisely calibrated to Bitcoin's 10-minute block time.
Google's paper doesn't just estimate qubit requirements. It maps out a practical attack scenario that reads like a technical thriller.
Here's the sequence: A quantum attacker doesn't need to break into old wallets sitting dormant on the blockchain. The far more dangerous approach targets transactions in flight. When someone sends Bitcoin, the transaction broadcasts to the network and sits in the mempool waiting for a miner to include it in a block. During this window - typically around 10 minutes - the sender's public key is visible to anyone watching.
A sufficiently powerful quantum computer could use that exposed public key to reverse-engineer the corresponding private key. Google's model suggests the computation could be pre-staged: much of the mathematical work can be done in advance using generic parameters, with only the final derivation step requiring the specific public key from the target transaction.
Once the private key is derived, the attacker submits a competing transaction that redirects the funds to their own wallet. If the attacker's transaction gets confirmed before the legitimate one, the money is gone. Google estimates this final derivation step takes approximately 9 minutes - just under Bitcoin's average block confirmation time of 10 minutes.
The math works out to a 41% success rate per attempt. Flip a coin, roughly. Except the attacker can try again on every transaction they target, and the defender has no way to speed up confirmation or detect the attack in progress.
"The attack model assumes the adversary can pre-compute a significant portion of the key derivation offline, reducing the real-time computation to approximately nine minutes once the target public key is observed." - Google Quantum AI Whitepaper, March 2026
There's a key asymmetry in this model that makes it worse than it sounds. The attacker only needs to succeed once to steal funds. The defender needs to succeed every time. And unlike traditional hacking - where security patches can close vulnerabilities after they're discovered - a quantum break of ECDSA would require a fundamental change to Bitcoin's cryptographic foundation. That's a hard fork. That's years of debate in a community that took three years to agree on a block size change.
Taproot: The Upgrade That Opened the Door

Taproot was Bitcoin's biggest upgrade since SegWit. Google's paper suggests it came with an unintended cost. Photo: Unsplash
Bitcoin's Taproot upgrade, activated in November 2021, was designed to solve real problems. It made multi-signature transactions indistinguishable from regular ones, improving privacy. It enabled more complex smart contracts through Merkelized Abstract Syntax Trees (MAST). It reduced transaction sizes and fees. The upgrade was widely celebrated as a technical achievement.
But Taproot introduced Schnorr signatures, replacing the older ECDSA scheme for many transaction types. The critical change: Taproot addresses (starting with "bc1p") expose the public key directly on the blockchain. Previous address formats - Pay-to-Public-Key-Hash (P2PKH) and Pay-to-Script-Hash (P2SH) - added an extra layer of indirection. The blockchain stored a hash of the public key, not the key itself. The actual public key was only revealed when funds were spent.
That indirection wasn't designed as quantum protection. It was simply how Bitcoin's original addressing scheme worked. But it had the incidental effect of keeping public keys hidden from potential quantum attackers until the moment of spending. Once funds were spent and the public key was revealed, the money was already gone - there was nothing left to steal.
Taproot removed that incidental protection. Now, the public key sits on the blockchain from the moment funds arrive at a Taproot address. A quantum attacker doesn't need to wait for a transaction to catch a public key in the mempool. For Taproot addresses, the key is already there, permanently visible, waiting.
Google's researchers specifically flagged this design choice as expanding the quantum attack surface. The paper states that Taproot's visibility model "increases the number of wallets vulnerable to future quantum attacks" compared to legacy address formats.
It's worth noting that Taproot adoption has grown steadily since 2021. According to on-chain analytics, approximately 15-20% of all Bitcoin transactions now use Taproot outputs. Major wallets including those from exchanges like Coinbase and Kraken default to Taproot addresses for new deposits. Every one of those addresses has an exposed public key sitting on the blockchain right now.

The 6.9 million exposed BTC comes from three distinct categories - and Taproot is the newest contributor.
6.9 Million BTC: The Exposure Map

One-third of all Bitcoin ever mined sits in wallets with exposed public keys. Photo: Unsplash
Google's whitepaper estimates that approximately 6.9 million BTC - roughly 33% of the total circulating supply - currently sit in wallets where the public key has been exposed in some form. At Bitcoin's current price of roughly $66,500, that's approximately $459 billion in potentially quantum-vulnerable funds.
The exposure breaks down into three categories:
Early-era wallets (approximately 1.7 million BTC): Bitcoin's earliest transactions used a format called Pay-to-Public-Key (P2PK), which stored the full public key directly on the blockchain. This includes Satoshi Nakamoto's estimated 1.1 million BTC, mined in the first two years of the network's existence. These coins haven't moved in over 15 years, and their public keys have been visible since day one. If a quantum computer ever becomes capable enough, these would be among the first targets - and the community has no way to force the owners (if they're even alive) to move funds to quantum-resistant addresses.
Address reuse (approximately 3.1 million BTC): When a user spends Bitcoin from a P2PKH or P2SH address and then receives new funds at the same address, the public key is already exposed from the previous spending transaction. Despite years of wallet developers warning against address reuse, it remains common - particularly among exchanges processing high volumes of transactions and users who publish static deposit addresses.
Taproot-exposed keys (approximately 2.1 million BTC): All Bitcoin held in Taproot (bc1p) addresses has its public key visible by default. This is the newest and fastest-growing category of exposure, and unlike the other two categories, it's a design feature rather than user error.
GOOGLE vs COINSHARES: DUELING EXPOSURE ESTIMATES
Google's 6.9 million BTC figure stands in sharp contrast to a CoinShares report from February 2026, which argued that only about 10,200 BTC are "concentrated enough to significantly move markets if stolen." The discrepancy comes down to methodology: CoinShares focused on large single-address holdings that could cause market impact if dumped. Google counted every wallet with an exposed public key regardless of balance size. Both numbers are correct - they're just measuring different things. The market impact question and the total vulnerability question are separate problems.
The implications for institutional holders are particularly severe. Companies running Bitcoin treasury strategies - MicroStrategy (now Strategy), Nakamoto Holdings, GameStop, Marathon Digital, and others - typically custody funds across multiple addresses, many of which use modern Taproot formats. The very features that made these corporate treasuries more efficient also made them more quantum-exposed.
David Bailey's Nakamoto Holdings, which just sold 284 BTC for $20 million to cover operational costs, holds approximately 5,400 remaining BTC. The company has an 8%, $210 million USDT loan from Kraken secured by a majority of those holdings. If quantum vulnerability concerns ever triggered forced liquidation clauses, the cascade effects could be brutal.
Real Yields, Oil at $103, and Why Bitcoin Is Stuck

March 2026 ends with crypto caught between war, yields, and now quantum risk.
The quantum research drops into a market already under severe pressure from multiple directions. Bitcoin trades at $67,500 as of Tuesday morning, roughly flat over the past 24 hours after recovering from a dip below $65,200 that briefly marked its lowest level since the Iran conflict began in late February.
The macro picture is ugly. WTI crude oil is trading above $100 per barrel for the first time since 2002, driven by the ongoing closure of the Strait of Hormuz. The S&P 500 is on its longest losing streak since 2022. MSCI Asia Pacific is tracking its worst month since October 2008 - the peak of the global financial crisis.
Real interest rates are the silent killer. The 10-year Treasury Inflation-Protected Securities (TIPS) yield has surged over 30 basis points to 2.02% since the U.S. and Israel first struck Iran on February 28. It hit 2.12% last week, the highest since June 2025. When risk-free real returns climb above 2%, the opportunity cost of holding a zero-yield asset like Bitcoin becomes punishing. Capital flows to safety. Bitcoin is not safety - not yet, not to the institutions that move markets.
"Bitcoin's situation is unlikely to improve without lower Fed rates and healthier liquidity, as rising real yields drive capital away from non-yielding assets." - Bitfinex Research, March 2026
The demand side confirms the squeeze. Bitfinex's absorption-to-emissions ratio (AER) - which measures institutional ETF demand relative to daily miner issuance of approximately 450 BTC - has collapsed from 5.3x in late February to just 1.3x. That means institutions are barely absorbing new supply. Any sustained rally would require the kind of aggressive inflows seen in late 2024 and early 2025, and there's no catalyst for that with yields rising and war ongoing.
ETF outflows punctuate the picture. Last week saw $171 million pulled from spot Bitcoin ETFs in the largest single-day outflow in three weeks. Stablecoin growth has stalled, signaling a drought of fresh fiat entering the crypto ecosystem. The pipeline is drying up at both ends.
And yet - and this is the genuinely strange part - Bitcoin is outperforming equities. The total crypto market cap sits at $2.32 trillion, roughly unchanged over a week in which the Nasdaq 100 dropped approximately 5%. JPMorgan noted Monday that Bitcoin is weathering the Iran crisis better than gold and silver, an observation that would have been unthinkable a year ago.
The range between $65,000 and $73,000 has held through every escalation of the conflict. Monday's dip below $65,200 and snap recovery above $67,000 looked like a classic stop-hunt that found real demand underneath. Someone is buying these dips. Whether that demand survives April - with potential ceasefire developments, Q1 earnings season, and now quantum vulnerability headlines - is the $2.32 trillion question.
The War That Won't End: Trump, Hormuz, and the Oil Trap

Hormuz remains largely closed. Oil above $100. And the president is talking about walking away. Photo: Unsplash
The Wall Street Journal reported Monday that Trump told aides he's willing to end the U.S. military campaign against Iran even if the Strait of Hormuz remains largely closed. The report sent equity futures up 0.8% and briefly knocked oil from $107 back to $103 before Iran struck a Kuwaiti crude carrier in Dubai's waters, stabilizing crude near the session highs.
The strategic calculus is clear: prying open Hormuz would push the conflict well beyond Trump's self-imposed four-to-six week timeline. The administration appears to be weighing whether a closed strait is an acceptable outcome if it means ending a war that's bleeding approval ratings and driving oil prices into recession territory.
For crypto, the scenario branches are binary and brutal. A genuine ceasefire would remove the headline risk that's kept Bitcoin range-bound for a month, potentially unlocking a relief rally toward $73,000-$75,000. But a closed Hormuz even after withdrawal keeps oil elevated, inflation expectations sticky, and rate-cut expectations dead on arrival. The Fed can't cut into $100+ oil. The market knows this.
Michael Kramer, founder of Mott Capital Management, put it bluntly: oil is in the driver's seat. "It is tightening financial conditions across the broader market complex - a process that is likely to persist as long as oil continues to rise." Rising oil feeds into CPI. Rising CPI kills rate-cut probability. Dead rate-cut probability kills the liquidity thesis that every Bitcoin bull has been banking on since 2024.
The 10-year real yield rising faster than the 5-year real yield tells a specific story: the market is pricing tighter conditions further out the curve. Not temporary tight. Structurally tight. That's the environment where zero-yield risk assets go to die, historically. That Bitcoin is holding $65,000+ despite this is either a sign of genuine structural demand or the calm before a much larger breakdown.
KuCoin's Permanent Exile and the Enforcement Cascade

KuCoin's U.S. chapter ends not with a fine, but with permanent exile. Photo: Unsplash
While quantum threats loom on the horizon, the enforcement machine continues grinding in real time. A federal court approved a CFTC consent order Monday permanently barring KuCoin operator Peken Global Limited from serving U.S. users unless it registers as a foreign board of trade - something no crypto exchange has ever done.
The order imposes a $500,000 civil penalty on top of the nearly $297 million in penalties and forfeitures from KuCoin's January 2025 guilty plea to operating an unlicensed money transmitting business. The relatively modest civil fine reflects that the DOJ already extracted the financial punishment - the CFTC action was about market access, not money.
KuCoin had approximately 1.5 million registered U.S. users and generated at least $184.5 million in fees from them. The exchange only introduced KYC requirements in August 2023 and didn't apply them retroactively to existing accounts - a gap that became central to the prosecution's case.
The enforcement structure here is notable. U.S. authorities ran a sequential prosecution: criminal charges first (DOJ), then civil market bans (CFTC). The effect is comprehensive - KuCoin faces both financial punishment and permanent exclusion. What had been a temporary two-year U.S. withdrawal is now an indefinite ban.
This matters for the broader market because it establishes a template. Any offshore exchange that served U.S. users without registration can expect the same one-two punch: DOJ for the criminal liability, CFTC for the permanent market ban. Binance already faced a similar structure. OKX, Bybit, and others are watching carefully.
The $184.5 million in fees that KuCoin earned from U.S. users is now effectively evidence of the crime. Every dollar of revenue from an unregistered U.S. user is a dollar of unlicensed money transmission. The message to offshore exchanges is explicit: serve U.S. users without registration, and we will take the money and the market access.
The Quantum Migration Problem: Bitcoin's Governance Bottleneck

Moving Bitcoin to quantum-resistant cryptography would be the largest protocol change in the network's history. Photo: Unsplash
Google's paper doesn't just identify the vulnerability. It implies a solution timeline that collides directly with Bitcoin's governance reality.
Post-quantum cryptographic algorithms exist. NIST finalized its first set of post-quantum standards in 2024, selecting CRYSTALS-Kyber for key encapsulation and CRYSTALS-Dilithium for digital signatures. These algorithms are designed to resist both classical and quantum attacks. Ethereum developers have already begun preliminary research into post-quantum signature schemes.
Bitcoin's problem isn't technology. It's governance. Migrating to post-quantum signatures would require a hard fork - a non-backward-compatible change to the consensus rules. The last time Bitcoin attempted anything approaching this scale of change was the block size debate of 2015-2017, which took three years, split the community, created Bitcoin Cash as a fork, and left scars that still shape protocol politics today.
A quantum migration would be orders of magnitude more complex. Every wallet would need to move funds from legacy ECDSA addresses to new post-quantum addresses. Users who don't migrate - including Satoshi's estimated 1.1 million BTC, lost wallets, deceased holders' funds, and simply inattentive users - would be left permanently vulnerable. The community would face an impossible choice: freeze unmigrated funds (effectively confiscating them) or leave a permanent vulnerability in the network.
Google appeared aware of this governance dimension. The team used zero-knowledge proofs to publish their findings - proving the attack methods work without revealing the specific techniques. It's responsible disclosure, cryptography-style. But the clock is still running. Every day that Bitcoin's cryptographic foundation remains unchanged is a day closer to the hardware catching up to Google's mathematical optimization.
The BIP (Bitcoin Improvement Proposal) process has shown no urgency on quantum migration. There are scattered proposals and mailing list discussions, but nothing approaching consensus on a timeline, an algorithm choice, or a migration mechanism. Google's paper may force the conversation, but forcing conversation and forcing action are very different things in Bitcoin's deliberately slow governance model.
Market Implications: Pricing the Unthinkable

Markets have never priced a cryptographic risk event. They may have to start. Photo: Unsplash
Financial markets are good at pricing wars, recessions, earnings misses, and policy changes. They are terrible at pricing existential technical risks with uncertain timelines. The quantum threat to Bitcoin falls squarely in the second category.
Today's price action shows no quantum panic. Bitcoin is up 2% on the week, holding $67,500, grinding sideways through the same $65K-$73K range it's occupied since the Iran war began. The market has clearly decided that quantum attacks are a 2030s problem, not a 2026 problem. Google's paper may not change that - today.
But the compounding dynamic matters. Every Google paper, every IBM qubit milestone, every quantum startup funding round moves the Overton window. At some point - and the paper argues it could be sooner than 2030 - the market will reprice the risk discontinuously. Not gradually. Not efficiently. In one ugly session where everyone tries to move funds to quantum-resistant alternatives simultaneously.
For the institutional players now dominating Bitcoin flows through ETFs, the quantum risk creates a novel fiduciary question. If a fund manager holds Bitcoin in a Taproot-based custody solution and Google publishes a paper saying those wallets could be vulnerable within the fund's investment horizon, does that create a disclosure obligation? A duty to migrate? The SEC hasn't addressed this. No regulator has. But the question is now on the table.
Keyrock, the Brussels-based crypto trading firm that just raised a Series C at a $1.1 billion valuation led by Standard Chartered's venture arm, represents the kind of institutional infrastructure that will eventually need to answer these questions. The firm operates across 80+ centralized and decentralized venues. Its market-making activity depends on the cryptographic integrity of every chain it touches. Quantum risk isn't theoretical for firms like Keyrock - it's a business continuity question.
The Hashdex NCIQ ETF, which added options trading on Nasdaq Monday, now gives institutional investors the ability to hedge diversified crypto exposure for the first time. The timing feels almost providential: the first week where institutions can buy puts on a broad crypto basket is the same week Google publishes the most aggressive quantum vulnerability assessment to date.
Q1 2026 CRYPTO SCORECARD
BTC: $67,500 (down from $96,000 Jan 1 - a 30% Q1 decline)
ETH: $2,062 (down from $3,400 Jan 1 - a 39% Q1 decline)
SOL: $83 (down from $190 Jan 1 - a 56% Q1 decline)
Total market cap: $2.32T (down from $3.4T Jan 1)
ETF AER: 1.3x (down from 5.3x in February)
WTI crude: $103 (up from $72 Jan 1 - a 43% Q1 increase)
10Y TIPS yield: 2.02% (up from 1.72% Jan 1)
Stablecoin growth: Stalled at $440B
What Happens Next
Google's paper will filter through the crypto ecosystem over the coming days. Bitcoin developers will cite it in BIP discussions. Quantum computing skeptics will argue - correctly - that 500,000 physical qubits don't exist yet and may not for years. Taproot proponents will point out - also correctly - that the privacy and efficiency benefits are real and immediate, while quantum attacks are still theoretical.
Both sides will be right. That's the problem. The benefits of Taproot are concrete today. The risks are probabilistic tomorrow. Humans are catastrophically bad at weighing certain present gains against uncertain future losses. It's why we build houses on flood plains and ignore pandemic warnings until the hospitals are full.
The actionable items are clear even if the timeline isn't. Bitcoin developers need to begin serious post-quantum migration planning now - not when the hardware arrives. Wallet providers should offer users the option to avoid Taproot addresses for high-value, long-term storage. Institutional custodians should disclose their address-type distribution to clients. And Google's approach of using zero-knowledge proofs for responsible disclosure should become the standard for all quantum vulnerability research.
The alternative is waiting. And if Google's trajectory holds - useful quantum systems by 2029, continued algorithmic optimization reducing qubit requirements further, Taproot adoption continuing to grow - then the window for an orderly migration narrows with every block.
500,000 qubits. 9 minutes. 41% success rate. One-third of all Bitcoin exposed.
The numbers don't lie. The clock doesn't stop. And the kill switch is already installed.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram