8.3 Million "Anonymous" Crime Tips Weren't. The Company Still Won't Admit It.
A hacker group called the Internet Yiff Machine claims to have pulled 93 gigabytes of data from P3 Global Intel - the tip management platform used by over 30,000 schools, hundreds of Crime Stoppers programs, and multiple law enforcement agencies. The data allegedly contains 8.3 million tips submitted by people who were promised anonymity. Navigate360, the company that owns P3, has been stonewalling since the breach first surfaced weeks ago.
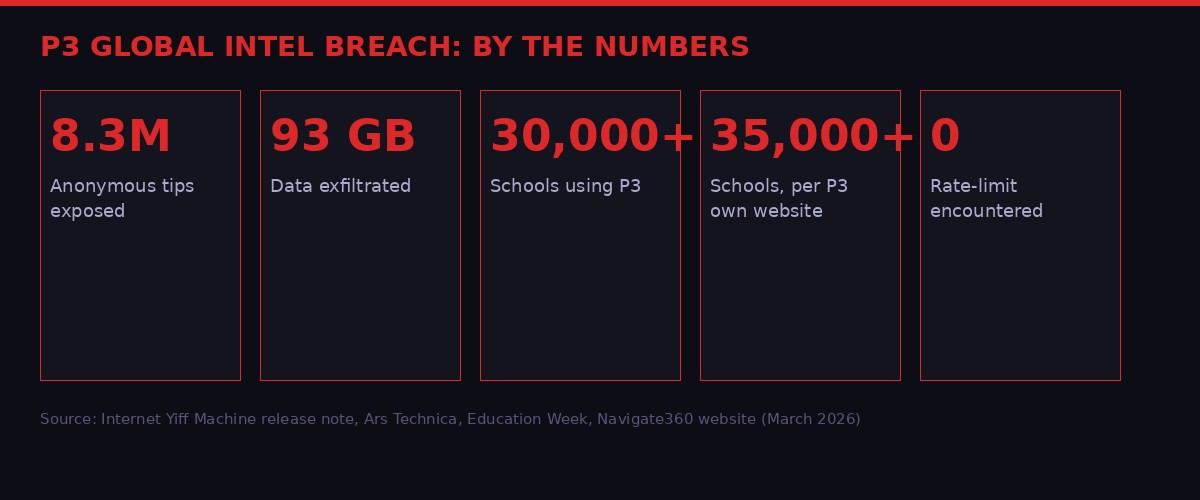
The scale of the P3 Global Intel breach: 8.3 million tips, 93GB of data, over 30,000 affected schools. Source: Internet Yiff Machine release note, Ars Technica, Education Week (March 2026)
The Platform Nobody Heard Of - That Knew Everything
P3 Global Intel is not a household name. That is by design. The platform works in the background of American safety infrastructure - a quiet conduit through which citizens report crimes, students flag threats, and witnesses share what they saw without putting their names on it. Since 1998, when Navigate360's predecessor built the original tip management software called TipSoft, the company has positioned itself as the infrastructure of anonymous disclosure.
By Navigate360's own accounting, the P3 platform has been deployed in more than 30,000 schools across the United States. Its campus-focused product, P3Campus, is the official technology partner for Sandy Hook Promise, Safe2Tell in Colorado and Wyoming, SafeVoice in Nevada, SafeSchools in Maryland, Courage2Report in Missouri, Safe2Say in Pennsylvania, SaySomething in North Carolina, and SpeakUpSpeakOut in Wisconsin. These are not fringe programs - they represent some of the most trusted school safety frameworks in the country, built explicitly on the promise that students and parents can report threats without being identified.
On the law enforcement side, P3 powers Crime Stoppers programs across North America, serving what the company calls "thousands of organizations" including law enforcement agencies and government bodies. Major urban crime tip lines - the kind that accept reports on murder suspects, gang activity, and drug trafficking - run on this infrastructure. Some fusion centers, the joint intelligence-sharing hubs operated by state and federal agencies, are also clients.
This concentration of sensitive, confidential reporting into a single vendor is not unusual in the government contractor space. It is, however, catastrophically risky when that vendor's security posture turns out to be dramatically weaker than its marketing implies.
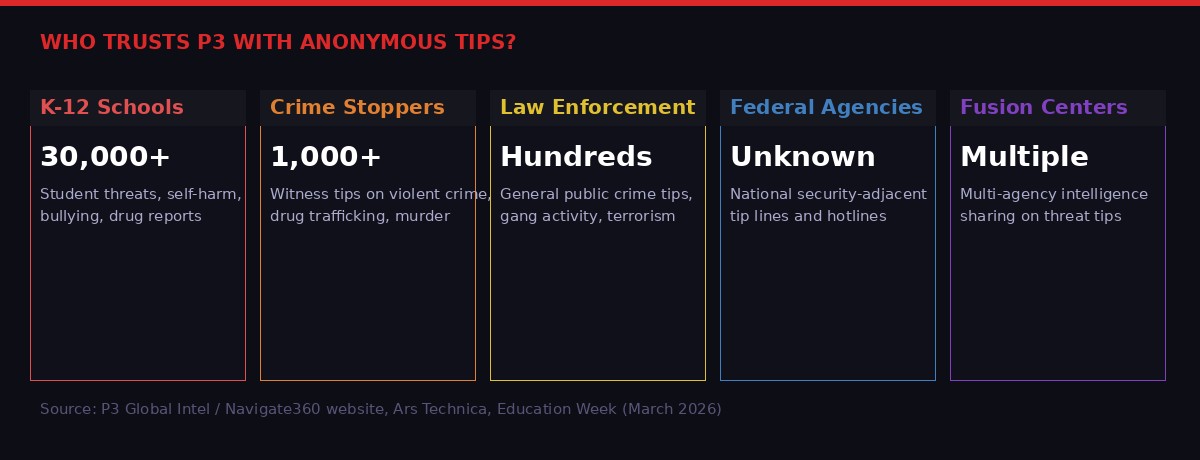
The breadth of P3's customer base spans schools, crime stoppers programs, law enforcement, federal agencies, and fusion centers - all now potentially affected by the breach. Source: Navigate360 website, Education Week (March 2026)
What the Hackers Say They Did - And How Easy It Was
The group calling itself Internet Yiff Machine claims the attack was not sophisticated. In a release note accompanying the alleged data dump, they stated they sent over 8 million requests to P3's systems pulling all available data - and encountered zero issues doing so. No rate limiting. No block. No alarm triggered. The database, by their account, was essentially unguarded.
"No joke, I sent over 8 million requests pulling all their data and didn't encounter any issues whatsoever."
- Internet Yiff Machine, release note accompanying alleged P3 data dump (March 2026), via Ars Technica
Rate limiting is a fundamental, table-stakes security control. It restricts how many requests a single client can make to an API or database within a given time window. Bypassing it requires either a sophisticated attack - or encountering a system with no rate limiting implemented at all. If the hacker's account is accurate, the latter is what happened here. A company promising anonymity to millions of people apparently left its back door not just unlocked but removed entirely.
The breach was first reported publicly by Straight Arrow News, the outlet founded by American businessman Joe Ricketts. The data was also allegedly shared with Distributed Denial of Secrets (DDoSecrets), a transparency organization that has previously published law enforcement and corporate data leaks. The fact that the data was shared with a transparency organization rather than sold on a dark web forum is consistent with hacktivist motives - though as Ars Technica's Nate Anderson notes, the manifesto trimmings could equally be cover for a nation-state operation seeking to sow domestic distrust.
The hacker group's stated ideology is anti-police and anarchist in character. Their release calls out the role of law enforcement in serving "billionaires, politicians, and corporations." Whatever their politics, the technical claim they made is either a damning indictment of P3's security, or an elaborate fabrication. Given that Portland's police bureau issued an advisory urging people to stop using the platform, the former seems increasingly likely.

How the breach unfolded over three weeks in March 2026 - from the initial hack to law enforcement advisories and media coverage, with Navigate360 still silent. Source: Ars Technica, Portland.gov, Education Week (March 2026)
Navigate360's Response: Corporate Silence as a Strategy
Navigate360 CEO JP Guilbault issued a statement that is a masterclass in saying nothing while appearing to say something.
"We are currently working to determine whether we have experienced an incident involving our computer network and, if so, the extensiveness of the incident and the information involved. We have not confirmed that any sensitive information has been accessed or misused."
- JP Guilbault, CEO of Navigate360, statement to Education Week (March 2026)
This statement was issued while law enforcement agencies were already advising their communities to stop using the platform. The Portland Police Bureau did not wait for Navigate360 to tell them whether the breach was real - they made a judgment call based on the available evidence and erred on the side of caution. Portland advised community members "out of an abundance of caution" to temporarily stop submitting tips through Crime Stoppers, and directed people to submit non-anonymous information directly via email instead.
Navigate360 did not respond to further requests for comment from Ars Technica even after a week had passed since the initial Straight Arrow News report. The company has hired an independent digital forensics firm to investigate - standard procedure that can also, conveniently, serve as a reason to defer all public comment indefinitely.
The company's legal exposure is significant. If the breach is confirmed, Navigate360 faces potential liability under state data breach notification laws (most states require notification within 30-90 days of discovering a breach), FERPA provisions covering student data, and potentially CISA guidelines for critical infrastructure cybersecurity. Every day the company delays confirmation is a day affected individuals cannot take protective action.
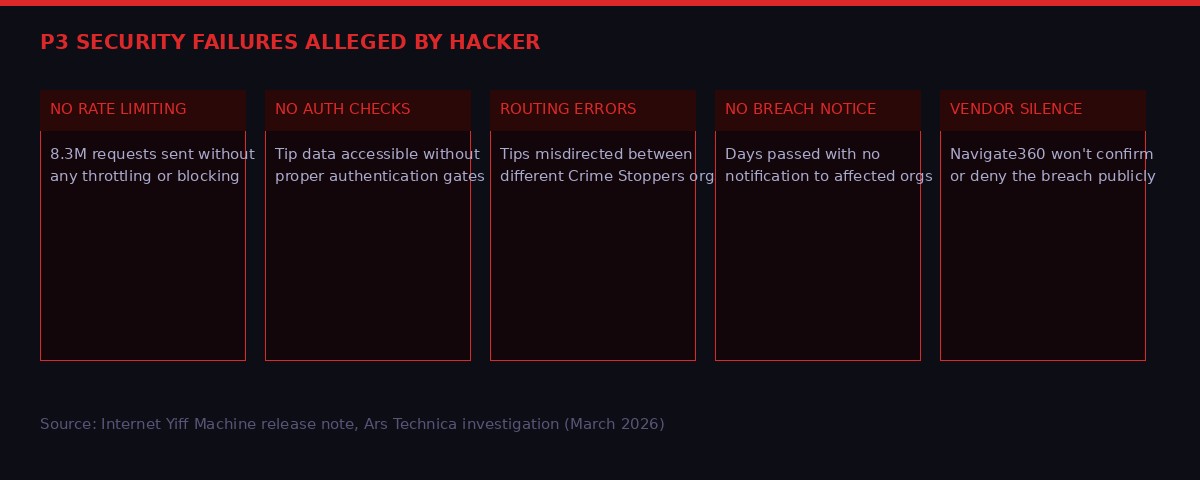
The security failures alleged by Internet Yiff Machine paint a picture of a platform that treated basic protections as optional. Source: Internet Yiff Machine release note, Ars Technica investigation (March 2026)
What Was In Those 93 Gigabytes
The sensitive nature of tip-line data is difficult to overstate. This is not leaked credit card numbers or email addresses. The tips flowing through P3 represent some of the most intimate disclosures people make to institutions.
According to P3Campus's own marketing, the three top categories of school tips the platform processes are suicide and self-harm reports, bullying and harassment complaints, and drug activity. These are the kinds of disclosures a student makes when they are at their most vulnerable - sometimes reaching out to report themselves, sometimes reporting a friend in crisis, sometimes identifying a threat actor that could become the next school shooter.
David Riedman, founder of the K-12 School Shooting Database and a professor of security and risk management at Idaho State University, was direct about what exposure means:
"This is an app that is sold to identify students who are thinking about self harm, being abused, abusing substances, or making threats of violence. That is the most sensitive information possibly available about a child."
- David Riedman, K-12 School Shooting Database founder, via Education Week (March 2026)
The risk runs in both directions. The student who filed a tip - believing they were anonymous - could now be identified and targeted. The student who was the subject of a tip - perhaps for behavior that never led to actual harm - now has that fact potentially accessible to whoever got the data. Both face real-world consequences: social retaliation, violence, and in cases where the tip triggered a threat assessment process, potential legal liability. Multiple lawsuits have been filed by families of students caught up in school threat assessments over the years.
On the law enforcement side, the risk profile is different but equally serious. Crime Stoppers tips often come from witnesses to violent crime. If those tips are compromised - if the identities of informants can be pieced together from the data - sources could be endangered. Retaliatory violence against tipsters is not a hypothetical in organized crime or gang-related investigations.
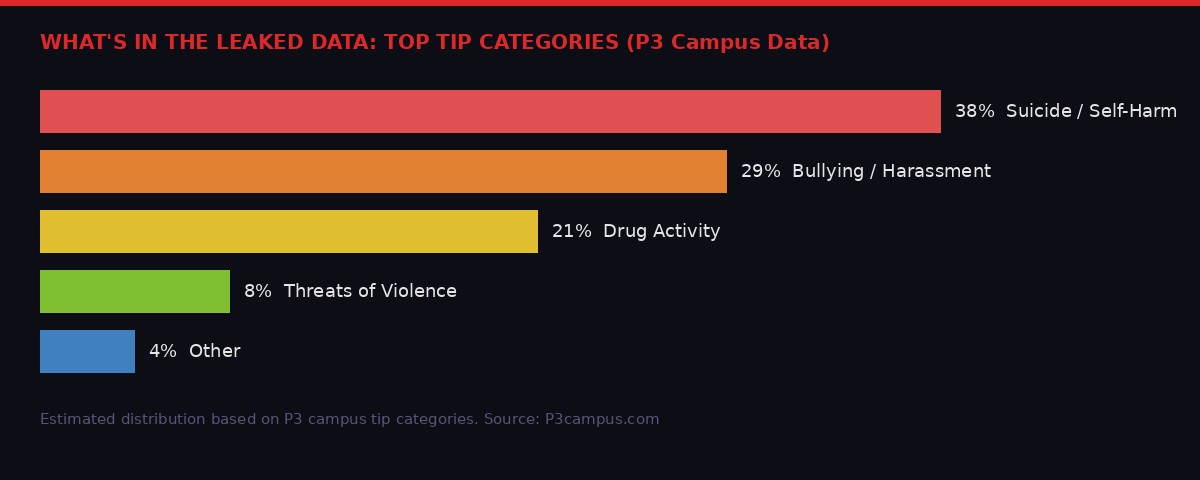
The three largest categories of P3 school tips involve the most sensitive possible student data - self-harm, bullying, and drug activity reports made under the assumption of anonymity. Source: P3Campus.com, March 2026
The Routing Error That Should Have Ended This Story Earlier
Among the technical details that emerged from the Ars Technica investigation is one that suggests P3's infrastructure problems run deeper than just the breach itself. When reporter Nate Anderson attempted to access the tips page for his local Philadelphia "fusion center" through P3's own site, clicking through sent him not to the Philadelphia program - but to the Greater Kansas City Crime Stoppers TIPS Hotline.
That is a basic routing error. Tips submitted to one jurisdiction were potentially being routed through or accessible to another's management system. The implications are uncomfortable: if Anderson stumbled onto this with a casual test click, what else might be misconfigured? How many tips submitted to one city's Crime Stoppers program were actually visible to administrators in a different city?
This kind of error does not happen in well-engineered systems. It suggests the kind of infrastructure that was built fast, scaled fast, and never received the security engineering attention that a platform handling millions of sensitive disclosures deserves. The fact that P3 marketed itself as industry-standard while apparently running this kind of configuration makes the company's claims of anonymity protection look less like a commitment and more like a sales pitch.
Kenneth Trump, school security expert and president of National School Safety and Security Services, identified the second-order problem immediately:
"School administrators work so hard to create that trust to get kids to come forward, and kids are not going to trust anonymous reporting if the system is actually not anonymous."
- Kenneth Trump, National School Safety and Security Services, via Education Week (March 2026)
That trust, once broken, is almost impossible to rebuild. A student who learns that their anonymous suicide report was sitting in an unsecured database - accessible to anyone with enough patience to send 8 million API requests - will not file another report. The next threat, the next crisis, the next "I think my friend is going to hurt himself" moment may go unreported. The downstream cost of a security failure at a tip-line operator is not just legal liability. It is human lives.
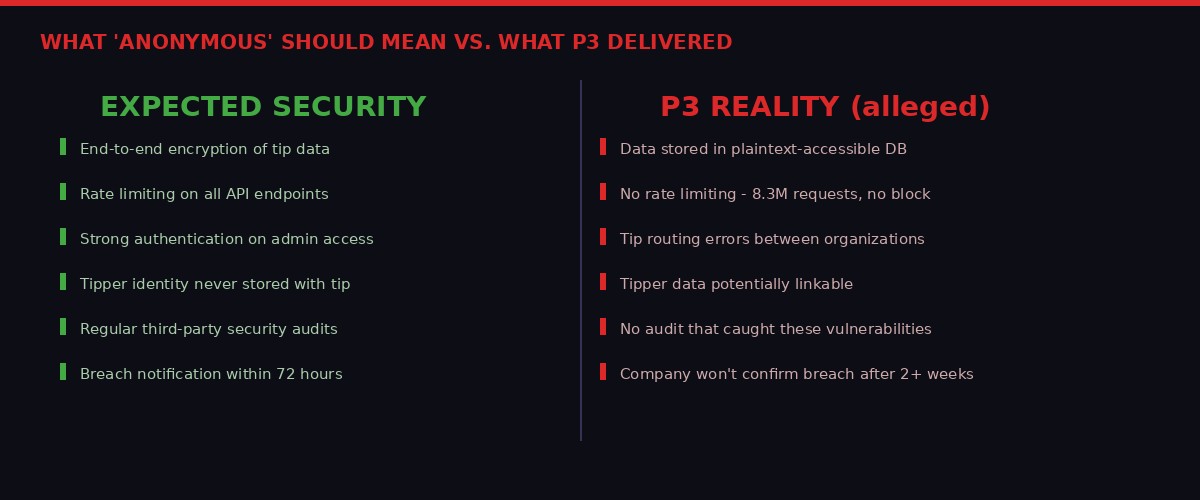
The gap between what anonymous tip systems should deliver and what P3 allegedly provided according to the hackers. Source: Internet Yiff Machine release note, Ars Technica (March 2026)
Hacktivism, Nation-States, or Something In Between
The identity and motivation of Internet Yiff Machine matters for understanding what happens next to the data. The group's manifesto reads as classic hacktivist theater - anti-police, anti-corporate, explicitly political. They describe themselves as being "made of copper wire, motherboards, fur, and homosexuality" - a deliberately absurdist self-description that blends hacker culture with furry community aesthetics. It is designed to be difficult to take seriously, which is perhaps the point.
Doug Levin, national director of the K12 Security Information Exchange and a school cybersecurity expert, characterized the incident as "classic hacktivism" - based on the fact that the data was shared with a nonprofit transparency organization rather than monetized or ransomed. In ransomware attacks, the data is leverage. In hacktivist attacks, the data is the message. Sharing it with DDoSecrets rather than selling it to a foreign intelligence service fits the hacktivist pattern.
But Ars Technica's Anderson raises a legitimate counter-possibility: nation-state actors have become adept at mimicking hacktivist aesthetics to obscure their real objectives. Accessing 8.3 million confidential tips about crime, student threats, and law enforcement intelligence is genuinely useful to a foreign intelligence service. Knowing which informants cooperated with police. Knowing which students were flagged as potential threats. Knowing the internal communications of fusion centers. All of that has intelligence value that dwarfs any hacktivist point-making.
The data has not been publicly released in full, which cuts against a pure hacktivist motivation - publicizing injustice typically involves actually publishing the evidence. The current situation, where the data exists in the hands of DDoSecrets and is not fully public, suggests either a responsible disclosure framework or a more calculated strategy. If the breach is confirmed and the data surfaces more widely, that ambiguity will sharpen considerably.
The Vendor Accountability Problem in School Safety Tech
The P3 breach is not an isolated incident. It fits into a pattern of school safety technology vendors operating with insufficient security discipline while marketing products that inherently require the highest possible security standards.
Education Week noted that the breach comes "in the wake of other companies that work with schools getting hacked" - a phrase that suggests the education technology vendor ecosystem has a systemic problem with security rather than a one-time lapse. Schools are under enormous pressure to implement safety technology in the wake of mass shootings. Vendors compete on features and price. Security is invisible until it fails.
The procurement problem is structural. A school district's IT team may not have the expertise to audit the security posture of a third-party tip management vendor. The contracts may not specify security standards. And the consequences of a vendor security failure land on the school and its students - not on the vendor's executives or investors.
Doug Levin of the K12 Security Information Exchange recommended that school districts take three immediate steps: suspend use of the platform during the investigation, demand updates directly from Navigate360, and determine whether their specific data was among what was compromised. None of those steps should be optional, and yet they require individual school districts to take initiative that the vendor itself has failed to take on their behalf.
The model of outsourcing highly sensitive data handling to private vendors who are not subject to the same accountability frameworks as public agencies is a structural vulnerability in American institutional security. P3 is the latest illustration of a problem that predates it and will outlast it.
What Happens to Anonymous Reporting Now
The hardest part of this story is not the technical failure. Security breaches happen - no system is perfectly secure. The hardest part is what the breach does to the fundamental premise of anonymous tip reporting as a public safety tool.
Anonymous tip lines exist because people will not report crimes if they fear retaliation. Students will not report threatening classmates if they fear being labeled a snitch. Witnesses will not report murders in neighborhoods where cooperating with police is dangerous. The anonymity is not a feature - it is the product. It is why the system works at all.
When the anonymity fails, the system fails. Not just for the people whose data was exposed in this breach - but for everyone who now learns that submitting an "anonymous" tip means trusting a private company with profit motives and apparently minimal security hygiene. That trust cannot be rebuilt by a press release. It requires demonstrated accountability, transparent disclosure, and structural reforms to how these vendors are selected, audited, and held responsible for failures.
None of that is happening right now. Navigate360 is not disclosing. The investigation is ongoing. The data is presumably in more hands than when the breach started. And 8.3 million people who thought they were protected are waiting to find out if they were wrong.
The Internet Yiff Machine says they hacked this system to expose that it was not actually anonymous. By that measure - whether or not the politics are sympathetic - they have made their point.
Key Facts: P3 Global Intel Breach
- Alleged data stolen: 93GB containing 8.3 million tips (per Internet Yiff Machine release note)
- Platforms affected: P3 Global Intel - used by 30,000+ schools, Crime Stoppers programs, law enforcement, and federal agencies
- Security failure alleged: No rate limiting - 8 million+ requests sent without triggering any block or alert
- Known routing error: Philadelphia fusion center tip page redirected to Greater Kansas City Crime Stoppers
- Confirmed response: Portland Police Bureau advised community to stop using platform (March 19, 2026)
- Navigate360 status: Company has not confirmed or denied breach; hired third-party forensics firm to investigate
- Data type: Anonymous crime tips including suicide reports, bullying disclosures, drug activity, violent crime witness accounts
- School programs exposed: Sandy Hook Promise, Safe2Tell, SafeVoice, SafeSchools, Safe2Say, and five other statewide school safety programs
The Reckoning That Is Coming - Or Isn't
Corporate accountability for data breaches in the United States follows a predictable arc. There is an incident. The company issues a vague statement. A forensics firm is hired. Months pass. If a regulator gets involved, there is a fine that represents a fraction of the harm done. The executives keep their jobs. The stock price recovers. The affected individuals receive a letter offering two years of free credit monitoring from yet another vendor they never agreed to trust.
That arc should look different when the exposed data is not payment card numbers but anonymous reports about child safety. The people who submitted tips through P3 did so as part of institutional safety programs - often encouraged to do so by school administrators, law enforcement outreach programs, or government safety campaigns. They were not voluntary consumers of a data-hungry app. They were participants in public safety infrastructure that their institutions vouched for.
The liability question extends beyond Navigate360. The school districts, law enforcement agencies, and government bodies that contracted with P3 owe their communities an explanation for why they deployed a tip management system that apparently lacked basic security controls. The federal programs that funded school safety technology may need to revisit the vendor qualification frameworks that allowed P3 to become the de facto standard without serious security scrutiny.
FERPA, the Family Educational Rights and Privacy Act, places obligations on educational institutions regarding student data - including data held by third-party vendors. If student tip data is among what was exposed, school districts face potential FERPA violations they did not directly cause but are responsible for under the law. The same framework that makes schools responsible for vendor security failures is the one that will determine who gets sued when the full scope of the breach becomes clear.
The most immediate practical concern is the chilling effect on reporting. Every school safety expert quoted in coverage of this breach said the same thing in different words: the system only works if people trust it. That trust is now broken in ways that will take years to repair - if it can be repaired at all. The next student who wants to report a threat about a classmate might now think twice, knowing that "anonymous" turned out to mean "8.3 million records in an unsecured database."
Anonymous reporting infrastructure is fragile by design. It depends entirely on the credibility of the promise of anonymity. Once you demonstrate that the promise was hollow, you do not get a second chance to make it. Navigate360 may survive this as a company. The concept of trusted anonymous tip reporting in American institutions may not recover as easily.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on TelegramSources: Ars Technica (Nate Anderson, March 26 2026); Education Week (March 2026); Portland Police Bureau public advisory (March 19 2026); Navigate360/P3 Global Intel website; P3Campus.com; Internet Yiff Machine release note via Straight Arrow News; Distributed Denial of Secrets.