Iran Built a Surveillance State to Control Its People. Israel Turned It Into a Kill Network.
Tehran installed hundreds of thousands of cameras to crush dissent. For years, Mossad was watching through every lens. When the moment came, those cameras guided the strike that killed the supreme leader.

A security camera mounted above a Tehran intersection. For years, footage from cameras like this streamed not just to Iranian authorities - but to Israeli intelligence servers. (Pexels)
The warnings were public. The evidence was there. For years, Iranian officials knew their country's surveillance network had been compromised. They said so out loud. A senior member of the Iranian parliament's national security committee stood before state media in September 2025 and delivered what should have been a national emergency: "All the cameras at our intersections are in the hands of Israel. Everything on the internet is in their hands ... if we move, they will find out."
Nobody fixed it.
On February 28, 2026, Ayatollah Ali Khamenei - supreme leader of the Islamic Republic for 35 years, the most protected man in Iran - was tracked to his leadership compound through the same street cameras his regime had installed to monitor dissidents. Israeli intelligence, drawing on years of accumulated camera access and AI-powered analysis, watched his movements in real time. The strike was ready. The trigger was pulled. Khamenei was dead within hours of the war's opening salvo.
A new Associated Press investigation, drawing on two intelligence sources with direct knowledge of the operation, has now confirmed what was long suspected: that Tehran's own surveillance infrastructure was a central instrument in the most consequential targeted killing in the history of the modern Middle East.
The story of how Iran built a panopticon to rule its people - and how that panopticon was systematically hollowed out and turned against them - is a story about power, technology, and an irony so complete it reads like fiction.
The Architecture of Fear

Dense surveillance camera networks in urban centers have become the primary tool of authoritarian population control - and the primary vulnerability for the regimes deploying them. (Pexels)
Iran's camera expansion was not accidental. It followed directly from the regime's terror of its own population.
After Mahsa Amini died in the custody of the morality police in 2022, protests erupted across Iran on a scale the regime had not seen in decades. The response was ferocious - thousands killed, tens of thousands arrested. But the Islamic Republic also drew a lesson about surveillance: the cameras it had were not enough. It needed more, better, faster.
By the time the January 2026 protests swept Iran - the largest demonstrations in the republic's history, ending in a crackdown that killed many thousands according to AP reporting - Tehran was carpeted in cameras. Subway systems used facial recognition to catch women not wearing the mandatory hijab, automatically sending violation notices to their registered phones. Intersection cameras mapped the movements of known activists. Traffic cameras fed continuous data on who was moving where, at what hour, in what vehicle.
The Iranian state built what researcher Michael Caster, who investigated China's sales of surveillance technology to Iran, calls a "data collection infrastructure" that was, in theory, impregnable. In practice, it was running on sanctioned hardware, pirated software, and a patchwork of Chinese-manufactured electronics that were years out of date. Hikvision and Dahua cameras - two of the world's most widely deployed brands, both Chinese - made up the backbone of the network.
Both companies' products were riddled with vulnerabilities that security researchers had been flagging for years. Patches were available. They were not consistently applied. The cameras were installed with minimal security by users who, as security engineer Paul Marrapese put it to AP, were "unsophisticated" - often leaving default passwords like "1234" in place, connected directly to the public internet.
"There are millions and millions and millions of these throughout the world. Many are trivially easy to hack. They're just dumb little things. It's fish in a barrel." - Paul Marrapese, security engineer who first documented mass camera vulnerabilities in 2019
Marrapese's 2019 scan found millions of unprotected cameras globally. His most recent scan, conducted this year, returned nearly three million hits in almost every country on earth - including nearly 2,000 cameras in Iran alone. The number of unprotected cameras has not shrunk since he first raised the alarm. It has grown.
How Israel Got Inside

Intelligence agencies and hackers alike have learned that poorly secured surveillance cameras connected to the public internet require minimal effort to penetrate at scale. (Pexels)
The hacking of Iran's cameras did not happen in a single dramatic operation. It happened incrementally, over years, across multiple attack surfaces.
In 2021, an Iranian exile group leaked footage from inside Tehran's Evin prison - a facility so notoriously brutal it had become a symbol of the regime's repression. The leak proved what cybersecurity experts had long argued: the cameras were already compromised. If dissidents and exile groups could get in, so could a nation-state with the resources of Israeli intelligence.
In 2022, another group claimed it had hacked over 5,000 cameras around Tehran, dumping gigabytes of surveillance footage and internal data on a Telegram channel. The footage included government buildings, military installations, and ordinary street intersections. The message was clear: Iran's surveillance network was not a closed system. It was a sieve.
According to the person briefed on the Khamenei operation who spoke to AP, the Israeli operation went far beyond individual hacks. For years, almost all traffic cameras in Tehran had been compromised. The footage was transferred in real time to servers in Israel. Algorithms processed the data continuously - identifying faces, tracking vehicles, logging patterns, building profiles of everyone who moved through the capital's key corridors.
The vulnerabilities exploited are now documented. Check Point Research, which has been tracking Iranian camera-hacking operations throughout the war, published a detailed analysis this month identifying the specific CVEs used in attacks against cameras across Israel, Qatar, Bahrain, the UAE, Kuwait, Lebanon, and Cyprus. Five critical vulnerabilities in Hikvision and Dahua cameras - some dating back to 2017 - formed the toolkit. Patches for all of them existed. Most cameras in Iran had not applied them.
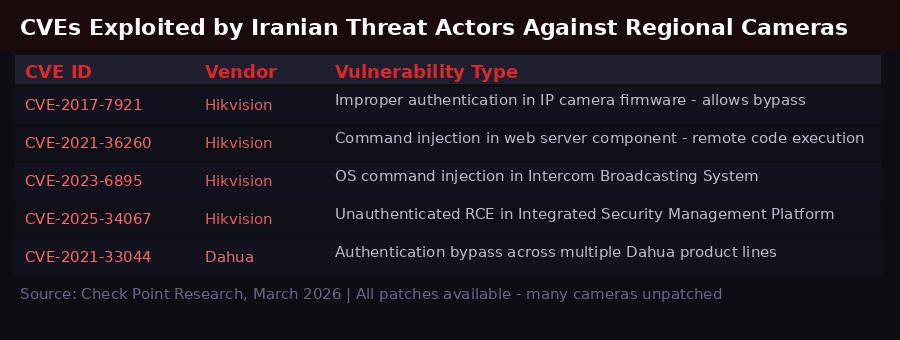
The five critical CVEs used by Iranian threat actors against regional cameras - and the mirror-image vulnerabilities that allowed Israeli intelligence to penetrate Tehran's network for years.
The timeline of compromise aligns precisely with the escalation of Iranian surveillance. As the regime installed more cameras to monitor its population, it created more entry points. Every new camera added to the network was another potential node for Israeli intelligence to tap. The expansion of the panopticon was simultaneously an expansion of the attack surface.
"The irony is that the infrastructure authoritarian states build to make their rule unassailable may be what makes their leaders most visible to the people trying to kill them. Do you trust who is watching?" - Conor Healy, director of research, IPVM (surveillance research publication)
The Intelligence Operation That Killed a Supreme Leader

Modern intelligence operations combine human sources, signals intelligence, and AI-processed surveillance feeds to build targeting packages with unprecedented precision. (Pexels)
According to the AP's sources, the operation that killed Khamenei had been in planning for months before February 28. The camera network was not the only source of intelligence - it was one layer in a comprehensive targeting package that included signals intelligence, human assets inside Iran, and intercepted communications.
But the cameras provided something the other sources could not: continuous, real-time visual confirmation of movements. At least one camera was positioned at an angle that gave Israeli intelligence a direct line of sight on the approaches to Iran's leadership compound. The footage showed where key officials parked their cars. It tracked the routes they took to and from work. It identified their security details - how many guards, where positioned, what vehicles they drove.
Algorithms processed this data automatically. What would have taken a team of analysts months could be done in hours. Patterns emerged: when Khamenei moved, how often, with what protection, at what times of day. The operation was expedited, AP sources said, once intelligence confirmed that Khamenei and his top officials would be in the compound together on the morning of February 28.
Col. Amit Assa, a former official with Israel's Shin Bet domestic security service, explained the operational logic to AP. When you see a person's face on the screen in the command center, he said, "it helps in making the decision to put your finger on the yellow button."
Visual confirmation is the difference between intelligence and action. The cameras provided that confirmation at scale, in real time, with AI-assisted identification that removed the uncertainty that had historically made such operations so risky.
This was not the first time Israel had used Tehran's cameras offensively. During the 12-day war between the two countries last summer, Israel tracked and bombed the location of a meeting of Iran's Supreme National Security Council using the same compromised camera network. Iranian President Masoud Pezeshkian was injured in that strike. The capability had been demonstrated and rehearsed. The February 28 operation was its full deployment.
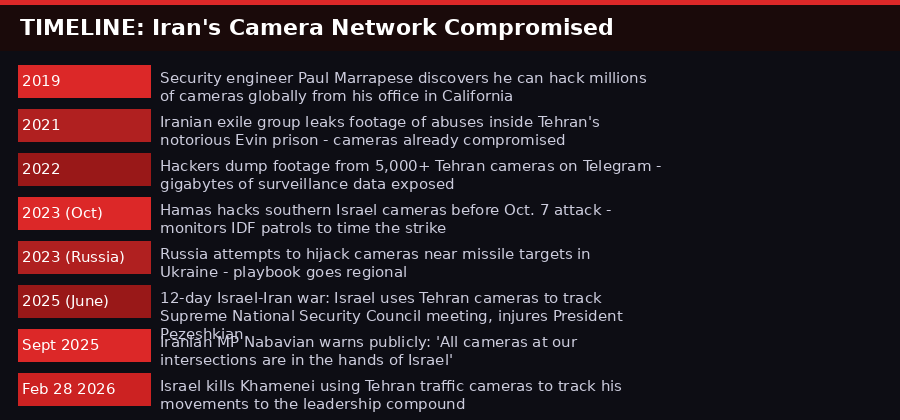
The five-year escalation from discovered vulnerabilities to operational targeting - a timeline that Iran's security establishment failed to interrupt at every stage.
AI Removes the Human Bottleneck

AI-powered video analysis has transformed what militaries and intelligence agencies can do with hacked surveillance feeds - turning terabytes of raw footage into actionable targeting data in real time. (Pexels)
The question security experts had long grappled with was not whether Iran's cameras could be hacked. They clearly could. The question was what you could do with the footage once you had it. A billion cameras worldwide generate more video data than any human intelligence apparatus could process.
Artificial intelligence changed that equation. Cryptographer and security expert Bruce Schneier described the transformation to AP with characteristic precision: "It used to be that you could hack the cameras, but humans had to do the real work of figuring out where the person was. With AI systems, you can do a lot more automatically."
The specific capabilities are not publicly detailed - but the general architecture is well understood. With a keyword search or a target photograph, AI systems can scan live and archived footage across thousands of camera feeds simultaneously, flagging appearances of a specific face or vehicle. Pattern recognition algorithms can map habitual routes, identify anomalies, and generate predictive models of future movements. What once took weeks now takes minutes.
This is why Hamas's use of hacked Israeli cameras before the October 7 attack in 2023 - flagged by Israeli media at the time - was a dress rehearsal for a capability that was already being deployed against Iran at far greater scale. Hamas used camera access to monitor Israeli army patrols and time the strike. Israel used camera access to build a comprehensive movement profile of the supreme leader over months, then act the moment the intelligence confirmed he was in the kill zone.
Gil Messing, Check Point Research's chief of staff, offered the analyst's perspective: "The more people are installing cameras, the more area is being covered by these cameras. It is very easy to use in order to get extra eyes into different places."
The paradox is structural. Authoritarian governments install cameras to gain information advantage over their populations. But the same cameras, once compromised, give adversaries information advantage over the government. The more comprehensive the surveillance network, the more complete the targeting package for anyone with access to it.
The Despot's Dilemma - and Why It Can't Be Solved

The dilemma facing authoritarian states is structural - the same technology that enables population control also creates exploitable attack surfaces for adversaries. (Pexels)
Muhanad Seloom, assistant professor in security studies at the Doha Institute for Graduate Studies, captured the regional shock in a single question: "How come Iran's whole leadership has been decapitated on the first day?"
Part of the answer is the cameras. But the deeper answer is the dilemma they represent - one that has no clean resolution for authoritarian governments.
To maintain control over a hostile population, these governments need surveillance. The surveillance requires cameras. The cameras need to be connected to processing networks to be useful. Connecting them to networks exposes them to external access. Securing them properly requires sophisticated IT infrastructure, constant patching, supply chains that are not compromised by sanctions, and technical expertise that may be in short supply precisely because the regime's best engineers have fled the country or been jailed.
Iran faced all of these problems simultaneously. Western sanctions cut off access to current-generation hardware and software. Pirated versions of Windows were common on government systems. Chinese-supplied cameras came with their own security vulnerabilities and, arguably, their own backdoors. The security professionals best equipped to address these problems had been leaving Iran for years.
Researcher Michael Caster, who studied China's surveillance technology exports to Iran, put the structural problem plainly: "Malicious parties can more easily gain access" when data is collected to consolidate authoritarian control. The act of building the infrastructure creates the vulnerability.
The warnings were not ignored entirely. Iran did attempt to segment some of its most sensitive networks from the public internet. But as Marrapese noted, even air-gapped systems are vulnerable: "It takes just one insider turncoat to compromise such systems. Humans are kind of the weakest link. There's really only so much you can do."
The Iranian MP who warned in September 2025 that the cameras were in Israeli hands was not operating in the dark. He was describing a known condition that had persisted for years - one that no amount of internal warning had succeeded in correcting.

The bitter irony: what Iran's regime built to monitor its people became the most precise tool its enemies had ever used against it.
Regional Alarm and the New Rules of Urban Surveillance

Governments across the Gulf and beyond are now urgently reviewing their camera security posture after the revelation that Iran's entire surveillance network was feeding Israeli intelligence for years. (Pexels)
The revelation has shaken every government in the region with a dense urban camera network - which is to say, every government in the region.
Check Point Research documented a dramatic escalation in Iranian camera-hacking operations beginning on February 28 - the same day Israel launched its strikes. The targeting extended across Israel, Qatar, Bahrain, Kuwait, the UAE, Lebanon, and Cyprus. The attacks focused on Hikvision and Dahua cameras using the same set of known vulnerabilities. The pattern, Check Point concluded, was consistent with Iran conducting battle damage assessment - using hacked cameras to evaluate the impact of its own missile strikes on adversary territory.
Both sides were doing the same thing. Both sides had been doing it for years. The difference was that Iran's network was more extensively penetrated, and the intelligence it yielded was more operationally decisive.

Check Point Research documented Iranian camera-hacking activity across seven countries starting February 28 - the same day Israeli strikes began. Camera access is now a standard instrument of modern conflict.
Seloom told AP that Gulf monarchies with highly secured petroleum facilities had known for years they were potential targets - and had locked those systems down accordingly. But the realization that street-level traffic cameras could be weaponized for leadership targeting came too late. "I don't think anyone anticipated that these traffic cameras would become targeting tools," he said. "There is alarm all over."
Across the region, governments have moved to restrict civilian photography and livestreaming near sensitive infrastructure. In some Gulf states, residents have been prohibited from filming near military or government sites. These measures address the surface of a problem that runs much deeper.
Eyal Hulata, Israel's former national security adviser now at the Foundation for the Defense of Democracies, noted that Israel itself operates under constant cyberattack from Iran and has worked to defend against camera compromise on its own networks. "There is high alert on all cyber fronts," he said. The arms race is symmetric. Both sides are trying to hack the other's cameras. One side, as of February 28, did it better.
The broader implication is one that security researchers have been flagging for over a decade: the global proliferation of internet-connected cameras - now estimated at over one billion worldwide, tripling in a decade with hundreds of millions more installed each year - has created an attack surface of almost incomprehensible scale. The cameras sit at every street corner, in every lobby, above every sensitive site. They are connected to public networks. They run outdated firmware. They use default passwords.
They are, in Marrapese's phrase, fish in a barrel.
Iran's Command Structure After the Kill

Tehran and Iran's political landscape have been fundamentally transformed by the assassination of Khamenei and the elimination of much of his senior leadership in the weeks since. (Pexels)
Khamenei's death on February 28 was the opening event in a war that has since consumed the region. His son Mojtaba Khamenei was quickly named supreme leader - but as of this writing, he has not appeared in public. Israeli Prime Minister Benjamin Netanyahu, at a press conference last week, said bluntly: "Mojtaba, the replacement ayatollah, has not shown his face. Have you seen him? We haven't, and we can't vouch for what exactly is happening there."
U.S. and Israeli officials suggest Mojtaba may have been wounded in the same strike that killed his father. His wife was killed in the attack.
With the supreme leader incapacitated or hiding, and a cascade of other senior figures dead - including Ali Larijani, secretary of Iran's Supreme National Security Council, and Revolutionary Guard spokesperson Gen. Ali Mohammad Naeini, killed in an airstrike last week - the question of who is running Iran has become genuinely uncertain.
Ali Vaez, Iran project director at the International Crisis Group, offered the most clear-eyed analysis: "The Revolutionary Guard is the state now." With the elder Khamenei gone and his son lacking the accumulated authority of his father, "it is really the Revolutionary Guards who are running the country."
Iranian Foreign Minister Abbas Araghchi said in early March that military units were effectively acting on pre-set instructions, without real-time central direction: "Our military units are now in fact independent and somehow isolated and they are acting based on instructions - you know, general instructions - given to them in advance." He acknowledged that attacks on neighboring countries like Oman were "not our choice" - a remarkable admission that the military had effectively gone autonomous.
Iran continues to fire missiles, according to Israeli military statements. Saudi Arabia said it downed 20 Iranian drones in a two-hour window late last week, near its eastern oil infrastructure. The Strait of Hormuz remains choked. Oil prices have soared. The U.S. is deploying another 2,500 Marines to the region on top of the 50,000 already there, while Trump simultaneously hints at "winding down" operations.
The war triggered by that February 28 strike - the strike guided, in part, by decades of accumulated camera intelligence - shows no signs of ending.
What Comes Next: The Surveillance Arms Race

The demonstrated effectiveness of AI-powered surveillance exploitation will accelerate an arms race in camera security - and in the offensive capabilities to defeat it. (Pexels)
The strategic lesson of the Khamenei operation will not be lost on the world's authoritarian governments. Surveillance cameras deployed to monitor populations are, simultaneously, a targeting network that can be turned against the regime that built them. The more comprehensive the camera network, the more complete the intelligence product available to any adversary capable of penetrating it.
Several responses are now predictable. Governments will move to isolate their most sensitive surveillance networks from the public internet entirely - relying on physically separate data links, hardware authentication, and air-gapping that genuinely works. They will replace Chinese-manufactured cameras in security-critical locations with domestically produced or verified alternatives. They will establish rapid-patch protocols that ensure firmware updates propagate immediately rather than sitting uninstalled for years.
These measures will help at the margins. They will not solve the structural problem. Any network large enough to provide comprehensive surveillance of a city of 10 million people is too large to secure with perfect consistency. Human operators remain the weakest link. The economics of surveillance - cheap hardware, mass deployment, minimal maintenance budgets - are structurally incompatible with the security practices required to keep the network from being exploited.
Burcu Ozcelik, senior research fellow for Middle East security at the Royal United Services Institute, predicted the change in Iran itself will be gradual and may take years to fully manifest. "The fixation on the terminology of 'regime collapse' is obscuring the fact that the regime is already changing," she told AP. The strikes, the leadership decapitation, the economic pressure of blocked Hormuz shipping - each is transformative. Together they represent a shift whose full consequences are not yet visible.
What is visible is this: the billion cameras watching the world's cities are not neutral infrastructure. They are contested terrain. They are watching - and the question of who is watching the watchers has never been more consequential. Iran's supreme leader found out the hard way.
Sources
AP News: Iran built a vast camera network to control dissent. Israel turned it into a targeting tool (March 24, 2026)AP News: A look at who holds the reins of power in Iran (March 2026)
AP News: Trump hints at wind-down as US sends more troops to Middle East (March 20, 2026)
Check Point Research: Interplay between Iranian Targeting of IP Cameras and Physical Warfare (March 2026)
IPVM / Paul Marrapese: Global unprotected camera map (2026 scan)
International Crisis Group - Ali Vaez, Iran Project Director
Royal United Services Institute - Burcu Ozcelik, Senior Research Fellow
Foundation for the Defense of Democracies - Eyal Hulata, former Israeli National Security Adviser
Doha Institute for Graduate Studies - Muhanad Seloom, Assistant Professor
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram