Bomb and Byte: Iran's Spyware Attacks Are Synchronized With Its Missile Barrages
As Iranians were firing six ballistic missiles and 29 drones at the Prince Sultan Air Base in Saudi Arabia on Friday, their digital proxies were doing something new: sending fake shelter apps to Israeli phones at the exact same minute the real missiles were falling. This is not a sideshow. It is the war's second front.

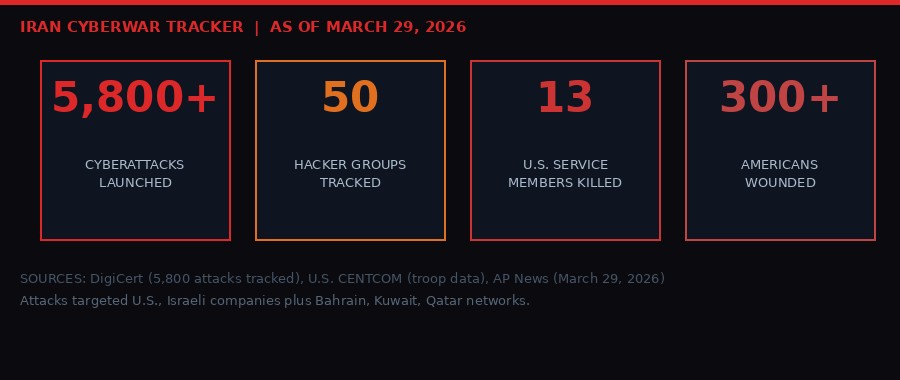
The Iran war turned one month old on Saturday. The casualty numbers are appalling but legible: more than 3,000 dead, 13 U.S. service members killed, over 300 Americans wounded, Iran claiming 1,900 of its own citizens dead, Lebanon's death toll at 1,100 since Israel opened its second front there. These numbers fit the vocabulary of conventional war.
The cyber numbers are harder to see but they tell a different story - one about the shape of modern warfare and what it looks like when a nation-state runs a military campaign on two simultaneous planes, one physical and one digital, each amplifying the damage of the other.
Investigators at DigiCert, the Utah-based cybersecurity firm, have tracked nearly 5,800 cyberattacks mounted by close to 50 different hacker groups tied to Iran since the war began on February 28. The attacks targeted U.S. and Israeli companies but also reached networks in Bahrain, Kuwait, Qatar and other Gulf states hosting American forces. The aim is not just to steal or disrupt - it is to fracture the coalition and install fear at scale across every connected device in the theater.
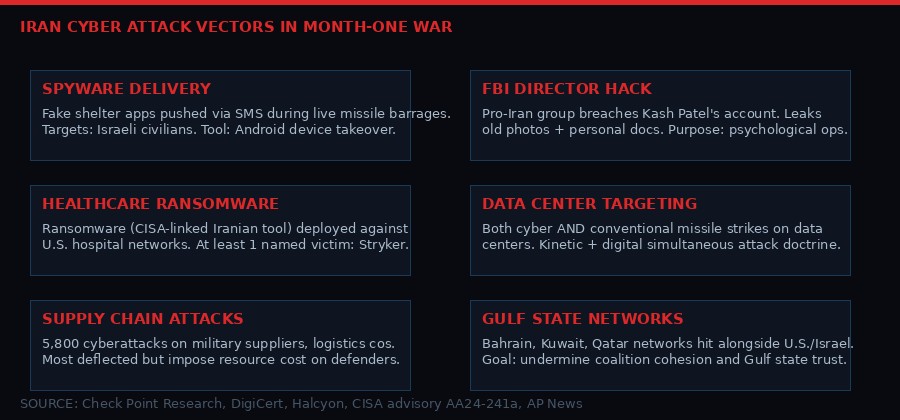
The Synchronized Strike - Spyware Drops as Missiles Fall

The spyware incident stands out even in a conflict already dense with digital attacks. As Israelis with Android phones fled for shelter during a recent Iranian missile strike, some received text messages offering a link to real-time information about bomb shelter locations - the kind of thing people would desperately want in that moment. The link delivered spyware instead. It gave the hackers access to the device's camera, microphone, location data and all stored information.
What made this particular operation notable was the timing. Gil Messing, chief of staff at Check Point Research, the cybersecurity firm with offices in Israel and the United States, confirmed the texts appeared to be sent at the exact moment the missiles were inbound.
"This was sent to people while they were running to shelters to defend themselves. The fact it's synced and at the same minute... is a first." - Gil Messing, Chief of Staff, Check Point Research (AP News, March 29, 2026)
The logic of the synchronized attack is brutal in its clarity. In the moment of maximum physical vulnerability - when people are already scared, already moving, already looking at their phones for information - they are also at maximum psychological susceptibility to clicking a malicious link. The spyware drops in the window between the air raid siren and the all-clear.
The operation required sophisticated coordination between at least two separate teams: one managing the missile launch logistics, one managing the cyber payload deployment. These two operations would have needed to synchronize timing, targets, and the content of the lure. The fact that it worked - that phones were compromised at scale during active missile alerts - signals a level of operational integration that Iran's adversaries had not previously documented.
Iran's cyber capabilities have long been assessed as formidable but asymmetric - good at harassment, disruption and psychological operations, less capable of the kind of precision destructive attacks that could, say, crash a power grid or disable a military network. That assessment may need updating. The question is not whether Iran can destroy Western infrastructure in a single strike. The question is what Iran can do when it runs thousands of low-to-medium intensity attacks continuously for 30 days while simultaneously waging a kinetic war.
5,800 Attacks in 30 Days - What Volume Warfare Looks Like
Most cyberattacks linked to the Iran war have been, as Michael Smith from DigiCert put it, "relatively minor when it comes to damage to economic or military networks." The goal of the majority is not to destroy - it is to impose cost. Every IT team that has to respond to an Iranian phishing campaign is a team not doing something else. Every company that has to patch a vulnerability because hostile actors are probing it is a company spending money and time on defense rather than offense or production.
Michael Smith, DigiCert's field chief technology officer, put it plainly:
"There are a lot more attacks happening that aren't being reported. High-volume, low-impact attacks are a way of telling people in other countries that you can still reach out and touch them even though they're on a different continent. That makes them more of an intimidation tactic." - Michael Smith, Field CTO, DigiCert (AP News, March 29, 2026)
The 5,800 documented attacks from nearly 50 groups in 30 days averages to roughly 193 attacks per day, or about eight per hour around the clock. They hit different sectors - healthcare, defense contractors, logistics companies, financial institutions, government systems. The breadth is deliberate. Iran does not need to penetrate any single target deeply. It needs to force its adversaries to defend everywhere at once, indefinitely.
This is sometimes described as "gray zone warfare" but that framing is increasingly misleading. Gray zone implies ambiguity about whether something constitutes conflict. There is no ambiguity here. Iran is waging an active military campaign on a digital front, coordinated with its kinetic operations, while simultaneously fighting with missiles, drones, and proxy forces on multiple physical fronts. Calling it "gray" undersells what is happening.
Iran's Digital War - Key Figures (Month One)
- 5,800+ cyberattacks documented by DigiCert
- ~50 distinct hacker groups tracked as Iran-aligned
- Targets in U.S., Israel, Bahrain, Kuwait, Qatar, other Gulf states
- Sectors hit: healthcare, defense supply chain, financial, government
- Notable breach: Kash Patel (FBI Director) personal account leaked
- Notable breach: Stryker medical technology (Michigan-based)
- Notable: synchronized spyware deployment during live missile alerts
- Iran also targeting data centers with conventional missile strikes
Stryker, Kash Patel, and the Art of the Splash Attack

Some attacks in the past month stand out not for their technical sophistication but for their symbolic targeting. A pro-Iranian hacking group known as Handala claimed responsibility for breaching Stryker, the Michigan-based medical technology company. The group framed the attack as retaliation for suspected U.S. strikes that killed Iranian schoolchildren. Cybersecurity researchers at Halcyon published findings on the attack - they confirmed Handala used a tool that U.S. authorities have previously linked to Iranian state actors to install destructive ransomware on Stryker's systems.
Medical technology companies occupy a particular place in the risk hierarchy. Stryker makes implants, surgical equipment, and hospital systems used across the United States and allied nations. A successful ransomware attack on a company like that does not just cause financial damage - it can disrupt supply chains for products that people's lives depend on. The choice of target was not random. It was calculated for maximum psychological impact in the U.S. population.
The attack on FBI Director Kash Patel's personal account followed a different logic. A pro-Iran group claimed responsibility, posted what appeared to be years-old photographs of Patel along with a work resume and personal documents. The actual intelligence value of this material appears limited - many of the records were more than a decade old. But the operation served a different purpose: demonstrating that Iran can reach the personal accounts of senior U.S. officials. That message is received not just by its target but by every official watching.
This pattern - high-visibility targets chosen for psychological impact rather than intelligence yield - is consistent with what analysts describe as "intimidation campaign" cyber doctrine. The goal is not necessarily to obtain the FBI Director's files. The goal is to make everyone who hears about the breach wonder whether their own accounts are next, and to signal to decision-makers in Washington that no one in the U.S. government is truly unreachable.
Data Centers Under Simultaneous Kinetic and Digital Fire

One of the most significant doctrinal developments in this war is Iran's coordinated targeting of data centers using both physical weapons and cyberattacks. Analysts tracking the war note that Iran has struck data centers with conventional missiles while simultaneously directing cyber proxies to attack their digital infrastructure. This convergence - treating data centers as unified targets to be hit from both directions at once - is a doctrinal development that most Western militaries have theorized about but not yet encountered at scale.
The reasoning is straightforward once you understand the role data centers now play. Modern warfare depends on communications, logistics software, targeting systems, intelligence processing, and command networks. All of these functions route through data centers. A data center that is taken offline - whether by a missile strike or a ransomware attack or both simultaneously - degrades military capabilities across dozens of dependent systems. Redundancy helps but it does not help uniformly, and the attackers only need to find the weakest redundancy link.
Iran's targeting of the Ras Laffan natural gas facility in Qatar on March 18 demonstrated this logic applied to energy infrastructure. The strike wiped out 17 percent of Qatar's LNG export capacity. QatarEnergy, the state-owned operator, said repairs would take up to five years. The facility was simultaneously subjected to cyber probing - a pattern that security researchers say they have documented at multiple critical infrastructure targets in the Gulf.
Energy infrastructure and data centers are converging as the war's most contested non-battlefield terrain. Iran cannot win a conventional military engagement against the combined U.S.-Israeli air power in the region. It can, and apparently is, attempting to inflict enough economic damage on the coalition and its allies to make continuing the war politically and economically untenable.
The April 6 Deadline, Conflicting Signals, and the Question of What Comes Next

President Trump has set April 6 as the deadline for Iran to reopen the Strait of Hormuz, the strategic waterway through which roughly a fifth of the world's oil normally passes. Iran has effectively closed it since February 28, when the war began. The closure has driven Brent crude from roughly $70 per barrel before the war to $105.32 as of Friday - a 50 percent increase in 30 days. Benchmark U.S. crude hit $99.64.
The International Energy Agency describes this as "the largest supply disruption in the history of the global oil market." Christopher Knittel, an energy economist at the Massachusetts Institute of Technology, said: "Historically, oil price shocks like this have led to global recessions."
Iran has twice watched Trump set and then extend deadlines, and its public posture remains one of defiance. Iranian Foreign Minister Abbas Araghchi has told his Turkish counterpart that Tehran is skeptical of diplomatic efforts and accused the U.S. of "unreasonable demands" and "contradictory actions." Iran's parliament speaker Mohammad Bagher Qalibaf denied Trump's claim that direct talks were underway. An Iranian military spokesman vowed to fight "until complete victory."
Meanwhile, Trump's conflicting signals have sown confusion at every level of the military and diplomatic chain. He has called talks "very well" while his envoy Steve Witkoff delivered a 15-point "action list" that Iran publicly rejected. He has threatened to "obliterate" Iran's energy infrastructure while saying the U.S. is "not affected" by the Hormuz closure - a claim at direct odds with the economic data. He delayed the Hormuz deadline twice while saying he did not know what he would do when asked directly.
"The administration is winging it. So how can you trust what the president says?" - Rep. Gregory Meeks (D-NY), ranking member, House Foreign Affairs Committee (AP News, March 29, 2026)
Republican Rep. Chip Roy of Texas, a Freedom Caucus member who sits on the House Budget Committee, said his constituents were on board with "blowing some crap up" but expressed reservations about ground troops and complained that classified Pentagon briefings revealed only what was already "read in the papers." The administration reportedly needs Congressional approval for an additional $200 billion to sustain the war effort.
An AP-NORC poll this week found that while 63 percent of Republicans back airstrikes against Iranian military targets, only 20 percent support deploying ground troops. The political calculation shifts significantly if ground operations begin - and the deployment of 1,000 soldiers from the 82nd Airborne Division, trained specifically to parachute into contested territory and secure airfields, is not the kind of asset you send to a war you plan to end with airstrikes alone.
War Reaches Month Two - The Full Kill-Chain
The war reached its one-month mark on Saturday with its full architecture visible. Thirteen American service members are dead. The six logistics soldiers of the 103rd Sustainment Command - Sgt. Declan Coady, 20, of Iowa; Sgt. 1st Class Nicole Amor, 39, of Minnesota; Capt. Cody Khork, 35, of Florida; Sgt. 1st Class Noah Tietjens, 42, of Nebraska; Chief Warrant Officer 3 Robert Marzan, 54, of California; and Maj. Jeffrey O'Brien, 45, of Iowa - died in a drone strike on a command post at Port Shuaiba, Kuwait on March 1, the day after the war began. They are the faces of what "no ground troops" looked like at the start.
Since then, the war has spread geographically. Israel has invaded southern Lebanon while targeting Hezbollah, killing more than 1,100 people there. Iranian-backed militia groups in Iraq have entered the fight; 80 Iraqi security force members are dead. In Gulf states, at least 20 civilians have been killed by Iranian strikes. Iran says 1,900 of its own people are dead inside its borders.
Saturday brought the war's next escalation: the Houthis, who had held back for the entire first month of the conflict, entered the fighting. Houthi Brig. Gen. Yahya Saree announced missile launches toward "sensitive Israeli military sites" in southern Israel. The Israeli military confirmed intercepting a Houthi missile fired from Yemen. The prospect of renewed Houthi attacks on Red Sea shipping - through the Bab el-Mandeb Strait, where 12 percent of world trade normally passes - has oil markets and shipping companies recalculating routes that only just settled after the first Houthi campaign in 2024-2025.
The USS Gerald R. Ford, the nation's newest aircraft carrier, arrived in Croatia on Saturday for maintenance after a laundry room fire damaged crew sleeping quarters. Its absence from the region opens a gap in U.S. carrier coverage at exactly the moment the Houthis are re-entering the fight. The USS Tripoli - an amphibious assault ship pulled from exercises near Taiwan - has arrived with 2,500 Marines. At least 1,000 soldiers from the 82nd Airborne are deploying. The U.S. now has the largest force in the Middle East in more than 20 years: two remaining carriers, roughly 50,000 troops, and an ever-expanding list of assets being diverted from other theaters.

The Doctrine Lesson - What War Looks Like Now

For decades, military analysts have debated what "hybrid warfare" really means and whether it represents a genuinely new form of conflict or just a relabeling of what states have always done. The first month of the Iran war has provided an answer in real time.
Iran is running what researchers at Check Point and DigiCert describe as a fully integrated campaign: missiles and spyware timed to the same moment. Data centers hit by both conventional and cyber weapons simultaneously. Healthcare companies ransomed to punish populations politically. High-visibility hacks of senior officials designed to degrade morale and signal reach. All of this running continuously, in parallel with missile barrages, drone strikes, proxy warfare in Iraq, and Hezbollah operations in Lebanon.
James Jeffrey, former U.S. ambassador to Iraq and deputy national security adviser under President George W. Bush, made the point bluntly in an assessment of the war's first month:
"We have not stopped Iran from its campaign against the Gulf. We have not eliminated all of their missiles. And of course, they still have the 400-plus kilograms of highly enriched uranium. It's buried, but still it's there." - James Jeffrey, Washington Institute for Near East Policy (AP News, March 29, 2026)
Jeffrey was speaking about the kinetic war. But his assessment applies equally to the cyber front. The U.S. has struck more than 11,000 Iranian targets in 30 days. It has the largest regional force in two decades. It has two carrier battle groups, two Marine Expeditionary Units, airborne infantry from the 82nd Division. And Iran is still firing.
On the digital plane, the United States and Israel have deflected most of the 5,800 documented attacks. The significant majority of Iranian cyber operations have been "easily thwarted by the latest cybersecurity precautions," according to DigiCert. But "easily thwarted" does not mean "without cost." It means that organizations that have invested in security posture are holding. Organizations that have not - hospitals, small defense contractors, logistics companies operating on aging systems - are losing. And the attacks continue whether the defenders hold or not.
The synchronized spyware drop during the missile barrage was technically novel but strategically logical: it weaponizes the civilian fear that missiles create into a vector for intelligence collection. The missiles make people reach for their phones. The spyware is waiting when they do. Fear becomes the delivery mechanism for surveillance.
This doctrine will outlast this war. Every military watching the Iran conflict is now studying how Iran coordinated its kinetic and digital operations - not to condemn the practice but to replicate it. The attack on Stryker, the targeting of the FBI Director's personal account, the fake shelter apps - these are not improvised acts of desperation. They are documented tactics in a playbook that is now being written in real time under fire. The next adversary to adopt this doctrine will have the benefit of Iran's month-one lessons without the month-one trial and error.
As the war enters its second month with the April 6 Hormuz deadline approaching, Trump's contradictory signals amplifying every uncertainty, the Houthis freshly in the fight, and Qatar's LNG terminal still dark for years to come, the digital front is not a sideshow. It is the front that will persist long after any ceasefire. Cyberattacks do not stop at ceasefires. The spyware already installed on those phones will still be there after the missiles stop falling.
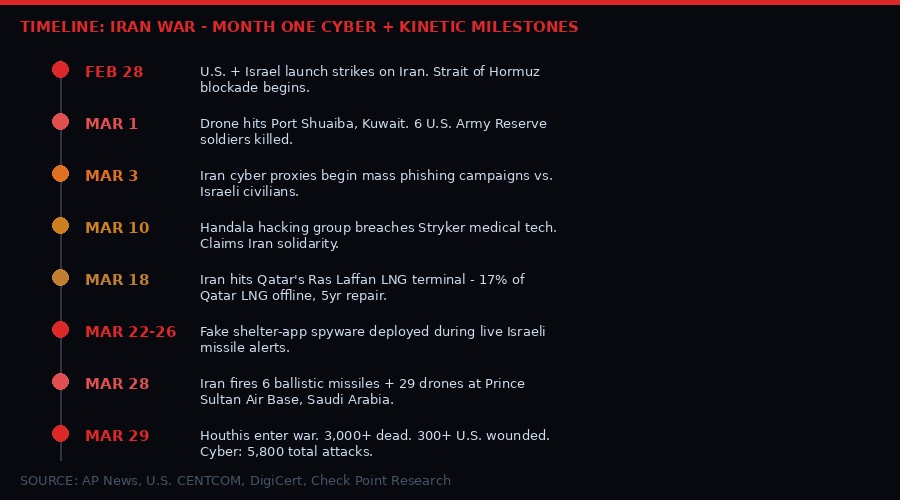
Timeline of Key Events - Month One
Total War Toll - Month One (March 29, 2026)
- Total killed (all parties): 3,000+
- Iranian civilians/military dead: 1,900+ (Iranian state figures)
- Lebanon deaths (Israeli operations, Hezbollah front): 1,100+
- U.S. service members killed: 13
- U.S. service members wounded: 300+ (10 seriously, 30 out of action)
- Iraqi security forces killed (Iranian proxy operations): 80
- Gulf state civilian deaths from Iranian strikes: 20+
- Brent crude price change: $70 to $105.32 (+50%)
- U.S. targets struck in Iran: 11,000+
- Documented Iran cyberattacks: 5,800+
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram