The AI Chip Heist: Six Arrested, $2.5 Billion in Nvidia GPUs Bound for China
In the same week that Nvidia's CEO announced restarting H200 sales to China through official channels, the Department of Justice unsealed charges against six people for allegedly doing the same thing - just without the paperwork, using Thai shell companies, unmarked boxes, and thousands of fake servers staged to fool auditors.

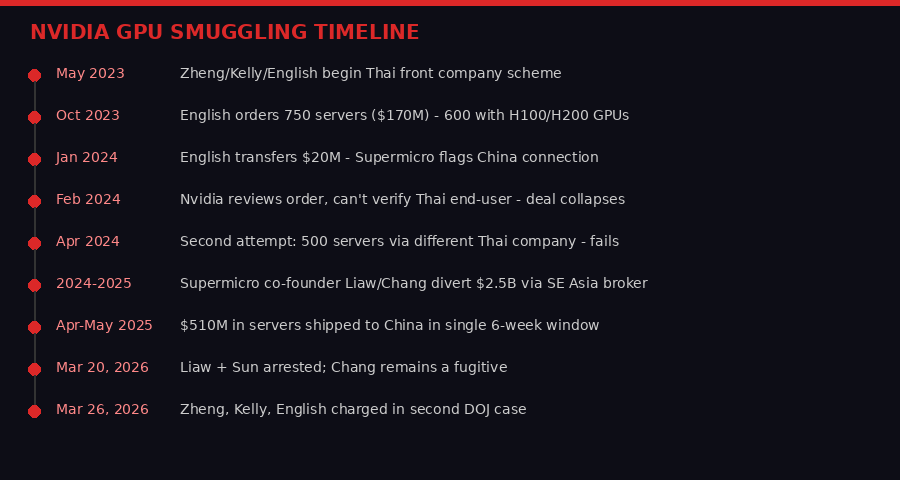
Two separate Department of Justice cases, unsealed six days apart in March 2026, paint a picture of an organized, multi-year effort to funnel American AI hardware into China by any means necessary. The first case, unsealed March 20, charged three people connected to server manufacturer Supermicro with diverting a staggering $2.5 billion in AI-capable servers to Chinese buyers through a Southeast Asian intermediary. The second, unsealed March 26, charged a Chinese national and two US citizens with attempting a separate $170 million scheme using Thai front companies - a deal that collapsed when both Supermicro and Nvidia reviewed it and found the paperwork suspicious.
Together the cases describe the same underlying dynamic: American-made H100 and H200 graphics processing units are worth dramatically more on the Chinese market than they can officially sell for, and that price gap is large enough to motivate elaborate criminal enterprises spanning multiple continents.
The Supermicro Insider Case
The larger and more audacious of the two cases involves Yih-Shyan "Wally" Liaw, a co-founder of Supermicro and its Senior Vice President of Business Development. Liaw was arrested March 20 alongside broker Ting-Wei "Willy" Sun, a Taiwanese national who allegedly served as a logistics fixer. A third defendant, Ruei-Tsang "Steven" Chang - a general manager in Supermicro's Taiwan office - remains at large as a fugitive.
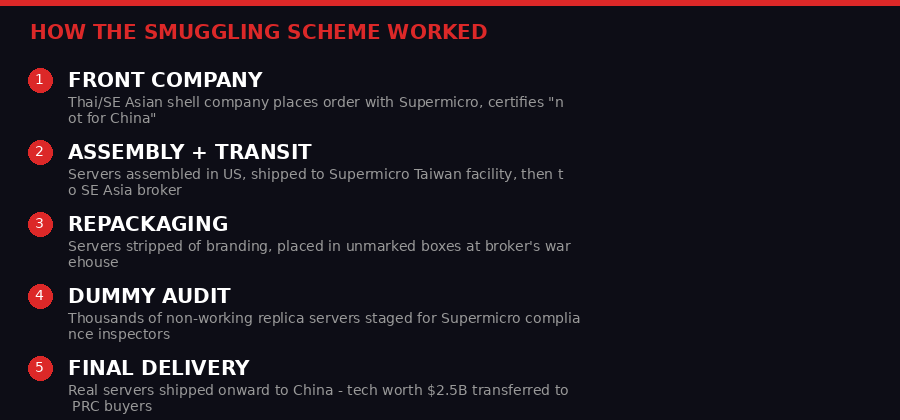
According to the indictment unsealed in Manhattan federal court, the three defendants systematically directed an unnamed Southeast Asian company to place purchase orders with Supermicro for servers containing controlled Nvidia GPUs. The servers were assembled in the United States, shipped to Supermicro's Taiwan facilities, then delivered to the intermediary elsewhere in Southeast Asia - before being repackaged in unmarked boxes and quietly forwarded to customers in China.
"These defendants allegedly fabricated documents, staged bogus equipment to pass audit inventories, and used a pass-through company to conceal their misconduct and true clientele list." - FBI Assistant Director in Charge James C. Barnacle Jr., New York Field Office (DOJ press release, March 20, 2026)
The alleged scheme ran from 2024 to 2025 and is accused of transferring approximately $2.5 billion worth of servers. The pace reportedly accelerated sharply: between late April and mid-May 2025 alone, roughly $510 million worth of servers assembled in the United States were diverted to China in a single six-week window.
Perhaps the most remarkable detail in the indictment is the dummy server operation. To deceive Supermicro's compliance team - the division responsible for ensuring US export laws were being followed - the defendants are alleged to have staged thousands of non-working physical replicas of the servers. When auditors came to verify that hardware was sitting in the Southeast Asian warehouse where it was supposed to be, they reportedly found convincing fakes. The real servers had already been repackaged and were in transit to China.
U.S. Attorney Jay Clayton for the Southern District of New York described the operation as "a tangled web of lies, obfuscation, and concealment - all to drive sales and generate revenues in violation of U.S. law." Supermicro, for its part, issued a statement saying the alleged conduct "is a contravention of the company's policies and compliance controls" and that the company is "cooperating fully" with investigators. Supermicro itself is not named as a defendant in the indictment.
The Thai Shell Company Case
Six days later, a second set of charges described a different group with a similar playbook. Stanley Yi Zheng of Hong Kong, along with US citizens Matthew Kelly and Tommy Shad English, allegedly began scheming in May 2023 to purchase GPU servers from Supermicro using Thai front companies as cover, with China as the intended final destination.
The scheme hit its peak ambition in October 2023, when English - purporting to act on behalf of a Thailand-based client - placed an order for 750 servers worth approximately $170 million from Supermicro. Of those servers, 600 contained H100 or H200 GPUs on the US Commerce Department's control list, requiring an export license to ship to China. English signed an "Advanced Computing Certification" swearing the hardware was not headed for any restricted country.

The deal unraveled during a January 2024 compliance review. When English asked Supermicro to add Zheng and Kelly to an email thread, the manufacturer noticed that Zheng's company was headquartered in China - and that no one from the purported Thai customer was on the thread. "China is an embargoed country restricted by the US government," Supermicro noted in the email chain. "US companies are restricted from selling to businesses or end users headquartered in China."
Nvidia then reviewed the order independently. Unable to verify the actual end-user in Thailand, the chipmaker declined to proceed. The $170 million order was cancelled. A second attempt in April 2024 - this time using a different Thai company and seeking 500 servers - also failed.
Text messages obtained through the investigation gave prosecutors a window into the alleged conspiracy. In a group chat titled "GPU Partnership," Kelly wrote in June 2023: "I know you mention you are better than CDW but they have a nice website, company decks, quarterly earning reports, etc that are all public information." English replied: "I'm not breaking my back. I fake these weeks ago." By July, Zheng was messaging the group with market pricing data for Nvidia chips in China - evidence, prosecutors say, that all three knew China was the destination.
In March 2024, Kelly sent Zheng a draft solicitation to recruit other participants, which read in part: "[I am] currently working on distributing GPU systems with [Company-2] chips for supercomputing. We have a few customers in China but it's a banned country for distribution."
How the Schemes Worked: The Mechanics of AI Chip Smuggling
Both cases reveal a common architecture for circumventing US export controls. The core challenge is that Nvidia H100 and H200 chips are on the Commerce Department's control list - any sale to China requires a license, and licenses for advanced AI accelerators to Chinese buyers are functionally unavailable under current policy.
The workaround involves three elements. First, a front company in a neutral country - Thailand, Taiwan, or elsewhere in Southeast Asia - presents itself as the actual buyer. These companies are sometimes real businesses with legitimate-looking documentation, websites, and financial histories. Second, the hardware is shipped to that neutral country, where it appears to be a legitimate import. Third, a logistics and repackaging operation erases identifying markings and routes the servers onward to China in unmarked containers.
The third step is where the Supermicro case got particularly elaborate. Staging thousands of dummy servers to pass compliance audits is not something improvised - it requires warehouse space, staff, and coordination between the buyer and logistics partners who are willing to set up an entire fake inventory. That level of operational sophistication suggests the Southeast Asian intermediary in the case was not an amateur front but an experienced smuggling infrastructure.
"Advanced computing technologies like Graphics Processing Units play a critical role in military artificial intelligence and national defense capabilities. When individuals attempt to illegally acquire or export this technology for profit, they are putting national security and our warfighters at risk." - Jason J. Sargenski, Special Agent-in-Charge, DCIS Southeast Field Office (DOJ press release, March 26, 2026)
The use of Internet-facing corporate structures - fake employee rosters, financial documents, business registration papers - reflects how export control evasion has professionalized. It is no longer the domain of individual brokers selling a few cards; it is increasingly organized, multi-year, and involves insiders at the manufacturing company itself.
The Policy Paradox: Banned and Legal at the Same Time

The timing of these arrests contains a deep irony that the Justice Department did not comment on. Nvidia CEO Jensen Huang announced at the company's GTC conference on March 17 that Nvidia had received purchase orders from Chinese customers for H200 GPUs and was restarting manufacturing for the Chinese market. "We've been licensed for many customers in China for H200," Huang said.
The Trump administration had lifted an export ban on H200 chips in December 2025. China's government briefly discouraged local buyers from purchasing the hardware, but by mid-March that pressure appeared to have eased. The H200 - a chip that people went to prison risks to smuggle for years - was being manufactured legally for Chinese buyers at the same time prosecutors were charging six people for attempting to smuggle it illegally.
This is not as contradictory as it looks. Export controls have always operated on a case-by-case basis. The banned H100s and the older H200 chips covered in the first wave of restrictions are different products than the H200s being licensed today. And the licensing regime itself is the point - Washington wants to control who in China gets advanced AI compute, and at what volume. Smuggling operations bypass that control entirely, leaving no audit trail, no end-user agreements, and no ability to claw back hardware if the geopolitical situation changes.
The broader context matters here. These cases follow a December 2024 rule that allowed H200 exports to China only if sufficient supply existed in the US first. They follow a January 2026 rule that put Chinese buyers at the back of the queue. They follow an ongoing Commerce Department proposal - reported by Axios in March 2026 - to require export approval on a country-by-country basis for any AI chip sale. The policy is in constant flux, but the underlying enforcement machinery keeps grinding forward regardless of what the official policy says today.
Why the Chips Are Worth the Risk
To understand why people are willing to risk federal prison for GPU servers, you need to understand the price differential. An Nvidia H100 GPU in an approved country costs roughly $25,000-$30,000 at retail. On China's gray market, where domestic alternatives like Huawei's Ascend series lag significantly behind Nvidia's hardware on key benchmarks, equivalent chips have reportedly commanded multiples of that price - in some periods, $40,000 to $50,000 per unit or more, depending on configuration and availability.
At that premium, a single truckload of servers can generate millions of dollars in profit. The $170 million order in the second DOJ case - 600 controlled GPUs - represents potential gray-market upside of tens of millions of dollars on a single transaction. The $2.5 billion in the first case, if even a fraction reached Chinese buyers at gray-market rates, represents an extraordinary windfall.
China's appetite for advanced AI compute is not abstract. The country is running large language model training programs, military AI research, autonomous systems development, and a push toward semiconductor self-sufficiency that requires vast amounts of GPU-accelerated simulation and training. Domestic alternatives exist - Huawei's Ascend 910B has been widely adopted - but American hardware, particularly Nvidia's H100 architecture, remains significantly more performant for many workloads. That performance gap is exactly what US export controls are designed to preserve.
The Commerce Department's formal determination, cited in the Supermicro indictment, puts it plainly: "The computing capabilities in advanced artificial intelligence accelerator hardware are of sufficient strategic significance that their transfer to China poses an unacceptable risk to national security."
The Enforcement Wave: More Cases Coming
The six defendants arrested this month are not isolated cases. They are part of a broader enforcement surge that intelligence officials and export control lawyers have been tracking since 2023, when the Biden administration first imposed sweeping restrictions on advanced AI hardware exports to China.
The DOJ's National Security Division - which brought both cases - has been staffing up for technology export enforcement for two years. The FBI's Counterintelligence and Espionage Division, which investigated both cases, cited "increasingly brazen schemes" as AI chip restrictions multiplied. In a statement, FBI Assistant Director Roman Rozhavsky said: "As our foreign adversaries escalate their efforts to dominate the field of artificial intelligence, we are seeing them employ increasingly brazen schemes to illegally acquire valuable U.S. technology."
The March 2026 cases are not the first. In late 2024 and early 2025, prosecutors charged several individuals in separate cases involving smaller volumes of restricted chips moving through Singapore, the UAE, and Central Asia. Those cases established the legal framework and investigative template that the current cases are built on.
What is new in March 2026 is the scale and the corporate insider element. Having a co-founder of a major server manufacturer allegedly at the center of a $2.5 billion diversion scheme is a qualitative escalation. It suggests that export control enforcement has not deterred participation at the executive level, that the profit margins are sufficient to attract insiders with deep access to manufacturing and logistics operations, and that the standard compliance controls at large hardware manufacturers are insufficient to catch schemes run by the people who designed those controls.
What Supermicro's Role Tells Us
Supermicro's position in both cases is worth examining carefully. In the second case - the $170 million Thai front company scheme - the company played a largely positive role. It noticed the Chinese connection during a compliance review, flagged it internally, and declined to complete the transaction. Nvidia reviewed the order independently and also refused to proceed. The deal collapsed because two levels of the supply chain did their jobs.
In the first case, one of the company's own co-founders is alleged to have been running the scheme from the inside. Liaw's role as SVP of Business Development would have given him direct access to Supermicro's sales pipeline, customer approval processes, and the compliance team he was allegedly deceiving with dummy servers. That kind of insider access is not something external due diligence can catch - it requires robust internal monitoring of senior executives' deal flow, which is a much harder problem.
Supermicro has had a turbulent few years regardless. The company nearly faced NASDAQ delisting in 2025 after accounting irregularities forced a delay in filing its annual 10-K with the SEC. It eventually cleared that hurdle and reported $12.7 billion in revenue in its most recent quarter. The GPU export case is a distinct matter, but it arrives at a company that has been under scrutiny on multiple fronts simultaneously.
The company's statement - that it is cooperating fully and that the defendants' alleged conduct contradicts company policy - is accurate in a technical sense. But when the person running a $2.5 billion diversion scheme is a co-founder with decades of history at the company, "this contradicts our policies" is a harder claim to make credibly. The indictment describes false documents and false communications prepared "to ensure that server allocations were approved internally at the U.S. Manufacturer" - meaning the scheme required actively gaming Supermicro's own internal approval process.
Second-Order Effects: What Happens to Export Controls Now
The two DOJ cases arrive in the middle of an ongoing policy debate about how aggressively the US should restrict AI chip exports. That debate now has new data points.
For the side arguing for tighter controls: if a $2.5 billion scheme ran for two years before being disrupted, and if a single six-week window saw $510 million in hardware move to China, then the leak rate through export controls is enormous. The official policy may say "no H100s to China," but the actual flow of chips does not respect that line. Tighter controls, more intrusive audits, and mandatory end-user verification at the chip level - not just the server level - might close some of those gaps.
For the side arguing against over-restriction: the fact that H200s are now being sold legally to China - while people face federal charges for smuggling the same hardware - illustrates exactly how unstable the policy is. Companies and individuals operating in the gray zone are partly responding to a policy environment that reverses itself repeatedly, making it difficult to know which hardware is actually off-limits at any given moment. Some market participants may have calculated that a practice that is legal today was worth the risk of doing illegally yesterday.
There is also a competitiveness argument. The Trump administration's Commerce Department has explicitly rejected the Biden-era AI Diffusion rule as "burdensome, overreaching, and disastrous." The emerging framework - bilateral licensing deals modeled on the UAE and Saudi Arabia agreements, with investment in US AI infrastructure as a condition - is designed to keep chip sales flowing while creating political accountability for where the chips end up. Whether that framework is more or less effective at actually preventing diversion than the prior rule is an empirical question that these prosecutions will help answer over the next several years.
What seems clear is that no policy framework, however tightly designed, can fully substitute for supply chain integrity and insider threat programs at the manufacturers themselves. The Supermicro case is ultimately a failure of internal controls, not just a failure of export policy. Companies that build hardware for the AI economy are now as much a national security actor as a defense contractor - and the enforcement apparatus is starting to treat them that way.
Key Facts: The Two DOJ Cases
- Case 1 (SDNY, unsealed Mar 20): Liaw, Chang, Sun - $2.5B in Supermicro servers via SE Asian broker; dummy server audits; Taiwan transshipment. Liaw + Sun in custody, Chang a fugitive.
- Case 2 (N.D. Georgia, unsealed Mar 26): Zheng, Kelly, English - $170M order (Oct 2023) + 500-server attempt (Apr 2024) via Thai front companies. All three in custody.
- The hardware: Nvidia H100 and H200 GPUs, controlled under US Commerce Department Export Administration Regulations. License required for China; licenses for advanced AI chips are functionally unavailable.
- The gap: At peak, $510M in servers moved to China in a six-week window (Apr-May 2025) under the Supermicro scheme - after controls were in place.
- Charges: Conspiracy to violate the Export Controls Reform Act, conspiracy to smuggle goods from the US, conspiracy to defraud the United States.
The Defendants and What Comes Next

Liaw and Sun were presented before a federal judge in the Northern District of California on March 20. Chang, the Supermicro Taiwan general manager, remains at large - likely outside US jurisdiction, complicating extradition. In the second case, Zheng appeared before a judge in the Northern District of California, while Kelly and English were taken into custody in Georgia, the jurisdiction of the prosecuting US Attorney's office.
The charges in both cases carry significant sentencing exposure. Conspiracy to violate the Export Controls Reform Act carries up to 20 years. Smuggling carries up to 10 years. Conspiracy to defraud the United States carries up to 5 years. Prosecutors will likely use those maximums as leverage in plea negotiations, particularly given the scale of the alleged schemes.
For Supermicro, the path forward is uncertain. The company's cooperation with investigators may provide some insulation from institutional liability, but the discovery that a co-founder allegedly ran a multi-billion-dollar diversion ring from inside the company will draw intense regulatory scrutiny of its compliance programs. Government customers - including US defense contractors who purchase Supermicro servers for AI workloads - will want assurances that the company's internal controls are adequate.
More broadly, the semiconductor industry is watching. Every major server vendor and chip manufacturer operates in the same export control environment. If Supermicro's co-founder could orchestrate a $2.5 billion scheme while the company filed compliance certifications with the US government, the enforcement community's question for every other vendor is simple: how confident are you that the same thing isn't happening at your company?
The answer, for now, is: not very. And that is why these cases matter beyond the individuals named. They are a stress test of the assumption that export controls can be enforced through paperwork and policy, rather than technology and oversight. The dummy servers in that Southeast Asian warehouse were not a failure of law - they were a failure of architecture. The law said no chips to China. The architecture let a co-founder build a system that made it happen anyway.
That gap is what the next round of export control policy - whatever form it takes under the Trump Commerce Department - will have to close.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram