Circle's Selective Justice: $230M in Stolen USDC Sailed Free While Legit Businesses Got Frozen

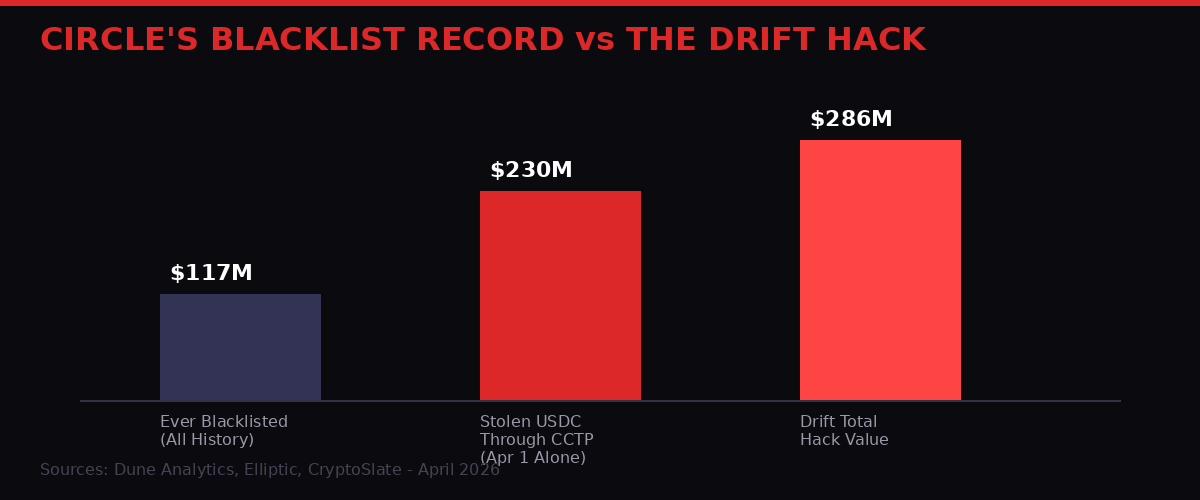
The numbers don't lie. In a single afternoon on April 1, 2026, more USDC flowed out of the Drift Protocol exploit through Circle's Cross-Chain Transfer Protocol than Circle has ever blacklisted in its entire operating history. That's not an operational failure. That's a policy choice.
Circle, the New York-based company behind USD Coin, holds one of the most powerful levers in decentralized finance: the ability to freeze any USDC wallet on any chain, instantly, at will. The company has exercised that power 601 times, locking up $117 million across its history (according to Dune Analytics data). But on the day of the largest DeFi exploit of 2026 - a North Korea-linked $286 million attack that funneled $230 million through Circle's own bridge - that lever stayed untouched.
What Actually Happened at Drift: The $286 Million Job
The Drift Protocol attack on April 1 was not an opportunistic exploit. It was a sophisticated, weeks-long operation executed with the precision of a professional intelligence service - which is exactly what it was.
Drift Protocol was the Solana ecosystem's largest decentralized perpetual futures exchange, holding approximately $550 million in Total Value Locked at the time of the attack. Three vaults held the bulk of that capital: the JLP Delta Neutral, SOL Super Staking, and BTC Super Staking vaults.
According to Drift Protocol's official post-mortem, the attacker compromised the protocol's Security Council. The mechanism was a "Durable Nonce" exploit - a phishing technique that blockchain security firm Slowmist founder Yu Xian described as having been "prevalent for at least 2 years." A durable nonce keeps an unconfirmed transaction valid indefinitely for offline approvals, meaning attackers can sit on a signed transaction until the moment is right, then trigger it on demand.
On March 30, the attackers quietly secured the necessary multisig approvals. The attack wallet was created approximately eight days before the exploit and had received a small test transfer from a Drift vault during that preparation period - a staging move consistent with DPRK operational security practices documented in previous Lazarus Group attacks.
On April 1, they moved. Admin authority was shifted, a fake asset called CVT was initialized, its value was artificially inflated through oracle manipulation, and the borrowed-against collateral was used to drain every major vault. Within hours, $286 million had left the protocol. DefiLlama data shows Drift's TVL collapsed to under $250 million - a 55% wipeout.
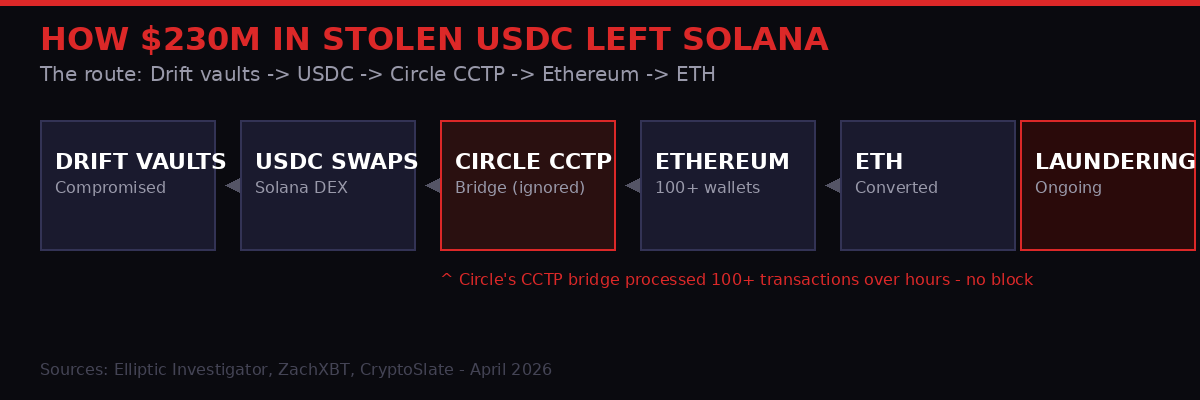
The laundering operation was equally methodical. ZachXBT's on-chain analysis documented that the attackers used a Solana-based DEX aggregator to rapidly swap stolen tokens into USDC, then bridged more than $230 million from Solana to Ethereum using Circle's Cross-Chain Transfer Protocol across over 100 transactions. On Ethereum, the USDC was converted to ETH and distributed further. The stolen funds held in USDC wallets for one to three hours before bridging - a window in which Circle could have deployed its blacklisting capability.
At least 20 third-party applications that relied on Drift's vaults for yield have reported financial impact from the attack. Prime Numbers Fi estimates losses exceeding $10 million from the protocol's collapse alone.
The March 23 Freeze: When Circle Did Act
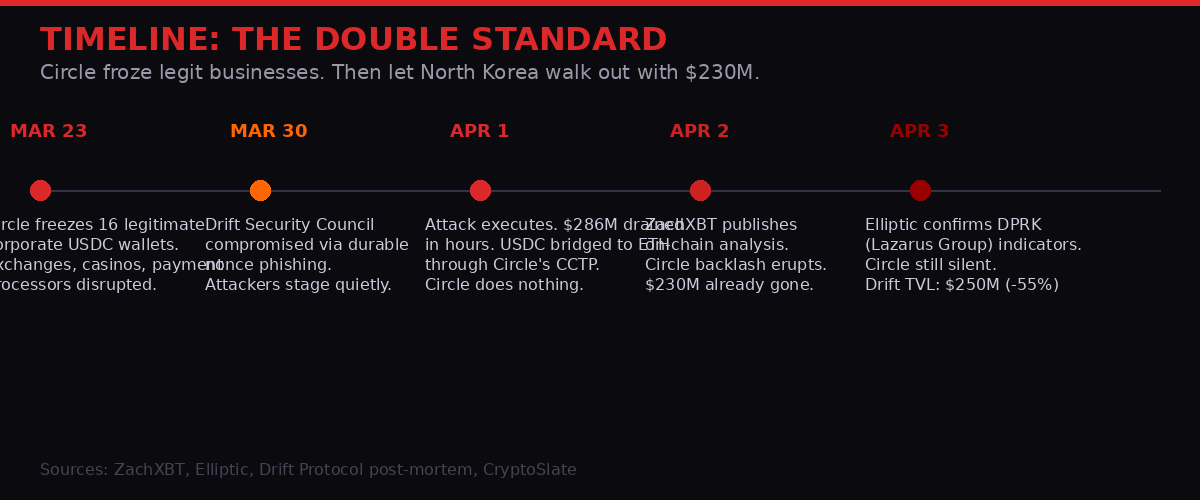
The contrast that has driven the backlash is not hypothetical. It exists on an exact timeline.
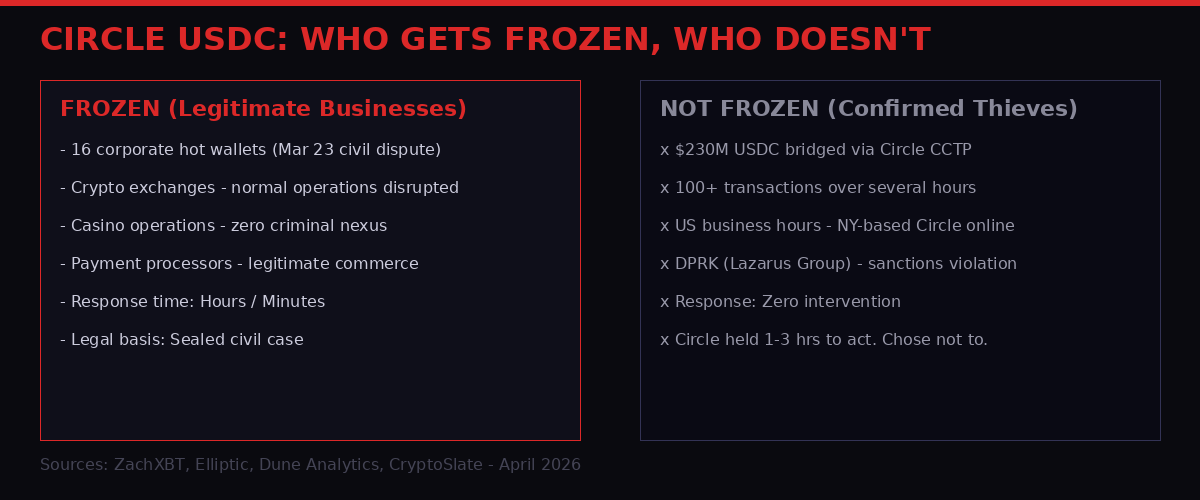
On March 23 - nine days before the Drift attack - Circle froze the USDC balances of 16 unrelated corporate hot wallets. The freeze was tied to a sealed US civil case. The companies affected included legitimate crypto exchanges, casino operations, and payment processors. None of them had been charged with a crime. None were under a criminal investigation. The legal basis was a civil dispute, behind a court seal, that Circle was using as grounds to immobilize the assets of businesses operating in good faith.
On-chain investigator ZachXBT, who has tracked Circle's enforcement activity for years, characterized the March 23 action as "potentially the single most incompetent" freeze he had witnessed in five years of monitoring the space. The freeze disrupted real-world commerce for businesses that had nothing to do with the underlying civil dispute.
Then nine days later, when a state-sponsored actor with documented sanctions violations and a track record of multi-hundred-million-dollar crypto theft was actively routing stolen funds through Circle's own CCTP bridge - during New York business hours, across 100+ transactions, over multiple hours - Circle's blacklist authority sat idle.
"Another encounter with the durable nonce offline pre-signature mechanism exploit. This phishing technique has been prevalent for at least 2 years. Once such a signature is phished away, the attacker can initiate 'legally signed' on-chain operations at a future opportune moment." - Yu Xian, Founder, Slowmist Security
The CCTP Argument: Did Circle Have a Choice?
Circle's defenders have pointed to a structural argument: the Cross-Chain Transfer Protocol is permissionless infrastructure. The company doesn't monitor every CCTP transaction in real-time. Intervening during a nine-figure exploit would require Circle to be actively watching on-chain activity at the moment of attack, identify the transactions as stolen, and make a split-second enforcement decision.
That argument holds less water than it might appear to. The attack lasted hours. The stolen USDC sat in identifiable wallets for one to three hours before bridging. The Drift team had already published an alert on X identifying an "active attack" and suspending deposits and withdrawals. Multiple blockchain security firms - Elliptic, PeckShield, Diverg, TRM Labs - were already flagging the attack in real time.
The DPRK attribution infrastructure, while it takes days to formally confirm, tends to trigger immediate monitoring alerts across the industry. The Bybit attack in February 2026, also attributed to Lazarus Group, had generated exactly this kind of cross-firm coordination - and $230 million flowing through CCTP in 100+ transactions over three hours during a known exploit would have been visible to any entity monitoring the bridge for anomalous volume.
There is also a precedent question. When the Drift attack began, Circle had already blacklisted $117 million across 601 wallets. It has clearly thought through what scenarios warrant intervention. The decision about whether to deploy the blacklist is not automatic - it requires human judgment. Someone at Circle made the call to act against 16 legitimate businesses on March 23. Someone did not make the call to act against $230 million in nation-state theft on April 1.
North Korea's 2026 Campaign: Drift Is Attack Number 18
The attribution is not speculative. Multiple independent blockchain intelligence firms have concluded, separately, that the Drift Protocol attack bears the hallmarks of North Korea's Lazarus Group - specifically the unit known as TraderTraitor, the same team behind the $1.5 billion Bybit attack in February 2026 and the $625 million Ronin bridge exploit in 2022.
Blockchain intelligence firm Elliptic published its analysis stating that "on-chain behavior, laundering methodologies and network-level indicators associated with the attack are consistent with techniques observed in previous DPRK-attributed operations." Diverg Security confirmed the same conclusion in coordination with TRM Labs and Elliptic.
"We can confirm along with TRM Labs and Elliptic that North Korea's Lazarus Group (TraderTraitor) [was behind the Drift attack]. The same unit [was] behind Bybit's $1.5 billion hack [and] Ronin's $625 million attack." - Diverg Security, via X
If confirmed at the formal intelligence level, Drift would represent the 18th DPRK-linked crypto theft in 2026, pushing the regime's confirmed haul for the year past $300 million (excluding the Bybit $1.5 billion, which alone would bring 2026 DPRK crypto theft to over $2 billion). The US Treasury has documented DPRK-linked actors stealing over $6.5 billion in cryptoassets across recent years, with proceeds directed toward the country's weapons programs.
The DPRK campaign is also escalating beyond direct protocol attacks. Google recently attributed a supply chain compromise of the Axios npm package to DPRK threat actor UNC1069 - a move that would theoretically allow infected code to propagate through countless crypto and web applications. The Drift attack is not an outlier. It is a data point in a sustained, sophisticated, state-level offensive against the crypto ecosystem.
The Cypherpunk Defense: Should Circle Ever Intervene?
Not everyone in the crypto community agrees that Circle should have acted. The debate has surfaced a genuine philosophical tension at the heart of stablecoin infrastructure.
Santisa, the pseudonymous CIO of investment firm Lucidity Cap, offered the counterargument on X:
"Circle not blacklisting is actually quite cypherpunk of them, no matter the reason. The industry pushing for active blacklisting puts us ever further away from decentralisation - not necessarily a bad thing! Just a trade-off." - Santisa, CIO of Lucidity Cap (via X)
The argument has internal logic. If Circle routinely blacklists wallets at the request of governments, law enforcement, or civil litigants, USDC becomes a censorship tool - no different from a traditional bank account that can be frozen by any court order. The asset's utility as permissionless money is compromised the moment it becomes routinely interruptible.
But the March 23 action undermines that defense entirely. Circle already proved it is willing to freeze assets in response to a sealed civil case. It is not operating as a neutral cypherpunk infrastructure provider. It is making selective enforcement decisions. The question is not whether to intervene - Circle has already answered that. The question is what criteria drive the decision, and right now those criteria appear opaque, inconsistent, and potentially liability-driven rather than principled.
If Circle had deployed its CCTP blacklist on April 1 against the Drift attackers, it would have been acting against a DPRK-linked entity under active US Treasury sanctions. That is one of the clearest possible legal grounds for enforcement action by a US-based financial entity. Instead, the company chose to take aggressive action against domestic businesses in a civil dispute while doing nothing about a confirmed sanctions violator transiting $230 million through its own bridge.
Regulatory Implications: What Happens to Circle Now
Circle is in the middle of building something ambitious. The company received conditional OCC approval for a national trust charter in December 2025 - part of a cluster of eight approvals in roughly four months that included Coinbase, Ripple, BitGo, Fidelity, and Paxos. That charter would allow Circle to operate custody and stablecoin infrastructure across all 50 states under a single federal supervisor.
The Drift episode puts that ambition in a complicated position. A national trust bank operating under OCC supervision has explicit compliance obligations around sanctions screening - particularly sanctions tied to DPRK, which the US Treasury's OFAC has designated as among the highest-risk jurisdictions for crypto-related money laundering. If Circle's CCTP bridge facilitated the movement of $230 million in funds connected to a DPRK-linked operation, regulators will want to understand what monitoring was in place and why no action was taken.
That is not a hypothetical concern. The Financial Crimes Enforcement Network (FinCEN) and OFAC have both signaled in recent years that stablecoin issuers operating bridges and settlement infrastructure have the same AML/sanctions obligations as traditional financial institutions. The "we're just infrastructure" defense is not one that US regulators have accepted from money services businesses, and it becomes even more untenable when the "infrastructure" company simultaneously demonstrates the ability and willingness to freeze assets in a civil dispute.
The broader regulatory trajectory is moving toward more stablecoin oversight, not less. The US Clarity Act stablecoin legislation is inching through Congress - stuck in a four-way deadlock over yield and regulatory authority, but moving. If that legislation passes, stablecoin issuers will face explicit federal requirements around reserve management, consumer protection, and potentially sanctions compliance. Circle's behavior during the Drift attack will become part of the documented record that regulators and legislators use to assess what those requirements need to look like.
What Circle Has (and Hasn't) Said
As of this writing, Circle has not issued a public statement specifically addressing its decision not to intervene during the Drift exploit. The company has not responded to questions about why the CCTP bridge continued processing transactions during a documented, multi-hour exploit by a DPRK-linked actor.
The silence stands in contrast to Circle's recent public positioning. CEO Jeremy Allaire has spoken extensively about USDC as a tool for financial inclusion and global dollar access. The company's pitch to regulators and institutional partners rests on the argument that USDC is both accessible and safe - that it can operate at scale without becoming a vector for illicit finance.
The Drift episode challenges both claims simultaneously. If $230 million can transit Circle's own bridge during a known exploit by a sanctions-designated actor, the "safe" argument needs work. If Circle's response to a civil dispute is to freeze 16 legitimate businesses while its response to North Korea is silence, the "accessible" argument is selective in a way that undermines user trust.
The Drift Users: What Comes Next
For the roughly 20 third-party protocols and the thousands of individual users who had funds in Drift's vaults, the situation is bleak in the short term and uncertain beyond that.
Drift Protocol has stated it identified "critical information about the parties involved" in the exploit - language that suggests law enforcement engagement. The Bybit hack earlier in 2026 generated significant inter-agency coordination, including US law enforcement and international partners in South Korea, Japan, and Europe. Similar coordination is likely underway for Drift.
Whether that coordination produces any asset recovery is a different question. The Lazarus Group has a documented record of successfully laundering large-scale crypto theft across chains. The Bybit haul, while partially frozen by exchanges that acted quickly, has mostly dispersed. The Drift funds are flowing through Ethereum in fragments across multiple wallets, with the clock ticking on the exchanges' ability to identify and freeze individual accounts before the trail goes cold.
Circle's inaction during the critical bridging window significantly reduced the odds of fund recovery. Once USDC crosses from Solana to Ethereum and is converted to ETH, the ability of any centralized actor to interrupt the flow drops dramatically. The 1-3 hour window in which the stolen USDC sat on Solana before bridging was the single best opportunity to stop or slow the theft. That window closed without intervention.
For Drift's remaining ecosystem, TVL collapsed from $550 million to under $250 million - a 55% wipeout that will take months to rebuild, if ever. The protocol is coordinating with security firms, bridges, and exchanges, but the trust damage to Solana's DeFi ecosystem from losing its largest perps exchange to a sophisticated state-sponsored attack is not something that disappears quickly. At least 20 third-party yield protocols have confirmed losses.
The Bigger Question: What Is a Stablecoin?
The Circle-Drift episode crystallizes a structural tension that the crypto industry has been avoiding for years: stablecoins like USDC cannot be both permissionless infrastructure and regulated financial instruments simultaneously. They are one or the other, and the entity issuing them has to pick.
Tether, Circle's main competitor, has a different reputation in this regard. USDT is renowned for blacklisting malicious actors. The Drift attackers explicitly avoided converting their stolen funds to USDT - a strategic calculation based on Tether's willingness to deploy its freezing capability. They bet that USDC would not intervene. They were right.
That calculus matters for the competitive dynamics of the stablecoin market. If sophisticated attackers consistently choose USDC as their preferred laundering vehicle because they have learned from experience that Circle won't act, USDC becomes infrastructure of choice for crypto crime. That is a reputational and regulatory problem that $77 billion in market cap cannot paper over indefinitely.
The $310 billion stablecoin market is heading toward formal federal regulation. Circle's OCC charter application puts it directly in the path of that process. Before that charter is finalized, regulators will have read every post-mortem from the Drift exploit. The question of what Circle knew, when it knew it, and why it didn't act is going to get answered - one way or another.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram