The Trojan Package: North Korea Hijacked Axios and Infected Millions of Developers in Three Hours
A state-sponsored hacking group compromised the most popular HTTP library in the JavaScript ecosystem, turning a routine npm install into a backdoor to Pyongyang. The window was short. The blast radius is still expanding.

A monitor displays system code - the same kind of environment where the Axios compromise silently executed. Photo: Pexels
Sometime around midnight UTC on March 31, 2026, while most of the Western world slept, a North Korean hacker executed one of the most precise software supply chain attacks in recent memory. The target: Axios, the single most downloaded HTTP client library in the JavaScript ecosystem, pulled from the npm registry over 100 million times every week. The weapon: a postinstall hook that silently deployed a cross-platform remote access trojan called WAVESHAPER.V2 onto any machine that ran npm install during a roughly three-hour window.
By the time security researchers at StepSecurity flagged the anomaly and npm yanked the compromised versions, the malicious code had been live for approximately two hours and 53 minutes. That is not a long time. But when your package gets pulled 100 million times a week - roughly 14 million times a day, or about 600,000 times an hour - even a brief window of exposure translates to a potentially staggering number of infections.
Google's Threat Intelligence Group (GTIG) attributed the attack to UNC1069, a financially motivated North Korean threat cluster that has been operating since at least 2018. "North Korean hackers have deep experience with supply chain attacks, which they've historically used to steal cryptocurrency," said John Hultquist, GTIG's chief analyst. "The full breadth of this incident is still unclear, but given the popularity of the compromised package, we expect it will have far reaching impacts."
The quote from security researcher Max Hegel, published by Reuters, captures the essence of why supply chain attacks are so terrifying: "You don't have to click anything or make a mistake. The software you already trust did it for you."
How the Attack Worked: Anatomy of a Postinstall Weapon

The attack exploited automated build processes that run silently in developer environments. Photo: Pexels
The technical mechanics of this attack are elegant in their simplicity. The attacker first compromised the npm account of one of Axios's primary maintainers. According to Google's analysis, the attacker changed the associated email address on the account to an attacker-controlled address at ifstap@proton.me, effectively locking the legitimate maintainer out while gaining full publishing rights to the package.
With control of the account, the attacker introduced a malicious dependency called plain-crypto-js (version 4.2.1) into two Axios releases: version 1.14.1 and version 0.30.4. The name was deliberately chosen to look like a legitimate cryptography utility - the kind of dependency that wouldn't raise immediate red flags during a casual code review.
The payload delivery mechanism abused npm's postinstall hook - a feature that allows packages to automatically execute scripts after installation. This is a legitimate feature used by thousands of packages for tasks like compiling native modules or setting up configuration files. In this case, the postinstall hook triggered a file called setup.js, which served as the first-stage dropper.
The dropper was heavily obfuscated using custom XOR and Base64 encoding routines. It dynamically loaded Node.js core modules - fs, os, and execSync - to avoid static analysis detection. The script then fingerprinted the host operating system and deployed platform-specific payloads tailored for Windows, macOS, and Linux.
This is the critical detail that sets this attack apart from typical npm-based malware campaigns, which tend to target a single platform. UNC1069 built a cross-platform arsenal. Whether the developer was running a MacBook Pro, a Windows workstation, or a Linux server in a CI/CD pipeline, the malware had a payload ready.
On Windows, the dropper copied the legitimate powershell.exe binary to %PROGRAMDATA%\wt.exe - disguising it as Windows Terminal - then downloaded and executed a PowerShell script with hidden execution and bypassed execution policies. On macOS, it dropped a Mach-O binary to /Library/Caches/com.apple.act.mond, a path designed to look like an Apple system daemon. On Linux, it deposited a Python-based backdoor to /tmp/ld.py.
After delivering the payload, the dropper attempted to clean up after itself - deleting the setup.js file and reverting the modified package.json to its original state by renaming a pre-staged backup file called package.md. This self-destructing behavior shows operational sophistication. The attackers wanted the infection to survive while the evidence disappeared.
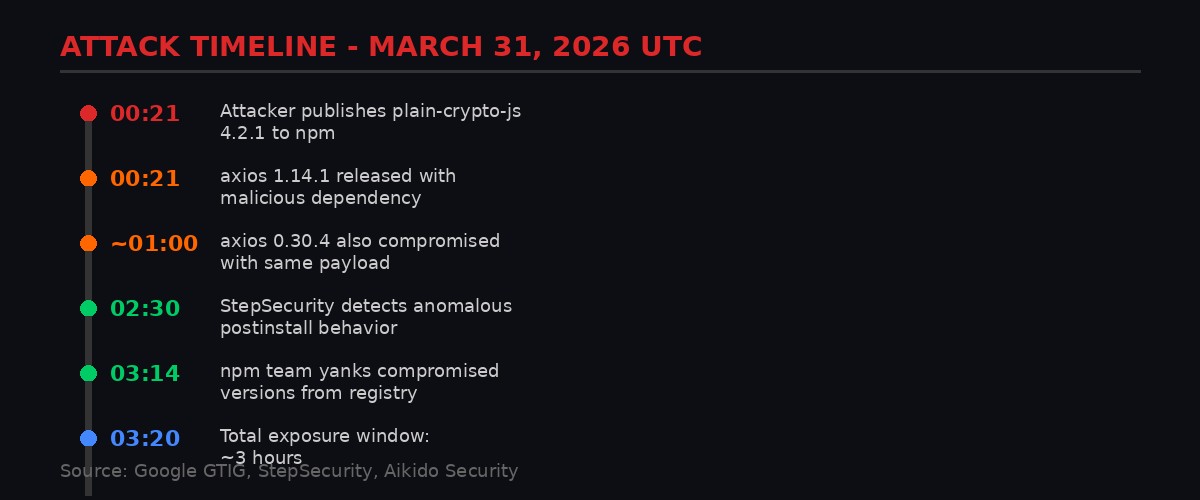
Timeline of the Axios supply chain compromise. Graphic: BLACKWIRE
WAVESHAPER.V2: A State-Grade Backdoor Hidden in a Package Manager

Server infrastructure of the kind targeted by WAVESHAPER.V2's reconnaissance capabilities. Photo: Pexels
The second-stage payloads all deploy variants of what Google tracks as WAVESHAPER.V2, a direct evolution of the original WAVESHAPER backdoor that GTIG has previously attributed to UNC1069. The upgrade is significant. While the original WAVESHAPER used a lightweight raw binary protocol for command-and-control communication, WAVESHAPER.V2 uses JSON-structured beacons, collects substantially more system information, and supports a wider range of remote commands.
Once installed, WAVESHAPER.V2 beacons to its command-and-control server at sfrclak[.]com on port 8000 every 60 seconds. The beacons consist of Base64-encoded JSON data and use a deliberately antiquated User-Agent string - mozilla/4.0 (compatible; msie 8.0; windows nt 5.1; trident/4.0) - which mimics Internet Explorer 8 on Windows XP. This choice is likely both an evasion technique (some security tools deprioritize ancient browser strings) and a signature that helps the operators filter their own traffic.
The backdoor's command set reveals its operational purpose. The kill command terminates the malware's process - useful for avoiding detection when operators decide a target isn't worth pursuing. The rundir command retrieves detailed directory listings including file paths, sizes, and creation timestamps - the kind of reconnaissance you'd run before deciding what to steal. The runscript command executes arbitrary AppleScript payloads on macOS. And the peinject command decodes and injects arbitrary binary payloads into memory on Windows - a technique that allows the operators to deploy additional tools without touching disk.
The reconnaissance phase alone is aggressive. WAVESHAPER.V2 extracts hostname, username, boot time, timezone, OS version, and detailed running process lists. On Windows, it also enumerates running services and scheduled tasks. This telemetry gives operators enough information to decide within minutes whether a compromised machine belongs to someone worth targeting further - say, a developer at a cryptocurrency exchange or a DevOps engineer with production access keys.
Persistence mechanisms vary by platform. On Windows, the malware creates a hidden batch file at %PROGRAMDATA%\system.bat and adds a registry entry named MicrosoftUpdate to the HKCU\Software\Microsoft\Windows\CurrentVersion\Run key, ensuring it launches at every logon. On macOS, the binary's placement in /Library/Caches/ with a name mimicking Apple's own daemons means it would survive casual inspection by all but the most security-conscious users.
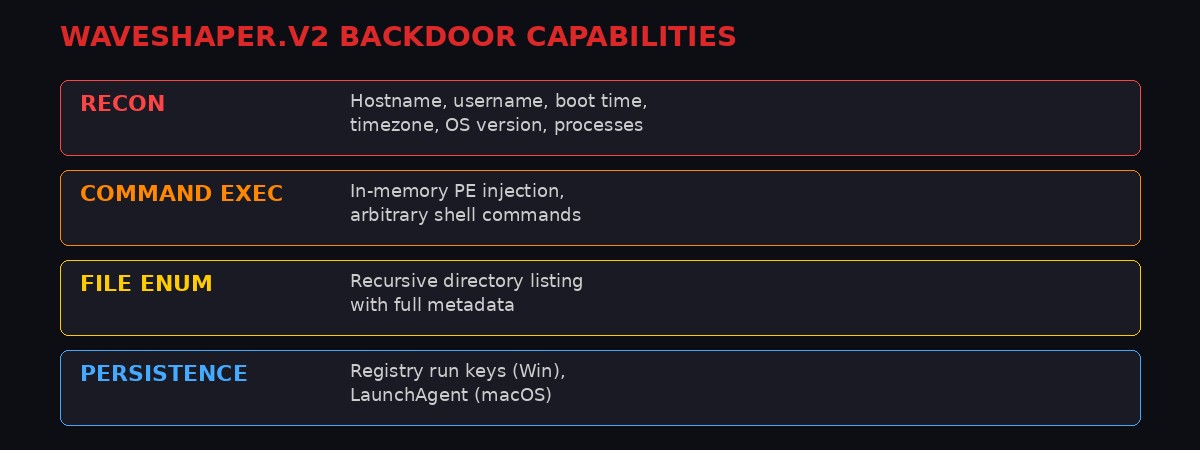
The four core capability categories of the WAVESHAPER.V2 backdoor. Graphic: BLACKWIRE
UNC1069: The Cyber Arm of Pyongyang's Treasury

North Korean threat actors have evolved from targeting individual organizations to poisoning the software supply chain itself. Photo: Pexels
UNC1069 is not a new player. Google's Threat Intelligence Group has tracked the cluster since at least 2018. In a February 2026 report, GTIG documented how the group had expanded its toolkit to include seven unique malware families - SILENCELIFT, DEEPBREATH, CHROMEPUSH, and others - while simultaneously embracing AI-generated social engineering lures to target employees at cryptocurrency firms and financial technology companies.
The group sits within a broader constellation of North Korean cyber operations that Western intelligence agencies have spent years mapping. The umbrella is vast: Lazarus Group (also tracked as APT38 or TraderTraitor by the FBI) remains the most publicly known, but UNC1069 operates alongside BlueNoroff, Andariel, and multiple other clusters that sometimes share infrastructure, tooling, and operational objectives. Elastic Security Labs noted that the macOS binary delivered in the Axios attack contained an internal project name - macWebT - that links directly to BlueNoroff's documented webT module from their RustBucket malware campaigns, suggesting either shared development resources or direct organizational overlap between the two clusters.
Attribution in this case rests on multiple technical pillars. The C2 domain sfrclak[.]com resolves to 142.11.206.73, and GTIG's infrastructure analysis revealed connections from a specific AstrillVPN node that UNC1069 has used in previous operations. AstrillVPN is a VPN service that North Korean operators have historically favored due to its acceptance of cryptocurrency payments and its infrastructure distribution across jurisdictions that don't cooperate readily with Western law enforcement. Adjacent infrastructure hosted on the same autonomous system number (ASN) has been linked to prior UNC1069 campaigns.
The financial motive is straightforward. North Korea's cyber operations have become one of the regime's primary revenue sources, rivaling and possibly exceeding traditional sanctions-evasion methods like coal exports and illicit arms sales. According to Chainalysis data cited by The Hacker News, North Korean threat actors stole approximately $2.02 billion in cryptocurrency during 2025 alone, bringing the cumulative lower-bound estimate to $6.75 billion since 2017. The single largest haul was the February 2025 Bybit exchange hack, which netted $1.5 billion in Ethereum - the biggest cryptocurrency theft in history, confirmed by the FBI as a Lazarus Group operation.
The Axios attack represents an evolution in this strategy. Rather than targeting individual exchanges or DeFi protocols, UNC1069 is now poisoning the tools that developers across the entire technology industry rely on. The thinking is clear: compromise enough developer machines and you will inevitably land inside organizations that handle cryptocurrency, maintain cloud infrastructure, or manage sensitive API keys. It's a volume play with strategic precision.
The Blast Radius: What 183 Million Weekly Downloads Actually Means

The interconnected nature of modern software dependencies means one compromised package can cascade across thousands of organizations. Photo: Pexels
Axios isn't just popular. It's foundational. The library simplifies HTTP requests in JavaScript, and it's used by virtually every significant Node.js application framework, countless React and Vue.js frontend projects, and a vast number of backend services. Combined, the two compromised version branches - 1.x and 0.x - account for approximately 183 million weekly downloads from the npm registry.
But raw download numbers overstate the immediate impact in one important way: not every download during the three-hour window would have pulled the compromised versions. Many organizations use private npm registries, cached dependencies, or pinned lockfiles that would have shielded them from the malicious update. CI/CD pipelines that run npm ci (which installs from the lockfile) rather than npm install (which resolves latest versions) would also have been protected.
The problem is that an unknowable number of developers, organizations, and automated systems don't follow these best practices. A developer who ran npm install axios fresh during that window would have pulled version 1.14.1 by default. A CI/CD pipeline configured with a loose semver range like ^1.14.0 would have automatically resolved to 1.14.1. A Docker build that doesn't pin dependencies would have pulled the compromised version.
Security firm Aikido, which published one of the earliest analyses of the incident, was blunt in its assessment: anyone who downloaded the compromised versions "should assume their system is compromised." Tenable's advisory was equally direct, warning that "any environment that downloaded these compromised Axios versions is at risk of severe data theft, including the loss of credentials and API keys."
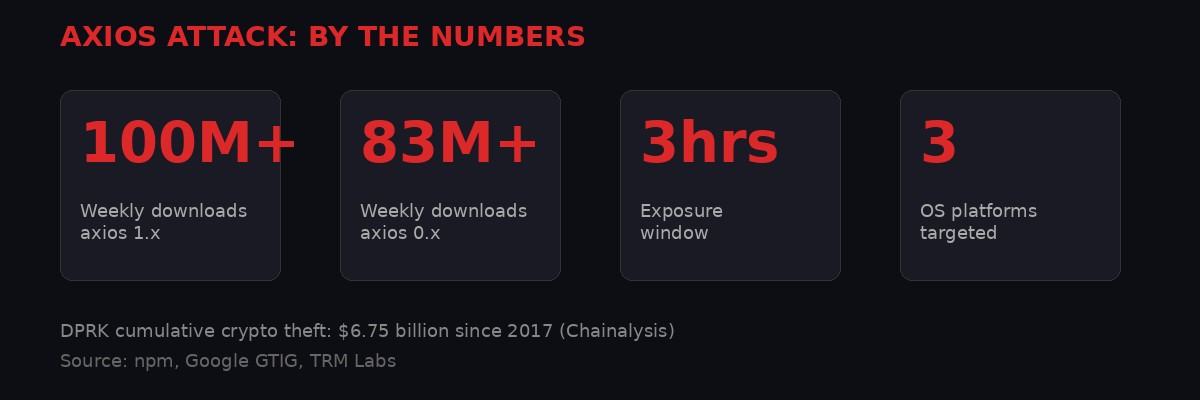
Key statistics from the Axios supply chain compromise. Graphic: BLACKWIRE
The ripple effects extend far beyond direct installations. Axios is a dependency of many other popular npm packages. If any of those packages published updates during the window that resolved to the compromised Axios version, their users would have been affected too - a cascade effect that is the hallmark of supply chain attacks. Google's own advisory acknowledged this: "The impact of this attack by North Korea-nexus actors is broad and has ripple effects as other popular packages rely on axios as a dependency."
The worst-case scenario is credential theft. If WAVESHAPER.V2 was deployed in a CI/CD pipeline that had access to production secrets - AWS keys, database credentials, API tokens for third-party services - those credentials should be considered compromised. Rotating credentials is a massive operational undertaking for any organization, and the scale of this attack means that hundreds or thousands of companies may need to do it simultaneously.
The Bigger Pattern: Open Source is Under Siege

The open-source software ecosystem faces a systemic trust crisis as state actors weaponize package managers. Photo: Pexels
The Axios compromise doesn't exist in isolation. It's part of an accelerating pattern of attacks targeting the open-source software supply chain that has been building for years and reached what feels like a breaking point in 2026.
Google's own advisory noted that UNC1069 isn't the only threat actor actively poisoning the well. Another group, tracked as UNC6780 (also known as TeamPCP), recently compromised GitHub Actions workflows and PyPI packages associated with Trivy, Checkmarx, and LiteLLM to deploy the SANDCLOCK credential stealer. That attack facilitated follow-on extortion operations. "Hundreds of thousands of stolen secrets could potentially be circulating as a result of these recent attacks," GTIG warned.
The timeline of major supply chain attacks tells a story of escalating ambition and diminishing detection windows:
SolarWinds (2020): Russian intelligence operatives compromised the Orion network monitoring platform's build system, injecting the SUNBURST backdoor into updates delivered to approximately 18,000 organizations, including multiple US federal agencies. The attack went undetected for roughly nine months. (Source: SolarWinds SEC filings, FireEye/Mandiant)
3CX (2023): North Korean hackers compromised the 3CX VoIP desktop application, which was used by over 600,000 organizations globally. The attack was itself a supply chain cascade - 3CX was compromised through a previously compromised version of the X_TRADER financial trading application. Detection took approximately four weeks. (Source: CrowdStrike, Mandiant)
Polyfill.io (2024): A Chinese company acquired the popular JavaScript CDN service and injected malicious redirects affecting over 100,000 websites. The attack was active for approximately three months before researchers at Sansec flagged it. (Source: Sansec, Cloudflare)
Axios NPM (2026): North Korean hackers compromised a package with 183 million weekly downloads. Detection took approximately three hours. (Source: Google GTIG, StepSecurity)
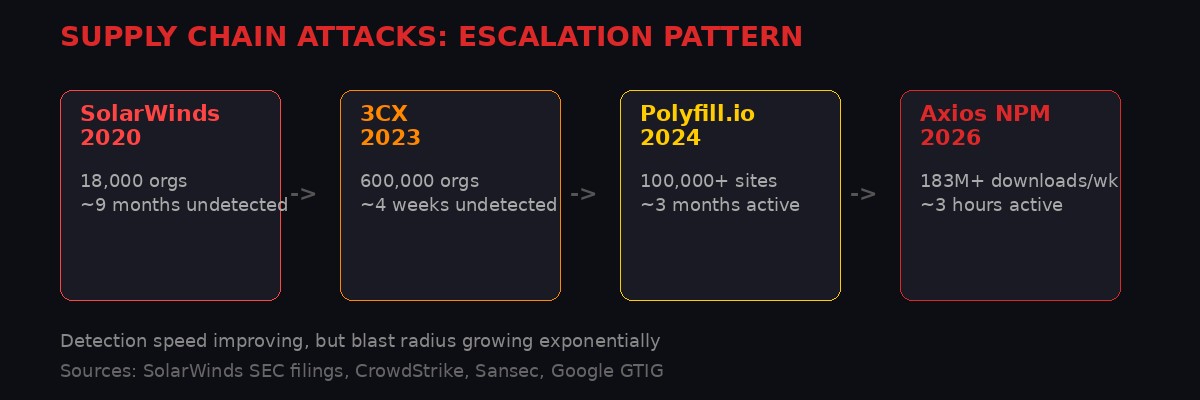
The escalation pattern of supply chain attacks: faster detection, but exponentially larger blast radius. Graphic: BLACKWIRE
The good news embedded in this pattern is that detection is getting faster - from nine months to three hours. The bad news is that the blast radius is getting larger. SolarWinds had 18,000 potential victims. Axios has 183 million weekly downloads. The attackers are winning the scale game even as defenders improve their detection speed.
This reflects a fundamental architectural vulnerability in how modern software is built. The JavaScript ecosystem alone has over 2 million packages on npm, with an average project depending on hundreds of transitive dependencies. Every one of those dependencies is a potential attack surface. And the trust model is largely implicit: developers trust that the maintainers of their dependencies are who they say they are, that their accounts haven't been compromised, and that the code they're pulling hasn't been tampered with.
That trust model is breaking. The question is what replaces it.
Remediation: What Organizations Should Do Right Now

Every development team running JavaScript needs to audit their dependency trees for compromised Axios versions. Photo: Pexels
Google's advisory included specific remediation guidance that organizations should act on immediately. The priority actions break down into three phases: containment, investigation, and hardening.
Immediate Containment
Do not upgrade to Axios version 1.14.1 or 0.30.4. If your organization uses a private npm registry (Artifactory, Verdaccio, GitHub Packages), configure it to serve only known-good versions: 1.14.0 or earlier for the 1.x branch, 0.30.3 or earlier for the 0.x branch. Pin Axios to a safe version in your package-lock.json to prevent accidental upgrades.
Inspect all project lockfiles for the plain-crypto-js package (versions 4.2.0 or 4.2.1). This is the malicious dependency that serves as the payload delivery vehicle. If it appears anywhere in your dependency tree, that project is compromised.
Pause all CI/CD deployments for any pipeline that builds projects depending on Axios. Validate that existing builds are not pulling compromised versions before resuming deployments.
Investigation
For any system that may have installed the compromised versions, conduct a full compromise assessment. Look for the following indicators:
Windows: Check for %PROGRAMDATA%\wt.exe (a copy of powershell.exe), temporary files matching %TEMP%\6202033.ps1, a hidden batch file at %PROGRAMDATA%\system.bat, and a registry entry named MicrosoftUpdate under HKCU\Software\Microsoft\Windows\CurrentVersion\Run.
macOS: Check for /Library/Caches/com.apple.act.mond, which is the Mach-O backdoor binary disguised as an Apple system daemon.
Linux: Check for /tmp/ld.py, the Python-based backdoor payload.
Network: Monitor for outbound connections to sfrclak[.]com on port 8000, or to the IP address 142.11.206.73. The malware beacons every 60 seconds using the User-Agent string mozilla/4.0 (compatible; msie 8.0; windows nt 5.1; trident/4.0).
If any of these indicators are present, assume the system is fully compromised. Rotate all credentials, API keys, and secrets that were accessible from that machine. This includes cloud provider credentials, database passwords, SSH keys, and any tokens stored in environment variables or configuration files.
Long-Term Hardening
This attack exploits a gap that most organizations have known about for years but haven't adequately addressed: dependency management hygiene. The remediation checklist for hardening against future supply chain attacks includes:
Use npm ci instead of npm install in CI/CD pipelines. The former installs from the lockfile exactly, while the latter resolves version ranges that can pull in new (potentially malicious) releases.
Enable npm's built-in audit feature and integrate it into your CI/CD pipeline as a blocking gate. Consider adopting tools like Socket, Wiz, or Snyk that provide deeper dependency analysis including behavioral analysis of package updates.
Implement multi-factor authentication on all npm accounts associated with packages your organization maintains. The Axios compromise began with an account takeover - MFA would have prevented it.
Evaluate the use of npm's provenance feature, which cryptographically links published packages to their source code and build environment. Packages with provenance attestations are significantly harder to tamper with.
Review your organization's use of postinstall scripts and consider disabling them by default. While this breaks some legitimate workflows, it eliminates the primary attack vector used in this and many other npm-based supply chain attacks. The npm configuration option ignore-scripts=true accomplishes this.
The Geopolitical Dimension: Why North Korea Chose Axios

North Korea's cyber operations now generate more revenue than many of the regime's traditional economic sectors. Photo: Pexels
North Korea's decision to target Axios specifically reflects a strategic calculation that deserves examination. The regime's cyber operations serve a dual purpose: intelligence collection and revenue generation. Under the weight of comprehensive international sanctions, the Kim regime has turned cyber theft into what the United Nations has described as a primary source of foreign currency for its weapons programs.
The $6.75 billion cumulative figure for North Korean cryptocurrency theft represents a sum larger than the GDP of several small nations. The February 2025 Bybit hack alone - $1.5 billion in a single operation - exceeded the entire annual GDP of countries like Tonga, Palau, and Nauru combined. The FBI, in its public service announcement confirming North Korean responsibility for the Bybit theft, designated the operation under the name "TraderTraitor" and noted the stolen funds were being rapidly converted and dispersed across thousands of blockchain addresses.
Axios, as a target, offers something that individual exchange hacks don't: breadth of access. By compromising a foundational developer tool, UNC1069 gains potential access to the development environments of companies across every sector - fintech, SaaS, healthcare, government contracting, gaming, and yes, cryptocurrency. The attackers can triage their victims after infection, pursuing those with the highest-value credentials while ignoring the rest. It's a dragnet approach, and it's efficient.
The timing is also notable. The attack launched in the early morning hours of March 31 UTC - late Sunday night in the United States, when security operations centers are typically running skeleton crews and developer activity is low. This timing maximized the window before detection while ensuring that any CI/CD pipelines running overnight builds would pull the compromised versions without human oversight.
There's also a darker implication. The GTIG advisory noted that "hundreds of thousands of stolen secrets could potentially be circulating" from this attack and the concurrent UNC6780/TeamPCP campaigns. Those secrets don't just enable cryptocurrency theft. They enable further supply chain attacks (using stolen publishing credentials to compromise additional packages), SaaS environment compromises (using stolen API keys to access customer data), ransomware and extortion operations, and unauthorized access to government and defense-adjacent systems.
The Axios attack may have been contained in three hours. The consequences of credentials stolen during those three hours could unfold over months or years.
What Comes Next: The Trust Crisis in Open Source

The JavaScript ecosystem's dependency model creates systemic vulnerability that no single security tool can fully address. Photo: Pexels
The Axios compromise forces a reckoning that the software industry has been deferring for years. The open-source ecosystem runs on trust, volunteer labor, and implicit assumptions about identity and integrity that are increasingly untenable in an era of state-sponsored supply chain attacks.
npm, the world's largest software registry with over 2 million packages, has been working to improve security through features like mandatory MFA for high-impact packages, provenance attestations, and improved audit tooling. But these measures are incremental improvements to a system that was designed in an era when the primary threat model was accidental bugs, not deliberate state-sponsored compromise.
The fundamental problem is structural. A single maintainer's compromised credentials can turn any popular package into a weapon. There is no human-in-the-loop approval process for publishing new versions of packages that millions of people depend on. There is no mandatory code review before updates go live. The system is optimized for speed and convenience - developers can push updates and have them available to the world within seconds - and that optimization creates an attack surface that state actors are increasingly exploiting.
Several proposals are circulating in the security community. Sigstore, an initiative backed by the Linux Foundation, provides tooling for cryptographic signing and verification of software artifacts. If widely adopted, it would make it possible to verify that a package was built from a specific commit in a specific repository by a specific (verified) identity. npm's provenance feature builds on similar principles. But adoption remains voluntary, and most packages - including Axios at the time of the attack - don't use it.
More radical proposals include "build from source" models where packages are compiled from audited source code rather than consumed as pre-built artifacts, sandboxed build environments that prevent postinstall scripts from accessing the network or file system, and even a move toward curated package registries where humans review updates before they're made available. Each of these approaches trades convenience for security, and the open-source community has historically prioritized convenience.
The Axios attack may change that calculus. When a three-hour window of compromise in a single package can potentially affect millions of machines across every sector of the global economy, the cost of convenience starts to look unacceptably high.
For now, the immediate priority is triage. Organizations need to determine whether they were exposed, whether their systems are compromised, and whether their credentials need to be rotated. The longer-term work - building a software supply chain that can withstand attacks from the intelligence services of nation-states - will take years. The question is whether the industry will start that work now, or wait for the next attack to force the issue.
North Korea's hackers aren't waiting. They're already planning the next one.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram