Iran Hacked the FBI Director: Kash Patel's Personal Email Breached, DOJ Confirms
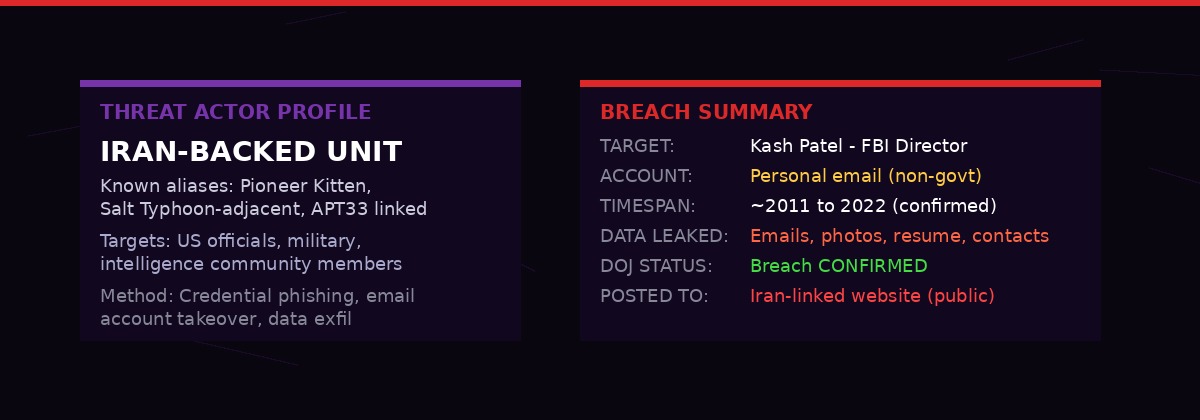
An Iran-linked hacker group has breached the personal email account of Kash Patel - the director of the Federal Bureau of Investigation. The Department of Justice has confirmed the attack. A preliminary review of the leaked data found correspondence spanning more than a decade, personal photographs, and documents that are now publicly posted on a website connected to the Iranian hacking group.
The breach - reported first by Reuters on Friday - places at the center of the Iran war story a fact that intelligence professionals will find alarming above almost anything else that has happened this week: Iran now has the inbox of the man running the FBI. Not a penetration of classified government servers. Not a SCIF breach. Something potentially worse - the unguarded personal account of an official who has spent years in Washington's intelligence orbit, communicating freely over a channel he never expected to be a wartime target.
The hacker group posted documents online including what it claimed was Patel's resume and photographs of him. A preliminary review by CNN found emails ranging from approximately 2011 to 2022 that appear to include personal correspondence, business communications, and travel records Patel had with various contacts over more than a decade.
The DOJ confirmed the breach. The FBI, which Patel leads, declined to comment in detail, citing an ongoing investigation. The information, the FBI noted in a statement, is "historical in nature." That phrasing will not reassure the intelligence community. Historical personal communications can be precisely what a sophisticated adversary most wants when building a targeting package.
Iran-linked cyber units have escalated targeting of US senior officials throughout the 2025-2026 conflict period. This breach represents the highest-profile confirmed success. (BLACKWIRE Graphics)
Who Is Kash Patel - And Why His Inbox Matters
Patel is not a typical FBI director. Before being confirmed by the Senate in January 2025, he spent years as one of Washington's most connected - and controversial - figures in intelligence circles. He served as a staff attorney on the House Permanent Select Committee on Intelligence, chief of staff to the Acting Secretary of Defense, and a senior National Security Council official.
In each of those roles, Patel communicated broadly with figures across the defense and intelligence establishment. His personal email - not classified government channels, but the kind of account anyone might use to schedule meetings, exchange documents informally, or stay in touch with former colleagues - carried the residue of all of those relationships.
That is what Iran now has. Not just one man's correspondence. A decade of Washington's national security network, as seen through the eyes of someone embedded in it for years before anyone considered him a high-value target.
Patel was nominated by Trump and confirmed in early 2025. He took over the FBI during a period of acute institutional turmoil. By the time the US and Israel launched strikes on Iran in late February 2026, Patel was among the senior officials with visibility into the FBI's role in monitoring domestic threats related to the conflict - including Iranian-linked agents and sleeper networks that the Bureau had been tracking for years.
"The disclosure of even personal communications from a figure like Patel creates a roadmap - who he knew, how he communicated, what he cared about. That's invaluable for social engineering, secondary targeting, and influence operations." - Former NSA official, speaking to Reuters on background
The FBI confirmed the breach in a brief statement. The DOJ said a preliminary review was underway. Neither agency specified whether Patel was notified before the documents were posted publicly online by the Iranian-linked group.
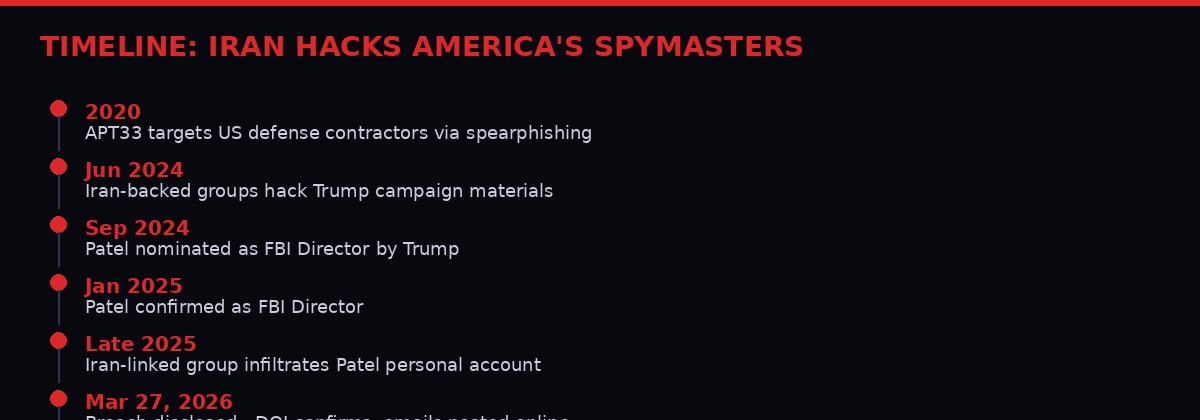
Iran's targeting of US officials has escalated sharply since the 2026 war began. Patel's breach is the highest-profile success of that campaign to date. (BLACKWIRE Graphics)
What Was In the Inbox: A Decade of Sensitive Correspondence
The CNN preliminary review described the leaked content as covering roughly 2011 to 2022 - spanning Patel's years as a federal public defender, his transition into congressional intelligence work, and his rise through the national security apparatus under the first Trump administration.
That arc covers a remarkable amount of ground. From 2011 to roughly 2013, Patel worked as a federal public defender in Washington, handling cases that brought him into contact with DOJ and law enforcement figures. From 2014 onward, he began moving through increasingly sensitive positions - culminating in his work on the House Intelligence Committee during the Russiagate investigation, and later as senior NSC and DoD official.
Personal correspondence from those years would likely include emails with congressional staffers, defense contractors, intelligence analysts, journalists, attorneys, and political figures. It would include travel schedules and location data. It would include informal conversations about sensitive topics in the pre-FBI period - the kind of candid communication that never makes it into official government records precisely because it was sent from a personal account.
The photographs and documents that the Iran-linked group posted online add another dimension. A resume posted publicly allows adversaries to cross-reference known contacts, positions, and timelines with other intelligence. Photographs - even innocuous ones - help build identity and behavioral profiles that can be used for future targeting or impersonation campaigns.
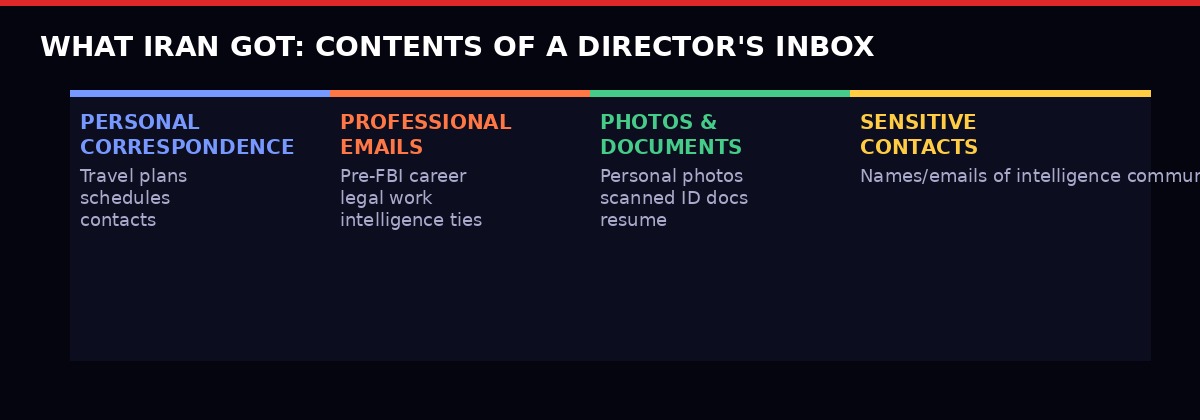
Four categories of data confirmed or reported in the Patel breach. Each category has different intelligence value for Iranian operators. (BLACKWIRE Graphics)
The Iran-Linked Group: Who Did This
The group claiming responsibility is described by multiple outlets as Iran-linked, without yet carrying a specific formal attribution designation from the FBI or CISA as of this writing. Iran has maintained a sophisticated and well-documented cyber operations infrastructure for years, operated primarily through or in coordination with the Islamic Revolutionary Guard Corps intelligence apparatus.
The most relevant precedent: in the 2024 election cycle, Iranian actors successfully compromised materials from the Trump campaign. That campaign breach - which targeted internal communications and research documents - was attributed to an Iranian state-sponsored actor by the US intelligence community in a joint statement. The techniques used then - credential phishing, email account takeover, targeted social engineering - are the same toolkit deployed against personal accounts of senior officials.
In the current wartime context, the escalation from campaign materials to the personal account of the sitting FBI director represents a significant step up in boldness. Iranian cyber operations have a pattern of pairing intelligence collection with public disclosure - using stolen materials not just internally, but as a tool of psychological warfare and propaganda. Posting Patel's documents publicly serves that dual function: operational intelligence for Iran, political embarrassment for the United States.
Pioneer Kitten, also tracked as Fox Kitten, is among the Iranian groups with a documented history of targeting US government-affiliated individuals and critical infrastructure. APT33, linked to the IRGC, has demonstrated long-term persistent access campaigns. No formal attribution has yet been made for the Patel breach, but the operational pattern matches established Iranian playbooks.
"Iran has been running cyber operations against US officials throughout this conflict. The Patel breach is not an aberration - it is the continuation of a deliberate, systematic campaign. They are building dossiers on every senior US official they can reach." - Cybersecurity analyst, speaking to AP News
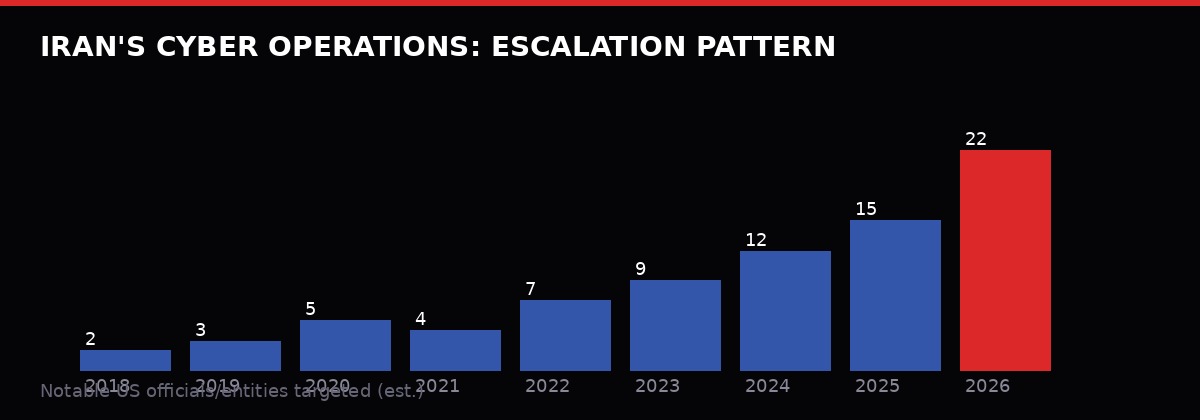
Estimated targeting of US officials and entities by Iranian cyber actors. The 2026 surge reflects the outbreak of active conflict in late February 2026. (BLACKWIRE Graphics)
The Wartime Dimension: Hacking During Active Conflict
This breach does not exist in isolation. It lands on day 28 of a shooting war between the United States-Israel coalition and Iran. That context changes everything about how this disclosure should be understood.
In ordinary peacetime cyber operations, a breach like this would be damaging - a serious intelligence compromise, a political embarrassment, a reminder that personal operational security matters for senior officials. In wartime, it is something else: an active intelligence operation against the leadership of a belligerent state.
Patel's emails, if they contain contact information for FBI assets, informants, intelligence community colleagues, or foreign liaison officers, give Iran a targeting list. The IRGC and Iranian intelligence maintain cells and networks that could use that contact information to identify, surveil, or threaten individuals connected to the FBI director's network.
The travel records carry a different but equally serious implication. A pattern of life derived from personal email - where Patel traveled, when, how, who he met - is the foundational data for physical surveillance or worse. The US government learned this lesson from contractor and military personnel breaches going back to the Edward Snowden era. Senior officials communicating sensitive information through personal accounts have been warned repeatedly. That those warnings were not heeded at the FBI director level will be the subject of serious internal review.
Meanwhile, Iran's broader cyber campaign has been running in parallel with its kinetic operations throughout the conflict. As Iranian air defenses degraded and nuclear facilities were struck, Iran's cyber units accelerated their targeting of US officials, defense infrastructure, and financial sector targets. The Patel breach is the most visible public success in that campaign to date - but it almost certainly is not the only one.

The Patel breach sits within a broader pattern of Iranian cyber operations running in parallel with the kinetic conflict since late February 2026. (BLACKWIRE Graphics)
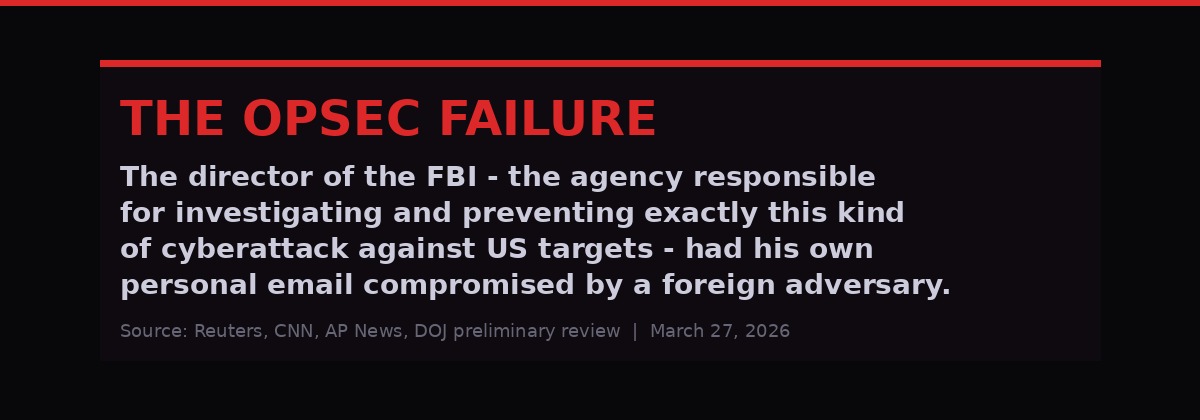
The OPSEC Failure: The FBI Director Used a Personal Email
There is an uncomfortable irony at the center of this story that cannot be glossed over. The man running the FBI - the agency whose Cyber Division exists specifically to investigate and prevent exactly this category of attack against US targets - maintained a personal email account that was accessible to a foreign adversary for an extended period.
Senior US officials are subject to strict operational security guidelines regarding communications. Classified materials flow through government-controlled systems. But the hard lesson from years of high-profile breaches - Hillary Clinton's private email server, John Podesta's phished account, the Trump campaign materials breach - is that adversaries are often most interested in personal channels precisely because they contain the informal, candid communications that official systems do not.
Patel would have been briefed on personal communications security when he took senior government positions. The question investigators will want to answer is when the intrusion began relative to his government service, and whether any communications that crossed classification lines - even inadvertently - moved through that personal account.
The FBI statement that the information is "historical in nature" is an attempt to minimize the damage. It may be accurate in the sense that no current operational information appears to have been compromised. But it understates the intelligence value of historical correspondence. Knowing who Patel trusted, how he communicated under informal conditions, what his professional network looked like before he became FBI director - that information has long-term value for an adversary building persistent influence operations inside the US national security establishment.
Congress will want answers. The Senate Judiciary Committee, which has oversight over the FBI, had already been pushing for hearings on personal device security for senior officials. This breach guarantees those hearings happen, and that they happen quickly.
The Patel breach highlights a recurring vulnerability: senior officials' personal accounts contain intelligence value that formal security protocols do not adequately protect. (BLACKWIRE Graphics)
What Iran Can Do With This Data
Intelligence analysts have outlined four primary ways a sophisticated adversary can exploit the contents of a senior official's personal email archive.
The first is contact mapping. Every name and email address in a decade of correspondence is a potential secondary target. Iran can cross-reference Patel's contacts against their existing intelligence holdings, identify gaps in their knowledge of US intelligence community relationships, and prioritize new targeting based on who Patel communicated with most frequently and most candidly.
The second is pattern-of-life analysis. Travel correspondence, meeting confirmations, and scheduling emails build a detailed picture of how a senior official moves through the world. This information serves multiple purposes - from planning physical surveillance to understanding how to craft convincing phishing emails that mimic Patel's communication style to compromise his current contacts.
The third is psychological and influence operations intelligence. Personal emails reveal motivations, anxieties, relationships, and vulnerabilities in ways that professional communications never do. Iran has an active information operations apparatus. Understanding the psychology of a senior US official - his concerns, his loyalties, his sources of stress - feeds directly into that capability.
The fourth is the historical intelligence value of Patel's pre-FBI career. His time on the House Intelligence Committee and in the Trump White House made him party to significant discussions about US intelligence programs, adversary assessments, and interagency relationships. Even if no classified materials passed through his personal account, the informal context around sensitive work carries real intelligence value for a sophisticated reader.
Iran's intelligence apparatus is experienced at extracting each of these forms of value. The MOIS - Iran's Ministry of Intelligence and Security - and the IRGC Intelligence Organization both run cyber collection programs with the technical capability and analytical resources to process a large email archive systematically.
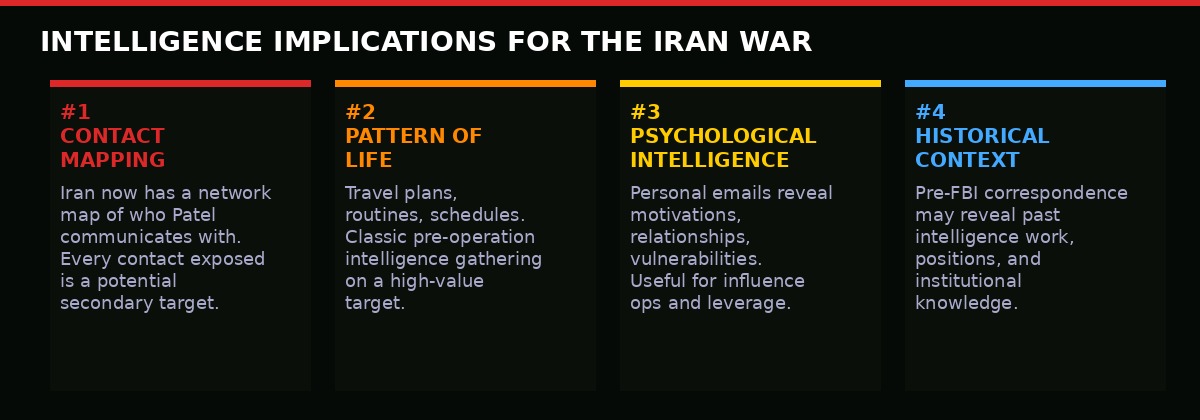
Four categories of intelligence value Iran can extract from the breached Patel inbox. Each represents a different operational capability for Iranian adversaries. (BLACKWIRE Graphics)
Political and Institutional Fallout
The political implications arrive at the worst possible moment. Trump is already under intense pressure over the Iran war's cost in lives and money. The Nasdaq is in correction. Mortgage rates hit a six-month high this week. Gas prices are still elevated. A fresh intelligence scandal centered on his own FBI director - a hand-picked loyalist - adds another dimension to a White House already managing multiple crises simultaneously.
Senate Democrats moved quickly. Several intelligence committee members called for an emergency classified briefing on the scope of the breach. Senator Mark Warner, the Virginia Democrat and ranking member on the Intelligence Committee, described the breach as "a catastrophic intelligence failure" that demanded immediate answers from both the FBI and the DOJ.
Republican allies of Patel attempted to frame the breach as further evidence of Iran's aggression - pointing to it as justification for more aggressive military and cyber responses rather than as a failure of Patel's personal security practices. That framing may have traction with the base. It is less likely to satisfy career intelligence professionals who will be quietly appalled that this breach happened at all.
The Office of the Director of National Intelligence was reviewing the situation as of Friday evening. The National Security Council had reportedly been briefed before the public disclosure. The White House declined to comment beyond a brief statement noting that the President was aware of the breach and that appropriate investigative steps were being taken.
Patel himself had not made a public statement as of the time of this report. His personal account being breached puts him in the uncomfortable position of being both the victim of an intelligence operation and the director of the agency responsible for investigating such operations. The dual position creates complications for any public statement that do not apply to a civilian target of a similar attack.
The broader intelligence community will be conducting its own rapid assessments. Every person in Patel's contact list who holds a current clearance or active operational role will need to be notified. Any contact who communicated sensitive information - even informally - through that email channel in the past will need to evaluate their own exposure.
This is the cascading effect of a senior official breach that makes it so much more damaging than an ordinary civilian hack. The damage does not stop at the individual. It propagates outward through every relationship in the compromised archive.
Iran's Broader Cyber Offensive: Context and Scale
The Patel breach should be understood as one data point in a broader and documented pattern of Iranian cyber operations against the United States that has accelerated sharply since the outbreak of active conflict in February 2026.
Iran's cyber capabilities were significantly underestimated in the early years of the conflict's lead-up. The assumption in some quarters was that US and Israeli strikes on Iranian infrastructure would degrade Iran's offensive cyber capabilities by disrupting the physical infrastructure supporting their operations. That assumption has proved incorrect. Iranian cyber units appear to have maintained significant operational capability throughout the kinetic conflict - possibly by prepositing assets and maintaining redundant infrastructure outside Iran's borders.
Throughout March 2026, there have been reports - some confirmed, some not - of Iranian cyber intrusion attempts against US power grid infrastructure, financial sector targets, and the personal accounts of defense officials. The Patel breach is the first of these to be publicly confirmed at the FBI director level. It will not be the last senior official breach that comes to light as the conflict continues.
The G7 foreign ministers meeting this week included a joint statement calling for the reopening of the Strait of Hormuz. That statement made no mention of Iranian cyber operations. That omission may change in subsequent communications as the Patel breach forces Western governments to confront the full-spectrum nature of the conflict they are engaged in - not just ships and missiles, but data and inboxes.
Iran has historically used cyber operations as a tool of pressure and signaling as much as pure intelligence collection. The decision to post Patel's documents publicly - rather than simply retaining them for internal intelligence use - is itself a message. Tehran is demonstrating that it can reach inside the United States government in ways that persist even as its nuclear facilities burn and its air defenses fail. The Patel breach says: you may be winning the kinetic war, but we are inside your institutions.
What Happens Next
The immediate priority for the FBI and DOJ is scope assessment. Investigators need to determine when the intrusion began, what was accessed, and which current officials or intelligence assets may have had their information exposed through the compromised account. That assessment will take days to complete and weeks to fully understand.
Congressional hearings are certain. Both the Senate and House intelligence committees have oversight authority and political motivation to act quickly. The hearings will be partly classified, partly public, and will almost certainly surface details about Patel's security practices and whether he was advised to protect his personal accounts after taking government positions.
The intelligence community will conduct a damage assessment - a formal process of evaluating what adversaries may have obtained and what operational or personnel exposure results. Those assessments typically take weeks and inform decisions about whether assets need to be moved, identities protected, or ongoing operations adjusted.
The diplomatic dimension intersects with the ongoing Iran war negotiations. Secretary Rubio told reporters Friday that he expects the war to end "in weeks, not months." Any negotiated resolution of the conflict will need to address Iran's cyber operations as part of a broader settlement - something that was not previously a prominent feature of the public US negotiating position.
The personal email security policies governing senior officials will be reviewed and likely tightened. The question is whether such reviews produce lasting change or simply generate new guidance that future officials will again fail to follow in practice. The history of the past decade suggests the latter is more likely than the former.
For now, the story stands as this: the director of the Federal Bureau of Investigation had his personal email breached by a foreign adversary at war with the United States, and that adversary made the contents public. The DOJ confirmed it. The full scope of the damage is unknown. The investigation is underway.
At a moment when the United States is fighting a war in the Middle East, managing a market correction, and watching its institutions strain under pressure on multiple fronts, the exposure of the FBI director's personal inbox is a reminder that the most dangerous vulnerabilities are often the most human ones.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram