The Kill List: Iran's IRGC Names 18 US Tech Giants as Military Targets Starting Tonight
Apple, Google, Nvidia, Microsoft, Tesla, Meta, Boeing, and eleven more corporations face imminent strikes across the Middle East after Tehran declares Silicon Valley infrastructure fair game in the AI-powered war.

Data centers across the Gulf now sit in the crosshairs of Iranian retaliatory doctrine. Photo: Pexels
Iran's Islamic Revolutionary Guard Corps issued the most explicit threat against American commercial infrastructure in the history of the 32-day war on Tuesday evening, naming 18 US and Gulf-based technology companies as "legitimate military targets" and setting an 8:00 PM Tehran time deadline on April 1 for strikes to begin.
The list reads like a Fortune 500 roll call: Apple, Google, Microsoft, Nvidia, Meta, Tesla, Boeing, Intel, IBM, Dell, Cisco, Oracle, HP, Palantir, General Electric, JPMorgan, and two UAE-based companies - G42 and Spire Solutions. The IRGC simultaneously warned all employees of these companies across the Middle East to "leave their workplaces immediately to save their lives" and instructed civilians living within one kilometer of any facility to evacuate.
This is not bluster from a regime trying to save face. Iran already hit Amazon Web Services data centers in Bahrain and the UAE during the first week of the war - the first deliberate strikes on cloud infrastructure in the history of armed conflict. What changed on March 31 is that Tehran moved from opportunistic strikes to publishing a formal target list, transforming scattered attacks into declared doctrine.
The implications extend far beyond the Middle East. The IRGC threat represents the first time a state actor has publicly classified civilian technology companies as military combatants in an active war. If Tehran follows through, it will redefine the legal, strategic, and economic boundaries between Silicon Valley and the Pentagon permanently.
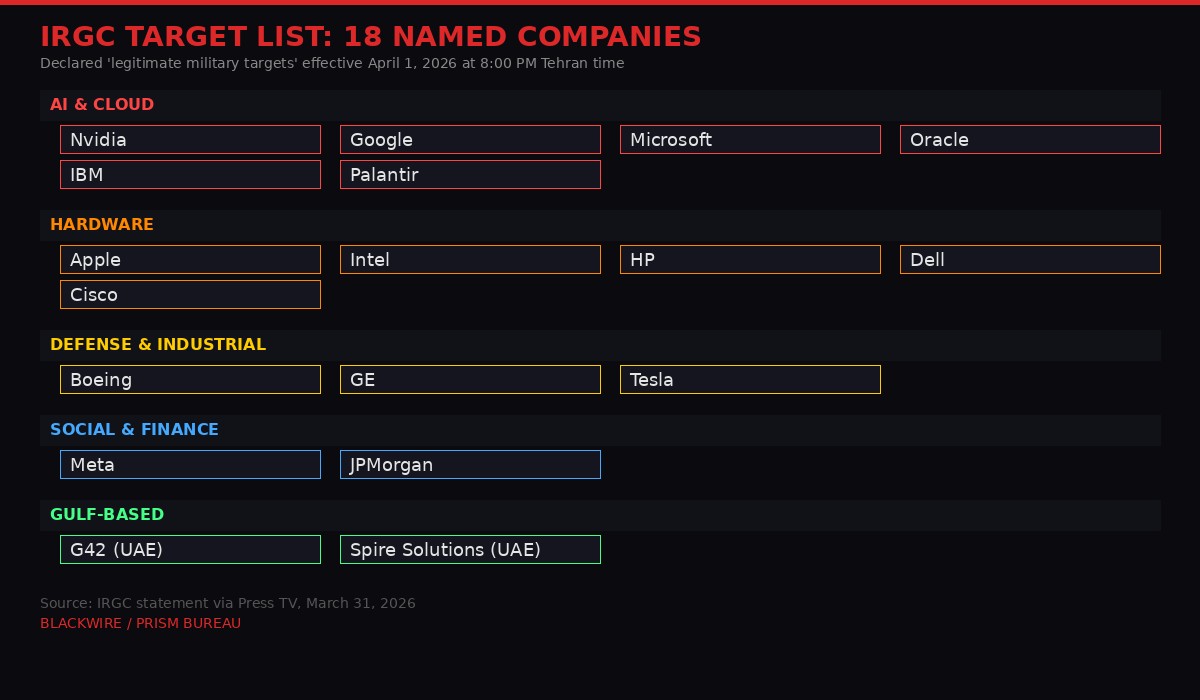
The 18 companies named by the IRGC, categorized by sector. BLACKWIRE/PRISM
The Statement: What the IRGC Actually Said

Tehran frames tech companies as integral nodes in the American kill chain. Photo: Pexels
The IRGC distributed its warning through official channels and state-linked media on March 31, setting an unmistakable deadline. The statement, carried by Iran's Press TV and the Tasnim News Agency, framed the 18 companies not as civilian businesses but as active participants in what Tehran calls "US-Israeli terror operations."
"Since the main element in designing and tracking terror targets are American information and communications technology and AI companies, in response to this terrorist operation, from now on the main institutions effective in terrorist operations will be our legitimate targets."
The language was carefully chosen. By using the phrase "legitimate targets," the IRGC is making a legal argument within the framework of international humanitarian law - claiming that these companies have lost their civilian protection by directly contributing to military operations. Whether that argument holds under the Geneva Conventions is a question international lawyers will debate for years. But the IRGC isn't waiting for a legal opinion.
The statement included operational specifics that set it apart from previous Iranian rhetoric. The April 1 deadline of 8:00 PM Tehran time (4:30 PM GMT, 12:30 PM Eastern) gives the threat a countdown structure typically associated with ultimatums, not propaganda. The one-kilometer evacuation radius suggests Tehran has already identified specific facilities. And the company-by-company listing - rather than a generic threat against "American interests" - indicates a targeting process that has moved well past the conceptual stage.
"We advise employees of these institutions to immediately leave their workplaces to protect their lives. Residents within a one-kilometer radius of these terrorist companies across all countries in the region are also urged to evacuate and move to safe locations."
The inclusion of JPMorgan - the only financial institution on the list - broadens the threat beyond technology into the financial infrastructure that underwrites American military procurement. Boeing and General Electric extend it into aerospace and defense manufacturing. This isn't just an anti-tech manifesto. It's a comprehensive strike list targeting the commercial ecosystem that makes American warfighting possible.
Perhaps most significant: the IRGC included two UAE-based companies - G42 and Spire Solutions - signaling that Gulf states hosting American technology infrastructure will not receive immunity. G42, the Abu Dhabi-based AI company that recently secured a $1.5 billion investment from Microsoft and partnered with the US government on a 5-gigawatt AI data center campus, now finds itself explicitly named as a target by a nation with proven missile and drone reach.
Why Tech Companies: The AI Kill Chain Argument
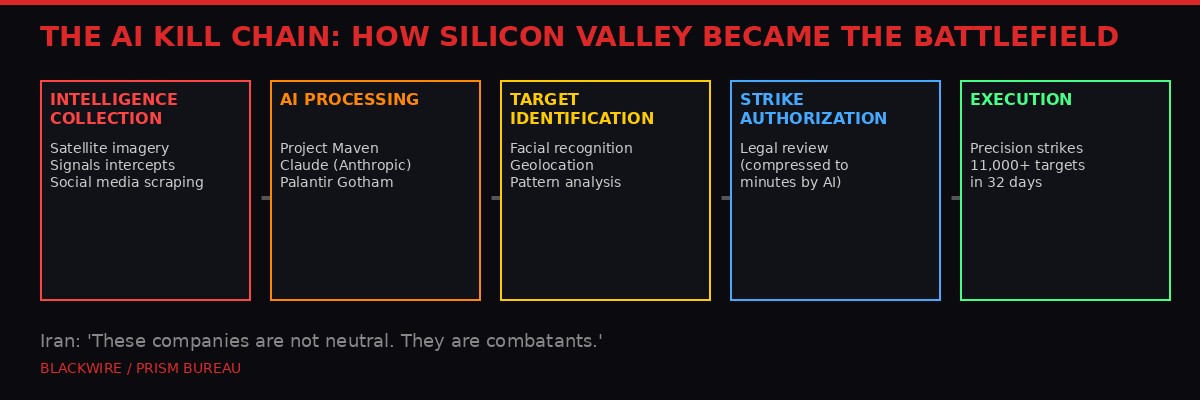
The five-stage AI kill chain that Iran says makes tech companies combatants. BLACKWIRE/PRISM
Iran's targeting rationale isn't arbitrary. It follows a specific logic rooted in how the United States has actually fought this war.
The US military struck over 1,000 targets in the first 24 hours of the campaign against Iran, beginning February 28. That volume was only possible because of artificial intelligence. Project Maven - the Pentagon's AI-powered targeting system, built primarily by Palantir Technologies and incorporating Anthropic's Claude AI model - compressed the traditional "kill chain" from hours or days into minutes. Intelligence collection, data processing, target identification, legal review, and strike authorization were all accelerated by machine learning algorithms running on commercial cloud infrastructure.
As General Brad Cooper, head of US Central Command, publicly stated, the military used AI to "sift through vast amounts of data in seconds" to "make smarter decisions faster than the enemy can react." By day 32 of the war, the Pentagon confirmed it had struck over 11,000 targets in Iran using this AI-assisted process.
Tehran's argument is straightforward: if Palantir's software identifies the target, if Anthropic's Claude processes the intelligence, if Google's cloud runs the computation, if Nvidia's GPUs power the processing, if Intel's chips sit inside the servers, if Cisco's networking routes the data - then these companies are not neutral commercial entities. They are nodes in a weapons system.
This argument gained particular force after the revelation that Anthropic's Claude AI was used in the initial wave of strikes against Iran, even as the company was locked in a bitter dispute with the Pentagon over the terms of military use. The Washington Post reported that the Pentagon demanded the ability to use Claude for "all lawful purposes," while Anthropic pushed back against fully autonomous targeting. That fight became moot when Claude was deployed anyway in the opening hours of the war.
Israel has deepened this dynamic with its own AI targeting platform, reportedly used to track the movements of Iranian officials for assassination. The convergence of American cloud infrastructure, Israeli intelligence systems, and Gulf-hosted server farms has created a unified technological ecosystem that Iran views - not without evidence - as a single integrated military apparatus.
The question of whether this interpretation has legal merit under international law is genuinely contested. Article 52(2) of Additional Protocol I to the Geneva Conventions defines military objectives as objects which "by their nature, location, purpose or use make an effective contribution to military action." If a Google Cloud server in Dubai is running workloads that feed targeting data to Palantir's Maven system, does that server become a military objective? International humanitarian lawyers will argue both sides for decades. Iran has already decided the answer is yes.
The AWS Precedent: What Happened When Iran Hit Data Centers

The AWS strikes in Bahrain and the UAE proved that data center warfare is now operational reality. Photo: Pexels
This isn't hypothetical. Iran already struck Amazon Web Services infrastructure during the first week of the war, establishing what experts at Fortune magazine called "a harbinger of new tactics in future conflicts."
On March 2, Iranian drones hit two AWS facilities in the United Arab Emirates and caused blast damage to a third facility in Bahrain. According to CNBC, the strikes caused "structural damage, power disruptions, and water damage" after firefighters worked to extinguish fires sparked by the drone impacts. AWS confirmed that its Bahrain region experienced "elevated error rates and degraded performance" across multiple services.
The Bahrain facility was specifically targeted. Iran's Fars News Agency stated on Telegram that the data center had been struck "to identify the role of these centers in supporting the enemy's military and intelligence activities." This was a deliberate, publicly acknowledged attack on civilian cloud infrastructure - not collateral damage from a strike on a nearby military installation.
AWS operates three geographic regions in the Middle East: the UAE, Bahrain, and Israel. Each region contains at least three availability zones, with data centers physically separated but connected by ultra-low-latency networks within 100 kilometers of each other. This architecture, designed for redundancy and reliability, also creates a concentrated target set. A coordinated attack on multiple availability zones within a single region could knock out cloud services for thousands of businesses, government agencies, and military operations simultaneously.
The US military uses AWS for a range of classified and unclassified workloads. The CIA's C2S (Commercial Cloud Services) contract with AWS is worth billions. Anthropic's Claude model, which the Pentagon used for targeting in Iran, runs on AWS infrastructure. When Iran hit those Bahrain data centers, it may have - intentionally or not - struck computational infrastructure directly involved in the war being waged against it.
The March 24 follow-up was even more pointed. AWS reported that its Bahrain region was again "disrupted" following renewed drone activity, this time after Iran had explicitly threatened US-linked commercial infrastructure. Al Jazeera reported the disruption came amid "Iran's threats to target US offices and infrastructure run by top US companies." The second strike confirmed that the initial hit wasn't a one-off - it was the beginning of a doctrine.
Fortune's assessment was blunt: the attacks "signal a new kind of war as AI plays an increasingly strategic role." Analysts noted that data centers had never before been deliberately targeted in armed conflict. The practice didn't exist because, until recently, data centers weren't considered military assets. The integration of commercial cloud computing into active warfare changed that calculus overnight.
$100 Billion in the Crosshairs: Gulf Tech Infrastructure
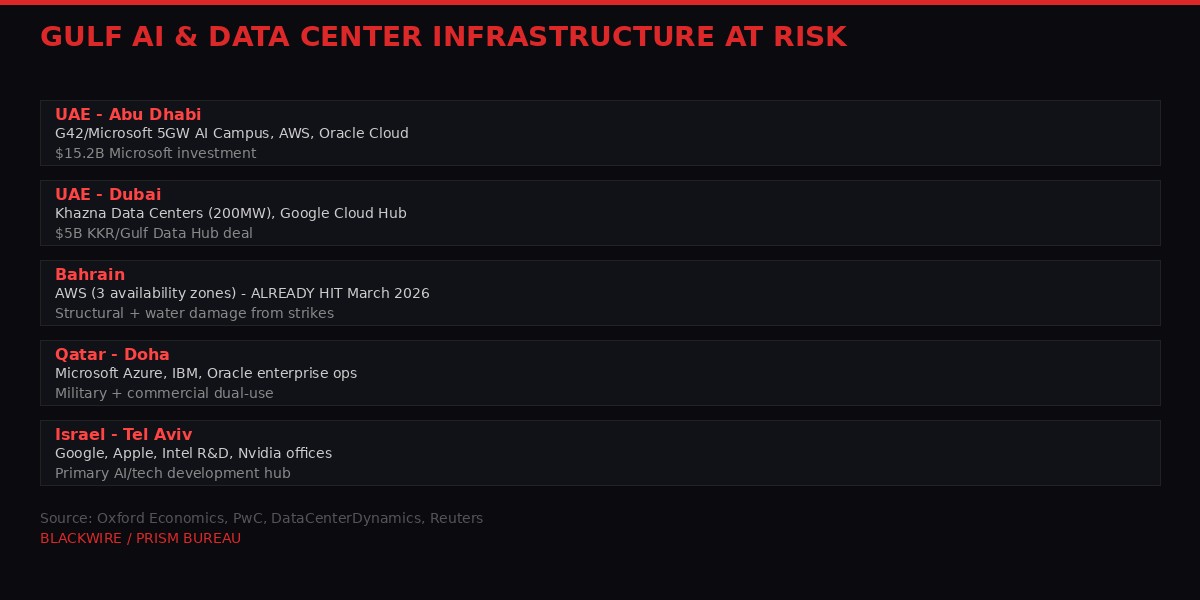
Over $100 billion in planned and operational tech infrastructure sits within Iranian strike range. BLACKWIRE/PRISM
The Gulf states have spent the past decade building themselves into global technology hubs. That ambition now sits directly in the line of fire.
Microsoft announced a $15.2 billion investment in the UAE in November 2025, much of it flowing through its partnership with G42 - the same company now on the IRGC's target list. The deal included massive data center expansion in Abu Dhabi, with new capacity expected to come online before the end of 2026. Microsoft and G42 were also the anchor tenants of a planned 5-gigawatt AI data center campus in Abu Dhabi, announced during a summit between President Trump and UAE President Sheikh Mohamed bin Zayed al-Nahyan in February 2026.
That 10-square-mile campus was supposed to be the crown jewel of Gulf AI ambitions. It would have been the largest AI computing facility in the Middle East, powered by American technology and operated by an Emirati company with deep ties to both Western corporations and Gulf security institutions. Its announcement came just days before the war started. Now its primary operator is named on an Iranian kill list.
The numbers across the region are staggering. KKR committed $5 billion to Gulf Data Hub for data center development. Khazna Data Centers, majority-owned by G42, expanded to 200 megawatts serving hyperscalers. Mubadala, the Abu Dhabi sovereign wealth fund, has a $250 billion portfolio with heavy technology exposure. Oxford Economics estimates that Gulf cities have collectively planned over $100 billion in AI infrastructure investment through 2030.
Dubai, Abu Dhabi, Doha, and Manama have positioned themselves as essential nodes for cloud computing, AI development, and cybersecurity connecting Europe, Asia, and the Middle East. Google, Microsoft, Oracle, and IBM all maintain substantial enterprise operations in the Gulf. Nvidia and Intel technologies are embedded throughout the region's AI initiatives, surveillance architectures, and defense projects.
All of that infrastructure now sits within range of Iranian ballistic missiles, cruise missiles, and the drone swarms that have already proven capable of hitting specific buildings. The Shahab-3 has a range of approximately 2,000 kilometers - more than enough to reach any facility in the UAE, Bahrain, Qatar, or Kuwait from launch sites in western Iran. The newer Khorramshahr-4 (Khaibar) missile extends that range even further.
Insurance markets are already reacting. War risk premiums for Gulf commercial properties have spiked since the conflict began, and the explicit naming of specific companies will force corporate risk departments to reassess their entire Middle Eastern footprint. Companies that spent years building regional headquarters, research labs, and server farms now face the possibility that those investments could be physically destroyed as acts of war.
The economic second-order effects are equally severe. If a coordinated strike disrupts cloud services in the Gulf, the impact cascades instantly through banking systems, telecommunications networks, aviation infrastructure, and government services across the entire region. The Gulf's digital economy doesn't exist in isolation - it's a chokepoint for data flows connecting three continents.
The Electromagnetic Weapon Claim

Iran claims it possesses electromagnetic weapons capable of disabling entire city power grids. Photo: Pexels
Buried within the escalating rhetoric, a former senior IRGC commander made a claim that caught the attention of defense analysts worldwide.
Hossein Kanani Moghaddam, a former high-ranking IRGC commander, appeared on Iranian state television on March 31 and stated that Iran possesses "electromagnetic weapons capable of disabling an entire city's power and electronic systems without harming civilians."
"There are still many surprises ahead, things the Americans and Israelis have yet to face. For example, we possess electromagnetic weapons, capable of disabling an entire city's power and electronic systems without harming civilians. That's why we have no concern about the war continuing or becoming prolonged."
Electromagnetic pulse (EMP) weapons, if functional, would represent a category of threat uniquely devastating to data centers and technology infrastructure. Unlike kinetic strikes that damage specific buildings, an EMP burst can destroy electronic circuits across a wide area, potentially bricking servers, networking equipment, storage arrays, and power management systems simultaneously. A single EMP detonation over Abu Dhabi could theoretically disable every data center in the emirate without physically destroying a single building.
The claim should be treated with significant skepticism. Weaponized EMP devices capable of city-scale disruption have historically required nuclear detonation at high altitude - something Iran has repeatedly denied pursuing. Non-nuclear EMP weapons (known as high-power microwave or HPM devices) do exist but typically have limited range, measured in hundreds of meters rather than kilometers. Russia and China have both invested in tactical HPM weapons, but no country has publicly demonstrated a city-scale non-nuclear EMP capability.
That said, Iran doesn't need city-scale EMP weapons to be dangerous to data centers. Targeted electromagnetic interference, combined with conventional drone strikes on power substations feeding data center campuses, could achieve functionally similar results. Data centers depend on stable power, cooling systems, and network connectivity. Disrupting any one of these can cause cascading failures. Iran has already demonstrated it can hit specific buildings with precision drones - adding electromagnetic disruption to the toolkit would multiply the damage.
Moghaddam's statement may also serve a deterrent purpose regardless of its truth. If Gulf-based technology companies believe their infrastructure faces both kinetic and electromagnetic threats, the calculus around maintaining Middle Eastern operations shifts dramatically. Even the perception of EMP capability forces defensive investments in hardening, shielding, and redundancy that run into hundreds of millions of dollars.
Project Maven: The Ghost in the Machine

Project Maven - the AI targeting system at the center of Iran's accusation against US tech companies. Photo: Pexels
At the center of Iran's argument - and the reason these specific companies appear on the list - is Project Maven, the Pentagon's AI-powered intelligence system that has become the backbone of targeting operations in the Iran war.
Project Maven began in 2017 as a modest initiative to use machine learning for analyzing drone surveillance footage. Google was the original contractor. When Google employees discovered the military application and organized a mass protest, the company withdrew in 2018, and the contract migrated to Palantir Technologies. Since then, Maven has evolved from an image-recognition tool into a comprehensive intelligence fusion platform that integrates satellite imagery, signals intelligence, human intelligence, social media analysis, and real-time sensor data into a unified targeting picture.
The system's role in the Iran war is unprecedented in scale. Democracy Now reported that the Pentagon used Maven to "speed up the process of identifying targets," enabling the military to strike over 11,000 targets in 32 days - a pace of operations that would be physically impossible without AI assistance. General Cooper's statement about processing data "faster than the enemy can react" reflects Maven's core capability: compressing the observe-orient-decide-act (OODA) loop from the human timescale of hours to the machine timescale of seconds.
Anthropic's Claude plays a critical role within this ecosystem. CBS News reported that Claude is being used for intelligence analysis and target development, despite Anthropic's public objections to fully autonomous military applications. The company reportedly pushed back against the Pentagon's demand to use Claude for "all lawful purposes," arguing that its acceptable use policy should limit military applications. The Pentagon responded by threatening to terminate the contract entirely. In practice, Claude was deployed in the opening hours of the war regardless of the unresolved dispute.
The supply chain behind Maven touches virtually every company on the IRGC's list. Palantir provides the core software platform. Anthropic provides the large language model. AWS provides the cloud infrastructure. Nvidia GPUs power the AI computation. Intel and AMD chips sit inside the servers. Cisco and Dell provide networking and hardware. Oracle provides database infrastructure. Microsoft's Azure hosts additional military workloads. Google Cloud, despite Google's 2018 withdrawal from Maven specifically, still provides commercial services used by defense contractors who feed the Maven pipeline.
Iran's position - that this supply chain makes every participant a legitimate target - is legally aggressive but not intellectually incoherent. The challenge for the companies named is that they cannot easily argue they have no connection to military operations. The connections are documented, public, and in several cases proudly advertised. Palantir CEO Alex Karp has openly boasted about his company's role in the war. Anthropic's military contracts are a matter of public record. AWS's relationship with the intelligence community is defined by billion-dollar contracts.
The second-order implications for the technology industry are severe. If being part of the Pentagon's supply chain makes a company a target in wartime, every defense contract becomes a strategic risk calculation. Companies will face pressure from shareholders, employees, and insurers to disclose their military relationships and assess the physical security implications of those relationships for their global operations.
The Casualty Count and Strategic Context

32 days of war: at least 1,937 killed in Iran, 13 American soldiers dead, and the Strait of Hormuz shut. Photo: Pexels
The IRGC's escalation comes at a specific moment in the war's trajectory. By March 31 - day 32 - the conflict had settled into a grinding pattern that neither side expected.
According to Al Jazeera's tracking, at least 1,937 people have been killed and 24,800 injured in Iran since the war began on February 28. Thirteen American soldiers have been killed with at least 200 wounded. In Lebanon, where Israel is conducting concurrent operations, 1,238 people have been killed and 3,543 injured. Twenty Israelis have been killed and 6,008 injured.
The war has failed to follow the script Washington wrote for it. President Trump and Defense Secretary Pete Hegseth initially framed the campaign as a rapid, overwhelming operation that would decapitate Iranian military and political leadership and force capitulation. The assassination of Supreme Leader Ayatollah Ali Khamenei was presented as the decisive blow. Trump declared victory and began planning a national address.
But Khamenei's death didn't end the war. His son, widely described as more radical than his father, assumed control. The IRGC remained operationally intact. Iranian missile and drone capabilities continued to function. And crucially, Iran maintained its blockade of the Strait of Hormuz - the chokepoint through which roughly 20% of the world's oil supply flows. Oil prices have already pushed past $4 per gallon in the United States, with no sign of relief.
Former IRGC commander Moghaddam's televised assessment was pointed: "The American strategy was clearly to carry out a rapid operation, achieve their objectives quickly, declare victory and exit. But that strategy simply did not work against Iran." Whether or not Moghaddam is correct about Iran's ultimate strategic position, his characterization of American expectations is accurate. The war was supposed to be over by now.
The tech company threat fits within this strategic context. Tehran is escalating horizontally - expanding the war's footprint into domains where it can impose costs on the United States without matching American firepower directly. Closing the Strait of Hormuz attacks America's energy supply. Targeting data centers attacks America's technological infrastructure. Threatening evacuations of US corporate facilities attacks America's economic presence in the Gulf. Each escalation is designed to make the war more expensive than Washington anticipated, creating pressure for negotiation or withdrawal.
The parallel with the Vietnam-era strategy of making war politically and economically unsustainable is unmistakable. Iran cannot win a conventional military engagement with the United States. But it can make every day of the war cost more - in dollars, in disrupted services, in corporate losses, in political capital - than the day before.
Corporate Responses and Market Impact

Markets face a new category of risk: state-sponsored kinetic attacks on tech company infrastructure. Photo: Pexels
As of early April 1, most of the 18 named companies had not issued public statements in response to the IRGC's threat. The silence itself is significant - corporate communications teams are clearly scrambling to determine whether a public response would escalate or de-escalate the situation.
Several companies have reportedly begun internal security reviews of their Middle Eastern operations. Sources familiar with the matter told Politico that some firms had already begun relocating non-essential personnel from Gulf offices before the IRGC's latest statement, based on earlier warnings in March. The explicit naming of companies and the countdown deadline accelerated those processes.
The market implications are multi-layered. Direct exposure comes from physical assets at risk - data centers, offices, R&D facilities, and manufacturing operations throughout the Gulf and Israel. Apple's extensive operations in Israel, Google's cloud infrastructure in multiple Gulf states, Microsoft's $15.2 billion UAE investment, and Nvidia's role in Gulf AI initiatives all represent billions in physical assets within Iranian missile range.
Indirect exposure comes from service disruption. If Iranian strikes knock out cloud services in the Gulf, every business that depends on those services - from regional banks to airlines to government agencies - suffers cascading failures. The March AWS outages provided a preview: even limited disruption caused elevated error rates across multiple services, affecting customers who had no direct connection to the conflict.
Insurance is the third layer. War risk exclusions in commercial property insurance are standard, but few companies anticipated that their data centers in Abu Dhabi or their R&D labs in Tel Aviv would become targets of state-sponsored military strikes. Reinsurance markets will reprice Gulf technology infrastructure risk immediately, and those costs will flow through to every company operating in the region.
The longer-term strategic question is whether the IRGC's threat accelerates a geographic diversification of critical technology infrastructure away from the Gulf. Companies that concentrated data center capacity in the UAE and Bahrain for their strategic location between Europe and Asia may now conclude that strategic location also means strategic vulnerability. India, Singapore, and Indonesia could benefit as alternative hosting locations, though none can replicate the Gulf's unique combination of sovereign wealth funding, favorable regulations, and geographic positioning.
What Happens at 8:00 PM Tehran Time
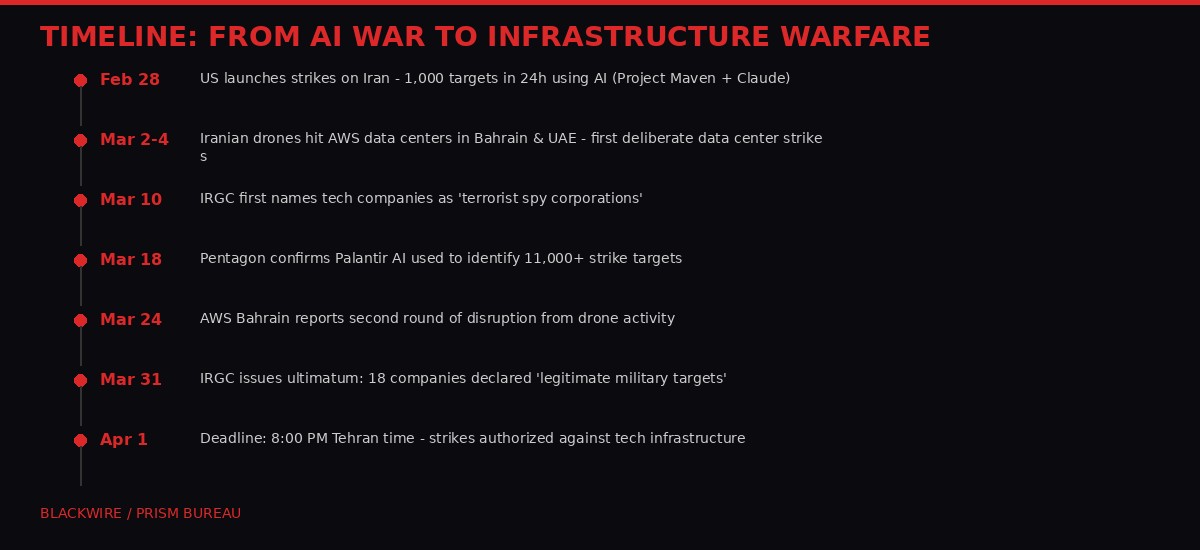
32 days of escalation: from AI-powered strikes to declared infrastructure warfare. BLACKWIRE/PRISM
The IRGC set its deadline for 8:00 PM Tehran time on April 1 - 4:30 PM GMT, 12:30 PM Eastern, 10:00 PM IST. What follows that deadline is genuinely uncertain.
Three scenarios dominate analyst assessments. The first: Iran follows through with strikes on one or more named companies' facilities, most likely data centers or office buildings in the UAE or Bahrain. This would represent a massive escalation but would be consistent with the precedent set by the March AWS strikes. Iran has demonstrated both the capability and the willingness to hit data centers. Doing so again, after a public ultimatum, would be the logical next step in an escalation ladder that has shown no signs of reversing.
The second scenario: Iran conducts cyberattacks rather than kinetic strikes against the named companies. The IRGC has significant cyber capabilities, and an attack on corporate networks would be devastating without creating the same escalatory pressure as a missile strike on a building. A coordinated cyber operation against all 18 companies simultaneously would be unprecedented in scale but would avoid the geopolitical consequences of physically destroying infrastructure in allied nations like the UAE or Bahrain.
The third scenario: the deadline passes without immediate action, and the threat functions primarily as a deterrent and political message. In this reading, the IRGC is establishing a framework for future retaliation rather than committing to immediate strikes. The target list becomes a standing threat - a permanent Damocles sword over American commercial operations in the Gulf - without requiring execution on a specific timetable.
None of these scenarios are mutually exclusive. Iran could conduct limited kinetic strikes on one facility, launch cyberattacks against several companies, and maintain the broader threat framework simultaneously. The March AWS strikes followed exactly this pattern - limited physical damage combined with ongoing disruption and a persistent threat posture.
What is clear is that the boundary between civilian technology infrastructure and military targets has been permanently redrawn. Whether or not strikes occur tonight, the IRGC's declaration establishes a precedent that will shape how nations think about the relationship between commercial technology companies and military operations for decades. The companies on the list can no longer claim neutrality. Their governments can no longer guarantee their safety. And their investors can no longer ignore the possibility that a server farm is also a target.
The AI that shortened the kill chain has now shortened the distance between Silicon Valley and the battlefield to zero.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram